Featured News
-

 206News
206NewsScammers Hack Cricket South Africa Facebook Page with Adult Content
Cricket South Africa page got hacked earlier today where hackers posted racist and sexual content on the page which surprised many of...
-

 256Data Security
256Data SecurityBitcoin’s Creator Satoshi Nakamoto Is Probably This Unknown Australian Genius
EVEN AS HIS face towered 10 feet above the crowd at the Bitcoin Investor’s Conference in Las Vegas, Craig Steven Wright was,...
-

 169Hacked
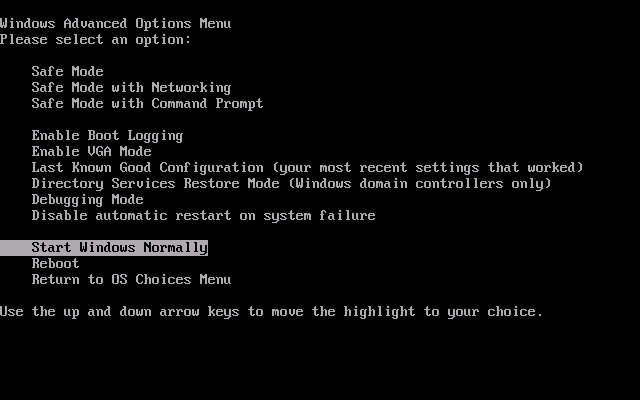
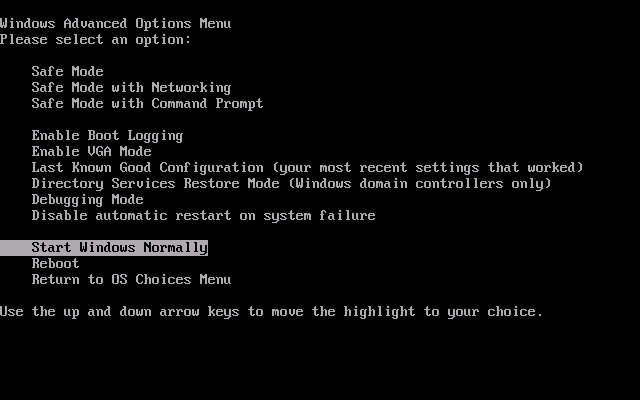
169HackedKudos! Microsoft Does It Once Again
Short Bytes: Microsoft, long known for harbouring different kinds of malware, this time, “unveils” bootkit, a malware which loads even before the Windows...
-
 179Malware
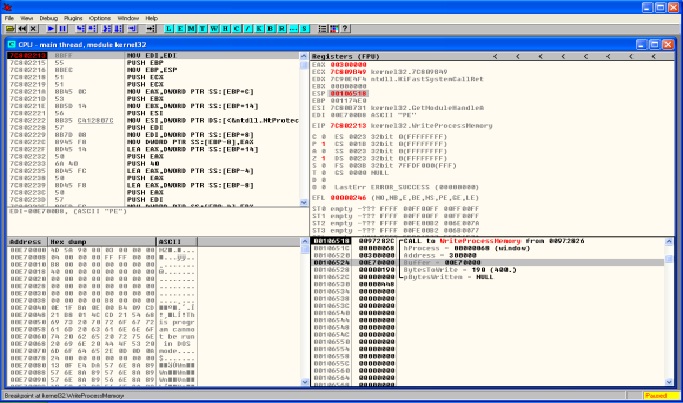
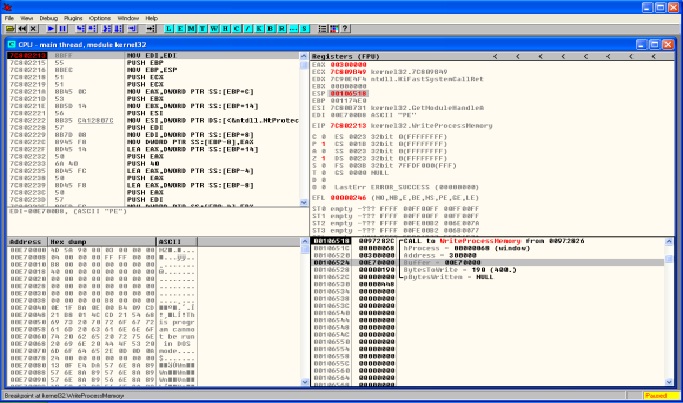
179MalwareMALWARE ANALYSIS – DRIDEX & PROCESS HOLLOWING
Lately the threat actors behind Dridex malware have been very active. Across all the recent Dridex phishing campaigns the technique is the same....
-

 162Vulnerabilities
162VulnerabilitiesApple Patches 50 Vulnerabilities Across iOS, OS X, Safari
Apple has piled on the patches already released by Adobe and Microsoft today, and pushed out updates for iOS, OS X, Apple...
-
 116Incidents
116IncidentsInternet’s root servers take hit in DDoS attack
The internet’s root servers came under a concerted distributed denial of service (DDoS) attack last week that effectively knocked three of the...
-

 279Geek
279GeekNew Facebook Phishing Scam Targets Page Admins
A recent Facebook phishing scam asks users on the social media giant to verify their page because a suspected page forgery was detected...
-

 130Data Security
130Data SecuritySecurity Flaw in Honeywell Gas Detectors Can Virtually Kill People
After hacking nuclear plants, Refrigerator, House Arrest Ankle Bracelet, Smartphones GPS Signals, Electronic Skateboards, Driverless Cars, Jeep, Computer Controlled Sniper Rifle and Jeep Cherokee etc, it is now time...
-

 227Hacked
227HackedContribute Anonymously To Git Repositories Over Tor With Gitnonymous Project
Short Bytes: With gitnonymous project, now you can obfuscate your true identity while making Git commits and pushing to public repositories. Using the...
-
 270News
270NewsPakistani Veteran Journalist Hamid Mir’ Twitter Account Hacked
The official Twitter account of renowned Pakistani journalist Hamid Mir has been hacked by an unknown hacker who is now leaking screenshots...
-

 295Geek
295GeekDisabled Intrusive Win10 Data Collection Features Re-enabled After Nov Update
Windows 10 spying on users is not a new thing nor its force downloading tactics but Windows 10’s November update saw marked improvement...
-

 295Opinion
295OpinionCopyright and social media
ESET's senior research fellow David Harley explores and discusses the main issues surrounding copyright and social media.
-

 139News
139NewsTuneCore Record Label Hacked, Musicians’ Data At Risk
TuneCore, an online music distribution/record label service on Friday, revealed that its database was breached by the hackers and they have been...
-

 214Data Security
214Data SecurityLearn how Eliot from Mr.robot hacked into to his therapist’s new boyfriend’s email and bank accounts
Social engineering is a pretty important item in a hacker’s toolkit.in Mr robot there was a time, we see Elliot, using social...
-

 89Data Security
89Data SecurityPersonal data of Dutch telecom providers extremely poorly protected: how I could access 12+ million records #phonehousegate
On September 11, 2015 I visited Media Markt in Utrecht Hoog Catherijne, a well-known electronics shop in The Netherlands. Since summer 2014, the biggest independent Dutch...
-

 181Opinion
181OpinionWearables: where’s the security risk?
At a recent conference on “the future of wearables” I was asked to speak about security. I think my presentation surprised some...
-

 138Vulnerabilities
138VulnerabilitiesGoogle patches critical vulnerabilities in Android
The flaws can be exploited remotely through emails, Web pages, MMS and rogue apps. Google has released a new batch of security fixes...
-
 173Data Security
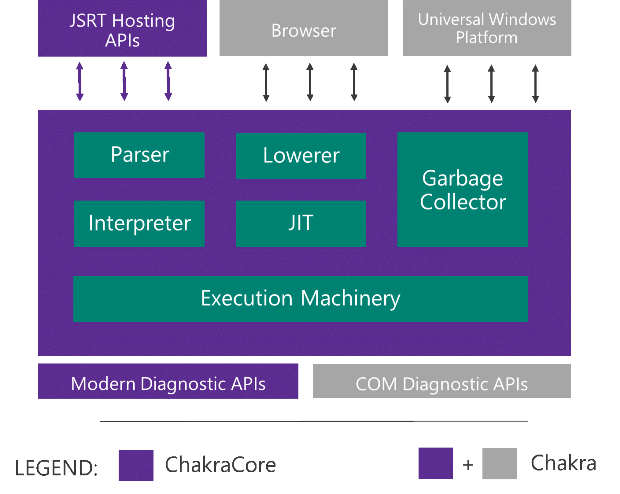
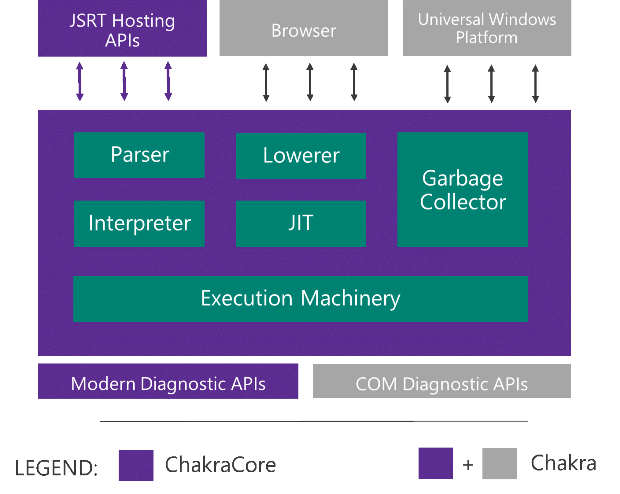
173Data SecurityMicrosoft Edge’s JavaScript engine to go open-source
Today at JSConf US Last Call in Florida, we announced that we will open-source the core components of Chakra as ChakraCore, which...
-

 194Incidents
194IncidentsMalware Steals iOS and BlackBerry Backups via Infected PCs
BackStab technique helps criminals get their hands on your private data, via unprotected phone backups A recent report from Palo Alto Networks...
-
 158Data Security
158Data Security“Nemesis” malware hijacks PC’s boot process to gain stealth, persistence
Bootkit targeting banks and payment card processors hard to detect and remove. Malware targeting banks, payment card processors, and other financial services...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




