Featured News
-

 166Cyber Crime
166Cyber CrimeHackers announce WWE’s Jim Ross is dead, after wrestling control of his Twitter account
Leeds United-loving football fans appear to have hacked the Twitter account of WWE legend Jim Ross, and announced his death.
-

 351Data Security
351Data SecurityFallout 4 Pirated Copy Leads To Bitcoin Theft
People who download stuff from torrents and other cracked software providing websites have a very bad news because a user recently downloaded...
-

 228Cyber Events
228Cyber EventsFrance May Ban Public Wi-Fi and Tor Following Paris Attacks
The government of France is in discussions on blocking Tor anonymity network and also the shared and free wifi network during a state...
-

 123Vulnerabilities
123VulnerabilitiesJava Deserialization Vulnerability Found in More Java Libraries
Initial issues trickle down to other Java toolkits.Exactly a month ago, we were reporting on an issue that exposed many Java applications...
-

 229Data Security
229Data SecurityFrance proposes to ban Tor and forbid free Wi-Fi
Proposed French Law Would Ban TOR In Response to Paris Terror Attacks France is looking to tighten its censorship laws after the...
-

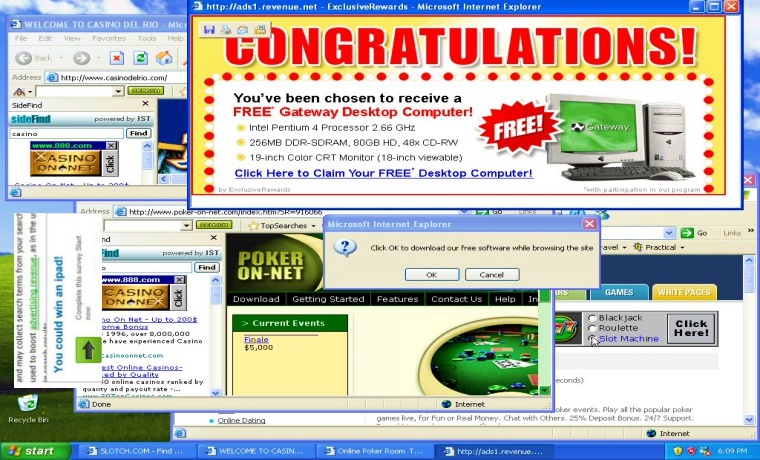
 205Malware
205MalwareInfostealers, Exploit Kits & Ransomware, Just Your Typical Malware Campaign
A look inside your typical malware campaign.In an optimal scenario, when you get infected with malware, you think it’s only one virus....
-
 225Vulnerabilities
225Vulnerabilities3-Year-Old Vulnerability Affects Millions of Smart TVs, Phones, and Routers
Trend Micro reports that 6.1 million devices are affected.A 3-year-old bug in the Portable SDK for UPnP Devices, also called libupnp, is...
-

 254Hacked
254HackedProposed Laws Can Result In Banning Tor And Free Wi-Fi In France
Short Bytes: The French government is actively researching the options to make its surveillance options more effective. In the wake of recent...
-

 239Data Security
239Data SecurityHackers Build Rootnik Trojan on Top of Android Rooting Toolkit
Why create your own rooting functions when someone else has already put the effort into doing the same thing Security researchers have...
-
 214Data Security
214Data SecurityUnwanted Browser Ads, A Sign Your PC is Infected with Malware
If your browser displays unwanted and wrongly placed ads such as an adult website ad on a website for kids or showing...
-

 292News
292NewsJoin Anonymous on 11 December, It’s The Official ISIS Trolling Day
After creating havoc among ISIS circles by hacking their social media accounts, Anonymous is back again and this time it aims at...
-
 260Geek
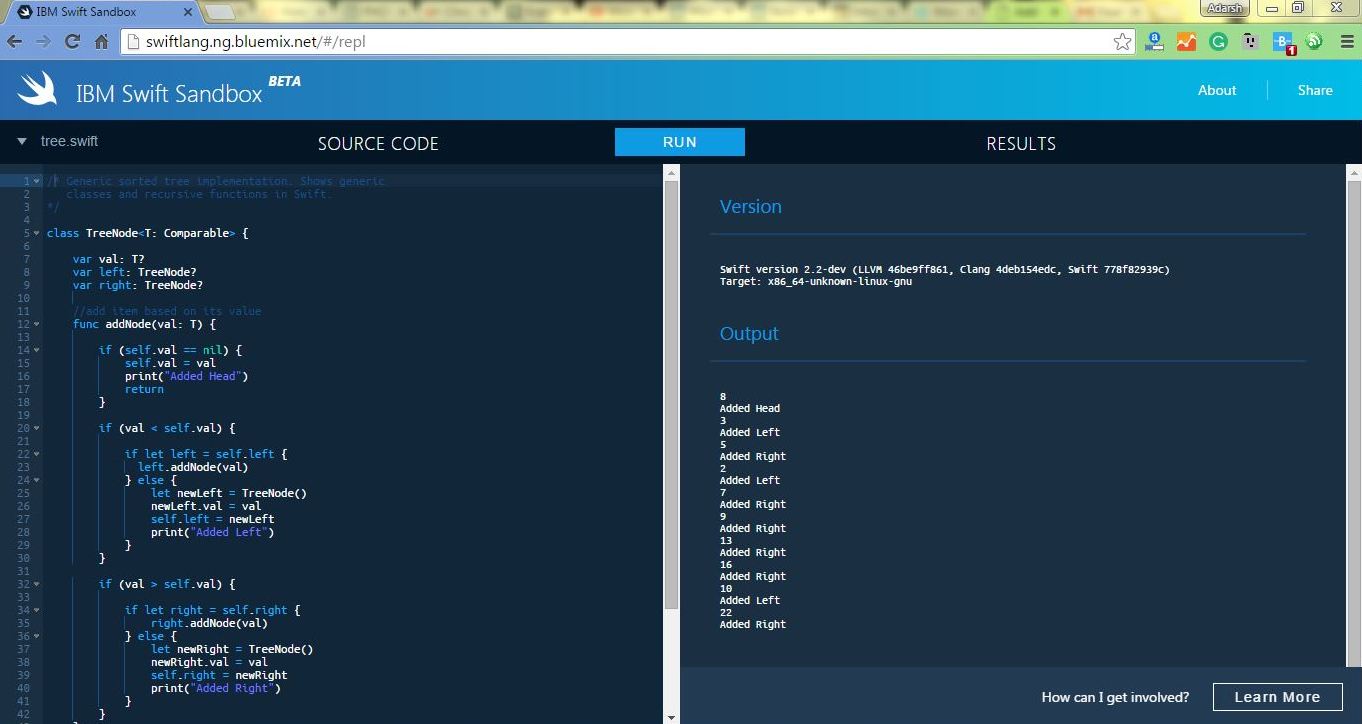
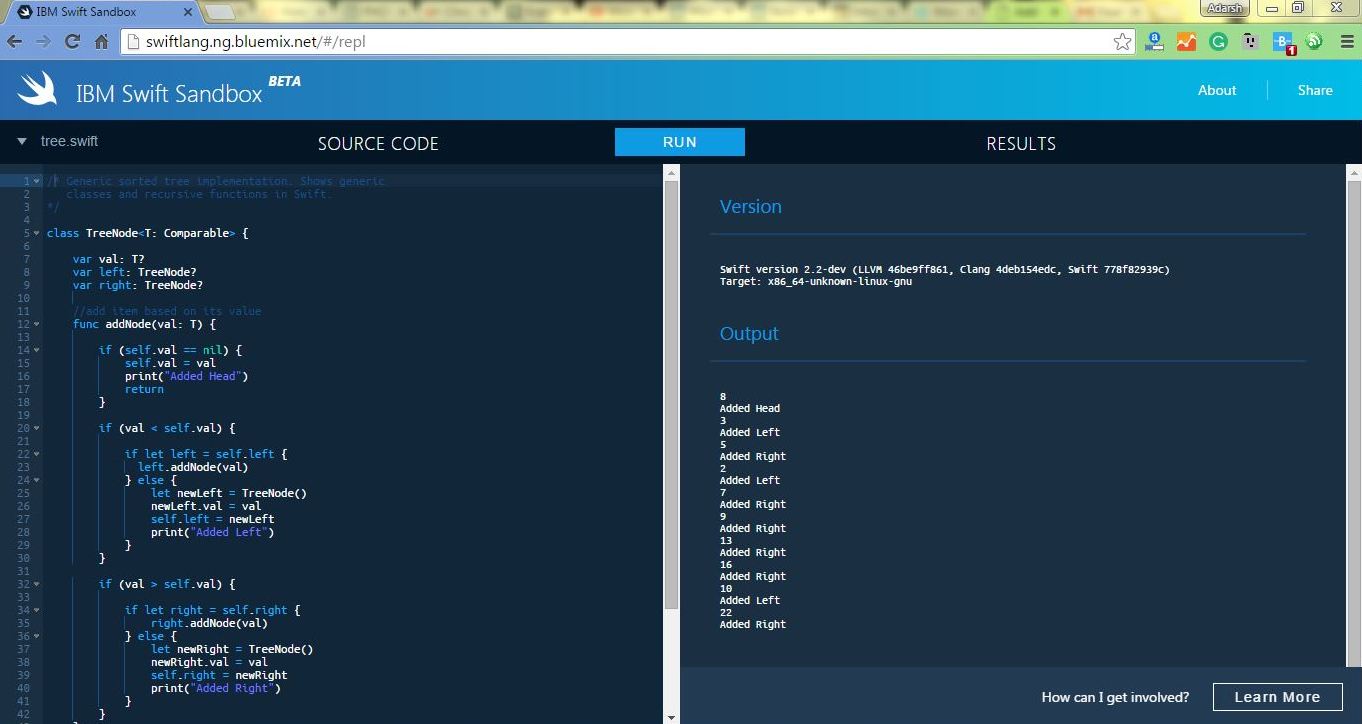
260GeekNow Run Apple’s Swift Programming Language Online In IBM Swift Sandbox
Short Bytes: To make learning Apple’s programming language Swift easier, IBM has launched an online Swift Sandbox. Here, you can write and...
-

 353Geek
353GeekArab Coalition Forces Let You Watch Yemen War on Snapchat
Do you want to watch the Saudi Arabian-led war in Yemen on your mobile device? Well, there is a guy who is...
-

 318Cyber Crime
318Cyber CrimeCrooks Targeting LinkedIn Users with Fake Profiles
LinkedIn can be a hacker’s treasure trove and job seeker’s nightmare. The IT security company Symantec revealed that dozens of fake accounts...
-

 239News
239NewsCanadian Police Vow to Hunt Cyber Criminals and Anonymous
Will Canada’s new Cybercrime division Curb Cybercrimes and capture Anonymous? Since the approval of Canadian Anti-Terror Bill C-51, online privacy is in...
-

 344Data Security
344Data SecurityNew Ransomware Exploit Kit Blends with Credential Theft Ability
A new campaign has come to light that spreads the CryptoWall 4.0 (file-encrypting ransomware program) using Angler exploit kit by inserting malicious...
-

 341Data Security
341Data SecurityDorkbot and associated Botnets Temporarily Disrupted
The world’s most widely proactive malware group Dorkbot and all of its associated Botnets have been disrupted. This disruption was made possible...
-
 202Hacked
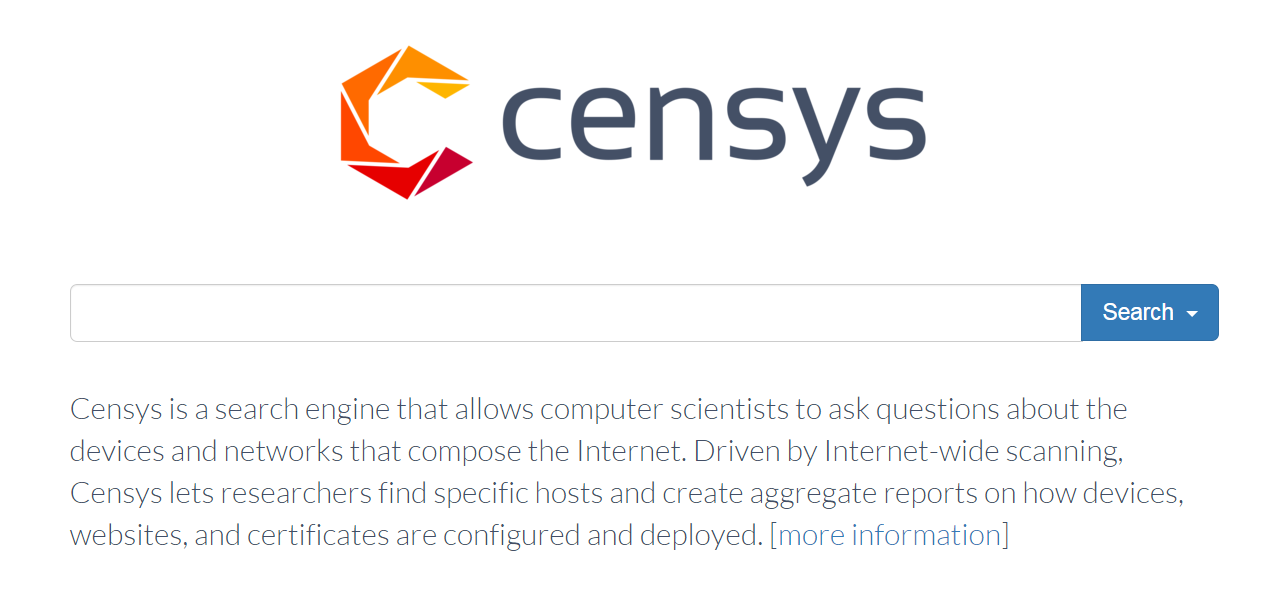
202HackedGoogle Is Powering A New Search Engine That Digs Internet’s Dirty Secrets
Short Bytes: Ever heard of Shodan and ‘appreciated’ its capabilities? Here, you are going to read about another similar, but a smarter hacker’s search...
-

 193Hacked
193HackedWorld’s Fastest Password Cracking Tool Hashcat Is Now Open Source
Short Bytes: The world’s fastest cracking tool Hashcat is now open source. The company has called it a very important step and listed...
-

 96Data Security
96Data SecurityHow to Hack Smartphones
More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




