Featured News
-
 300Geek
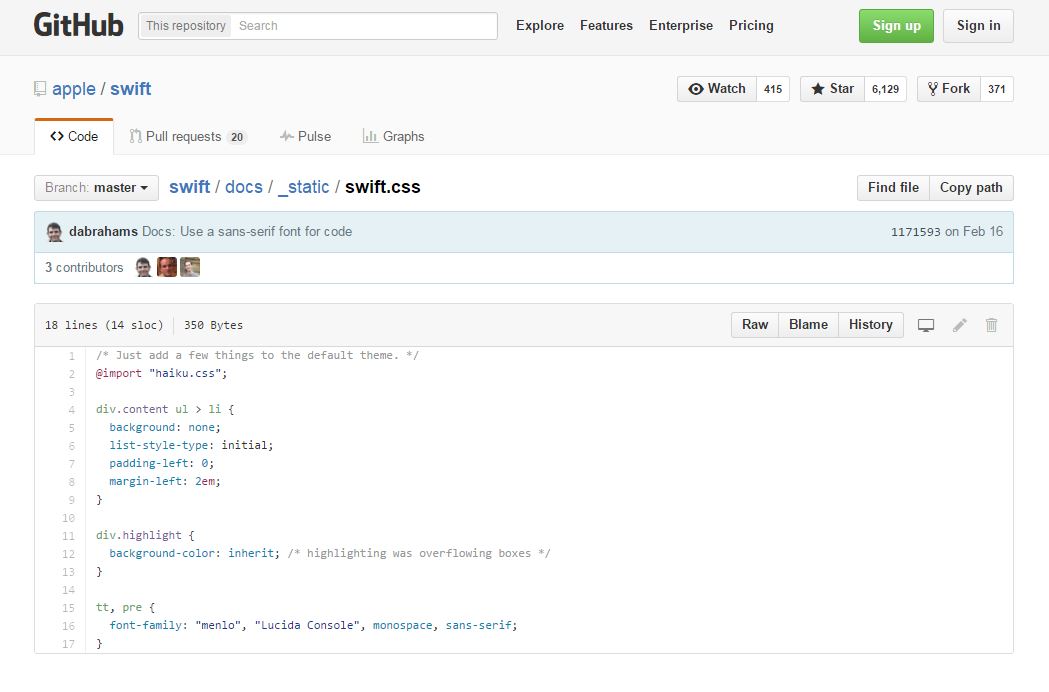
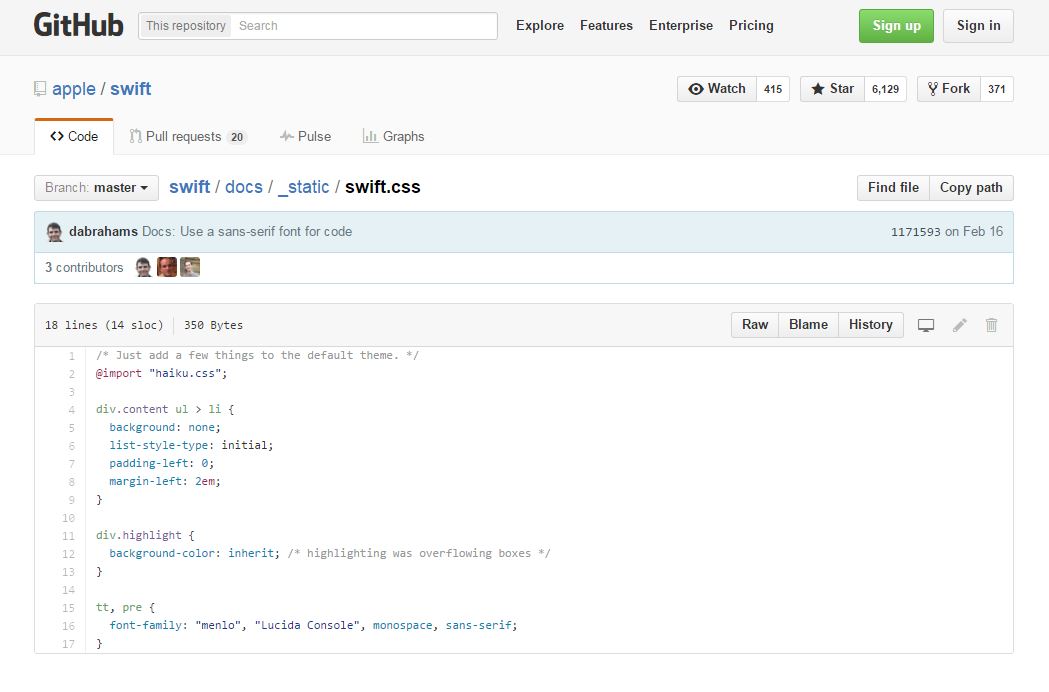
300GeekApple Makes Its Swift Programming Language Open Source
Short Bytes: Apple has made good on its promise to make Swift an open source programming language under the Apache License. The...
-

 280News
280NewsAnonymous Trolls ISIS with Photoshopped Images on Twitter
The largest Anonymous Twitter account was found trolling the ISIS symporters with memes and photoshopped images. Anonymous is known for exposing social...
-

 304Data Security
304Data SecuritySnowden’s Advised Encrypted Messaging Service Available For Desktop
In November 2015, the Open Whisper system launched protected voice calling and texting application for Android called “Signal” but soon after the...
-

 254Geek
254GeekPrivacy Advocate Group Accuses Google of Spying via Chromebook
Google accused by EFF for Collecting Students Data via Chromebook. The Electronic Frontier Foundation, a civil liberties group, has lodged a complaint...
-
 255Geek
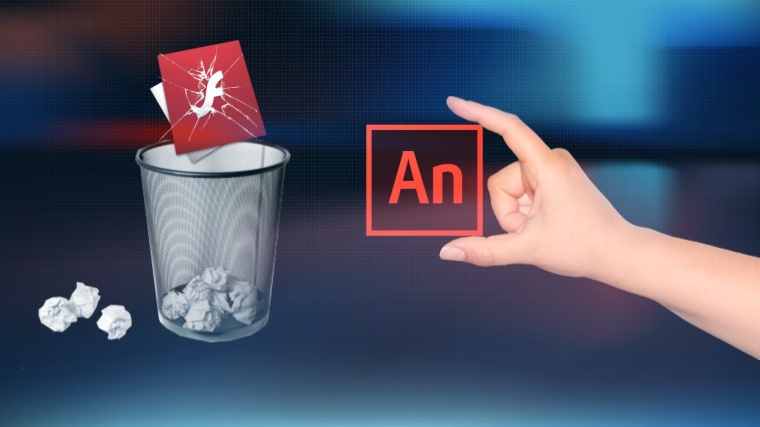
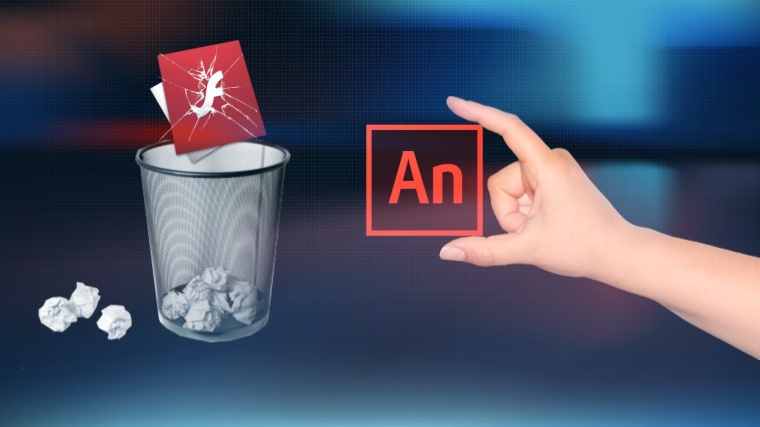
255GeekRIP Flash- Adobe is Getting Rid of Flash, Introducing Animate CC
After being an object of constant criticism universally by IT professionals for being volatile, unstable and unreliable, the time has come to...
-
 270Vulnerabilities
270VulnerabilitiesElasticZombie Botnet – Exploiting Elasticsearch Vulnerabilities
With the rise of inexpensive Virtual Servers and popular services that install insecurely by default, coupled with some juicy vulnerabilities, like CVE-2015-5377...
-

 130Incidents
130IncidentsAccidental DDoS takes down Google’s European cloud
Google got accidentally DDoSed by an unnamed European network carrier, sending its cloud service offline on the old continent for about an...
-

 177Data Security
177Data SecurityChina arrested hackers suspected of OPM hack
The Chinese Government says it has arrested the hackers responsible for breaching the Office of Personnel Management database (OPM). The Chinese government...
-

 109Vulnerabilities
109VulnerabilitiesCritical Vulnerabilities in 3G/4G Modems
This report is the continuation of “#root via SMS”, a research made by the SCADA Strangelove team in 2014. It was devoted...
-

 231Incidents
231IncidentsGCHQ admits for the first time to ‘persistent’ hacking in the UK and abroad
The UK’s digital spy agency, GCHQ, has admitted for the first time in court that it hacks computers, smartphones, and networks in the...
-
 202Vulnerabilities
202VulnerabilitiesAdvantech ICS Gear Still Vulnerable to Shellshock, Heartbleed
Twice in the past year, security researchers have found and reported critical vulnerabilities in Modbus gateways built by Advantech that are used...
-
 273Cyber Crime
273Cyber CrimeScammers Running Phishing Scam with Tennessee Government Email ID
It is easy to hack a domain and set up scams for visitors but using a government email address to run a...
-

 264Cyber Crime
264Cyber CrimeScammers Threatening Users with Apple ID Suspension Phishing Scam
New day, new phishing attack! This time, it’s the Apple id which has been used by the attackers to steal from the...
-

 280Cyber Crime
280Cyber CrimeHackers Behind ProtonMail Attacks Now Targeting Greek Banks for Bitcoins
A hacking group (Armada Collective) which was previously held responsible for launching DDoS attacks on ProtonMail is back and this time targeting...
-

 285News
285NewsAnonymous Hacks Thailand Police Server Against Internet Censorship
Thailand police servers are the latest in the online breaches — This breach is a part of the campaign (#OpSingleGateway) launched by...
-

 98Data Security
98Data SecurityMicrosoft’s enterprise security software now offers PUA protection
Microsoft has started to offer potentially unwanted application (PUA) protection in its anti-malware products for enterprise firms. The news means that businesses...
-

 209Vulnerabilities
209VulnerabilitiesCritical Medical Equipment Vulnerable to LDAP and SQL Injection Attacks
Attackers can bypass authentication and access patient data. CERT/CC sounded the alarm on users of the Cardio Server ECG Management System, a broad-scope...
-
 345How To
345How ToFind Problems With Your Wi-Fi Connection Using Ofcom Wi-Fi Checker App
Short Bytes: Facing problems with your broadband connection is a common headache that most people struggle with. The UK telecom regulator Ofcom...
-
 270Hacked
270HackedThis Is The New Shocking Plan Of Anonymous To Mock ISIS Online
Short Bytes: Anonymous is planning to ‘celebrate’ December 11 as an ‘anti-ISIS day of rage’. The hacktivist collective is planning to fill...
-

 99Incidents
99IncidentsAustralia Bureau of Meteorology ‘hacked’
China is being blamed for a major cyber attack on the computers at the Bureau of Meteorology, which has compromised sensitive systems...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




