Featured News
-
 93Cyber Crime
93Cyber CrimePolice arrest couple suspected of running malware encryption service
British police arrested a man and a woman earlier this week, suspected of operating a website which offered services to online criminals...
-
 125Vulnerabilities
125VulnerabilitiesVPN Vulnerability “Port Fail” Reveals User’s Real IP Address
Attackers can unmask users hidden under a VPN connection. A vulnerability into how VPN providers deal with port forwarding exposes the real IP...
-

 185Geek
185GeekJava 9 is Coming – Release Dates and Major Features
Short bytes: General availability of Java 9 is announced by Oracle and it is coming on Sep 22nd, 2016. The major feature in...
-

 103Incidents
103IncidentsISIS: Ghost Sec, Anonymous hack Islamic State website
IT’S enough to make Islamic State sit up and take notice, or at the very least get a little hot under the...
-
 105Incidents
105IncidentsHTTPSohopeless: 26,000 Telstra Cisco boxen open to device hijacking
Embedded device mayhem as rivals share keys. More than 26,000 Cisco devices sold by Australia’s dominant telco Telstra are open to hijacking...
-
 109Vulnerabilities
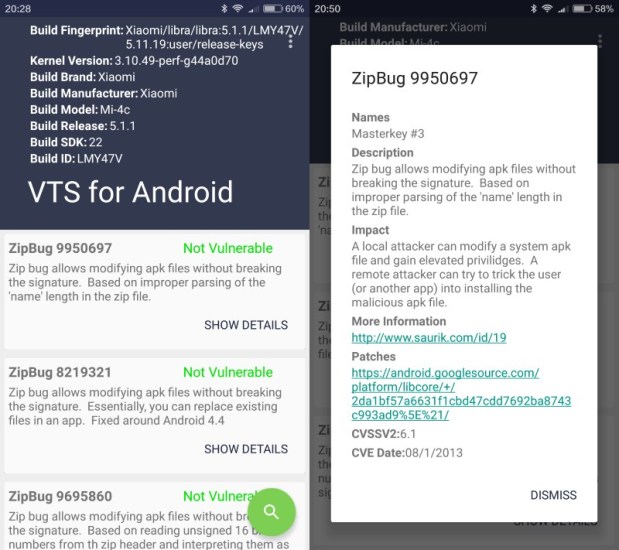
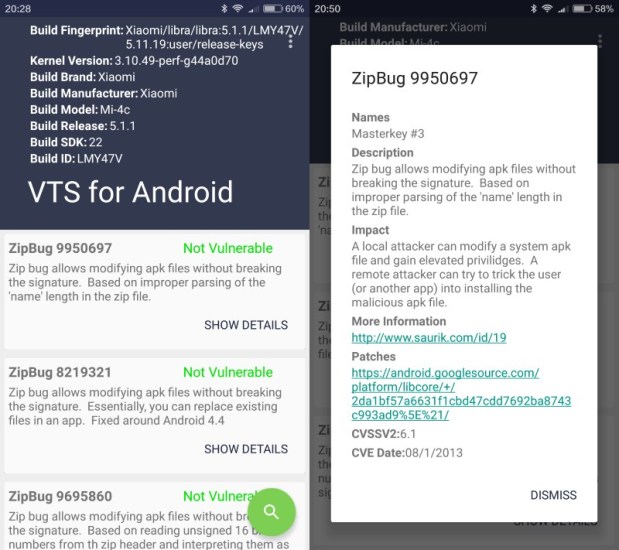
109VulnerabilitiesVTS scans Android devices for publicly-known vulnerabilities
Vulnerability Test Suite (VTS) is a free application for Android that scans devices running the operating system for publicly-disclosed vulnerabilities. Publicly-disclosed vulnerabilities...
-

 85Data Security
85Data SecurityHackers can hijack Wi-Fi Hello Barbie to spy on your children
Security researcher warns hackers could steal personal information and turn the microphone of the doll into a surveillance device. Mattel’s latest Wi-Fi...
-

 501How To
501How ToHow To Find The WiFi Password Of Your Current Network
Short bytes: There are different ways to retrieve the WiFi password of the network that you are connected to. Out of these,...
-

 318News
318NewsAnonymous Hacks ISIS Website, Defaces it with Viagra Ad
Just a week after the news of ISIS moving their online operations to the dark web, one of their main websites has...
-

 138News
138NewsPossible Breach, Amazon Sending Password Resetting Emails To Customers
On Tuesday, Amazon started sending out emails to its users asking for a quick password reset, the reason is a possible breach...
-

 99News
99NewsWhopping 1.2 Billion Credentials Leaked By Russian Hackers: FBI
According to an official document from the FBI, a Russian gang has been involved in a breach of 1.2 billion login credentials....
-

 288Hacked
288HackedAnonymous Hacks ISIS Darknet Website, Trolls By Replacing It With Viagra Ads
Short Bytes: Anonymous hacktivist group has just hacked an ISIS propaganda website on the dark web. Trolling ISIS and its supporters, the...
-

 169Data Security
169Data SecurityDRIDEX Spam Runs Resurface Against US Targets
DRIDEX is steadily regaining its footing in the US just over a month after its takedown orchestrated by US and UK law enforcement...
-
 71Data Security
71Data SecurityLazy IoT, router makers reuse skeleton keys over and over in thousands of devices – new study
SSH logins, server-side HTTPS certs baked in firmware. It’s what we all assumed, but quietly hoped wasn’t quite this bad. Lazy makers...
-

 173Incidents
173IncidentsCriminals Steal $4 Million In Cash With Novel ‘Reverse ATM’ Attack
Over the last year, criminals in Russia found a way to steal 252 million Rubles ($3.8 million) from five unnamed banks, using a...
-
 174Data Security
174Data SecurityNUCLEAR EXPLOIT KIT SPREADING CRYPTOWALL 4.0 RANSOMWARE
In short order, the newest version of Cryptowall has begun showing up in exploit kits. The SANS Internet Storm Center said on...
-

 296Data Security
296Data SecurityHackers Use Malware To Steal Cisco, IBM and Oracle Certification Manager
A certification tracking system (Credential Manager System) used by companies like Cisco, F5, IBM and Oracle has faced a data breach and...
-

 207Reviews
207ReviewsElephone P6000 Pro Review: A Budget Smartphone With High-End Specifications
Short Bytes: Budget smartphones are a very interesting smartphone segment where a customer looks for tons of features for a not-so-high price. As...
-

 175Kids Online
175Kids Online4 top security tips for parents
This introductory guide to online safety offers parents some useful security tips on how to protect their children.
-

 172Malware
172MalwareRansomware on Your TV, Get Ready, It’s Coming
A PoC shows the future dangers for smart TV sets.Many cyber-security vendors view ransomware as 2016’s biggest threat, and to help drive...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




