Featured News
-

 212Malware
212MalwareRelentless Sofacy APT Attacks Armed With Zero Days, New Backdoors
A new analysis of the Sofacy APT gang, a Russian-speaking group carrying out targeted attacks against military and government offices for close...
-

 186Tricks & How To's
186Tricks & How To'sSwitch your computer into Iron Man’s J.A.R.V.I.S
JARVIS is Iron Man’s personal assistant. With the help of a few windows utilities we can create our own JARVIS system. ...
-

 134Data Security
134Data SecurityHow to Hack TOR Hidden Services
A lot of people think that TOR services are unhackable because they are on a “secure environment”, but the truth is that...
-

 170Incidents
170IncidentsVariety Jones, Alleged Silk Road Mentor, Arrested in Thailand
MORE THAN TWO years after Ross Ulbricht was arrested in a San Francisco and accused of creating and running the Dark Web...
-

 223Cyber Crime
223Cyber CrimeChinese Group ‘Admin338’ Use DropBox To Deliver Their Payload
FireEye Threat Intelligence analysts have discovered a new phishing attack carried by a Chinese group using legitimate service like dropbox. Analysts found...
-
 166Lists
166ListsApple Named The Most Innovative Company In The World
Short Bytes: The Boston Consulting Group has released its 10th edition of the top 50 most innovative companies in the world. The list...
-

 208News
208NewsWetherspoon Pub Chain Faces Massive Data Breach
J D Wetherspoon, a famous pub chain in Ireland and the UK has announced that they’ve faced a massive data breach when...
-

 297Geek
297GeekLatest Facebook Phishing Scam Targets Video Users
The latest Facebook scam asks users to download a video player — The price for this player is your login credentials. Facebook...
-

 224Data Security
224Data SecurityResearchers Found Another Malware Targeting Linux Users
Linux is considered as one of the most secure operating systems — However, there’s a trojan attacking specifically those on Linux. Linux...
-

 253Kids Online
253Kids OnlineHow parents can assess the suitability of apps for their kids
Confused about being able to assess the suitability of apps for your children? This handy features highlights some of the key things...
-

 241Lists
241ListsGoogle Tells This Year’s Most Popular Movies, Books, Music, TV Shows On Android
Short Bytes: Just like every year, Google has just released its annual End Of The Year lists. This list contains 2015’s top...
-

 275News
275NewsHacker Breaches UAE Bank Server, Demands $3m in Ransom
A Sharjah-based Investbank has been asked for ransom by a hacker who breached into bank’s database and has threatened the bank if...
-
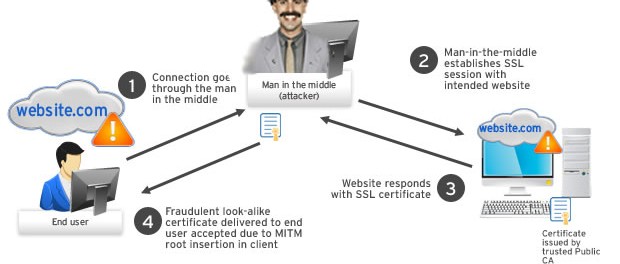
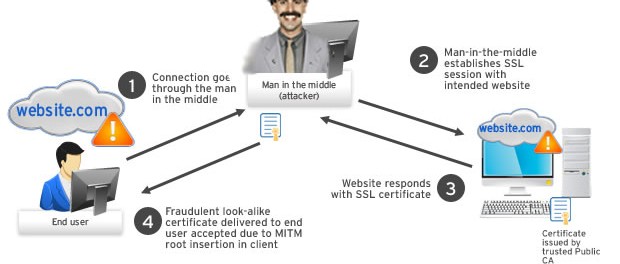 172Data Security
172Data SecurityKazakhstan will force its citizens to install internet backdoors
The poorly thought-out and crude surveillance technique could have a devastating effect on the country’s internet security. In less than a month,...
-
 289Geek
289GeekTop Programming Languages That Generate Most Software Security Bugs
Short Bytes: In the past, time and again, people have called the scripting languages a root cause of software vulnerability and the latest...
-

 222Data Security
222Data SecurityNew ransomware campaign pilfers passwords before encrypting gigabytes of data
Surreptitious attacks often prey on people visiting legitimate sites. A new wave of crypto ransomware is hitting Windows users courtesy of poorly...
-
 320Data Security
320Data SecurityCountless Adult Websites Attacked by Large-scale Malvertising Campaign
Cyber criminals have turned their attention towards x-rated sites and are using their most favorite tool- malvertising. Malvertising is short-term used for...
-

 112Incidents
112IncidentsPonmocup, never underestimate a botnet that infected 15 million PCs
Ponmocup is one of the oldest botnet that infected more than 15 million machines across the years, but many experts still ignore...
-

 253Data Security
253Data SecurityHack Remote Windows PC using The Backdoor factory with Metasploit
The goal of BDF is to patch executable binaries with user desired shellcode and continue normal execution of the prepatched state. First...
-

 110Incidents
110IncidentsJD Wetherspoon pub chain warns customers of ‘hack’
Pub chain JD Wetherspoon says card data of 100 customers has been stolen from a database after it was hacked. “Very limited”...
-
 113Incidents
113IncidentsHacker Leaks Customer Data After a United Arab Emirates Bank Fails to Pay Ransom
A HACKER WHO broke into a large bank in the United Arab Emirates made good on his threat to release customer data...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




