Featured News
-

 533Banking
533BankingOnline banking on‑the‑move? For most it’s a no‑go
What environment do you consider the safest for online banking? Would you make your financial transactions solely in the safety of your...
-

 110Incidents
110IncidentsOn China’s fringes, cyber spies raise their game
By Clare Baldwin, James Pomfret and Jeremy Wagstaff HONG KONG/SINGAPORE (Reuters) – Almost a year after students ended pro-democracy street protests in...
-

 107Incidents
107IncidentsAnonymous Takes Down Five Government Websites in Iceland to Protest Whale Hunting
Group also goes after the website of a whale hunting company Online activists associated with Anonymous took down five websites belonging to...
-
 111Incidents
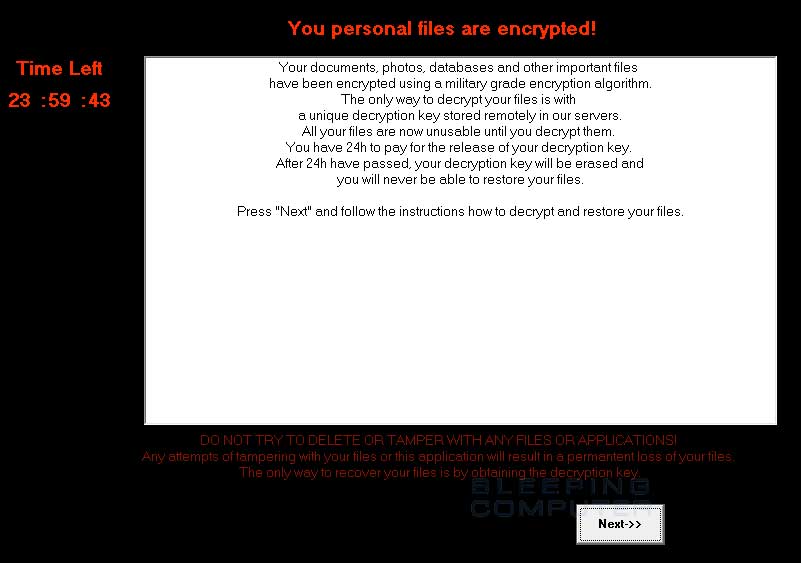
111IncidentsDecryptorMax Ransomware Decrypted, No Need to Pay the Ransom
Emsisoft researchers creates decryption tool.Fabian Wosar of Emisoft has created a tool capable of decoding files encrypted by the DecryptorMax ransomware, also...
-

 173Hacked
173HackedOne of the Only Publicly Known Anonymous Hacker Tells How Anonymous Fights ISIS
Short Bytes: Only very few members of the hacktivist collective Anonymous have been publicly identified. One such person is Gregg Housh, who recently...
-

 270News
270NewsAnonymous Crushes Almost Every Iceland Govt Site Against Whale Slaughter
Anonymous kicked started the operation #OpWhales and shut down almost all the Iceland government websites for about 13 hours as a protest against...
-

 270Hacked
270HackedThe “Secret ISIS Cybersecurity Guide” Was Just A Simple Security Guide In Arabic
Short Bytes: After the unfortunate Paris attacks, online media outlets like Wired, Yahoo News, and The Telegraph uncovered a ‘secret ISIS OPSEC...
-

 357Cyber Crime
357Cyber CrimeCouple Arrested For Providing Malware Encryption Service To Cyber Criminals
A couple (22-year-old man and a 22-year-old woman from Colchester, Essex) offering malware encryption services has been arrested by British police — The...
-

 193Data Security
193Data SecurityCritical Vulnerability in VPN Exposes User’s Real IP Address to Attacker
Researchers have found a vulnerability in VPN networks that could allow hackers or scammers to access real IPs of the users. Though,...
-

 217How To
217How ToHow To Capture Your Screen In Mac OS X In Simple Steps
Short Bytes: Mac OS X has a very nice way to capture full or partial screen without any software, but many users are...
-

 213Data Security
213Data SecurityRussians embrace Bitcoins, the West sticks with PayPal
One day, as you’re busy surfing on one of your favorite online stores, you stumble upon a pair of chic shades …...
-

 186Hacked
186HackedNSA Is Finally Ending Its Bulk Phone Syping Program From Tomorrow
Short Bytes: The NSA will end its bulk phone spying program by 11:59 p.m. EST Saturday (4:59 a.m. GMT Sunday). This step is...
-

 178Incidents
178IncidentsWindows Phone hacked! Unlock Lumia bootloader, get root access, flash custom ROMs
If you are the type of person that likes to tinker, Linux-based operating systems are for you. You would probably have many hours...
-
 116Vulnerabilities
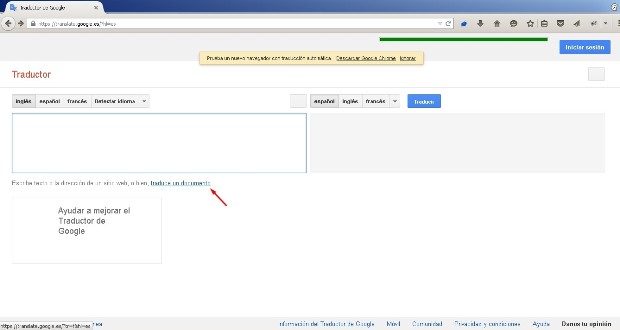
116VulnerabilitiesGoogle Translate Website Affected by XSS Bug, Google Says It’s OK
The bug is in the website’s “translate a document” feature.Madrid-based Francisco Javier Santiago Vazquez, a security auditor for Mnemo, has discovered a...
-

 99Incidents
99IncidentsWhen children are breached—inside the massive VTech hack
4.8 million records from a Hong Kong toy company were compromised. I suspect we’re all getting a little bit too conditioned to...
-

 290News
290NewsPro-ISIS Group Hacks Richland County Veterans Services Website
It seems that the Richland County, Wisconsin is the new victim of the pro-ISIS hackers as Team System DZ hacked three of...
-

 265Cyber Crime
265Cyber CrimeHackers Dropping Malware in Fake “terror alert” Emails
An email with a “terror alert” seems to be a new way of launching phishing attack and dropping malware from cyber criminals....
-

 142Hacked
142HackedChina Just Made These Anti-Terror Robots Armed With “Guns And Grenades”
Short Bytes: At the 2015 World Robot Conference in Beijing, a Chinese firm has unveiled three armed robots that are equipped with grenade...
-
 97Cyber Crime
97Cyber CrimePolice arrest couple suspected of running malware encryption service
British police arrested a man and a woman earlier this week, suspected of operating a website which offered services to online criminals...
-
 129Vulnerabilities
129VulnerabilitiesVPN Vulnerability “Port Fail” Reveals User’s Real IP Address
Attackers can unmask users hidden under a VPN connection. A vulnerability into how VPN providers deal with port forwarding exposes the real IP...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




