Featured News
-

 242News
242NewsThis Group Spies on ISIS Rather Than Exposing Twitter Handles
The readers know about Anonymous waging war against ISIS, but hardly anyone knows about a group which has been working quietly (well,...
-

 221Data Security
221Data SecurityAnti-NSA Phone Developers Vow to Keep Their Product Away From Terrorists
Silent Circle, the developer of the self-proclaimed NSA-proof smartphone has announced that it is making sure to distances itself from criminals and terrorists...
-

 270Password
270PasswordIs biometrics the future of secure payments?
Is the idea of biometrics as a secure payment system a fad, fiction or fact? This feature looks at whether DNA is...
-

 302Hacked
302HackedISIS Moving To The Dark Web To Escape Hackers And Spread Its Message
Short Bytes: In order to protect its online operations from security agencies and hackers, and to propel its propaganda, ISIS is looking...
-

 321News
321NewsISIS Releases Another Kill List of US Military and Security Officials
ISIS has unveiled list of U.S. officials who are on their target — The list includes names of both current and former...
-

 260Hacked
260HackedHow Belgians Trolled And Confused ISIS Terror Threats With Cat Pictures On Twitter
Short Bytes: Belgian people have found a new weapon to deal with the terror threats in the form of cat pics. As...
-

 96Data Security
96Data Security‘Spying’ on Islamic State instead of hacking them
In the wake of the Paris attacks, the vigilante hacker group Anonymous has declared war on so-called Islamic State using the internet...
-

 182Data Security
182Data SecurityHere’s the ISIS OPSEC Manual Used to Train Recruits About Cyber-Security
ISIS hijacks Kuwait security firm’s OPSEC manual.Yesterday, various Twitter accounts were tweeting about an ISIS OPSEC manual describing the terrorist group’s cyber-security...
-
 181Data Security
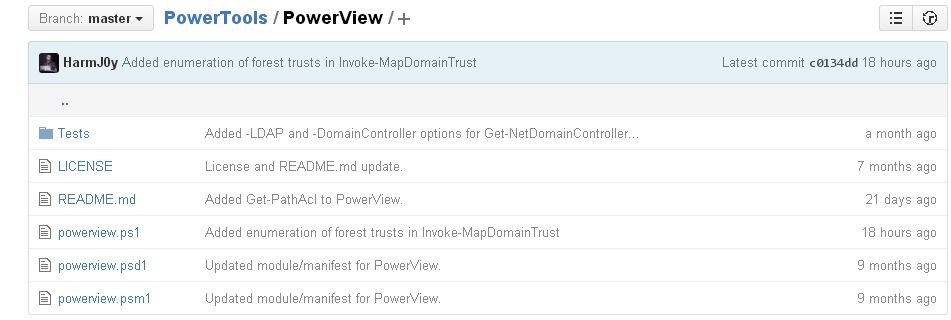
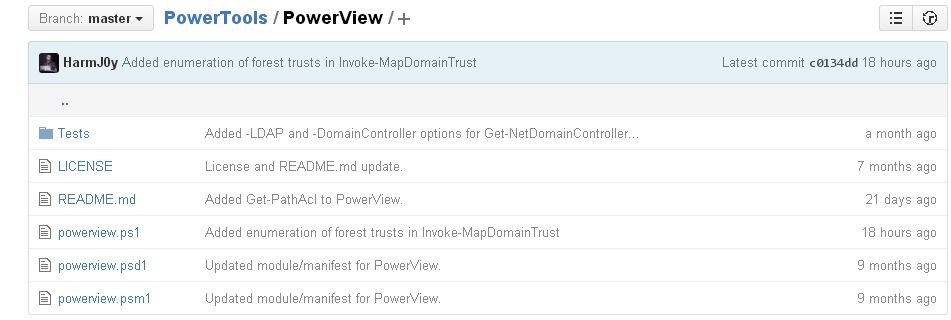
181Data SecurityHacking and exploiting Active Directory Permissions
PowerView is a PowerShell tool to achieve network information on Windows domains for cyber security services and ethical hacking training professionals. It...
-

 255Data Security
255Data SecurityResearchers say they’ve cracked the secret of the Sony Pictures hack
Log wipers, timestompers may have helped hackers stay quiet in terabyte raids. Damballa researchers Willis McDonald and Loucif Kharouni say the attackers...
-
 158Malware
158MalwareCryptInfinite or DecryptorMax Ransomware Decrypted
We have received a lot of reports about a new ransomware that we are calling CryptInfinite based on the Windows Registry key created by this ransomware....
-

 182News
182NewsHackers Target Starwood Hotels, Steal Credit Card Data Using Malware
Chain of hotels owned by Starwood Hotels & Resorts Worldwide properties faced a data breach earlier this year and hackers got access...
-
 178Hacked
178HackedISIS Hackers Post A “Wanted To Be Killed” List Of U.S. Officials
Short Bytes: The ISIS hackers, calling themselves the “Islamic State Cyber Army,” have used Twitter to post the names and addresses of...
-

 277Cyber Crime
277Cyber CrimeSmart eBay Scammer Tricks, Steals Identity of His Investigating Officer
Rohit Jawa, a 25-year-old man, was arrested in Cincinnati, Ohio on 15th June 2015 for scamming on eBay — He was accused...
-

 172Hacked
172HackedAnonymous Warns About Possible “Worldwide Attack By ISIS” Today (Updated)
Short Bytes: The Anonymous hacktivists have claimed that they have uncovered a secret Islamic State plan for a worldwide terror attack this Sunday....
-
 268News
268NewsAnonymous Has Shutdown 28,000+ ISIS’ Twitter Accounts Since OpParis Began
The online hacktivist Anonymous shut down 8824 Twitter accounts of ISIS members + followers in the first phase of OpParis — In...
-

 316News
316NewsSelf-Proclaimed Anonymous Hacktivists Predict Potential ISIS Terror Attacks
Someone is using Anonymous’s name to spread rumors about ISIS planning to target different events worldwide. A Pastebin post posted by someone claiming to have a...
-

 309Cyber Crime
309Cyber CrimeCrooks Hack World Bank SSL Certificate To Host PayPal Phishing Scam
Hackers have again attacked PayPal but this time by making a clone site that even had an SSL certificate of the World...
-

 310Data Security
310Data SecurityAnonymous Has Now Taken Down 20,000 ISIS Twitter Accounts, Promises to Go On
Hacking group remains as focused as one week ago Quite a lot has happened after Anonymous declared cyber-war on ISIS members last...
-

 105Data Security
105Data SecurityHow to Baffle Web Trackers by Obfuscating Your Movements Online
ONLINE AD NETWORKS and search engines love it when you surf around. Everything you do—every page you load, every query you type—helps...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




