Featured News
-
 116Vulnerabilities
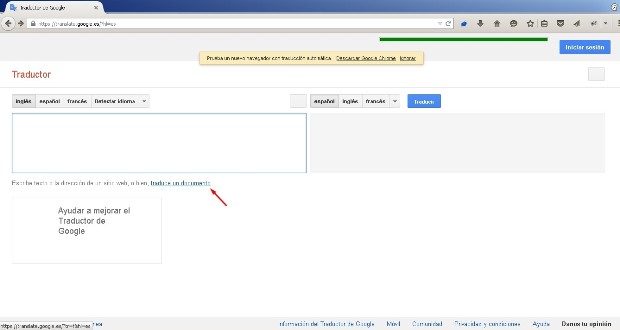
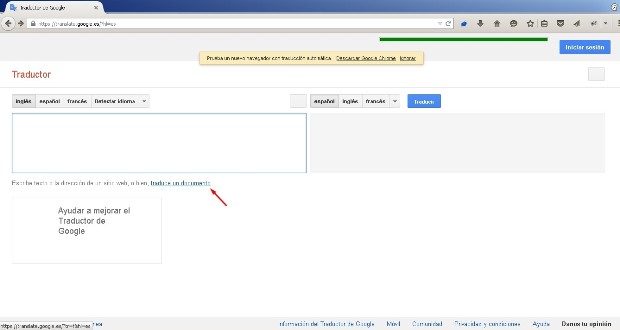
116VulnerabilitiesGoogle Translate Website Affected by XSS Bug, Google Says It’s OK
The bug is in the website’s “translate a document” feature.Madrid-based Francisco Javier Santiago Vazquez, a security auditor for Mnemo, has discovered a...
-

 99Incidents
99IncidentsWhen children are breached—inside the massive VTech hack
4.8 million records from a Hong Kong toy company were compromised. I suspect we’re all getting a little bit too conditioned to...
-

 291News
291NewsPro-ISIS Group Hacks Richland County Veterans Services Website
It seems that the Richland County, Wisconsin is the new victim of the pro-ISIS hackers as Team System DZ hacked three of...
-

 265Cyber Crime
265Cyber CrimeHackers Dropping Malware in Fake “terror alert” Emails
An email with a “terror alert” seems to be a new way of launching phishing attack and dropping malware from cyber criminals....
-

 142Hacked
142HackedChina Just Made These Anti-Terror Robots Armed With “Guns And Grenades”
Short Bytes: At the 2015 World Robot Conference in Beijing, a Chinese firm has unveiled three armed robots that are equipped with grenade...
-
 97Cyber Crime
97Cyber CrimePolice arrest couple suspected of running malware encryption service
British police arrested a man and a woman earlier this week, suspected of operating a website which offered services to online criminals...
-
 130Vulnerabilities
130VulnerabilitiesVPN Vulnerability “Port Fail” Reveals User’s Real IP Address
Attackers can unmask users hidden under a VPN connection. A vulnerability into how VPN providers deal with port forwarding exposes the real IP...
-

 188Geek
188GeekJava 9 is Coming – Release Dates and Major Features
Short bytes: General availability of Java 9 is announced by Oracle and it is coming on Sep 22nd, 2016. The major feature in...
-

 110Incidents
110IncidentsISIS: Ghost Sec, Anonymous hack Islamic State website
IT’S enough to make Islamic State sit up and take notice, or at the very least get a little hot under the...
-
 108Incidents
108IncidentsHTTPSohopeless: 26,000 Telstra Cisco boxen open to device hijacking
Embedded device mayhem as rivals share keys. More than 26,000 Cisco devices sold by Australia’s dominant telco Telstra are open to hijacking...
-
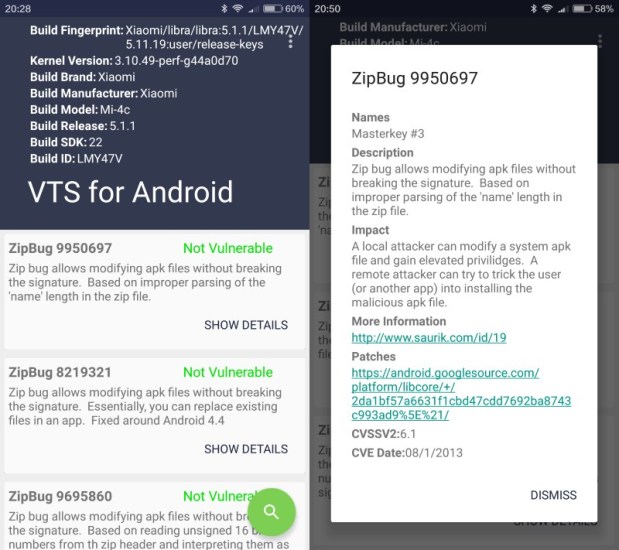
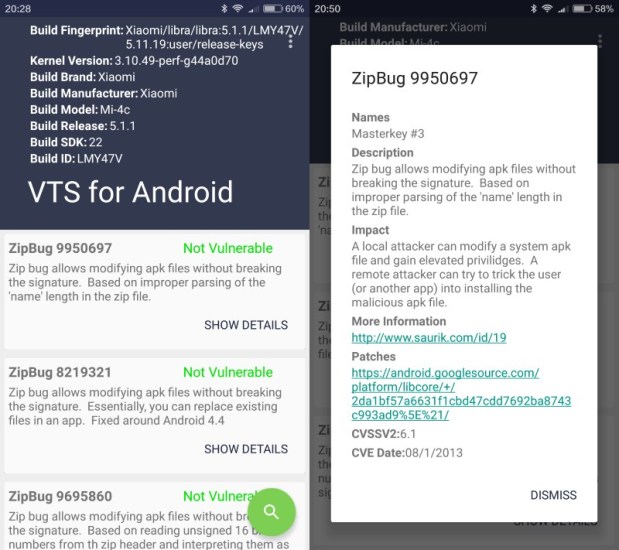 115Vulnerabilities
115VulnerabilitiesVTS scans Android devices for publicly-known vulnerabilities
Vulnerability Test Suite (VTS) is a free application for Android that scans devices running the operating system for publicly-disclosed vulnerabilities. Publicly-disclosed vulnerabilities...
-

 89Data Security
89Data SecurityHackers can hijack Wi-Fi Hello Barbie to spy on your children
Security researcher warns hackers could steal personal information and turn the microphone of the doll into a surveillance device. Mattel’s latest Wi-Fi...
-

 504How To
504How ToHow To Find The WiFi Password Of Your Current Network
Short bytes: There are different ways to retrieve the WiFi password of the network that you are connected to. Out of these,...
-

 324News
324NewsAnonymous Hacks ISIS Website, Defaces it with Viagra Ad
Just a week after the news of ISIS moving their online operations to the dark web, one of their main websites has...
-

 147News
147NewsPossible Breach, Amazon Sending Password Resetting Emails To Customers
On Tuesday, Amazon started sending out emails to its users asking for a quick password reset, the reason is a possible breach...
-

 103News
103NewsWhopping 1.2 Billion Credentials Leaked By Russian Hackers: FBI
According to an official document from the FBI, a Russian gang has been involved in a breach of 1.2 billion login credentials....
-

 295Hacked
295HackedAnonymous Hacks ISIS Darknet Website, Trolls By Replacing It With Viagra Ads
Short Bytes: Anonymous hacktivist group has just hacked an ISIS propaganda website on the dark web. Trolling ISIS and its supporters, the...
-

 173Data Security
173Data SecurityDRIDEX Spam Runs Resurface Against US Targets
DRIDEX is steadily regaining its footing in the US just over a month after its takedown orchestrated by US and UK law enforcement...
-
 73Data Security
73Data SecurityLazy IoT, router makers reuse skeleton keys over and over in thousands of devices – new study
SSH logins, server-side HTTPS certs baked in firmware. It’s what we all assumed, but quietly hoped wasn’t quite this bad. Lazy makers...
-

 175Incidents
175IncidentsCriminals Steal $4 Million In Cash With Novel ‘Reverse ATM’ Attack
Over the last year, criminals in Russia found a way to steal 252 million Rubles ($3.8 million) from five unnamed banks, using a...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




