Featured News
-

 188Geek
188GeekJava 9 is Coming – Release Dates and Major Features
Short bytes: General availability of Java 9 is announced by Oracle and it is coming on Sep 22nd, 2016. The major feature in...
-

 109Incidents
109IncidentsISIS: Ghost Sec, Anonymous hack Islamic State website
IT’S enough to make Islamic State sit up and take notice, or at the very least get a little hot under the...
-
 108Incidents
108IncidentsHTTPSohopeless: 26,000 Telstra Cisco boxen open to device hijacking
Embedded device mayhem as rivals share keys. More than 26,000 Cisco devices sold by Australia’s dominant telco Telstra are open to hijacking...
-
 112Vulnerabilities
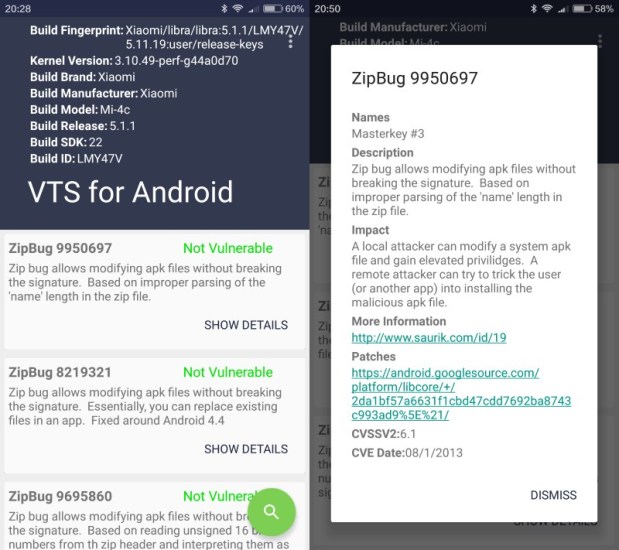
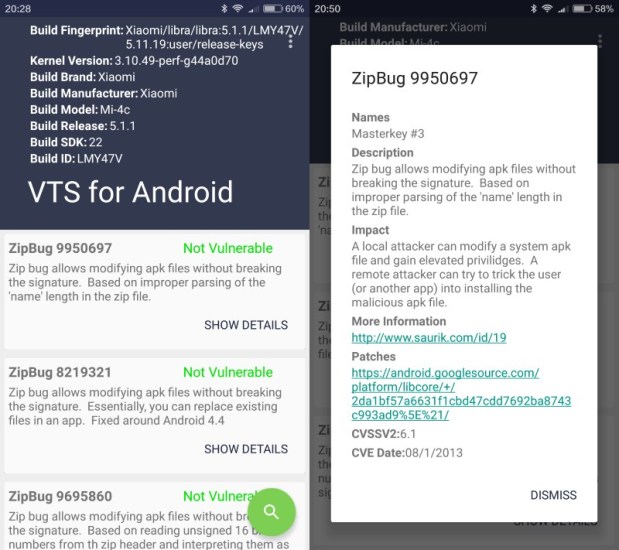
112VulnerabilitiesVTS scans Android devices for publicly-known vulnerabilities
Vulnerability Test Suite (VTS) is a free application for Android that scans devices running the operating system for publicly-disclosed vulnerabilities. Publicly-disclosed vulnerabilities...
-

 89Data Security
89Data SecurityHackers can hijack Wi-Fi Hello Barbie to spy on your children
Security researcher warns hackers could steal personal information and turn the microphone of the doll into a surveillance device. Mattel’s latest Wi-Fi...
-

 504How To
504How ToHow To Find The WiFi Password Of Your Current Network
Short bytes: There are different ways to retrieve the WiFi password of the network that you are connected to. Out of these,...
-

 324News
324NewsAnonymous Hacks ISIS Website, Defaces it with Viagra Ad
Just a week after the news of ISIS moving their online operations to the dark web, one of their main websites has...
-

 146News
146NewsPossible Breach, Amazon Sending Password Resetting Emails To Customers
On Tuesday, Amazon started sending out emails to its users asking for a quick password reset, the reason is a possible breach...
-

 102News
102NewsWhopping 1.2 Billion Credentials Leaked By Russian Hackers: FBI
According to an official document from the FBI, a Russian gang has been involved in a breach of 1.2 billion login credentials....
-

 295Hacked
295HackedAnonymous Hacks ISIS Darknet Website, Trolls By Replacing It With Viagra Ads
Short Bytes: Anonymous hacktivist group has just hacked an ISIS propaganda website on the dark web. Trolling ISIS and its supporters, the...
-

 173Data Security
173Data SecurityDRIDEX Spam Runs Resurface Against US Targets
DRIDEX is steadily regaining its footing in the US just over a month after its takedown orchestrated by US and UK law enforcement...
-
 73Data Security
73Data SecurityLazy IoT, router makers reuse skeleton keys over and over in thousands of devices – new study
SSH logins, server-side HTTPS certs baked in firmware. It’s what we all assumed, but quietly hoped wasn’t quite this bad. Lazy makers...
-

 175Incidents
175IncidentsCriminals Steal $4 Million In Cash With Novel ‘Reverse ATM’ Attack
Over the last year, criminals in Russia found a way to steal 252 million Rubles ($3.8 million) from five unnamed banks, using a...
-
 178Data Security
178Data SecurityNUCLEAR EXPLOIT KIT SPREADING CRYPTOWALL 4.0 RANSOMWARE
In short order, the newest version of Cryptowall has begun showing up in exploit kits. The SANS Internet Storm Center said on...
-

 303Data Security
303Data SecurityHackers Use Malware To Steal Cisco, IBM and Oracle Certification Manager
A certification tracking system (Credential Manager System) used by companies like Cisco, F5, IBM and Oracle has faced a data breach and...
-

 214Reviews
214ReviewsElephone P6000 Pro Review: A Budget Smartphone With High-End Specifications
Short Bytes: Budget smartphones are a very interesting smartphone segment where a customer looks for tons of features for a not-so-high price. As...
-

 177Kids Online
177Kids Online4 top security tips for parents
This introductory guide to online safety offers parents some useful security tips on how to protect their children.
-

 178Malware
178MalwareRansomware on Your TV, Get Ready, It’s Coming
A PoC shows the future dangers for smart TV sets.Many cyber-security vendors view ransomware as 2016’s biggest threat, and to help drive...
-

 254Geek
254GeekA Lazy Programmer Wrote These “Hacker Scripts” To Secretly Get His Jobs Done
Short Bytes: Sometimes it takes too much effort to fetch a cup of coffee, replying a couple emails, and some other small...
-
 210Malware
210MalwareGNU.org Website Says Microsoft’s Software Is Malware
Both Amazon and Apple are in the same boat.GNU.org has a category on its website named “Philosophy of the GNU Project” where...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




