Featured News
-
 178Data Security
178Data SecurityNUCLEAR EXPLOIT KIT SPREADING CRYPTOWALL 4.0 RANSOMWARE
In short order, the newest version of Cryptowall has begun showing up in exploit kits. The SANS Internet Storm Center said on...
-

 304Data Security
304Data SecurityHackers Use Malware To Steal Cisco, IBM and Oracle Certification Manager
A certification tracking system (Credential Manager System) used by companies like Cisco, F5, IBM and Oracle has faced a data breach and...
-

 215Reviews
215ReviewsElephone P6000 Pro Review: A Budget Smartphone With High-End Specifications
Short Bytes: Budget smartphones are a very interesting smartphone segment where a customer looks for tons of features for a not-so-high price. As...
-

 177Kids Online
177Kids Online4 top security tips for parents
This introductory guide to online safety offers parents some useful security tips on how to protect their children.
-

 178Malware
178MalwareRansomware on Your TV, Get Ready, It’s Coming
A PoC shows the future dangers for smart TV sets.Many cyber-security vendors view ransomware as 2016’s biggest threat, and to help drive...
-

 254Geek
254GeekA Lazy Programmer Wrote These “Hacker Scripts” To Secretly Get His Jobs Done
Short Bytes: Sometimes it takes too much effort to fetch a cup of coffee, replying a couple emails, and some other small...
-
 211Malware
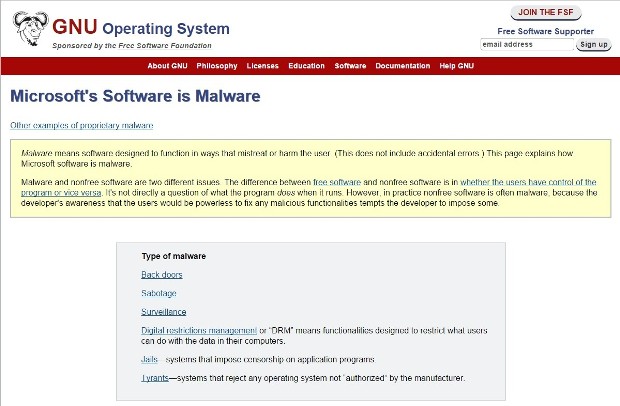
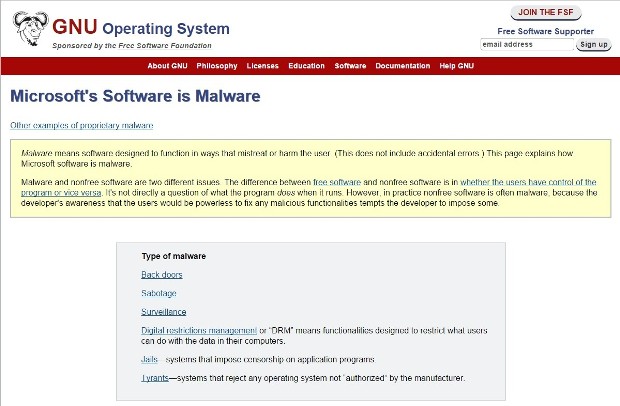
211MalwareGNU.org Website Says Microsoft’s Software Is Malware
Both Amazon and Apple are in the same boat.GNU.org has a category on its website named “Philosophy of the GNU Project” where...
-

 164Data Security
164Data SecurityHow easy is it to hack a cellular network
It was last year when a new method of attack on cellular networks was discovered. It requires neither costly radio scanners nor...
-

 177Vulnerabilities
177VulnerabilitiesUnited Airlines Slow to Patch Mobile App Vulnerability
A vulnerability reported to United Airlines that could have been exploited to manipulate flight reservations and customer data sat unpatched for almost...
-
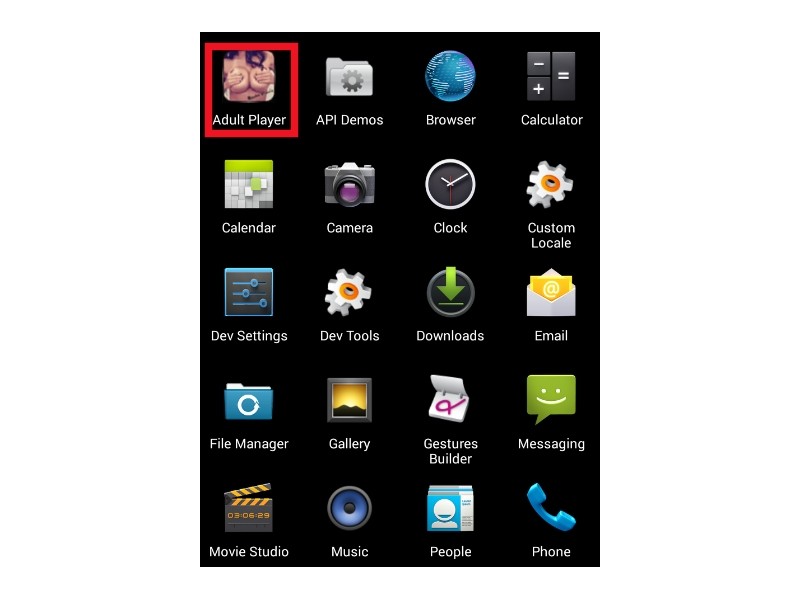
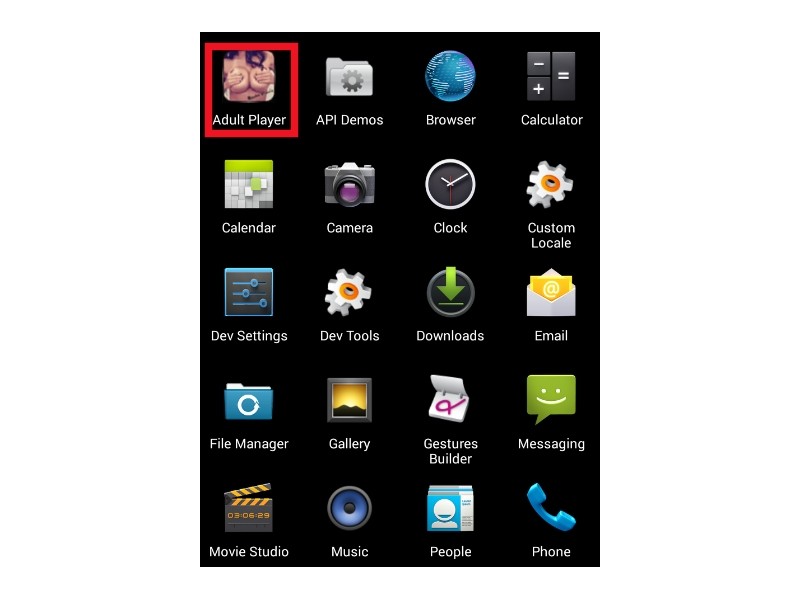 96Malware
96MalwareAdult Apps on Android Might Be Harboring Ransomware, Scareware and SMS Trojans
The trend of using adult-themed Android apps to deliver malware is ramping up, as Zscaler security researchers are warning about two new...
-

 106Data Security
106Data SecurityA $10 Tool Can Guess (And Steal) Your Next Credit Card Number
WHEN SAMY KAMKAR lost his American Express card last August and received its replacement in the mail, something about the final digits...
-

 267News
267NewsArmenian Group Hacks Azerbaijan Central Bank, Leaks A Trove of Data
The cyber war between Armenians and Azerbaijani hackers is never ending — Like in this recent cyber attack in which the Armenian...
-

 213Cyber Events
213Cyber EventsTurkish Attackers Shut Down Russian Central Bank Website
Turkish hackers just took down the official website of Russian Central Bank amid tension near Syrian-Turkey border. A group of Turkish hacktivist...
-

 250Geek
250GeekChina Working on Its Own Secure Smartphone for Government Officials
Short Read: China is working on developing its own smartphone for government officials to avoid snooping from the enemy side. China, one...
-

 331Geek
331GeekGoogle Appoints VMware co-founder to Charge Up Cloud Ventures
Diane Greene, well-known tech expert and co-founder of VMware, is now senior the vice president for Google’s enterprise businesses. The New York...
-

 216Geek
216GeekDell, The Latest in The List of Pre-Rooted PC and Laptop Sellers
Dell is found to be shipping laptops having eDellRoot certificate installed by default. The certificate is through trusted but has all the...
-

 79Malware
79MalwareNew Dridex campaign achieves high infection ratio in European countries
When discussing banking trojans these days, Dridex is the one that everybody seems to be talking about the most. This trojan has...
-

 122Cyber Crime
122Cyber CrimeYou are 6 security steps away from Black Friday brilliance
Black Friday and Cyber Monday promise to offer some fantastic deals at low prices. But it’s also a time of year when...
-
 410Hacked
410HackedHere’s the Best Antivirus Software for Windows 7, 8.1, and 10 PCs, According to Tests
Short Bytes: Reputed antivirus testing house AV-Test has released the latest results of the best antivirus software for Windows. Take a look...
-

 283Hacked
283HackedAnonymous Now Plans to Start Offensive Hacking To Kill ISIS Online
Short Bytes: After facing backlash over the “wildly inaccurate” accounts reported to Twitter, Anonymous has decided to switch to their area of...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




