Featured News
-

 163Data Security
163Data SecurityHow easy is it to hack a cellular network
It was last year when a new method of attack on cellular networks was discovered. It requires neither costly radio scanners nor...
-

 177Vulnerabilities
177VulnerabilitiesUnited Airlines Slow to Patch Mobile App Vulnerability
A vulnerability reported to United Airlines that could have been exploited to manipulate flight reservations and customer data sat unpatched for almost...
-
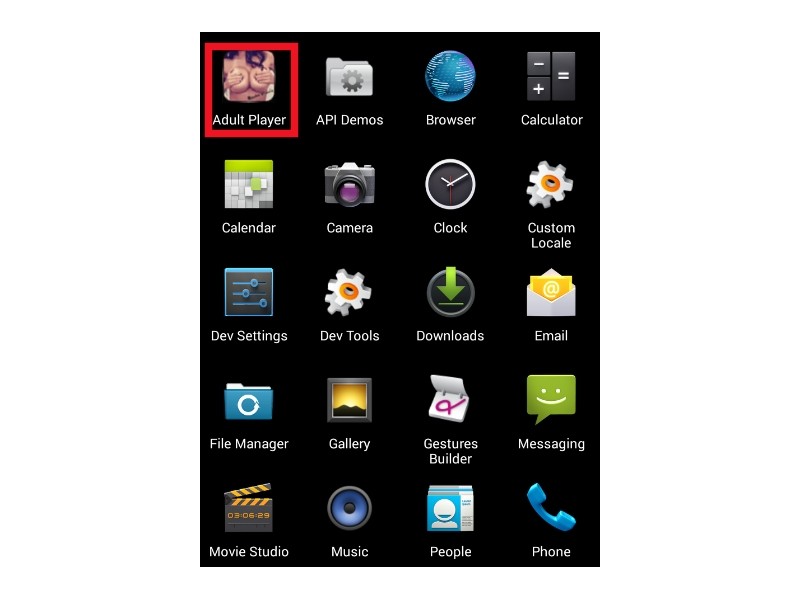
 96Malware
96MalwareAdult Apps on Android Might Be Harboring Ransomware, Scareware and SMS Trojans
The trend of using adult-themed Android apps to deliver malware is ramping up, as Zscaler security researchers are warning about two new...
-

 105Data Security
105Data SecurityA $10 Tool Can Guess (And Steal) Your Next Credit Card Number
WHEN SAMY KAMKAR lost his American Express card last August and received its replacement in the mail, something about the final digits...
-

 265News
265NewsArmenian Group Hacks Azerbaijan Central Bank, Leaks A Trove of Data
The cyber war between Armenians and Azerbaijani hackers is never ending — Like in this recent cyber attack in which the Armenian...
-

 212Cyber Events
212Cyber EventsTurkish Attackers Shut Down Russian Central Bank Website
Turkish hackers just took down the official website of Russian Central Bank amid tension near Syrian-Turkey border. A group of Turkish hacktivist...
-

 249Geek
249GeekChina Working on Its Own Secure Smartphone for Government Officials
Short Read: China is working on developing its own smartphone for government officials to avoid snooping from the enemy side. China, one...
-

 331Geek
331GeekGoogle Appoints VMware co-founder to Charge Up Cloud Ventures
Diane Greene, well-known tech expert and co-founder of VMware, is now senior the vice president for Google’s enterprise businesses. The New York...
-

 216Geek
216GeekDell, The Latest in The List of Pre-Rooted PC and Laptop Sellers
Dell is found to be shipping laptops having eDellRoot certificate installed by default. The certificate is through trusted but has all the...
-

 78Malware
78MalwareNew Dridex campaign achieves high infection ratio in European countries
When discussing banking trojans these days, Dridex is the one that everybody seems to be talking about the most. This trojan has...
-

 122Cyber Crime
122Cyber CrimeYou are 6 security steps away from Black Friday brilliance
Black Friday and Cyber Monday promise to offer some fantastic deals at low prices. But it’s also a time of year when...
-
 409Hacked
409HackedHere’s the Best Antivirus Software for Windows 7, 8.1, and 10 PCs, According to Tests
Short Bytes: Reputed antivirus testing house AV-Test has released the latest results of the best antivirus software for Windows. Take a look...
-

 283Hacked
283HackedAnonymous Now Plans to Start Offensive Hacking To Kill ISIS Online
Short Bytes: After facing backlash over the “wildly inaccurate” accounts reported to Twitter, Anonymous has decided to switch to their area of...
-

 93Malware
93MalwareGlassRAT Zero-Detection Trojan Targets Chinese Nationals
A previously undetectable remote administration tool has been uncovered, dubbed “GlassRAT” The zero-detection Trojan appears to have operated stealthily for three years,...
-

 169Data Security
169Data SecurityCatching Up With The ‘EITest’ Compromise, A Year Later
We are seeing dozens of WordPress sites compromised recently with the same malicious code redirecting to the Angler exploit kit. The attack involves conditionally...
-

 169Data Security
169Data SecurityDocuments demonstrate NSA continued mass surveillance
Newly disclosed documents show that the NSA had found a way to continue spying on American citizens’ email traffic from overseas. The...
-
 186Data Security
186Data SecurityResearchers Find Multiple Chrome Extensions Secretly Tracking Users
Hidden analytics code tracks everything users do, EVERYTHING Analytics code deeply hidden in popular Google Chrome extensions is being used to track...
-
 195Data Security
195Data SecurityDell does a Superfish, ships PCs with easily cloneable root certificates
Root certificate debacle that hit Lenovo now visits the House of Dell. In a move eerily similar to the Superfish debacle that...
-

 245News
245NewsThis Group Spies on ISIS Rather Than Exposing Twitter Handles
The readers know about Anonymous waging war against ISIS, but hardly anyone knows about a group which has been working quietly (well,...
-

 227Data Security
227Data SecurityAnti-NSA Phone Developers Vow to Keep Their Product Away From Terrorists
Silent Circle, the developer of the self-proclaimed NSA-proof smartphone has announced that it is making sure to distances itself from criminals and terrorists...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




