Featured News
-

 313Cyber Crime
313Cyber CrimeCrooks Hack World Bank SSL Certificate To Host PayPal Phishing Scam
Hackers have again attacked PayPal but this time by making a clone site that even had an SSL certificate of the World...
-

 312Data Security
312Data SecurityAnonymous Has Now Taken Down 20,000 ISIS Twitter Accounts, Promises to Go On
Hacking group remains as focused as one week ago Quite a lot has happened after Anonymous declared cyber-war on ISIS members last...
-

 109Data Security
109Data SecurityHow to Baffle Web Trackers by Obfuscating Your Movements Online
ONLINE AD NETWORKS and search engines love it when you surf around. Everything you do—every page you load, every query you type—helps...
-
 213Vulnerabilities
213VulnerabilitiesVMware Patches Pesky XXE Bug in Flex BlazeDS
VMware has patched an information disclosure vulnerability affecting a number of its products that use Flex BlazeDS. The original vulnerability was discovered...
-

 207Incidents
207IncidentseBay Scammer Steals Identity of the Police Officer Investigating His Case
Rohit Jawa fools officer into revealing personal details. Police officers investigating an eBay scammer must have been very surprised when the criminal, in...
-

 210Hacked
210HackedIndian Hackers Attack Pakistan Government and Defense Websites
Short Bytes: In the past, Pakistani and India cyber hackers have been targeting each other by hacking different government websites. In the latest...
-
 186News
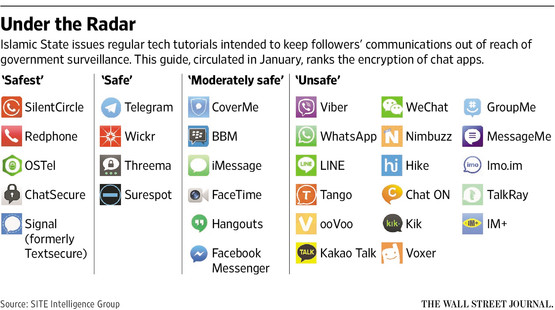
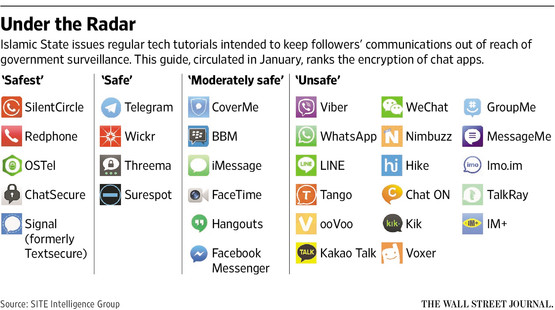
186NewsISIS issues anti-hacking guidelines for its online supports after Anonymous threats
After calling Anonymous ‘Idiots’ ISIS issues guidelines to its cronies to protect from hackers like Anonymous The Islamic State militant ISIL who...
-

 151Incidents
151IncidentsSome Starwood Hotels payment systems hit by malware
Starwood Hotels & Resorts Worldwide Inc said payment systems at 54 of its hotels in North America had been infected with a...
-
 166Geek
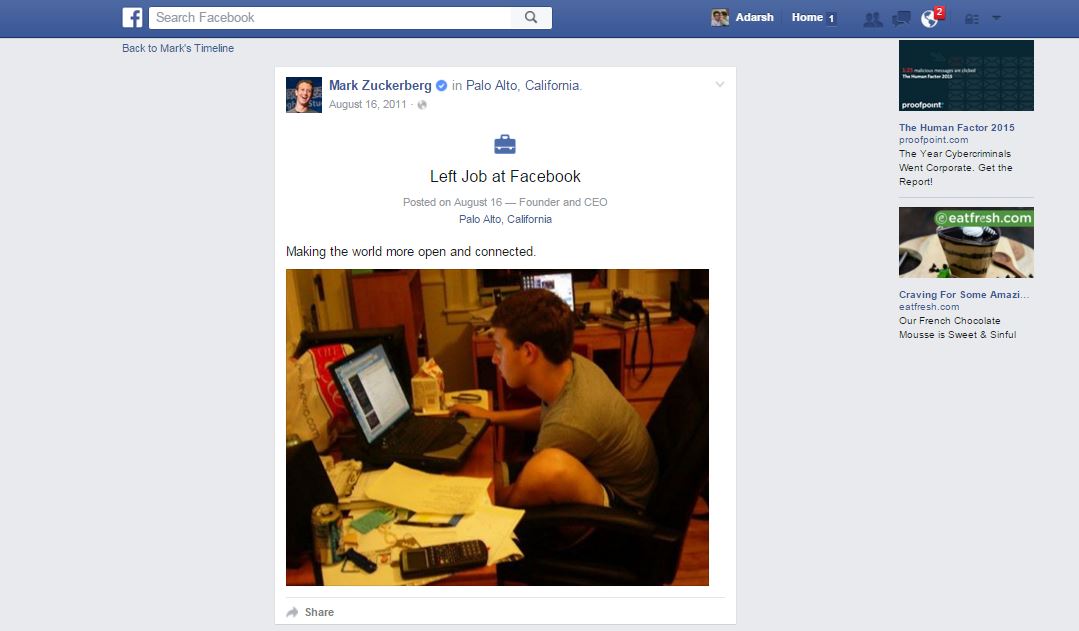
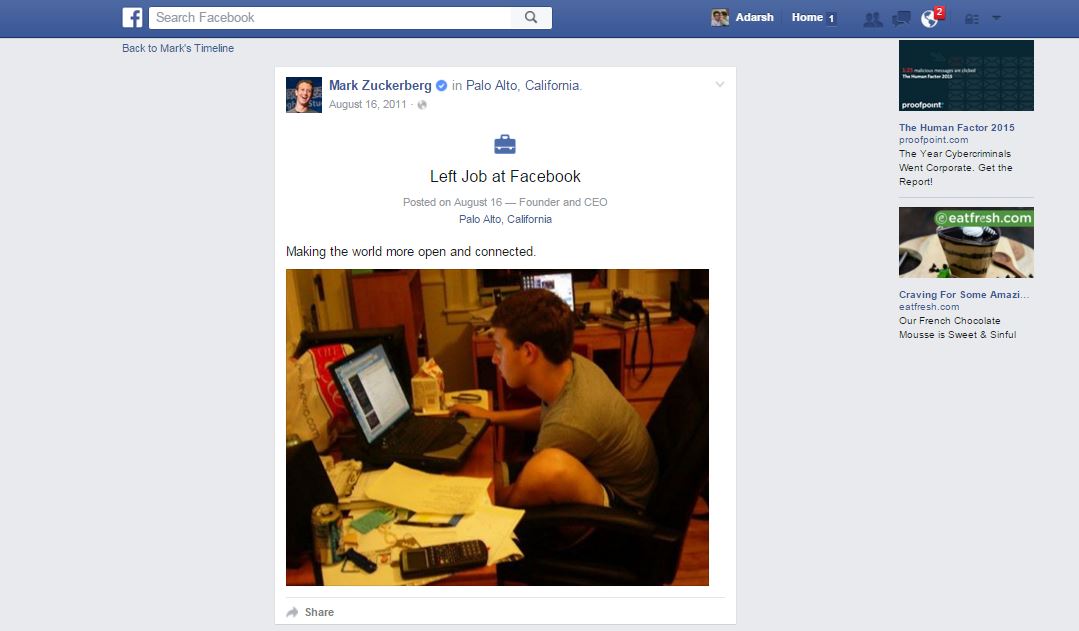
166GeekResearcher Founds Bug That Made Mark Zuckerburg Quit his job at Facebook
A Facebook bug is not a surprising thing to know about but Zuckerberg quitting his job as the Facebook’s CEO is not...
-
 101Cyber Crime
101Cyber CrimeCourt Charges Kid with Bomb Threats and DDoS Attacks
A 15-year-old guy in Plymouth has been arrested by British police on the charges of launching DDoS attacks and for sending false bomb...
-
 194Vulnerabilities
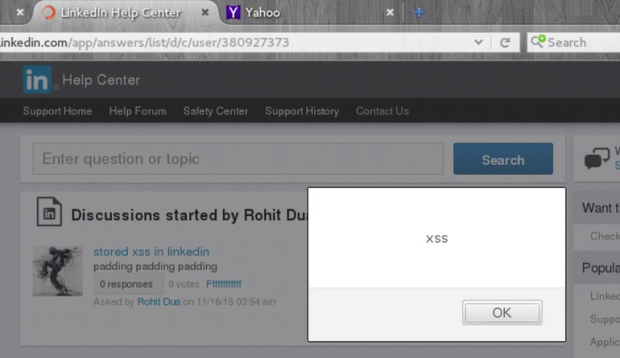
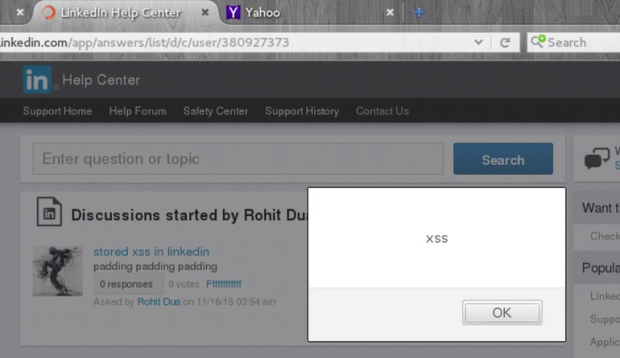
194VulnerabilitiesLinkedIn patches serious persistent XSS vulnerability
Developers at LinkedIn fixed a persistent cross site scripting vulnerability in the social network this week that could have been exploited to...
-

 143Data Security
143Data Security600,000 cable modems have an easy to pop backdoor in a backdoor
Brazilian whacks Arris for easy-t-o-guess default password, fix promised fast. Security bod Bernardo Rodrigues has found a backdoor-within-a-backdoor affecting some 600,000 Arris...
-

 215Hacked
215HackedThis Coder Forces Careless Twitter Users To Tweet ‘Meow, I By Adarsh Verma – November 20, 2015
Short Bytes: Tweeting your personal information on Twitter could result in an unwanted subscription of a torrent of cat facts, thanks to...
-

 118Data Security
118Data SecurityNo money, but Pony! From a mail to a trojan horse
In this post, we will take a high and low-level look at the Pony Trojan, delivered through a recent spam campaign. During our case...
-

 236Malware
236MalwareVirusTotal Adds Sandbox Execution for OS X Apps
Mac malware is a thing. It’s real. Granted it hasn’t reached the critical mass of malicious code for Windows, but recent encounters...
-

 101Data Security
101Data Security‘Hacked by China? Hack them back!’ rages US Congress report
How dare they demand we do exactly what we demand of them! The foreign rotters. A report laid before the US Congress...
-

 253Geek
253Geek6 Things You Should Know About Facebook’s Security!
Facebook has over 1 billion daily active users, with people in the US spending a staggering 27 hours on the social networking site every month. The company...
-

 139Data Security
139Data SecurityCybercriminals Can Drop Malware On Your PC Using Video Ads
Visual ads directing users to malicious sites are things of past, cyber-criminals have added a new dimension to this: the video ads....
-
 175Hacked
175HackedMark Zuckerberg Quits His Job At Facebook, All Due To A Facebook Bug
Short Bytes: No, there isn’t any typo in the article heading. Read ahead to see Mark Zuckerberg’s post and know the whole...
-

 170Data Security
170Data SecuritySecure messaging service Telegram blocks 78 ISIS-related channels
Telegram, the popular instant messaging service that offers end-to-end encryption, announced on Wednesday that they have “blocked 78 ISIS-related channels across 12...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




