Featured News
-
 277News
277NewsAnonymous Has Shutdown 28,000+ ISIS’ Twitter Accounts Since OpParis Began
The online hacktivist Anonymous shut down 8824 Twitter accounts of ISIS members + followers in the first phase of OpParis — In...
-

 322News
322NewsSelf-Proclaimed Anonymous Hacktivists Predict Potential ISIS Terror Attacks
Someone is using Anonymous’s name to spread rumors about ISIS planning to target different events worldwide. A Pastebin post posted by someone claiming to have a...
-

 317Cyber Crime
317Cyber CrimeCrooks Hack World Bank SSL Certificate To Host PayPal Phishing Scam
Hackers have again attacked PayPal but this time by making a clone site that even had an SSL certificate of the World...
-

 316Data Security
316Data SecurityAnonymous Has Now Taken Down 20,000 ISIS Twitter Accounts, Promises to Go On
Hacking group remains as focused as one week ago Quite a lot has happened after Anonymous declared cyber-war on ISIS members last...
-

 113Data Security
113Data SecurityHow to Baffle Web Trackers by Obfuscating Your Movements Online
ONLINE AD NETWORKS and search engines love it when you surf around. Everything you do—every page you load, every query you type—helps...
-
 216Vulnerabilities
216VulnerabilitiesVMware Patches Pesky XXE Bug in Flex BlazeDS
VMware has patched an information disclosure vulnerability affecting a number of its products that use Flex BlazeDS. The original vulnerability was discovered...
-

 211Incidents
211IncidentseBay Scammer Steals Identity of the Police Officer Investigating His Case
Rohit Jawa fools officer into revealing personal details. Police officers investigating an eBay scammer must have been very surprised when the criminal, in...
-

 216Hacked
216HackedIndian Hackers Attack Pakistan Government and Defense Websites
Short Bytes: In the past, Pakistani and India cyber hackers have been targeting each other by hacking different government websites. In the latest...
-
 188News
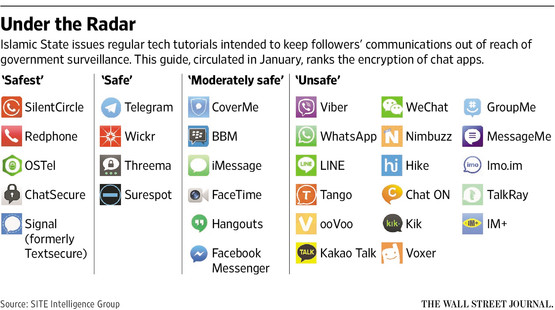
188NewsISIS issues anti-hacking guidelines for its online supports after Anonymous threats
After calling Anonymous ‘Idiots’ ISIS issues guidelines to its cronies to protect from hackers like Anonymous The Islamic State militant ISIL who...
-

 153Incidents
153IncidentsSome Starwood Hotels payment systems hit by malware
Starwood Hotels & Resorts Worldwide Inc said payment systems at 54 of its hotels in North America had been infected with a...
-
 170Geek
170GeekResearcher Founds Bug That Made Mark Zuckerburg Quit his job at Facebook
A Facebook bug is not a surprising thing to know about but Zuckerberg quitting his job as the Facebook’s CEO is not...
-
 104Cyber Crime
104Cyber CrimeCourt Charges Kid with Bomb Threats and DDoS Attacks
A 15-year-old guy in Plymouth has been arrested by British police on the charges of launching DDoS attacks and for sending false bomb...
-
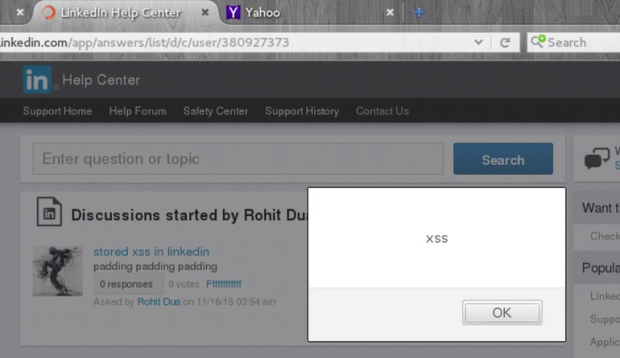
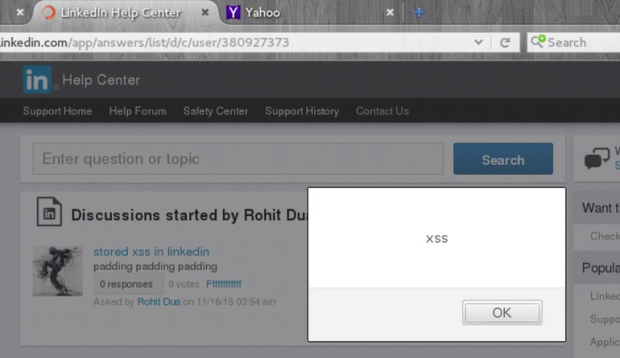 197Vulnerabilities
197VulnerabilitiesLinkedIn patches serious persistent XSS vulnerability
Developers at LinkedIn fixed a persistent cross site scripting vulnerability in the social network this week that could have been exploited to...
-

 154Data Security
154Data Security600,000 cable modems have an easy to pop backdoor in a backdoor
Brazilian whacks Arris for easy-t-o-guess default password, fix promised fast. Security bod Bernardo Rodrigues has found a backdoor-within-a-backdoor affecting some 600,000 Arris...
-

 221Hacked
221HackedThis Coder Forces Careless Twitter Users To Tweet ‘Meow, I By Adarsh Verma – November 20, 2015
Short Bytes: Tweeting your personal information on Twitter could result in an unwanted subscription of a torrent of cat facts, thanks to...
-

 119Data Security
119Data SecurityNo money, but Pony! From a mail to a trojan horse
In this post, we will take a high and low-level look at the Pony Trojan, delivered through a recent spam campaign. During our case...
-

 238Malware
238MalwareVirusTotal Adds Sandbox Execution for OS X Apps
Mac malware is a thing. It’s real. Granted it hasn’t reached the critical mass of malicious code for Windows, but recent encounters...
-

 102Data Security
102Data Security‘Hacked by China? Hack them back!’ rages US Congress report
How dare they demand we do exactly what we demand of them! The foreign rotters. A report laid before the US Congress...
-

 255Geek
255Geek6 Things You Should Know About Facebook’s Security!
Facebook has over 1 billion daily active users, with people in the US spending a staggering 27 hours on the social networking site every month. The company...
-

 143Data Security
143Data SecurityCybercriminals Can Drop Malware On Your PC Using Video Ads
Visual ads directing users to malicious sites are things of past, cyber-criminals have added a new dimension to this: the video ads....
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




