Featured News
-

 324Cyber Events
324Cyber EventsResearcher Claims Dark Web is the next safe haven for the ISIS
Al-Hayat, an agency that spreads all the content relevant to ISIS on different online platforms has announced the ISIS intentions on moving...
-

 215News
215NewsAnonymous Expose and Shutdown 8824 Pro-ISIS Twitter Accounts
The online hacktivist group Anonymous has declared a “total war” against the terrorist group and so-called Islamic State (IS, previously ISIS/ISIL) group. To keep up...
-

 316Data Security
316Data SecurityISIS May Have Used Sony PS4 to Plan Paris Attacks
French authorities after the Paris attacks are busy trying to find the source using which the whole massacre was planned. Last Friday,...
-
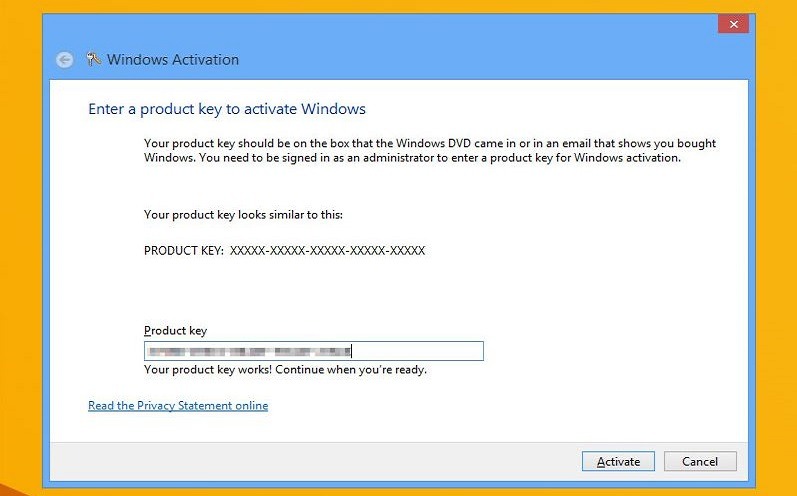
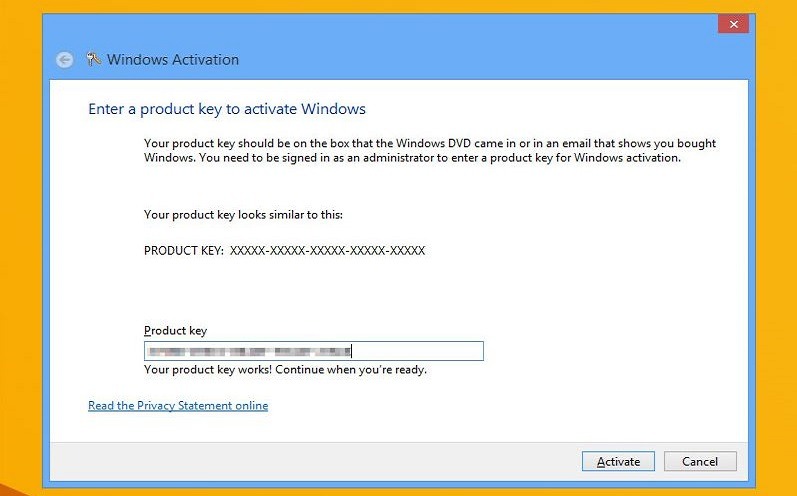 257How To
257How ToHow To Activate Windows 10 Using Windows 7 or 8.1 Product Key
Short Bytes: Microsoft has finally responded to the user feedback in the form of recognizing Windows 7 and 8.1 product keys to...
-
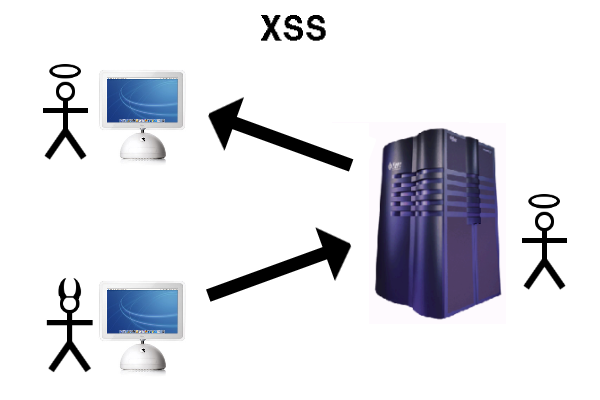
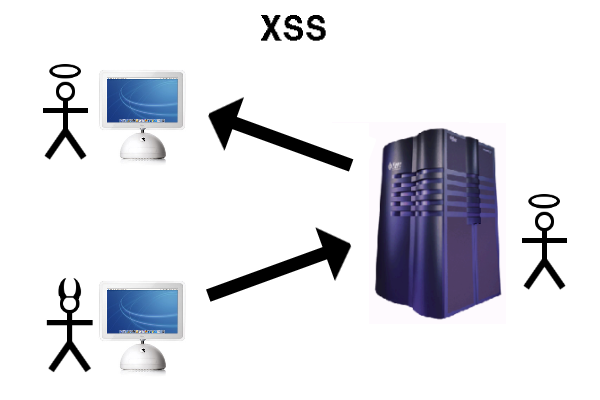 311Vulnerabilities
311VulnerabilitiesXSS in Hidden Input Fields
At PortSwigger, we regularly run pre-release builds of Burp Suite against an internal testbed of popular web applications to make sure it’s...
-
 316Data Security
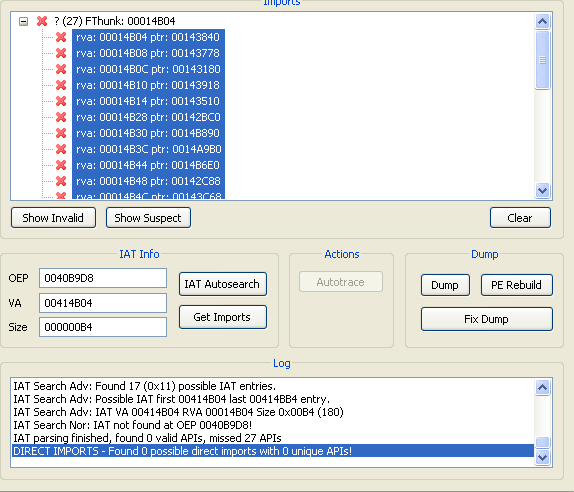
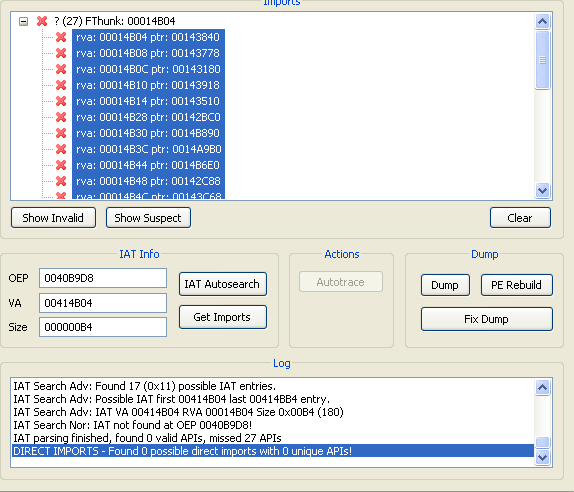
316Data SecurityA Guide to Malware Binary Reconstruction
Often we come across times where binary reconstruction while analyzing malware / unpacking malware is required . Taking leverage of automated tools...
-

 332Data Security
332Data SecurityBitLocker popper uses Windows authentication to attack itself
Microsoft squashes offline logic flaw that makes lost laptops dynamite. Blackhat Europe Synopsys security boffin Ian Haken says un-patched PCs in enterprises...
-

 131Data Security
131Data SecurityLinux.Encoder.1 Ransomware Spreads to 3,000 Websites
Expect a new ransomware version in the coming weeks.The Linux.Encoder.1 ransomware, a special strand that has a taste for Web hosting and...
-

 301Data Security
301Data SecurityHacker Develops Undisputed KillerRat to Spy on Windows PCs
Egyptian Hacker Uses njRAT Codebase to Create KillerRat — The RAT goes completely hidden upon scanning. A new Remote Access Trojan/RAT has...
-

 263Geek
263GeekPhotoshop Fail: Sikh Man in Canada Smeared as Suspected Paris Terrorist
Someone photoshopped this guy’s pic from an iPad to a Quran and the mainstream media took it as real and made it viral....
-

 192News
192NewsCyberwar games lead to foul play resulting in leaked Brazilian Army data
Earlier this week the servers of Brazilian Army got hacked leading to private details of around 7,000 military officials getting stolen. Hackers...
-

 222Geek
222GeekFacebook’s New Feature Will Let You Search within Individual Profiles
Going through Facebook profiles will now be a different experience with Facebook experimenting a new feature, which will allow anyone visiting user...
-

 297News
297NewsAnonymous Waging War on ISIS, Vows to Hunt Down Terrorists After Paris Attacks
The online hacktivist group Anonymous has announced a new series of cyber attacks against the ISIS/ISIL terrorist group. This Friday, terrorists targeted...
-

 174Malware
174MalwareMore POS malware, just in time for Christmas
VXers stuff evidence-purging malware in retailer stockings. Threat researchers are warning of two pieces of point of sales malware that have gone...
-
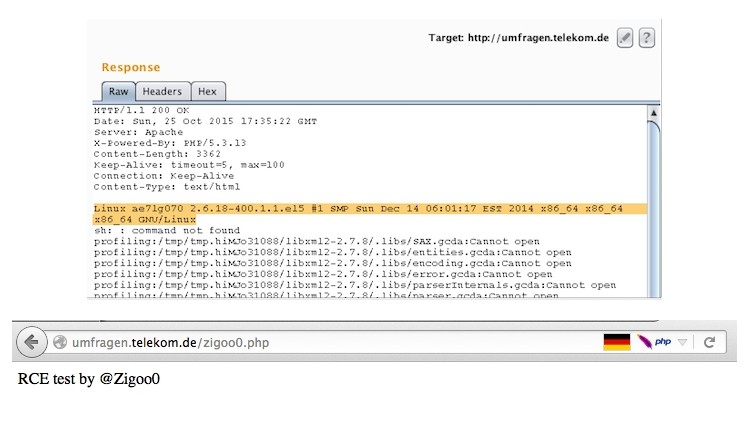
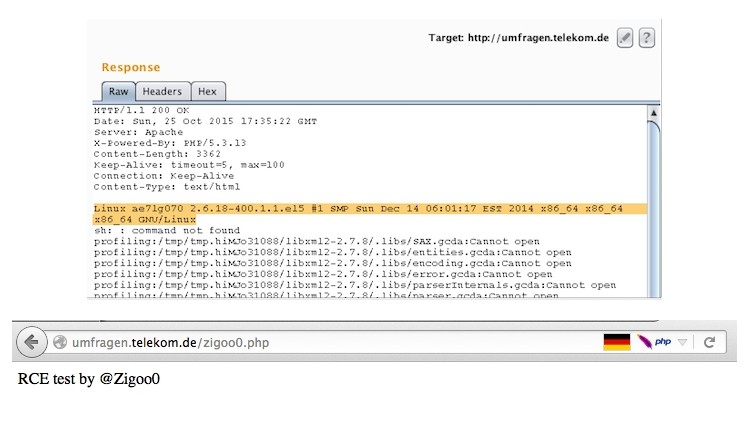 129Vulnerabilities
129VulnerabilitiesRCE Vulnerability Fully Compromises Deutsche Telekom Server
Attackers could have had full control over DT’s Web server. Independent Egyptian security researcher Ebrahim Hegazy has found another vulnerability, and this one...
-

 257Hacked
257HackedYes, You Are Now Allowed To Hack Your WiFi Router
Short Bytes: After facing tons of criticism over the new proposed rules governing the 5GHz spectrum devices (basically your WiFi routers), the...
-
 87Vulnerabilities
87VulnerabilitiesPNG pongs: critical bug patched in ubiquitous libpng
Crafted image crashes apps, server processes. This will not be fun: the graphics processing library libpng has a vulnerability and needs to...
-

 150Data Security
150Data SecurityAnonymous Announces Payback for ISIS Paris Attacks
It didn’t take long for Anonymous members to rally and swear payback for the recent ISIS terror attacks that took place in...
-

 168Geek
168GeekSecurity Flaw in Samsung Galaxy Devices Lets Attackers Record Phone Calls
A telephone tower-like device (IMSI-catcher) can be used for recording phone calls from the latest versions of Samsung Galaxy, demonstrated by two...
-

 296Hacked
296HackedAnonymous Announces Revenge Campaign For Paris Attacks By ISIS #OpParis
Short Bytes: In response to the Paris attacks, Hacktivist group Anonymous was quick to issue a warning to its long-time foe ISIS....
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




