Featured News
-

 260Cyber Crime
260Cyber CrimeHackers Infect British Parliament Computers with Ransomware
Cyber cooks breached the security of British parliament’s secure network and hacked into many of its computer systems. The hack allowed the...
-

 253Kids Online
253Kids Online5 things you can monitor with your parental control tool
One of the biggest concerns parents have about the internet is the sites their children are browsing. Parental control tools can help...
-

 92Cyber Crime
92Cyber CrimeSocial media savvy students ‘better at avoiding cybercrime’
A new study finds that current university students have a mature approach to social media that helps keep them safe from cybercrime.
-

 167Incidents
167IncidentsComcast resets nearly 200,000 passwords after customer list goes on sale
Over the weekend, a reader (@flanvel) directed Salted Hashto a post on a Dark Web marketplace selling a number of questionable, if...
-

 154Hacked
154HackedThis 9-Year-Old Boy Is An Accomplished Hacker And CEO Of A Company
Short Bytes: Reuben Paul is a cybersecurity expert who lives in Austin, Texas, and attends third grade. He is the CEO of...
-
 207Data Security
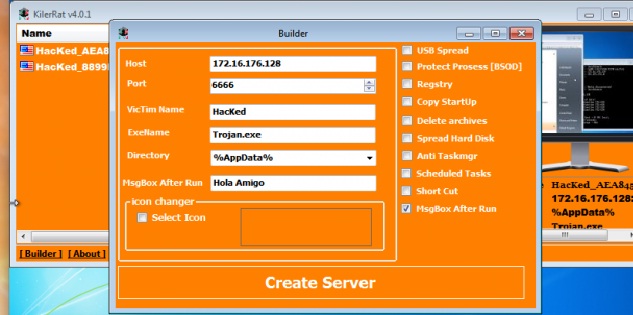
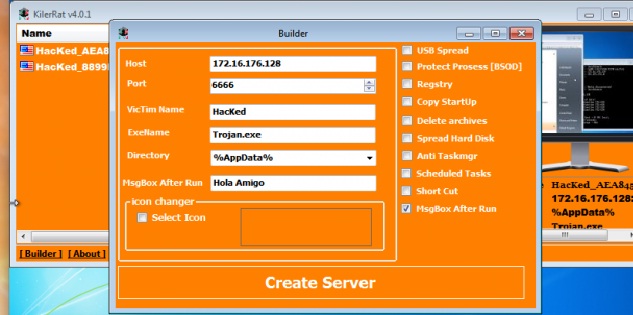
207Data SecurityKilerRat: Taking over where Njrat remote access trojan left off
This remote access trojan (RAT) has capabilities ranging from manipulating the registry to opening a reverse shell. From stealing credentials stored in...
-

 282Data Security
282Data SecurityMan Hacks Norwich International Airport Website for Passengers Safety
A hacker going by the handle of His Royal Gingerness (HRG) hacked into the official website of Norwich International Airport last month...
-

 78Data Security
78Data SecurityHigh-Risk SAP HANA Vulnerabilities Patched
Critical business applications such as SAP and Oracle ERP products process and store the Fortune 2000’s most critical data, yet spur relatively...
-
 173Vulnerabilities
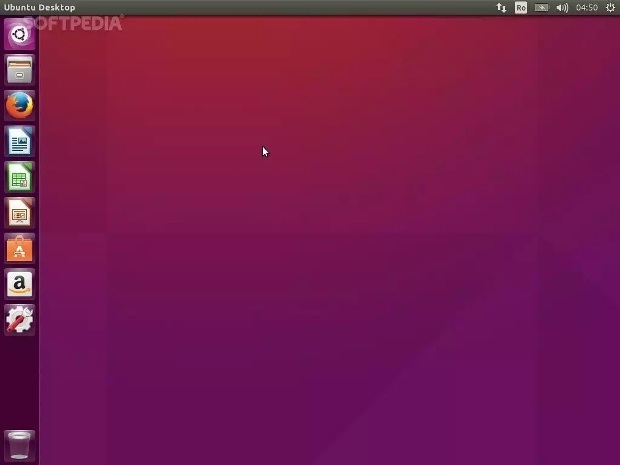
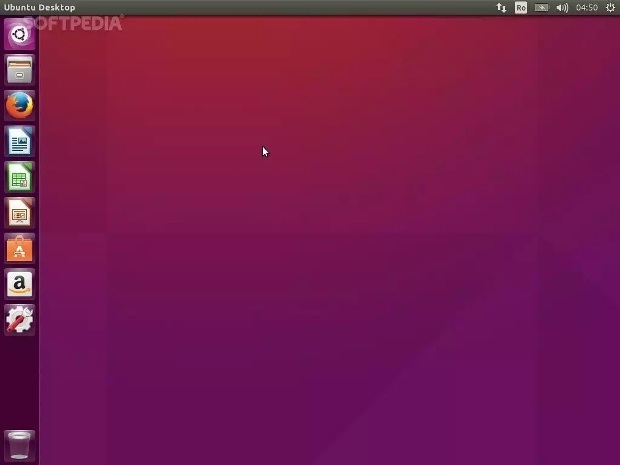
173VulnerabilitiesCanonical Patches Linux Kernel Vulnerability in Ubuntu 15.10, 15.04, 14.04 and 12.04 LTS
All Ubuntu users are urged to update as soon as possible. Canonical has just published four Ubuntu Security Notices that detail a recent...
-
 230Data Security
230Data SecurityNSA claims it shares 91% of security flaws with its manufactures
NSA discloses 91 percent of the zero-day bugs it finds in the online systems to its manufacturers while it keeps the 9...
-

 102Cyber Crime
102Cyber CrimeScammers Trying to Steal Apple IDs with Sophisticated Phishing Scam
The best tool for cyber criminals with limited social engineering skills is tricking users into phishing scams and it doesn’t matter if...
-

 94Incidents
94IncidentsParliament HACKED: Sensitive data STOLEN, used to hold MP to ransom
CYBERTHIEVES hacked into the parliament’s secure computer network and used sensitive files to hold an MP to ransom, it has been revealed....
-

 237Hacked
237HackedRussian Engineers Create “USB Killer 2.0” To Protect Your Data
Short Bytes: Rusian engineers have created an ultimate data security device for you as a last line of defence. A USB Killer...
-
 83Hacked
83HackedLinux Systems Are Responsible for 50% DDoS Attacks in Past 3 Months
Short Bytes: DDoS attacks are targeting the networks and websites all over the world relentlessly. In the past three mnths, there has...
-
 91Incidents
91IncidentsOz submarine bidders paper over hack attacks, deliver tenders by hand
Report: Germany, France, Japan contract hopefuls spotted multiple attacks. Hacking attempts are forcing bidders in Germany, France, and Japan for Australia’s A$50...
-

 141Incidents
141Incidents54,000 Twitter accounts hacked by Cyber Caliphate; Is anyone safe at all?
Daesh’s cyber squad hacks over 54,000 Twitter accounts In the current era, there is no such thing that we have come across...
-
 176Hacked
176HackedMicrosoft: “We Want To Create A World Without Passwords”
Short Bytes: Windows 10 comes with better options to keep an eye on your devices and ensure that your every work session...
-
 100Data Security
100Data SecurityThe Infernal-Twin tool, easy hacking wireless networks
The Infernal-Twin is an automated tool designed for penetration testing activities, it has been developed to automate the Evil Twin Attack. The Infernal-Twin...
-

 177Data Security
177Data SecurityNSA Discloses 91 Percent of Zero-Day Bugs It Finds, Keeps the Rest for Itself
US spying agency reveals bug disclosure program’s stats An NSA spokesperson said the agency discloses zero-day bugs to manufacturers and affected companies...
-

 120News
120NewsHackers Who Obtained CIA emails Breach FBI Servers
The teen hacking group “Crackas With Attitude” (CWA), who hacked into the email account of CIA’s director John Brennan last month has...
The Latest
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets
-
 Vulnerabilities
VulnerabilitiesFortinet Rolls Out Critical Security Patches for FortiClientLinux Vulnerability
-
 Malware
Malware‘eXotic Visit’ Spyware Campaign Targets Android Users in India and Pakistan
-
 Malware
MalwareRaspberry Robin Returns: New Malware Campaign Spreading Through WSF Files
-
 Malware
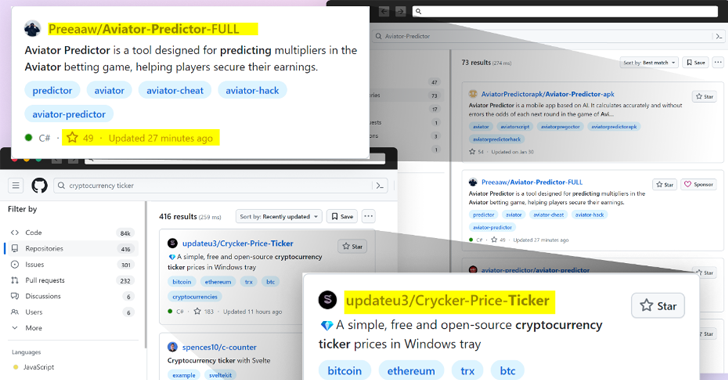
MalwareBeware: GitHub’s Fake Popularity Scam Tricking Developers into Downloading Malware
-
 Vulnerabilities
VulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
-
 Vulnerabilities
VulnerabilitiesMicrosoft Fixes 149 Flaws in Huge April Patch Release, Zero-Days Included
-
 Vulnerabilities
VulnerabilitiesCritical ‘BatBadBut’ Rust Vulnerability Exposes Windows Systems to Attacks
-
 Vulnerabilities
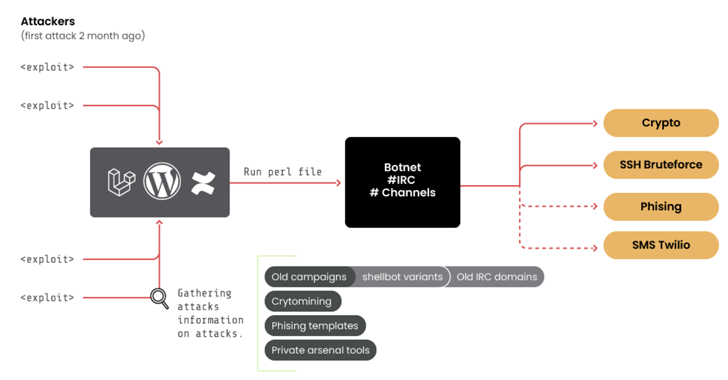
Vulnerabilities10-Year-Old ‘RUBYCARP’ Romanian Hacker Group Surfaces with Botnet
-
 Malware
MalwareHackers Targeting Human Rights Activists in Morocco and Western Sahara
-
 Vulnerabilities
VulnerabilitiesResearchers Discover LG Smart TV Vulnerabilities Allowing Root Access
-
 Malware
MalwareCL0P’s Ransomware Rampage – Security Measures for 2024
-
 Malware
MalwareAttackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing
-
 Vulnerabilities
VulnerabilitiesCritical Flaws Leave 92,000 D-Link NAS Devices Vulnerable to Malware Attacks
-
 Malware
MalwareWatch Out for ‘Latrodectus’ – This Malware Could Be In Your Inbox




