Featured News
-

 322Geek
322GeekCourt Orders Facebook to Stop Tacking Non-Users or Pay €250K Fine Daily
A Belgian court has ordered Facebook to stop tracking internet users within next 48 hours or they will impose fines of up...
-

 116Cyber Crime
116Cyber CrimeResearchers Expose Iranian Phishing Servers Targeting Opposition
A group of researchers from Checkpoint Security firm claimed that they have breached phishing servers that were used by the Rocket Kitten....
-

 268Cyber Crime
268Cyber CrimeHackers Infect British Parliament Computers with Ransomware
Cyber cooks breached the security of British parliament’s secure network and hacked into many of its computer systems. The hack allowed the...
-

 260Kids Online
260Kids Online5 things you can monitor with your parental control tool
One of the biggest concerns parents have about the internet is the sites their children are browsing. Parental control tools can help...
-

 97Cyber Crime
97Cyber CrimeSocial media savvy students ‘better at avoiding cybercrime’
A new study finds that current university students have a mature approach to social media that helps keep them safe from cybercrime.
-

 172Incidents
172IncidentsComcast resets nearly 200,000 passwords after customer list goes on sale
Over the weekend, a reader (@flanvel) directed Salted Hashto a post on a Dark Web marketplace selling a number of questionable, if...
-

 159Hacked
159HackedThis 9-Year-Old Boy Is An Accomplished Hacker And CEO Of A Company
Short Bytes: Reuben Paul is a cybersecurity expert who lives in Austin, Texas, and attends third grade. He is the CEO of...
-
 213Data Security
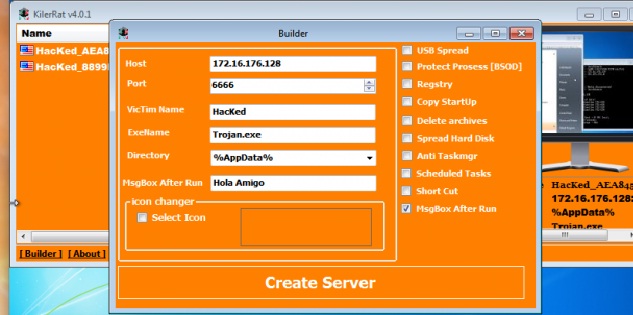
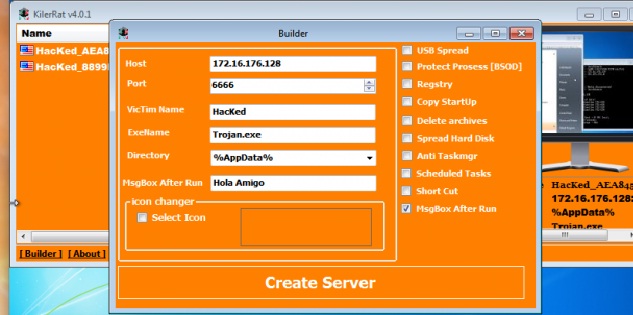
213Data SecurityKilerRat: Taking over where Njrat remote access trojan left off
This remote access trojan (RAT) has capabilities ranging from manipulating the registry to opening a reverse shell. From stealing credentials stored in...
-

 290Data Security
290Data SecurityMan Hacks Norwich International Airport Website for Passengers Safety
A hacker going by the handle of His Royal Gingerness (HRG) hacked into the official website of Norwich International Airport last month...
-

 82Data Security
82Data SecurityHigh-Risk SAP HANA Vulnerabilities Patched
Critical business applications such as SAP and Oracle ERP products process and store the Fortune 2000’s most critical data, yet spur relatively...
-
 179Vulnerabilities
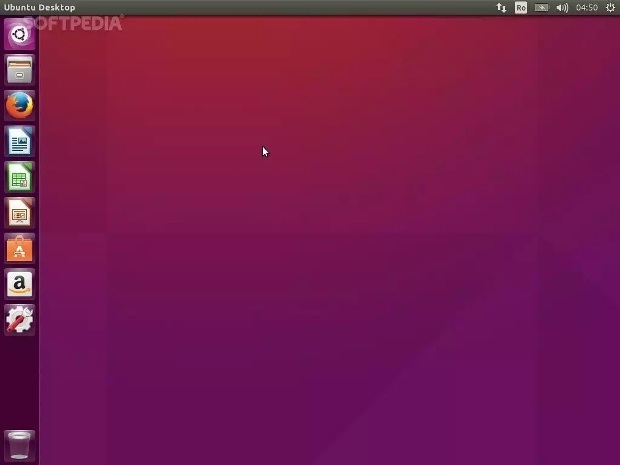
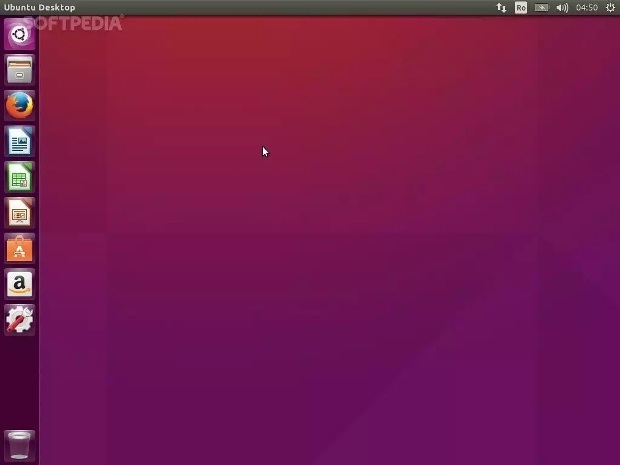
179VulnerabilitiesCanonical Patches Linux Kernel Vulnerability in Ubuntu 15.10, 15.04, 14.04 and 12.04 LTS
All Ubuntu users are urged to update as soon as possible. Canonical has just published four Ubuntu Security Notices that detail a recent...
-
 237Data Security
237Data SecurityNSA claims it shares 91% of security flaws with its manufactures
NSA discloses 91 percent of the zero-day bugs it finds in the online systems to its manufacturers while it keeps the 9...
-

 107Cyber Crime
107Cyber CrimeScammers Trying to Steal Apple IDs with Sophisticated Phishing Scam
The best tool for cyber criminals with limited social engineering skills is tricking users into phishing scams and it doesn’t matter if...
-

 99Incidents
99IncidentsParliament HACKED: Sensitive data STOLEN, used to hold MP to ransom
CYBERTHIEVES hacked into the parliament’s secure computer network and used sensitive files to hold an MP to ransom, it has been revealed....
-

 244Hacked
244HackedRussian Engineers Create “USB Killer 2.0” To Protect Your Data
Short Bytes: Rusian engineers have created an ultimate data security device for you as a last line of defence. A USB Killer...
-
 90Hacked
90HackedLinux Systems Are Responsible for 50% DDoS Attacks in Past 3 Months
Short Bytes: DDoS attacks are targeting the networks and websites all over the world relentlessly. In the past three mnths, there has...
-
 94Incidents
94IncidentsOz submarine bidders paper over hack attacks, deliver tenders by hand
Report: Germany, France, Japan contract hopefuls spotted multiple attacks. Hacking attempts are forcing bidders in Germany, France, and Japan for Australia’s A$50...
-

 147Incidents
147Incidents54,000 Twitter accounts hacked by Cyber Caliphate; Is anyone safe at all?
Daesh’s cyber squad hacks over 54,000 Twitter accounts In the current era, there is no such thing that we have come across...
-
 181Hacked
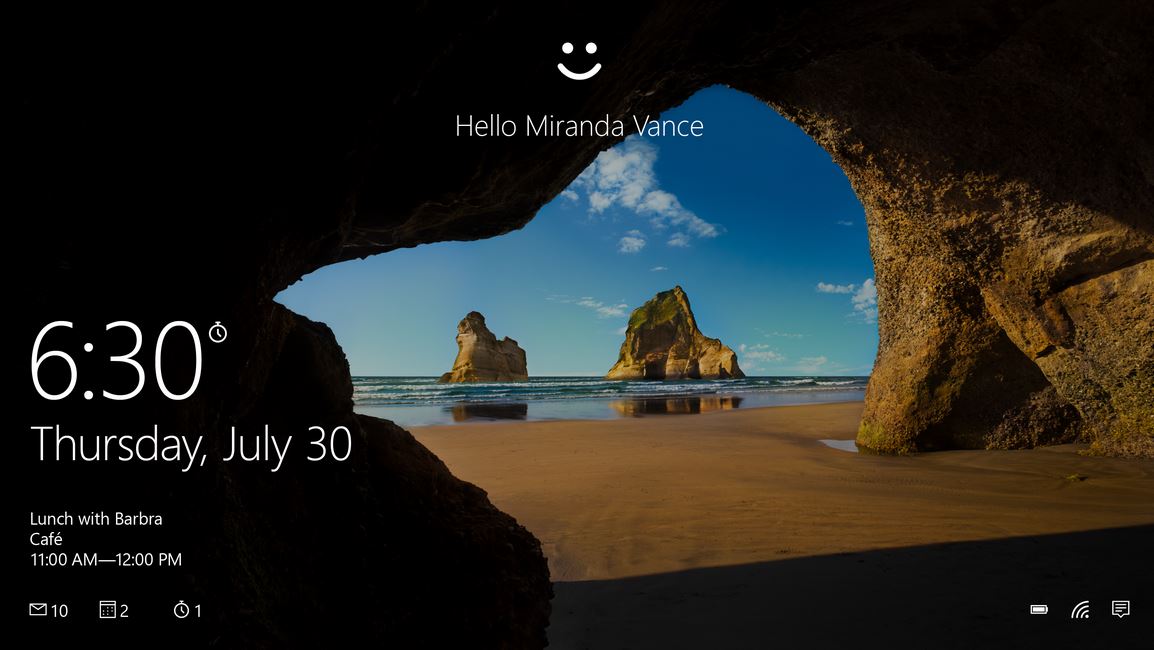
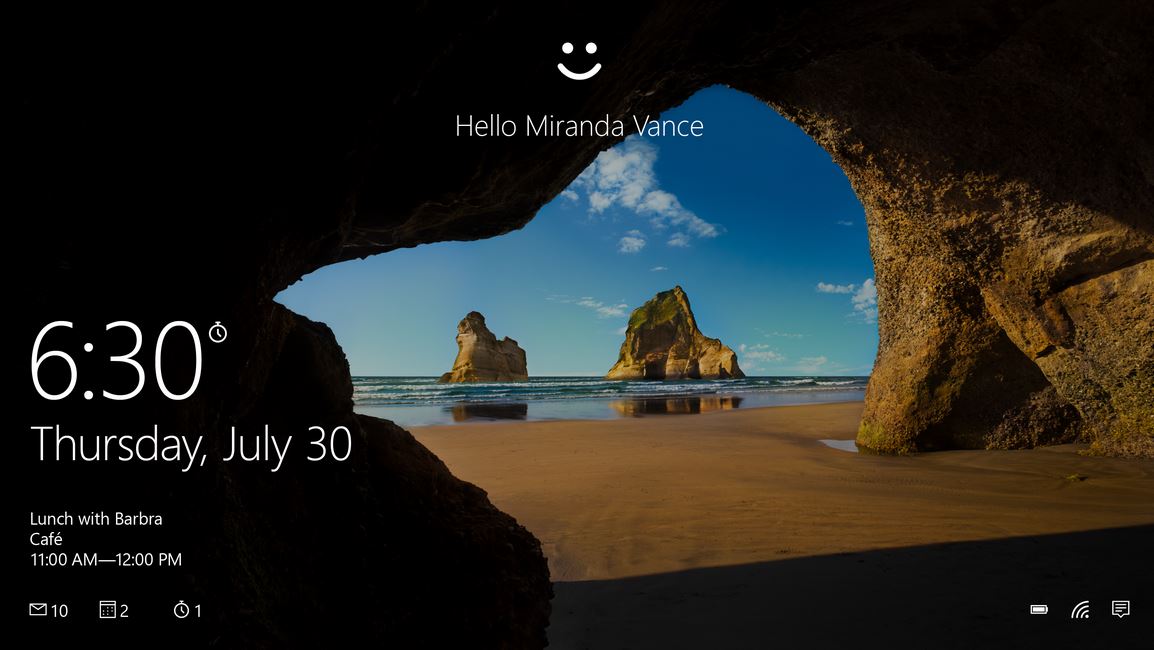
181HackedMicrosoft: “We Want To Create A World Without Passwords”
Short Bytes: Windows 10 comes with better options to keep an eye on your devices and ensure that your every work session...
-
 104Data Security
104Data SecurityThe Infernal-Twin tool, easy hacking wireless networks
The Infernal-Twin is an automated tool designed for penetration testing activities, it has been developed to automate the Evil Twin Attack. The Infernal-Twin...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




