Featured News
-
 134Incidents
134IncidentsWebhosting company loses 13 million plaintext passwords, says “thanks for your understanding”
There’s another data breach to report – and it’s a big one, affecting approximately 13 million customers of the “free” web hosting...
-

 88Cyber Crime
88Cyber CrimeUsing DroidJack to spy on an Android? Expect a visit from the police
Law enforcement agencies across Europe have searched homes this week, as part of an international crackdown against users of a notorious piece...
-

 321News
321NewsHacker Leaks 13 million emails and passwords in 000Webhost Breach
A security researcher (Troy Hunt), who owns the website (haveibeenpwned) have discovered a possible breach of webhosting service 000Webhost servers. Basically, hunt’s...
-

 256Lists
256Lists30 Toughest Questions Asked In Apple Interviews
Short Bytes: Apple boasts one of the best workforces in the tech world with employees ranging from a software engineer to a...
-

 188Geek
188GeekFacebook, WhatsApp Users can be tracked down by hackers
A group of researchers have demonstrated how locations of Facebook and WhatsApp users can be exposed by a security flaw in 4G networks....
-

 430Password
430Password11‑year‑old sets up cryptographically secure password business
An 11-year-old girl from New York has set up her own business selling cryptographically secure passwords, using a technique known as diceware.
-

 128Cyber Crime
128Cyber CrimeThe great car hacking debate
Can cars be hacked remotely or is the idea of remotely hackable cars still only a hypothetical threat? Evidence is presented to...
-
 201Hacked
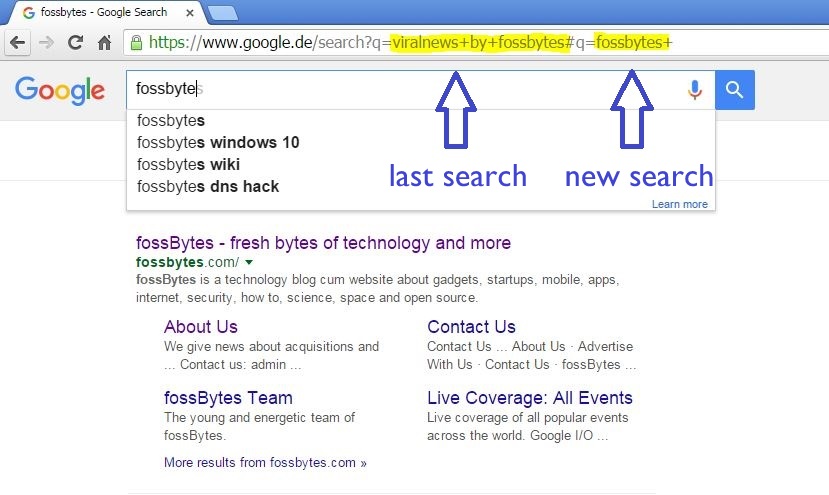
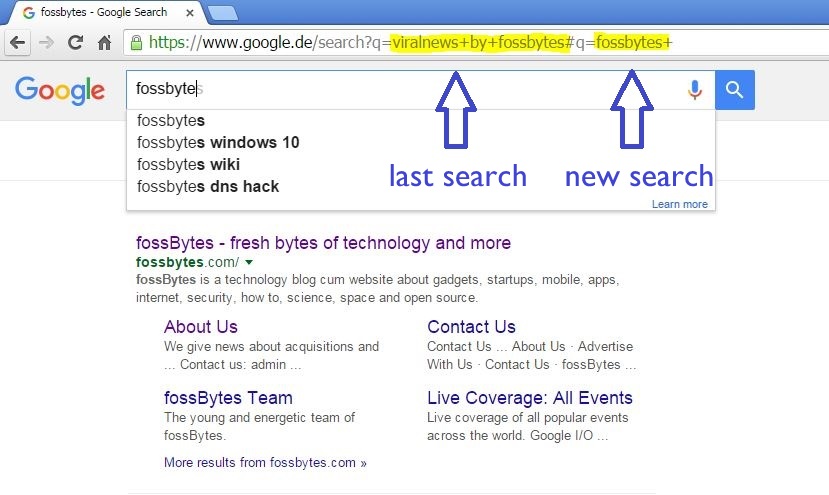
201HackedHow Innocent Copy-Paste Leaks Your Previous Embarrassing Google Searches
Short Bytes: Our innocent habit of copy-paste is reflected when we send the URLs of search pages as some reference to our...
-
 194Malware
194MalwareMulti-stage exploit installing trojan
ESET researchers receive and analyze thousands of new malware samples every day. Earlier this year, one of them caught our attention because...
-
 93Data Security
93Data SecurityGoogle HTTP Search, yes, it is still possible
Google began to implement SSL on its search engine back in 2010. First on its own domain name, then as a...
-

 163Vulnerabilities
163VulnerabilitiesFewer IPsec VPN Connections at Risk from Weak Diffie-Hellman
A challenge has been made against one of the conclusions in a potentially blockbuster academic paper on cryptographic weaknesses that may be...
-

 178Vulnerabilities
178VulnerabilitiesJaguar car hack in New Zealand
A Jaguar XFR may have been stolen using hacking techniques increasingly seen on keyless cars. This unidentified thief did not have the...
-

 286Cyber Events
286Cyber EventsAnonymous Vows To Leak Personal Information of 1,000 KKK Members
The online hacktivist Anonymous is planning to leak personal information of around 1000 members of the white supremacist Christian organization the Ku Klux Klan...
-
 219Geek
219GeekFacebook “Message Requests” Lets You Talk to People You’re Not Friends With
The most common problem you may face on social media platforms like Facebook is receiving unwanted messages from strangers. But, Facebook’s new feature...
-

 76Data Security
76Data SecurityUS Army Experts Call for military bug bounty program AVRP
US Army Military experts urge the establishment of an Army Vulnerability Response Program (AVRP), a sort of military bug bounty program. What...
-
 226Data Security
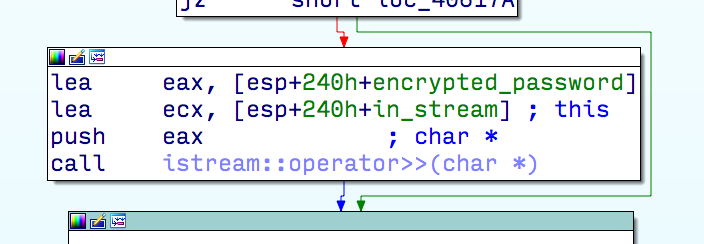
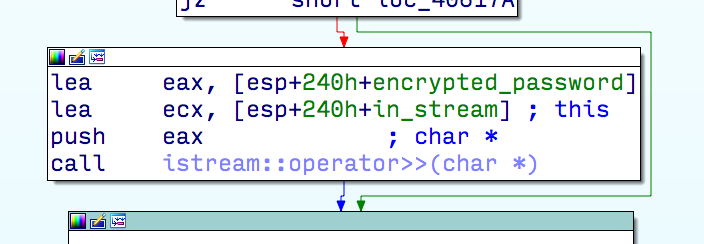
226Data SecurityTiming attack vulnerability in most Zeus server-sides
Timing attacks has proven practical since 96′ as shown in a paper by Paul C. Kocher. In his paper Paul demonstrate how,...
-
 88Data Security
88Data SecurityFake Chrome browser replaces real thing and serves up unwanted ads
Does your Chrome browser seem a little “off”, but you can’t figure out why? Maybe it’s eFast. Here’s another reason to slow...
-

 75Data Security
75Data SecurityTrain rider has his contactless card e-pickpocketed
It could have been just another one of those jostlings that happen on the train: a man bumped into a writer for...
-

 191Hacked
191HackedGermany Suspects, Will Investigate Google and Facebook Over Data Transfers
Short Bytes: The European Union has many a times been apprehensive of the US-based tech companies, especially on the matters of privacy and...
-

 294Data Security
294Data SecurityFBI Wants You To “Just Pay The Ransom” to Cyber Criminals
The Federal Bureau of Investigation (FBI) has stated that it’s completely fine to pay ransom to cyber criminals. If you are a fan...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




