Featured News
-

 85Cyber Crime
85Cyber CrimeProtonMail hit with another DDoS attack
After experiencing an onslaught of DDoS attacks, which saw it hand over the ransom that was demanded, ProtonMail has once again been...
-
 92Data Security
92Data SecurityTop FBI lawyer: You win, we’ve given up on encryption backdoors
We’re your servants, says general counsel unconvincingly After spending months pressuring tech companies to add backdoors into their encryption software, the FBI...
-
 82Malware
82MalwarejQuery.min.php Malware Affects Thousands of Websites
Fake jQuery injections have been popular among hackers since jQuery itself went mainstream and became one of the most widely adopted JavaScript...
-
 108Data Security
108Data SecurityCrypto e-mail service pays $6,000 ransom, gets taken out by DDoS anyway
Follow-on attacks show capabilities “commonly possessed by state-sponsored actors.” A provider of end-to-end encrypted e-mail said it paid a ransom of almost...
-
 273Cyber Events
273Cyber EventsAnonymous stands true to its words, leaks more data on alleged KKK members
The online hacktivist Anonymous released what they called a list of Ku Klux Klan members and sympathizers on Thursday. As reported earlier, the Anonymous...
-

 342Data Security
342Data SecuritySDK Security Flaw Puts 100 Million Android Users Vulnerable to Backdoor Attack
A software development kit that has been provided by Baidu (A Chinese search engine) can easily be exploited for installing backdoors on...
-

 168Data Security
168Data SecurityLinux Servers to Blame for 45 Percent of All DDoS Attacks in the Past 3 Months
Cyber-security vendors are revealing their statistics for the third quarter (Q3) of 2015, and a popular topic is DDoS attacks, a tactic...
-

 191Data Security
191Data SecurityUK cyber-spy law takes Snowden’s revelations of mass surveillance – and sets them in stone
IPB The encryption bothering parts of the UK’s Investigatory Powers Bill have left IT security experts flabbergasted. Introducing the draft internet surveillance...
-
 433How To
433How ToTop 10 Coolest Notepad Tricks and Hacks for Your PC
Short Bytes: The humble Notepad of your laptop goes unappreciated many times. This little tool is capable of doing some amazing tricks...
-

 332Data Security
332Data SecurityTeen Hackers Who Doxed CIA Chief Are Targeting More Government Officials
A cybersecurity expert once told me something I’ll never forget: “don’t underestimate what bored teenagers can do.” A group teenagers that call...
-

 103Cyber Crime
103Cyber CrimeUK and US banks to face transatlantic cyberattack test
Banks in the UK and US will be tested on how capable they are in coordinating a transatlantic response to a cyberattack.
-

 378How To
378How ToWhat is DNS (Domain Name System) and How it Works ?
What is the definition of DNS? DNS, which stands for Domain Name System, is used as the medium to translate domain names...
-

 113Data Security
113Data SecurityRussian Banks Under Attack from Tinba Banking Botnet
Customers of Russia’s biggest banks are under attack.Dell SecureWorks has detected an ongoing campaign that is targeting users of several Russian banks...
-

 255Malware
255MalwareNew type of auto-rooting Android adware is nearly impossible to remove
20,000 samples found impersonating apps from Twitter, Facebook, and others. Researchers have uncovered a new type of Android adware that’s virtually impossible...
-

 321Hacked
321HackedMan Hires “Hacker” to Erase $16,000 Fine, Actually Hires Undercover Cop and Goes to Prison
Short Bytes: What is the worst thing that could happen when you hire a hacker to conduct some criminal activity? Yes, police...
-

 87Malware
87MalwareSchrödinger’s antivirus: The immortality of antivirus software
The question of antivirus software being dead is one that doesn't seem to go away. Why is that? Distinguished ESET researcher Aryeh...
-

 196Data Security
196Data SecurityStuxnet-style code signing of malware becomes darknet cottage industry
Even reports of crims offering signing-as-a-service. Underground cybercrooks are selling digital certificates that allow code signing of malicious instructions, creating a lucrative...
-
 245Data Security
245Data SecurityReturn of the EXIF PHP Joomla Backdoor
Our Remediation and Research teams are in constant communication and collaboration. It’s how we stay ahead of the latest threats, but it...
-

 180Vulnerabilities
180VulnerabilitiesGoogle Project Zero Turns Over 11 Bugs in Galaxy S6 Edge
Google’s Nexus Android devices are considered the most secure by default since they’re guaranteed to receive all security patches for vulnerabilities found...
-

 218Data Security
218Data SecuritySecurity Researcher Creates Tool to Extract Passwords from KeePass Databases
Denis Andzakovic, a security researcher for Security Assessment, has created a tool that can fool the KeePass password manager into exporting its...
The Latest
-
 Data Breach
Data BreachAre Your SaaS Backups as Secure as Your Production Data?
-
 Data Breach
Data BreachMS Exchange Server Flaws Exploited to Deploy Keylogger in Targeted Attacks
-
 Data Breach
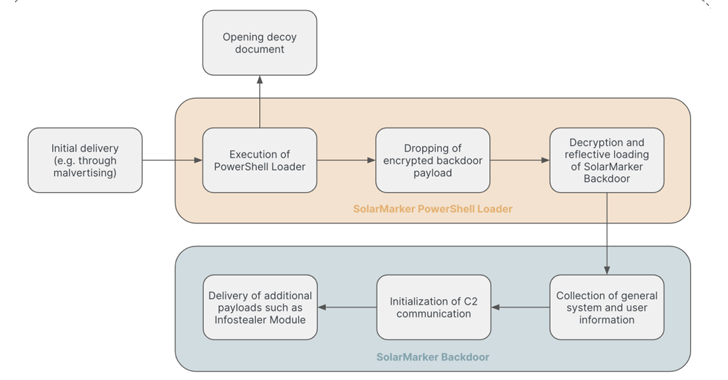
Data BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
-
 Cyber Attack
Cyber Attack“Linguistic Lumberjack” Vulnerability Discovered in Popular Logging Utility Fluent Bit
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
 Malware
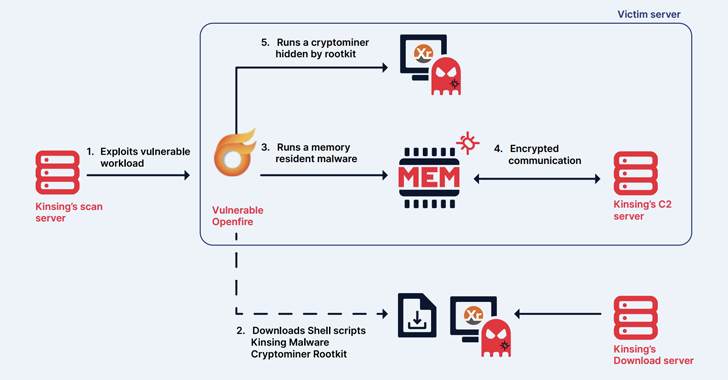
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
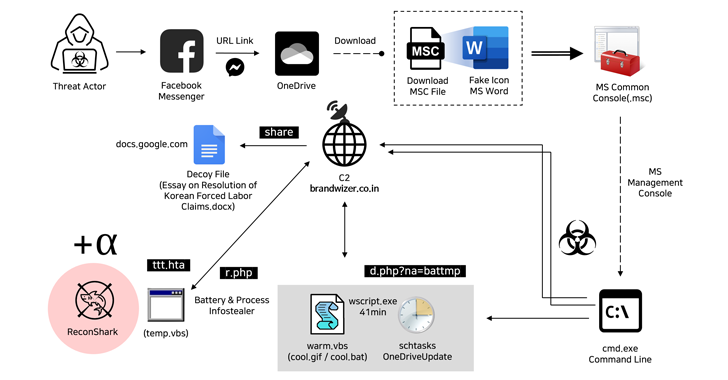
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
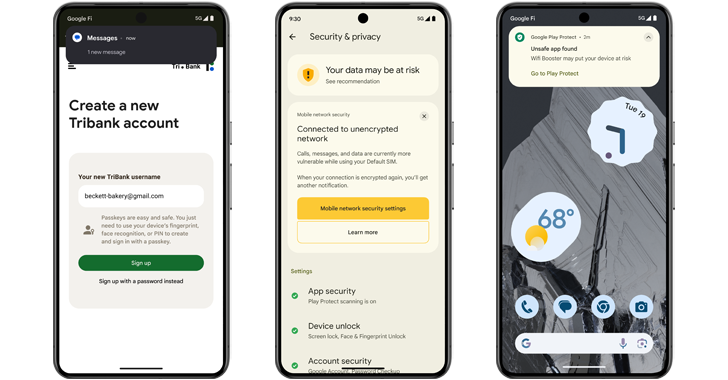
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage




