Featured News
-

 328Data Security
328Data SecurityHacker Steals, Drives Away Jaguar XFR Exploiting Flaw in Wireless System
A silver Jaguar XFR parked in a parking lot in Auckland, New Zealand was stolen with the help of a hacking device that sends...
-

 188Surveillance
188SurveillanceWhatsApp Found Collecting Data on Calls and Phone Numbers
WhatsApp, one of the most popular online calling apps, has been exposed by a group of researchers who identified how app’s internal...
-

 82Malware
82MalwareTrick or treat? Beware so a ransomware won’t end up between your Halloween sweets
Ghosts, monsters and the living dead can all send a chill down one's spine. Ransomware, for some people, is just as spooky....
-

 255Hacked
255HackedForget Credit Cards, Now Withdraw Cash With Iris Scan Technology
Short Bytes: Diebold has developed a concept ATM that reduces the use of plastic money for cash withdrawal to zero. The self-serving...
-

 315Hacked
315HackedAndroid Malware Hides as MS Word File, Sends Data To Hacker
Short Bytes: Attackers are now using an android malware app which camouflages itself as a Microsoft Word document. The malware once triggered, scans...
-

 195Hacked
195HackedNow Chat Anonymously with Tor Instant Messenger
Short Bytes: The Tor Project has announced the release of the beta version of its Tor Messenger that allows you to chat...
-

 328Vulnerabilities
328VulnerabilitiesHow to Build a Portable Hacking Station with a Raspberry Pi and Kali Linux
Cracking Wi-Fi passwords, spoofing accounts, and testing networks for exploits is all fun enough, but if you want to take the...
-
 228Malware
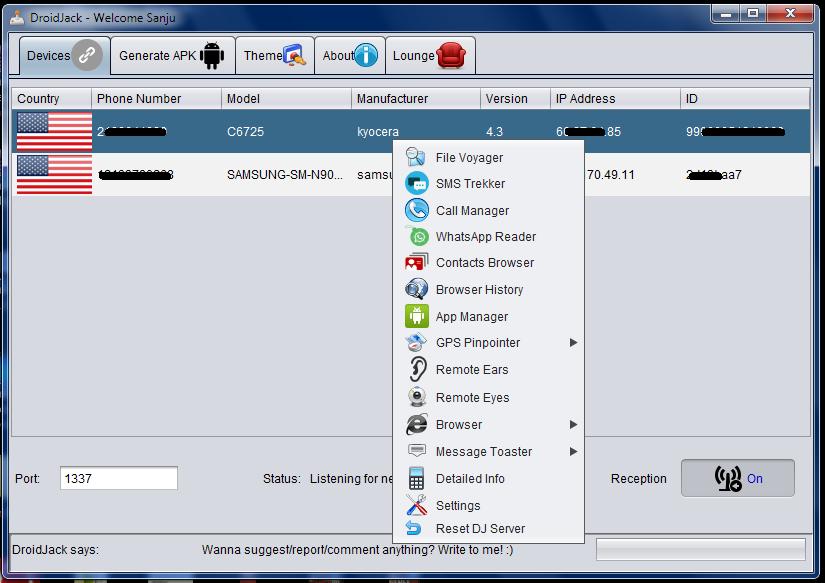
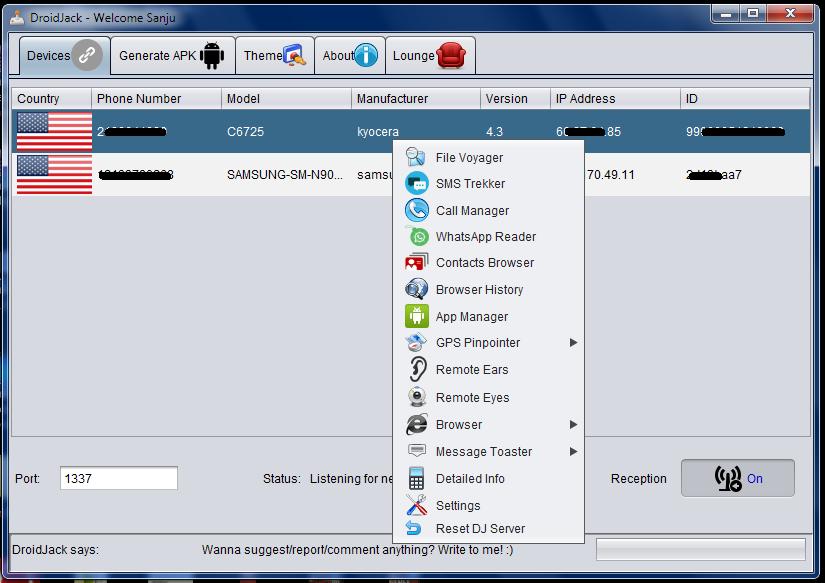
228MalwareEuropean Police Agencies declare war on DroidJack RAT
Authorities in several European countries announced they have coordinated an operation to arrest criminals using the popular DroidJack RAT. Android RATs are becoming...
-

 186Incidents
186IncidentsThousands stolen identities of Britons available on the Darkweb
600k customer identities have been stolen in 2014 and according to government officials thousands of Britons data available for sale in the...
-

 108Vulnerabilities
108VulnerabilitiesChikdos cross-platform DDoS botnet hit SQL servers worldwide
Experts at Symantec have discovered a new variant of the Chikdos DDoS-Trojan that is targeting MySQL servers worldwide. There is a malware...
-

 201Malware
201MalwarePolice raid homes across Europe over DroidJack malware
Thirteen homes in Germany were raided as part of the operation – Image by Thinkstock Police have raided homes in five European countries...
-
 141Incidents
141IncidentsWebhosting company loses 13 million plaintext passwords, says “thanks for your understanding”
There’s another data breach to report – and it’s a big one, affecting approximately 13 million customers of the “free” web hosting...
-

 93Cyber Crime
93Cyber CrimeUsing DroidJack to spy on an Android? Expect a visit from the police
Law enforcement agencies across Europe have searched homes this week, as part of an international crackdown against users of a notorious piece...
-

 334News
334NewsHacker Leaks 13 million emails and passwords in 000Webhost Breach
A security researcher (Troy Hunt), who owns the website (haveibeenpwned) have discovered a possible breach of webhosting service 000Webhost servers. Basically, hunt’s...
-

 261Lists
261Lists30 Toughest Questions Asked In Apple Interviews
Short Bytes: Apple boasts one of the best workforces in the tech world with employees ranging from a software engineer to a...
-

 195Geek
195GeekFacebook, WhatsApp Users can be tracked down by hackers
A group of researchers have demonstrated how locations of Facebook and WhatsApp users can be exposed by a security flaw in 4G networks....
-

 439Password
439Password11‑year‑old sets up cryptographically secure password business
An 11-year-old girl from New York has set up her own business selling cryptographically secure passwords, using a technique known as diceware.
-

 138Cyber Crime
138Cyber CrimeThe great car hacking debate
Can cars be hacked remotely or is the idea of remotely hackable cars still only a hypothetical threat? Evidence is presented to...
-
 206Hacked
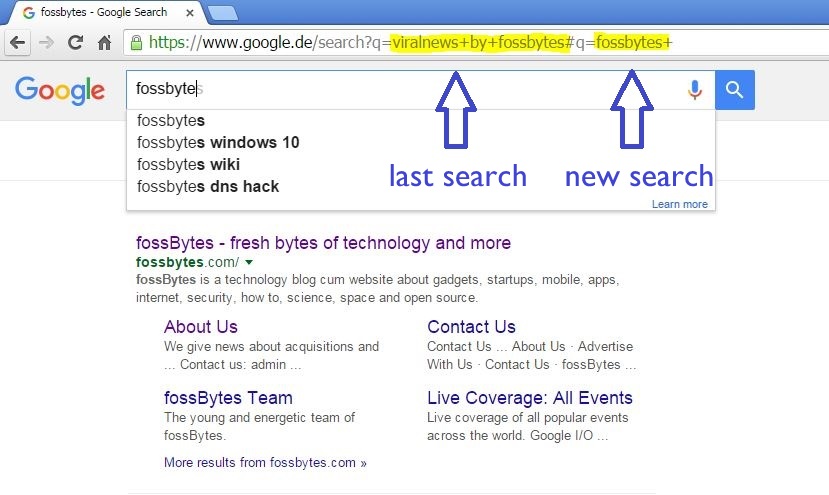
206HackedHow Innocent Copy-Paste Leaks Your Previous Embarrassing Google Searches
Short Bytes: Our innocent habit of copy-paste is reflected when we send the URLs of search pages as some reference to our...
-
 204Malware
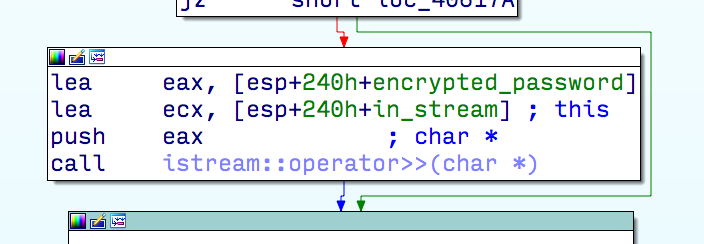
204MalwareMulti-stage exploit installing trojan
ESET researchers receive and analyze thousands of new malware samples every day. Earlier this year, one of them caught our attention because...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




