Featured News
-

 219Hacked
219HackedAre You Under the Attack of CCTV Botnet?
Short Bytes: Internet of Things are constantly being targeted by attackers to get the better off of the companies or individuals. CCTV...
-

 172Incidents
172IncidentsSony pays up to $8m over employees’ hacked data
Sony has agreed to pay up to $8m over employees’ personal data lost in the 2014 hacking scandal surrounding the release of...
-
 237Hacked
237HackedThis Hacker is Destroying Racist and Homophobic Websites One by One
Short Bytes: A hacker that operates a Twitter handle named Amped Attacks, is taking down the websites spreading homophobia and racism one...
-

 168Vulnerabilities
168VulnerabilitiesNovel NTP Attacks Roll Back Time
Sharon Goldberg remembers the cold February day when her Boston University PhD candidate Aanchal Malhotra was studying routing security, in particular, attacks...
-

 96Vulnerabilities
96VulnerabilitiesApple pushes out critical security updates for OS X, iOS, watchOS, and other products
Apple has released security updates to fix critical vulnerabilities in the following Apple products: OS X El Capitan, Mavericks and Yosemite, OS...
-

 95Vulnerabilities
95VulnerabilitiesLinux Kernel 4.2.4 Is Now Available for Download, Has Hundreds of Changes
All users of the Linux 4.2 kernel must upgrade It looks like it’s still October 22 in some countries, so Greg Kroah-Hartman...
-
 107News
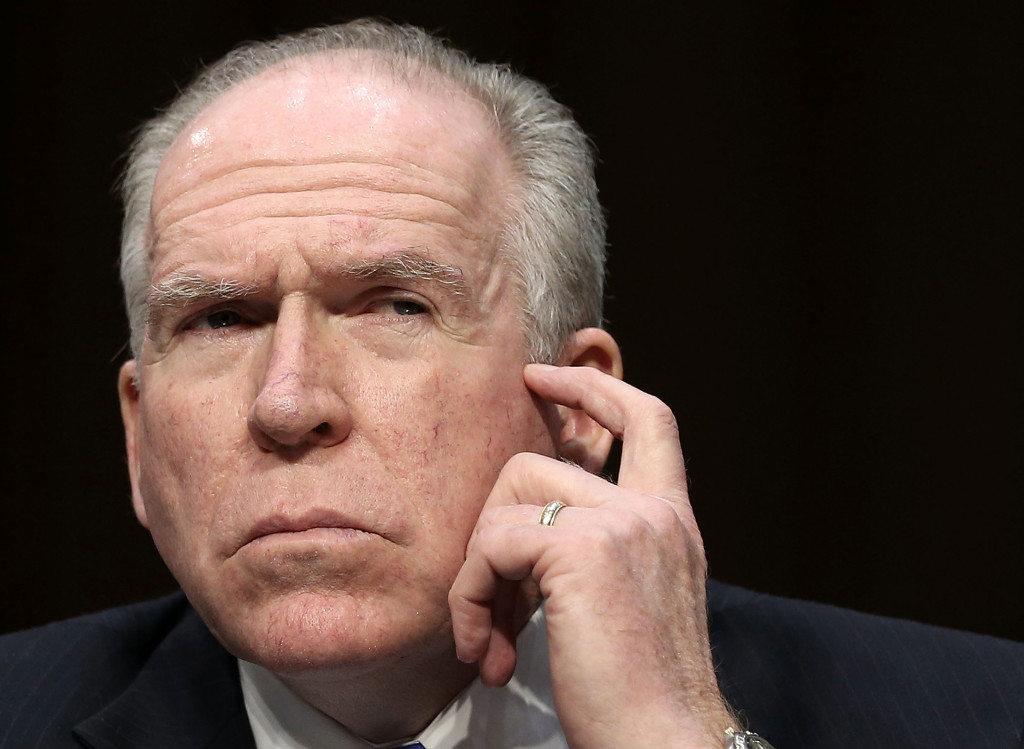
107NewsWikileaks Releases Documents From CIA Boss John Brennan’s Email Account
The CIA boss John Brennan had his AOL-based email account hacked earlier this week by pro-Palestinian hackers — Now WikiLeaks has leaked some...
-

 85Vulnerabilities
85VulnerabilitiesNew attacks on Network Time Protocol can defeat HTTPS and create chaos
Exploits can be used to snoop on encrypted traffic and cause debilitating outages. New attacks on Network Time Protocol can defeat HTTPS...
-
 177Incidents
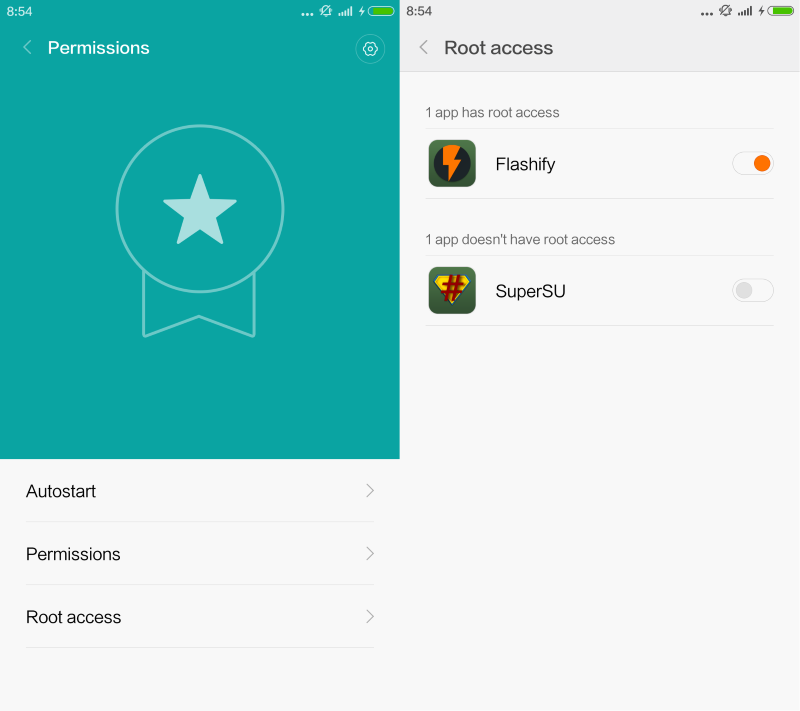
177IncidentsHow to root Xiaomi smartphones effectively
My new Xiaomi Mi 4c smartphone arrived yesterday after an interlude with a German customs agent and several days of delay. I...
-

 154Vulnerabilities
154VulnerabilitiesOracle Quarterly Security Update Patches 154 Vulnerabilities
Oracle on Tuesday patched 154 vulnerabilities in 54 different products as part of its regularly scheduled Critical Patch Update. More than half...
-

 169Data Security
169Data SecurityApple fixes 49 security bugs in iOS 9.1; kills jailbreak
Jailbreak team PanguTeam was credited with finding two security flaws. Apple fixes 49 security bugs in iOS 9.1; kills jailbreak Apple has...
-
 109Data Security
109Data SecurityWikiLeaks Is Publishing the CIA Director’s Hacked Emails
WIKILEAKS MAY DESCRIBE itself as an outlet for whistleblowers, but it’s never hesitated to publish stolen documents offered up by a helpful...
-

 287Data Security
287Data SecurityApple Claims New iPhones are “impossible” to Hack
The CIA and the FBI are always looking for backdoors in Apple devices, in fact, the agency spent years trying to hack iPhone...
-

 226Hacked
226HackedHow A Researcher Hacked iKettles to Steal WiFi Passwords All Across London
Short Bytes: A security researchers from the Pen Testers Partners has revealed that the smart iKettles in your homes are very “insecure.”...
-

 87Data Security
87Data SecurityWith goal of universal HTTPS, Let’s Encrypt reaches important milestone
Free service backed by EFF is now trusted by all major browsers. A nonprofit effort aimed at encrypting the entire Web has...
-
 114Hacked
114Hacked3 Students Arrested for Hacking the School Computer and Changing Their Grades
Short Bytes: An incident of hacking into the school computer systems and changing the subject grades has been spotted in a New...
-

 171Data Security
171Data Security’10-second’ hack jogs Fitbits into malware-spreading mode
To avoid viral stains, go jogging alone or with Bluetooth binned. A vulnerability in FitBit fitness trackers first reported to the vendor...
-
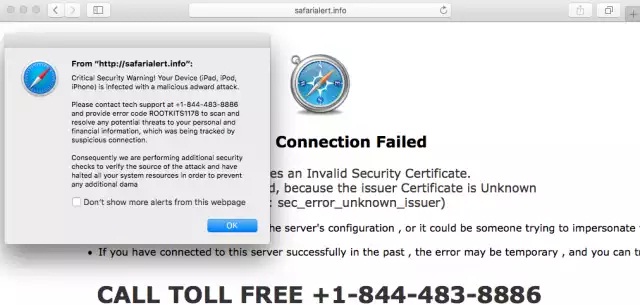
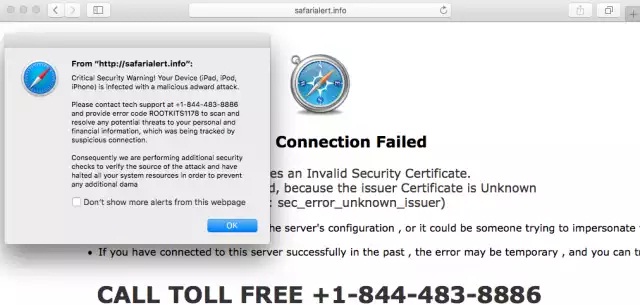 90Data Security
90Data SecuritySupport scams that plagued Windows users for years now target Mac customers
Swindlers impersonate Apple service that remotely accesses user desktops. For years, scammers claiming that they’re “calling from Windows” have dialed up Microsoft...
-
 98Vulnerabilities
98VulnerabilitiesAcademics Find Critical Flaws in Self-Encrypting Hardware Drives
Some consumer-grade, self-encrypting external hard drives are littered with security vulnerabilities that render their encryption an afterthought. An academic paper published in...
-

 232Cyber Events
232Cyber EventsBack to the Future II: 13 Technologies That Became Reality in 2015
How many of you have watched the sci-fi film’s sequel “Back to the Future II”? Do you know the time machine on...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




