Featured News
-
 142Data Security
142Data SecurityNSA warns of growing danger of cyber-attack by nation states
The deputy director of the US National Security Agency (NSA), Richard Ledgett, has warned of the increasing danger of destructive cyber attacks...
-

 137Data Security
137Data SecurityNew Campaign Shows Dridex Active, Targeting French
Two weeks after authorities announced they had taken down the botnet behind the banking malware Dridex, new research suggests the threat is alive and...
-

 244Hacked
244Hacked15-year-old Boy Arrested Over the TalkTalk Hacking Attack
Short Bytes: A 15-year-old has been arrested in Northern Ireland in connection with the cyber-attack on the TalkTalk’s website. This news of 15-year-old...
-

 170Hacked
170HackedHere’s How This Web Page Sniffs Anyone’s Browser History Using Sniffly Attack
Short Bytes: By abusing the HTTP policies of your web browser, a security engineer has devised a new technique to sniff the...
-

 177Hacked
177HackedSecure Your Password With Enigmaze Password Generating Book
Short Bytes: Enigmaze Secure Password Generating Grid System Manager has come up with the most efficient and innovative ways of generating new and...
-
 243Hacked
243HackedMicrosoft: Windows 10 Collects Data to Improve ‘Your’ Experience
Short Bytes: In another attempt to clear the confusion clouds, Microsoft said that users shouldn’t worry about the Windows 10 data collection...
-

 228Geek
228GeekThis Open-source Program Recognize Your Faces in Real Time
Short Bytes: OpenFace, the open source face recognition technology developed by the researchers at the Carnegie Mellon University, has been rolled out. The...
-
 250Operating Systems
250Operating SystemsThe Most Secure Linux Based OS Ever to Date
Qubes OS is different than other operating systems starting right from the kernel. Operating systems such as Windows, Linux, BSD, and OSX...
-
 235Hacked
235HackedCase Against NSA Dismissed Because Nobody Can Prove That It is Spying
Short Bytes: The US District Court has dismissed a lawsuit by Wikimedia against the NSA surveillance. The District Court ruled that the lawsuit...
-
 311Hacked
311HackedGoogle Hacker James Forshaw Tells Why Windows 10 Is Good As Well As Bad
Short Bytes: Accomplished Google hacker James Forshaw thinks that Microsoft has delivered a “good” operating system, but it has failed to ensure...
-
 200Incidents
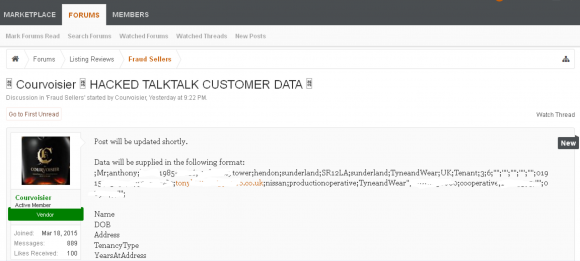
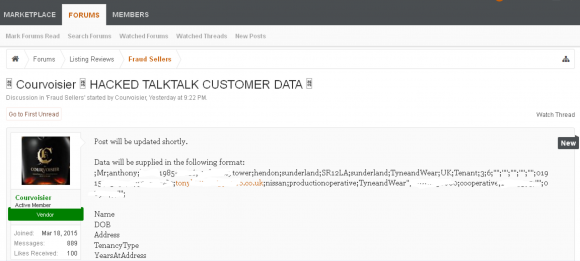
200IncidentsTalkTalk Hackers Demanded £80K in Bitcoin
TalkTalk, a British phone and broadband provider with more than four million customers, disclosed Friday that intruders had hacked its Web site...
-
 330Vulnerabilities
330VulnerabilitiesHackers Found Conducting DDoS Attacks Through Hacked CCTV Cameras
Researchers have found out that hackers took over around 900 CCTV cameras with weak login credentials and used them as a DDosS...
-
 206Data Security
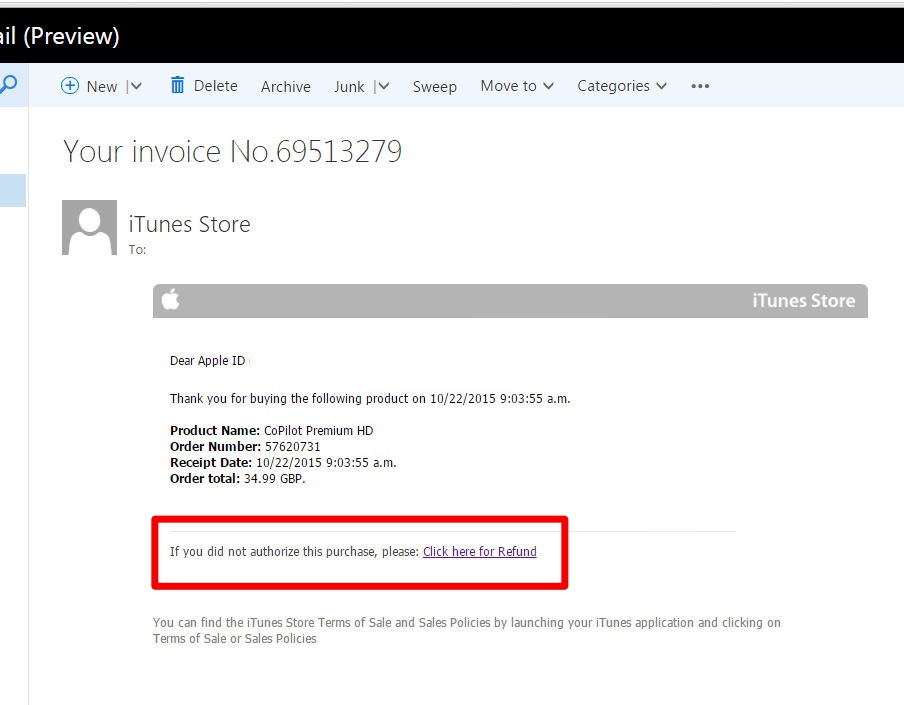
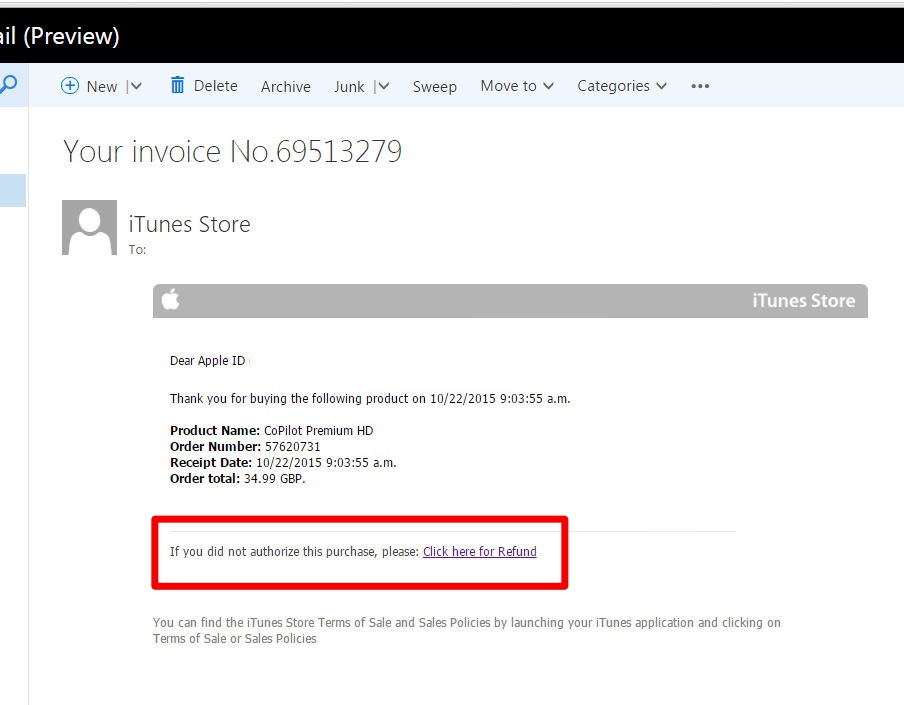
206Data SecurityApple Users Beware: Your Payment Info Can Be Swiped By This New Phishing Scam
Cyber criminals are targeting Apple users with yet another sophisticated phishing scam where users are asked to click a link for payment refund....
-

 187Hacked
187HackedHere’s How Your Fitbit Could be Hacked in Just 10 Seconds
Short Bytes: With the ever advancing fast-paced technology, we are now more open to the more intimate devices like wearables. They are...
-
 249Geek
249GeekHow a Codeless Hack Won $5000 at Facebook Hackathon Without a Single Line of Code
Short Bytes: Driven by the open source philosophy, two Facebook interns won $5,000 at a Facebook Hackathon. They performed a codeless hack...
-

 361News
361NewsAnonymous Targets Thai Govt, Leaks Data from State-owned Telecom Firm
Anonymous, the world famous hacktivist group, has now declared war on the Thai government due to its implementation of single internet gateway...
-
 202Hacked
202HackedThis 11-year-old Girl is Selling Super Secure Passwords for $2 Each
Short Bytes: Mira Modi, an 11-year-old girl, has started a business of selling cryptographically secure passwords for $2 each. She generated Diceware...
-

 332Lists
332Lists29 Toughest Questions Asked in Facebook Job Interviews
Short Bytes: As the latest employee surveys indicate, Facebook is one of the best places to work for. But, getting a job...
-

 337Data Security
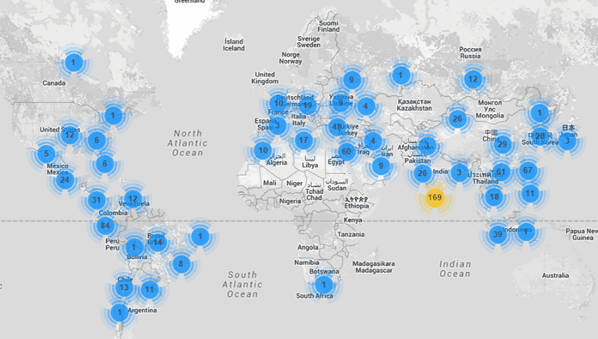
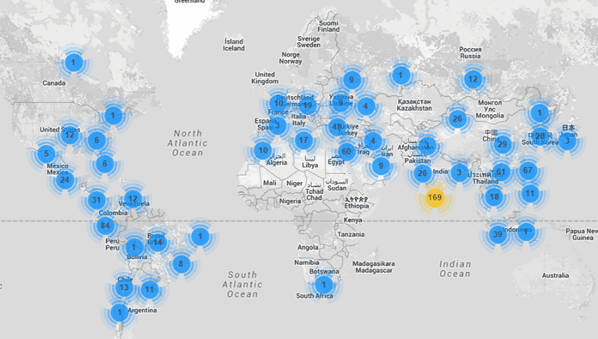
337Data SecurityAn Alarming Number of Governments are using FinFisher Malware: Report
According to a study carried out by the Citizen Lab (a research department at the University of Toronto), FinFisher is the most...
-

 197Hacked
197HackedSelf-driving Cars Must be Programmed to Kill, Study Says
Short Bytes: As we advance more and more in artificial intelligence and related technologies, we must solve some complex ethical problems. A...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




