Featured News
-
 171Vulnerabilities
171VulnerabilitiesSMTP bug-hunt turns up vuln in LibreSSL
Code reviewers looking over a mail daemon have turned up a couple of reasonably serious bugs in the Libre SSL code base...
-
 169Data Security
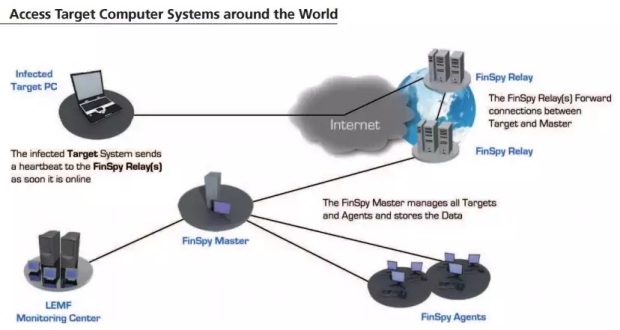
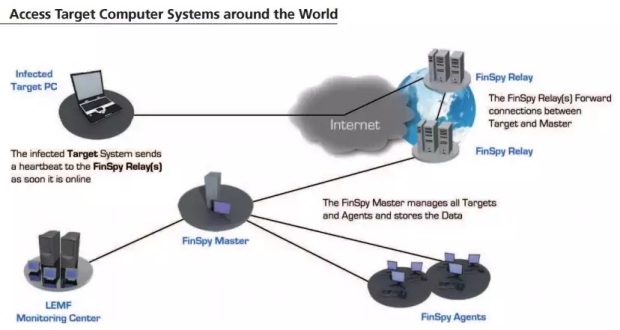
169Data SecurityFinFisher Spyware Becomes More Popular Among Government Agencies
The number of countries deploying it grows to 32.FinFisher, a piece of spyware sold to governments by a German security vendor, has...
-

 251News
251NewsUndisputed Hacker Group Fin5 Stole 150000 Credit Cards From Casinos
Two security firms (FireEye and Mandiant), have found a group of hackers (Fin5) who specialize in credit card stealing and have till date stolen...
-

 266Geek
266GeekLTE Security Flaw Puts Android Devices Vulnerable to DDoS Attack
An alert from Carnegie Mellon University CERT database reveals how Android devices are affected by LTE security flaw and use for DDoS...
-

 239Tricks & How To's
239Tricks & How To'sRemove Your Phone Number from TrueCaller
Over the past few months, TrueCaller has helped us in tracing the mobile number well ahead in advance, before picking up the phone....
-
 242Cryptography
242CryptographyHow to set your Pendrive as your password protector for PC
If you prevent access to your computer with just a password, you are missing out on an alternate (and more secure) way...
-

 231Geek
231GeekThis New Gadget Transforms Paper Airplanes into Powerful Drones
Powerup and French drone-maker firm Parrot collaborated together to create a revolutionary new gadget that easily converts something as insignificant like a...
-
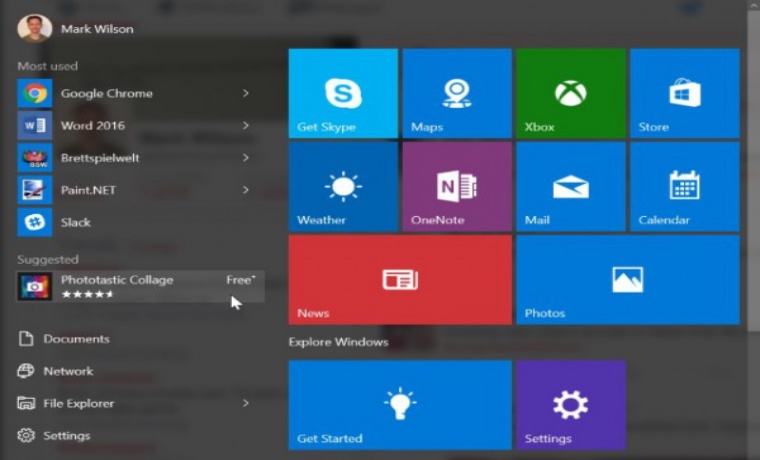
 179Geek
179GeekWindows 10 Start Menu- Microsoft’s Chosen Platform for Displaying Online Ads
Microsoft’s Windows 10 is known for collecting personal data of its users, but who thought the firm will be forcefully displaying ads...
-
 204Cyber Crime
204Cyber CrimeKosovan Hacker Detained in Malaysia for Hacking, Sharing Military Data to IS
A Kosovan man named Ardit Ferizi has been arrested in Malaysia for suspected hacking of US military databases comprising of personal information of...
-

 156News
156NewsDid Russians Hack Dow Jones for Trading Tips?
Dow Jones Hacked by Russians for Obtaining Trading Tips — No one knows how much money the made. A group of Russian...
-

 151Data Security
151Data SecurityYahoo only the latest at “kill the password” altar
Industry looking to improve access controls and authentication, but decisions still governed by security requirements, use cases, hacker disruption. Yahoo this week...
-

 163Data Security
163Data SecurityRussian Hackers of Dow Jones Said to Have Sought Trading Tips
A group of Russian hackers infiltrated the servers of Dow Jones & Co., owner of the Wall Street Journal and several other...
-

 89Vulnerabilities
89VulnerabilitiesFirst Major Ubuntu Touch Exploit Is a Wake-up Call for Canonical
Developers have been quick to fix the problem. An important security issue on Ubuntu phone that has been revealed this morning has been...
-

 163Malware
163MalwareMicrosoft is ready to save your PC from huge ransomware infection
TeslaCrypt doesn’t mean anything to many PC users, but there are thousands of people who have somehow contracted this infectious malware program that...
-
 277Hacked
277HackedInternet Inventor Vint Cerf and Experts Suggest 5-Points to Improve WiFi Router Security
Short Bytes: The FCC is on the receiving end over its proposed rules to alter WiFi routers to make them secure as...
-

 198Geek
198GeekHere are few things you should know about Facebook privacy before it’s too late
Facebook is a great platform for those who are looking for new friends, finding old ones or to promote their business. In...
-

 193Incidents
193IncidentsUltraDNS Server Problem Pulls Down Websites, Including Netflix, for 90 Minutes
UltraDNS, a web content delivery service, went down Thursday afternoon, taking with it a number of popular websites, including Netflix and Expedia....
-
 274Hacked
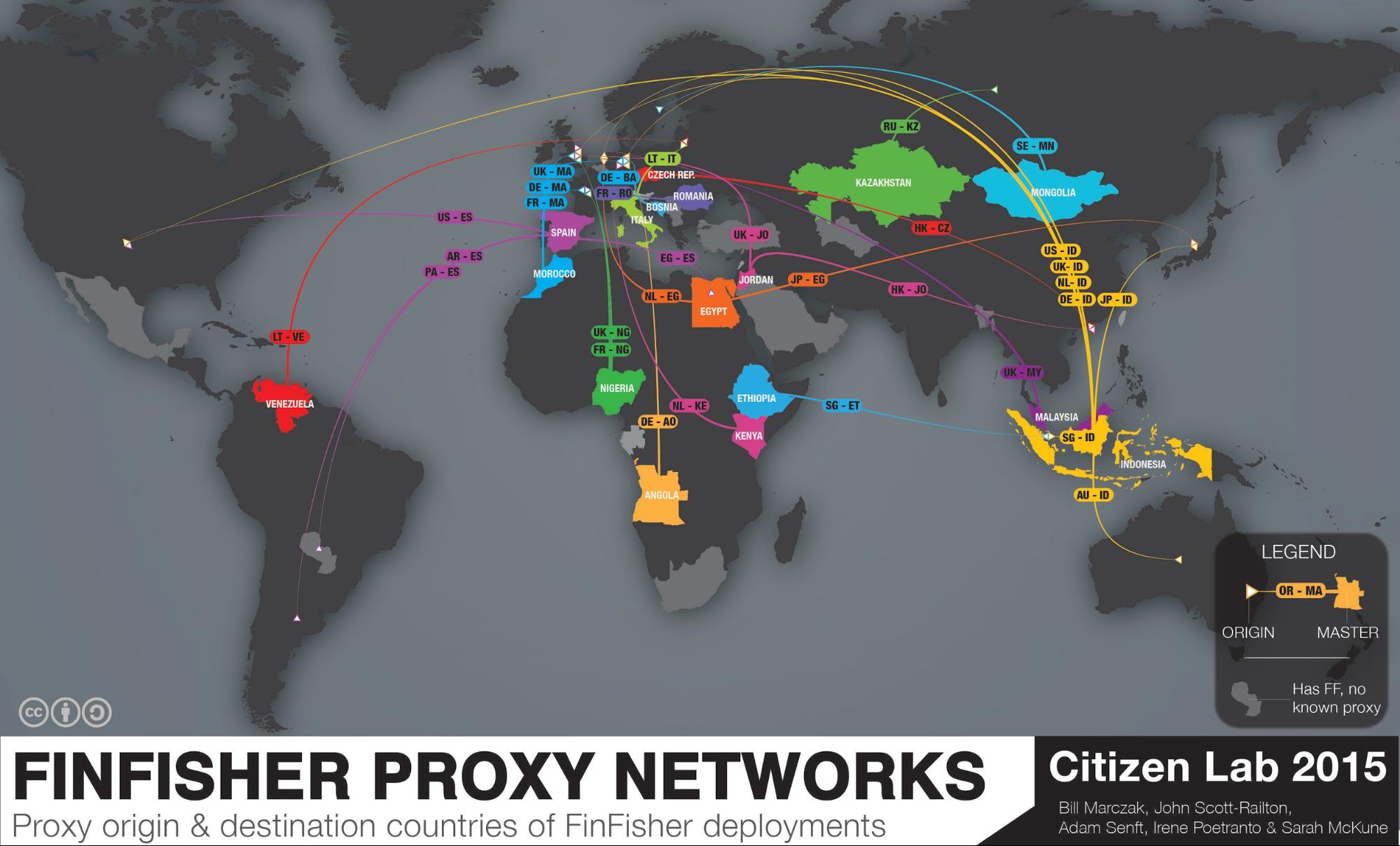
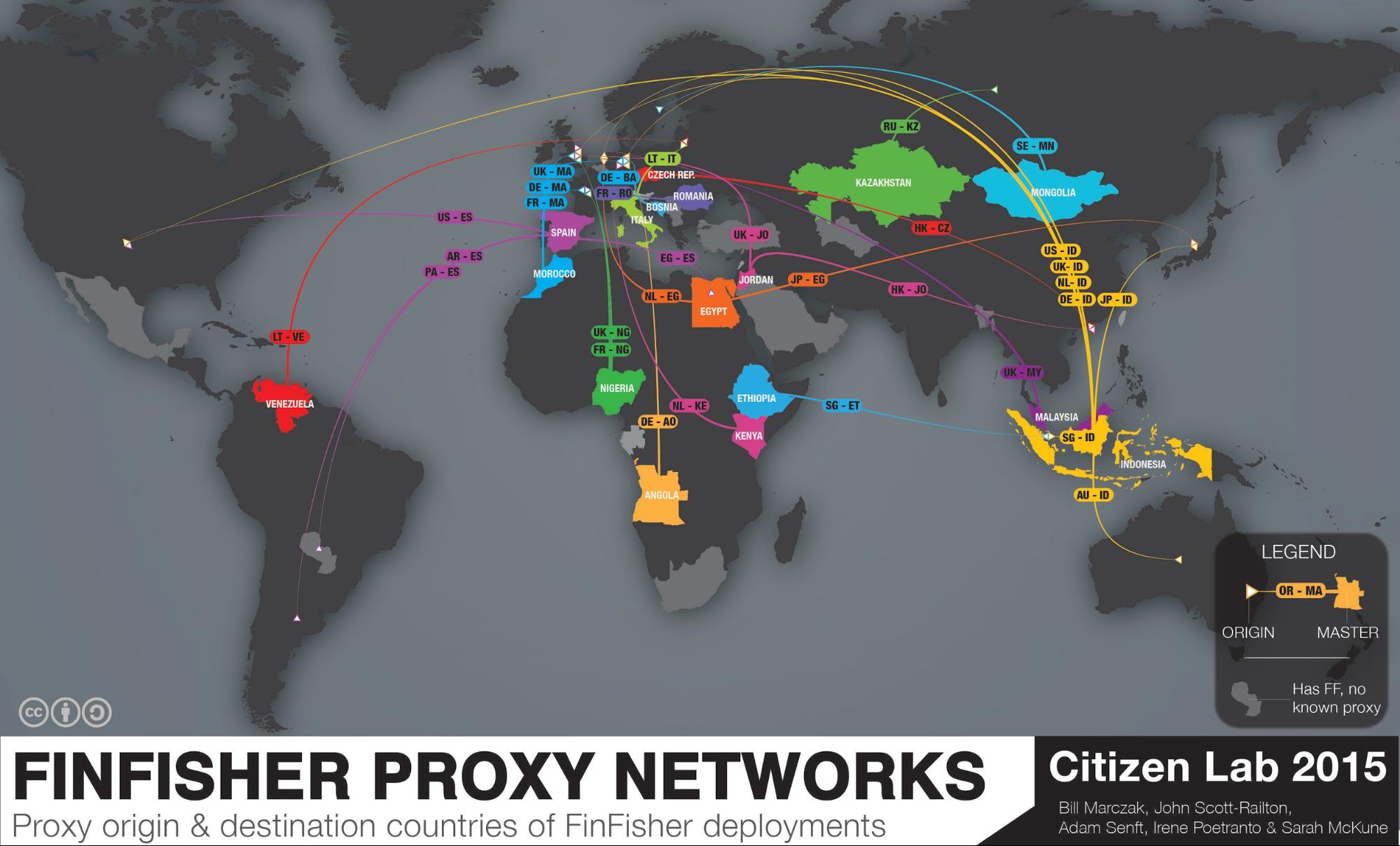
274HackedThis Nearly “Impossible to Trace” Spyware is Used by 32 Governments to Spy on You
Short Bytes: In 2015, the infamous spyware FinFisher is spread in 32 countries to perform advanced citizen surveillance. Citizen Lab, a security watchdog,...
-
 175Data Security
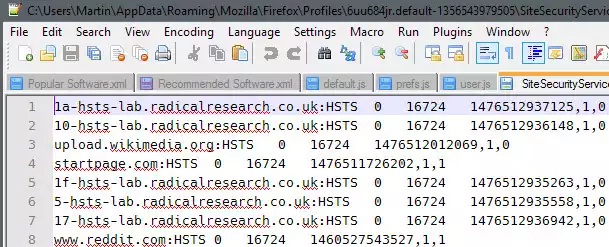
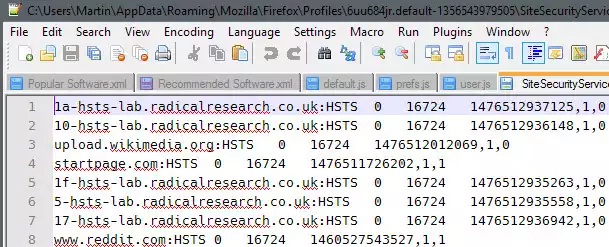
175Data SecurityHow to prevent HSTS tracking in Firefox
HTTP Strict Transport Security (HSTS) was designed to help secure websites (those using HTTPS) by declaring to web browsers that they should...
-

 173Hacked
173HackedFacebook Scans Your Phonebook To Guess Who You Are Dating Online
Short Byte: In a bizarre incident, Facebook users are reportedly seeing increasing friend suggestions of the people they have dated before through...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




