Featured News
-

 171Hacked
171HackedHow An Attacker Can Kill Your Phone and PC by Making It Older and Some “MAGIC”
Short Bytes: The researchers at NYU have revealed a way of attacking electronic devices by accelerating the aging of electronic chips. The...
-
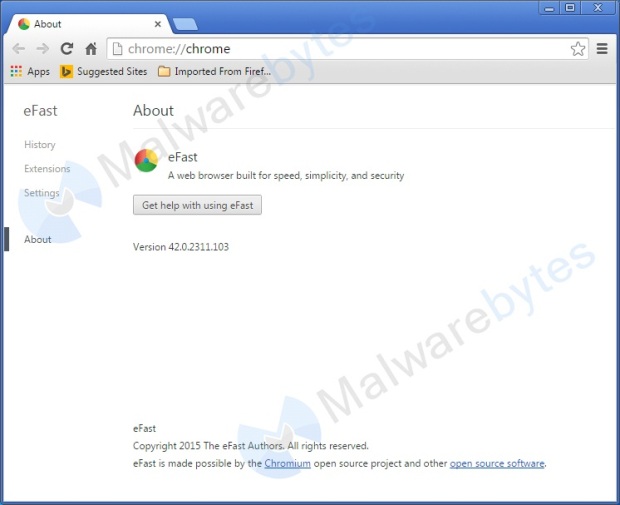
 148Malware
148MalwareTricky new malware replaces your entire browser with a dangerous Chrome lookalike
This malicious browser looks and acts just like Chrome–except for all the pop-up ads, system file hijacking, and activity monitoring. Security researchers...
-

 157Data Security
157Data SecurityX-Ray Scans Expose an Ingenious Chip-and-Pin Card Hack
THE CHIP-ENABLED CREDIT card system long used in Europe, a watered down version of which is rolling out for the first time...
-
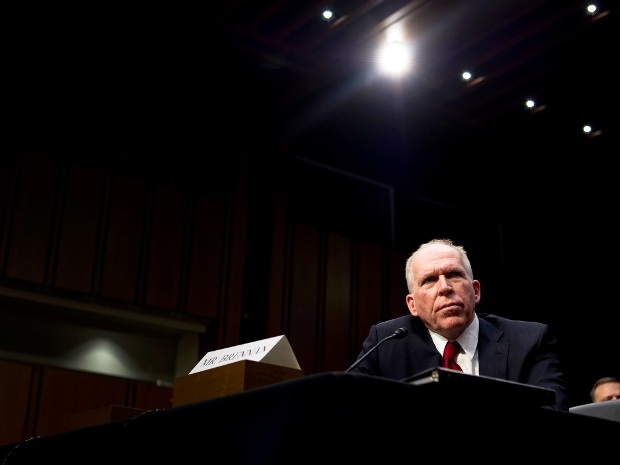
 116Incidents
116IncidentsTeen Who Hacked CIA Director’s Email Tells How He Did It
A HACKER WHO claims to have broken into the AOL account of CIA Director John Brennan says he obtained access by posing...
-
 174Geek
174GeekSecurity Agencies Eager to Get Hold of User Data: Microsoft’s Transparency Report
Microsoft announced the launch of a new transparency website in order to provide free access to the transparency reports published by the...
-
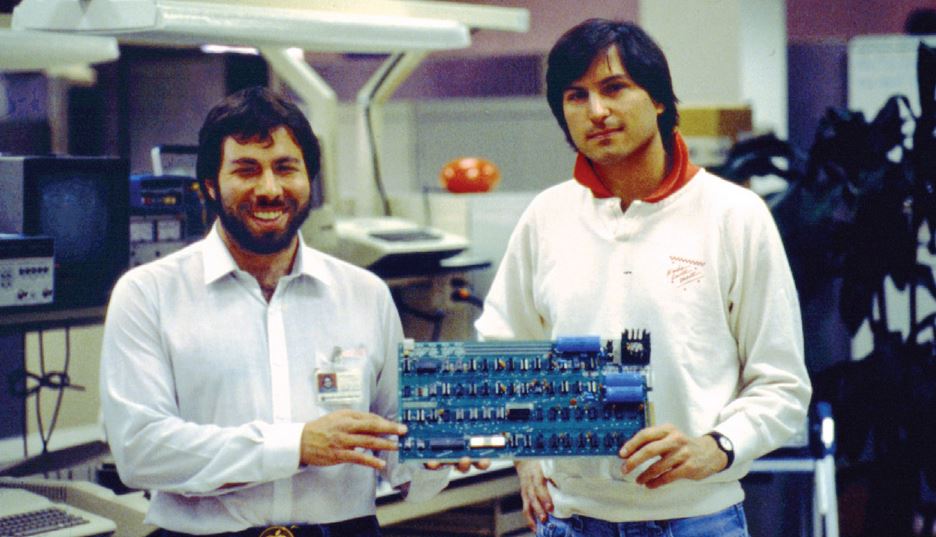
 197Lists
197ListsWho Were the First 10 Employees Of Apple and What Happened to Them?
Short Bytes: Each of the first 10 employees of Apple had made outstanding contributions to Apple in the field of design, funding,...
-
 183News
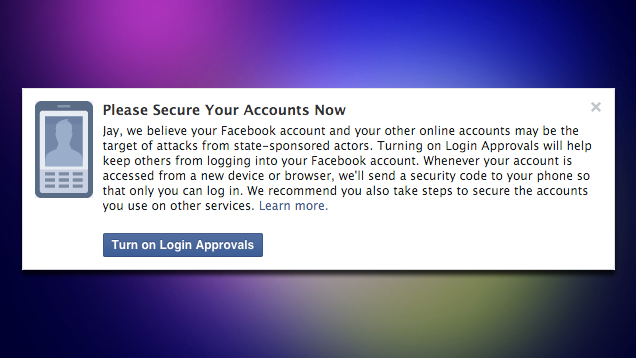
183NewsFacebook Will Warn You If It Thinks a Government Is Attacking Your Account
If you haven’t enabled two-factor authentication on Facebook, you should. If Facebook thinks someone has attempted to access your account, it will...
-
 134Geek
134GeekFacebook will notify you if the government is trying to get into your account
Facebook accounts are notorious for being hacked, either through poor passwords or phishing scams. So to help keep its users safe, the...
-

 217Vulnerabilities
217VulnerabilitiesMagento Websites Exploited in Massive Malware Distribution Campaign
A recently discovered zero-day bug may be at fault.Security researchers from both Sucuri and Malwarebytes have observed a recent massive malware distribution...
-

 301Hacked
301HackedFacebook Will Tell You if Your Government is Trying to HACK You
Short Bytes: To make your favorite social network more secure, Facebook is now sending out notifications to the compromised accounts. Facebook mentions...
-

 166Data Security
166Data SecurityResearchers find 256 iOS apps that collect users’ personal info
Apps are “definitely the kind of stuff that Apple should have caught,” researcher says. Researchers said they’ve found more than 250 iOS...
-

 110Data Security
110Data SecurityFacebook Will Warn Users When State-Sponsored Groups Are Trying to Hack Their Accounts
Facebook will now detect when state hackers are trying to hijack accounts, and alert users when it happens Alex Stamos, Chief Security...
-

 261Hacked
261HackedYour Password Manager 1Password Leaks Your Account’s Important Metadata
Short Bytes: 1Password, a password manager feature has been found to leak traces of the user account’s metadata which could be exploited...
-
 208Hacked
208HackedWhy ISIS is Trying Hard to Hack America’s Energy Grid – and Failing Terribly
Short Bytes: According to the latest revelations made by the American law enforcement agencies, ISIS terrorists are failing hard at hacking the...
-
 182Incidents
182IncidentsAnonymous Shut Down Japanese Airport websites against Dolphin Slaughter
The online hacktivist Anonymous conducted powerful DDoS attacks on the official websites of two of the Japan‘s busiest airports and forced them...
-
 173Vulnerabilities
173VulnerabilitiesSMTP bug-hunt turns up vuln in LibreSSL
Code reviewers looking over a mail daemon have turned up a couple of reasonably serious bugs in the Libre SSL code base...
-
 172Data Security
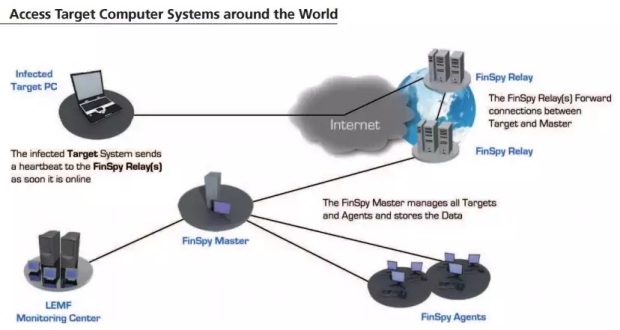
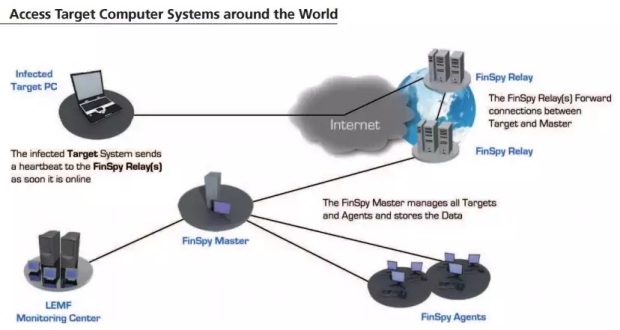
172Data SecurityFinFisher Spyware Becomes More Popular Among Government Agencies
The number of countries deploying it grows to 32.FinFisher, a piece of spyware sold to governments by a German security vendor, has...
-

 253News
253NewsUndisputed Hacker Group Fin5 Stole 150000 Credit Cards From Casinos
Two security firms (FireEye and Mandiant), have found a group of hackers (Fin5) who specialize in credit card stealing and have till date stolen...
-

 272Geek
272GeekLTE Security Flaw Puts Android Devices Vulnerable to DDoS Attack
An alert from Carnegie Mellon University CERT database reveals how Android devices are affected by LTE security flaw and use for DDoS...
-

 241Tricks & How To's
241Tricks & How To'sRemove Your Phone Number from TrueCaller
Over the past few months, TrueCaller has helped us in tracing the mobile number well ahead in advance, before picking up the phone....
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




