Featured News
-

 197Lists
197ListsBest Flying Cars of The Future, Pick Your Ride
Short Bytes: Flying cars dream would soon change into a reality. So, get ready and pick your ride in advance. Good luck...
-

 196Vulnerabilities
196VulnerabilitiesWordPress Fixes Critical Stored XSS Error in Akismet
Developers at Automattic, the parent company behind the blogging platform WordPress, fixed a nasty stored cross-site scripting error this week in Akismet,...
-

 75Data Security
75Data SecurityBrolux trojan targeting Japanese online bankers
A banking trojan, detected by ESET as Win32/Brolux.A, is targeting Japanese internet banking users and spreading through at least two vulnerabilities: a...
-

 133Data Security
133Data SecurityHow the NSA can break trillions of encrypted Web and VPN connections
Researchers show how mass decryption is well within the NSA’s $11 billion budget. For years, privacy advocates have pushed developers of websites,...
-

 168Geek
168GeekHackers show Google Now and SIRI can be hacked via Radio waves
Hacking SIRI and Google Now silently from 16feet away now possible via Headphones, claim ANSSI Researchers. French researchers at the government’s information...
-
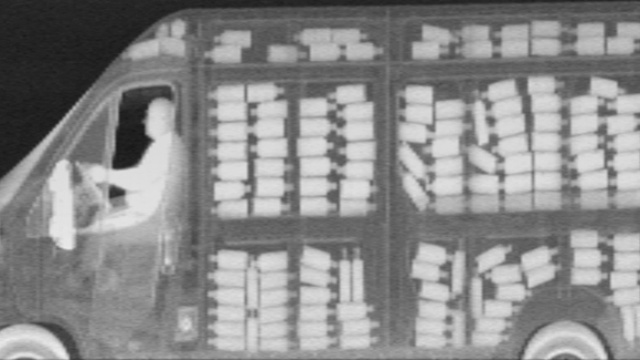
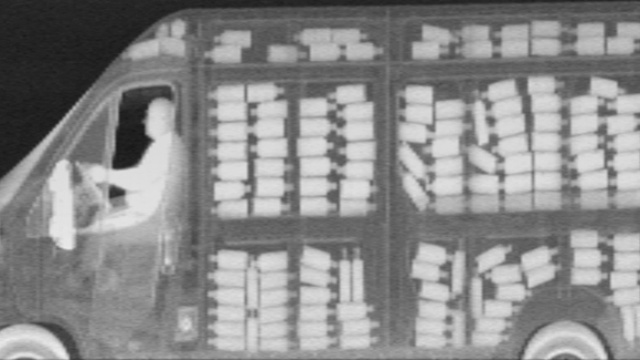 272Surveillance
272SurveillanceEverything in New York to be X-rayed as NYPD brings in X-ray vans
Extremely secretive spy vehicles equipped with X-ray facility, Z Backscatter, will now be seen patrolling the city streets — NYPD hasn’t disclosed...
-

 119Geek
119GeekPost popularity exposed on Facebook, thanks to a new bug
For a Facebook marketer, the most important statistic is how many people have viewed their post and although Facebook provides details regarding...
-
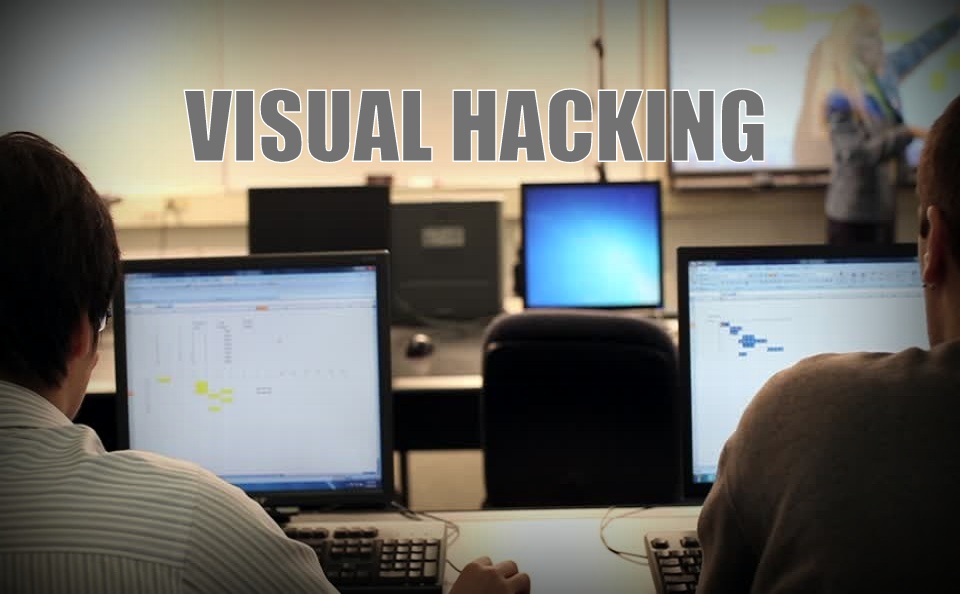
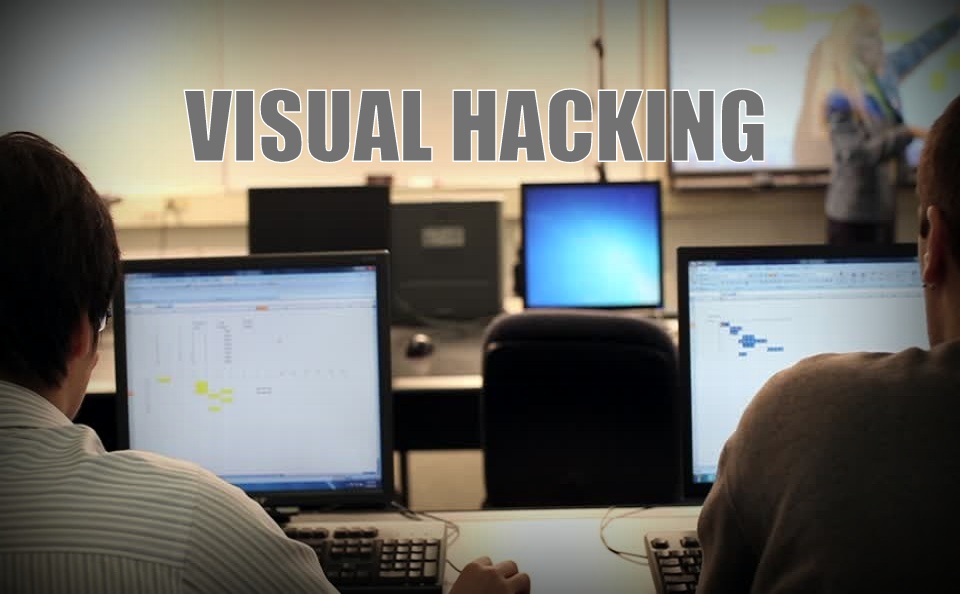 263Hacked
263Hacked“You Can Hack a Computer Just by Looking at It” – HP Explains Visual Hacking
Short Bytes: Visual Hacking is a security threat that is often overlooked by us. This is the act of stealing information by...
-

 306Hacked
306HackedExplained: How Criminals Hack Your Chip And Pin Card
Short Bytes: EMV credit cards have till now been assumed to be unhackable. The security professor from the University of California explains how...
-

 86Data Security
86Data SecurityVideo Explainer: How Criminals Can Easily Hack Your Chip & PIN Card
You may be under the impression that the new EMV chip system for credit card payments is nice and secure. But the...
-

 166Data Security
166Data SecurityPrices of stolen data on the Dark Web
Over the years, the McAfee Labs team has worked with IT security vendors, law enforcement and others to identify and evaluate numerous...
-

 59Cyber Crime
59Cyber CrimeAdobe Flash is putting your computer at risk – and there’s no patch yet
Sooner or later you are going to have to address the Flash problem on your computers. And there doesn't seem a better...
-
 266Hacked
266HackedHere’s How Hackers Can Control Your Entire Digital Life in Minutes
Short Bytes: Continuing our “steps to effective security” series, we are here with a true story that tells about the basic security...
-
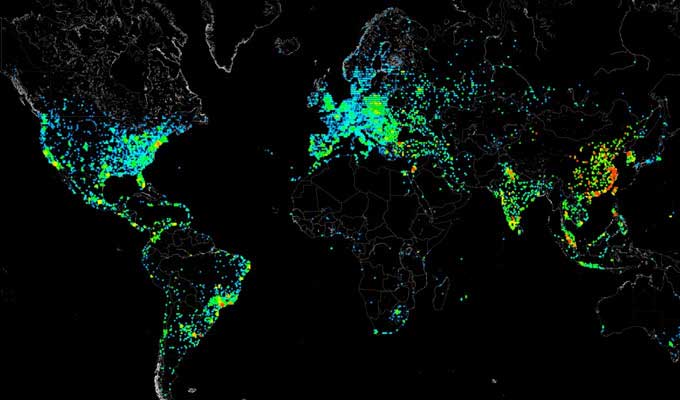
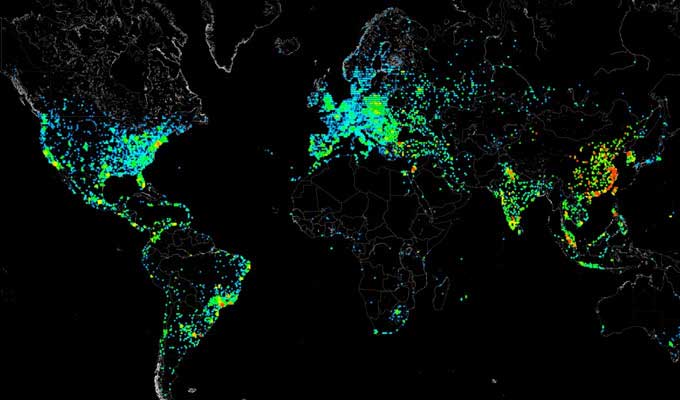 159Data Security
159Data SecurityHow to scan whole Internet 3.7 billion IP addresses in few minutes?
Cyber security audit and ethical hacking training professionals normally use scanner to scans the networks. Scanning every IP address on the internet...
-

 199Incidents
199IncidentsHackers being hunted after stealing $30.7M via malware
Global law enforcement agencies have arrested a gang member behind the theft of £20 million ($30.7 million) via a piece of malicious...
-
 235Lists
235Lists5 Free PDF Password Remover Software to Crack Any Protected File
Short Bytes: Forgetting PDF passwords is something that happens to us all the time. In this article, I’m here with the 5...
-

 173Cyber Events
173Cyber EventsDownloading movies, music can hand you the status of a criminal under TPP
The Internet will soon be quite different, as downloaders of illegal software, movies and songs will be seen as criminals and will...
-

 211Hacked
211HackedCanadian Military Is Recruiting Car Hackers, Anyone Up For It?
Short Bytes: Car hacking is illegal as we know it, but if you have the skill, you can work for the Canadian military. ...
-

 154Vulnerabilities
154VulnerabilitiesMagento database tool Magmi has a zero-day vulnerability
Magento has contacted the websites that appear to be vulnerable, Trustwave said. An open-source tool for importing content into the Magento e-commerce...
-
 175Hacked
175HackedMicrosoft Releases Critical Security Fix For All Version of Windows, Download Now
Short Bytes: Microsoft has issued critical security fixes as a part of this month’s patch Tuesday. Users are advised to download these...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




