Featured News
-

 207Vulnerabilities
207VulnerabilitiesEuropean Aviation Agency Warns of Aircraft Hacking
The director of one of Europe’s top aviation agencies warned on Thursday that hackers could infiltrate critical systems in an airplane on...
-

 243Cyber Events
243Cyber EventsSaudi Wife May Face Prison For Uploading Video of Cheating Husband
A Saudi woman created a furor by scandalizing her cheating husband by posting a video of him kissing their maid on social...
-

 249Hacked
249HackedDuckDuckGo Taunts Google: “You Don’t Need To Track Users To Make Money”
Short Bytes: DuckDuckGo CEO Gabriel Weinberg takes a dig at Google in his AMA session saying, “It is a myth you need...
-

 208Data Security
208Data Security2015 NOBEL PEACE PRIZE IS BETWEEN SNOWDEN, POPE AND MERKEL?
Today the Nobel Peace Prize 2015 will be announced. Will it be a controversial choice? The Nobel Committee will announce the 2015...
-

 210Data Security
210Data SecurityWordPress XML-RPC Service Used to Amplify Brute-Force Attacks
Hackers are hiding hundreds or thousands of username/password combinations in one single XML-RPC request. WordPress sites are being abused once again and there...
-

 477Cyber Crime
477Cyber CrimePublic Wi‑Fi: Convenience trumps risks
In the rush for convenience, we have overlooked security when it comes to public Wi-Fi. And, as this feature investigates, there are...
-

 302Hacked
302HackedHow to Keep Your WhatsApp Data Safe With Google Drive and Encryption
Short Bytes: To keep your WhatsApp data safe and encrypted, WhatsApp has partnered with Google Drive. Take a look to know how to...
-

 107Privacy
107PrivacyWebcam hacker spent up to 12 hours a day watching his victims
A hacker who used the notorious Blackshades RAT malware to hijack webcams on computers, and secretly watch people engaged in sexual activity,...
-
 160Vulnerabilities
160VulnerabilitiesDisclosed Netgear Router Vulnerability Under Attack
A vulnerability in Netgear routers, already disclosed by two sets of researchers at different security companies, has been publicly exploited. Netgear, meanwhile,...
-

 198Hacked
198HackedJournalist Convicted of Hacking With the Help of Anonymous, Could Face 25-Years Jail Time
Matthew Keys with his attorneys outside Federal Court in Sacramento. He was found guilty in the hacking case against L.A.Times and Tribune...
-

 202Hacked
202HackedThis Dangerous Malware Has the Ability to Root Your Smartphones
Short Bytes: A new malicious adware is here to make your lives harder. Kemoge adware has the ability to do some serious damage...
-

 168Hacked
168HackedGoogle’s Guardian: Parisa Tabriz ‘The Security Princess’
Short Bytes: “Parisa Tabriz-The Security Princess” is Google’s guardian who protects the tech giant from the ‘black hat’ attackers. She is Google’s biggest...
-

 139Malware
139MalwareWebcam hacker spied on sex acts with BlackShades malware
A Leeds-based hacker used a notorious piece of malware called BlackShades to spy on people via their webcams. Investigators from the National...
-
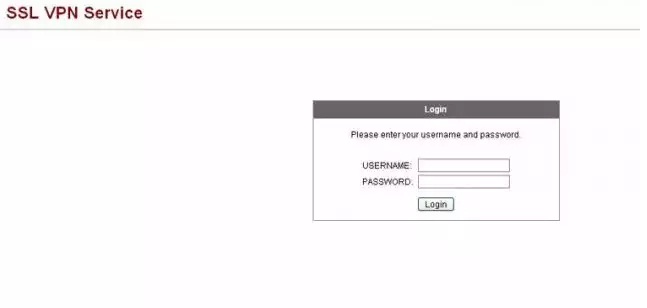
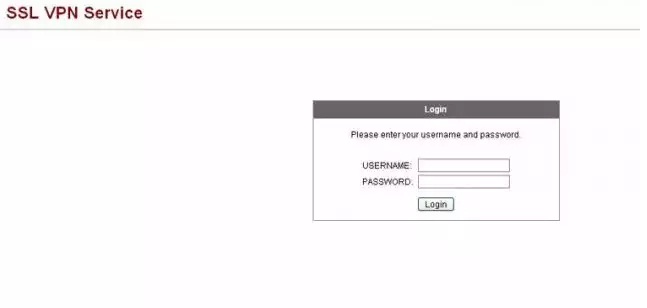 112Incidents
112IncidentsBackdoor infecting Cisco VPNs steals customers’ network passwords
Dozens of successful attacks detected that install malicious code on company portals. Attackers are infecting a widely used virtual private network product...
-

 146Geek
146GeekNew Android Malware “Kemoge” Spams Your Smartphone with Ads
Smartphones of Android users are again under a malware attack, this time with unsolicited unwanted ads. Did you know hackers develop Android malware...
-

 126Cyber Crime
126Cyber CrimeHacker Caught Spying on Users’ Webcams During Sexual Activities
A hacker named Stefan Rigo used intrusive software known as Blackshades to gain access and control over strangers’ webcams. The computers of a couple got hacked by...
-
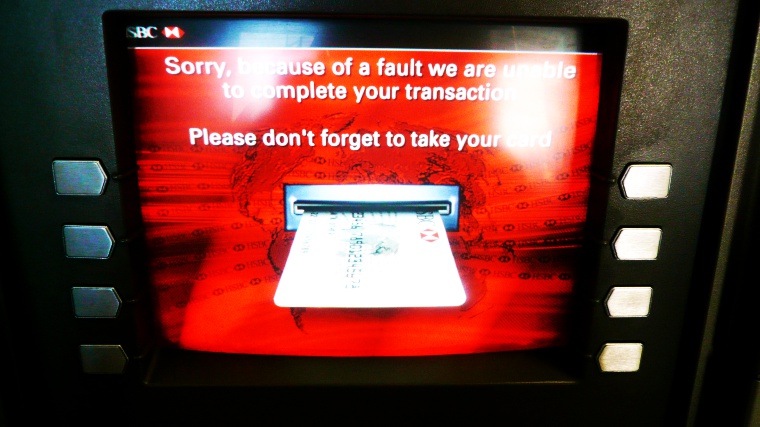
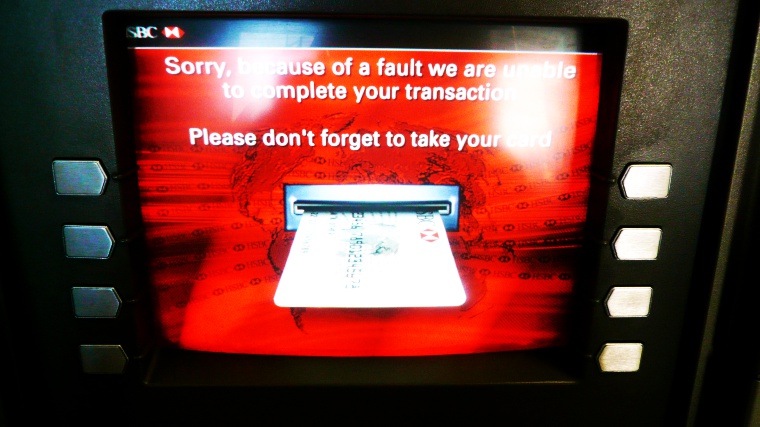 307Cyber Crime
307Cyber CrimeHackers Targeting ATMs with “GreenDispenser” Money Stealing Malware
The global security company ProofPoint has identified a suspicious malware on its radar capable of stealing money from an ATM faster than...
-

 173Data Security
173Data SecurityChinese Hackers Breached LoopPay, Whose Tech Is Central to Samsung Pay
Months before its technology became the centerpiece of Samsung’s new mobile payment system, LoopPay, a small Massachusetts subsidiary of the South Korean...
-

 662How To
662How ToHow To Enable Two-factor Authentication For Google, Facebook?
Short Bytes: Two-factor authentication is amongst many options, yet one of the most underestimated methods, to improve your online security. If you...
-

 165Data Security
165Data SecuritySHA1 algorithm securing e-commerce and software could break by year’s end
Researchers warn widely used algorithm should be retired sooner. SHA1, one of the Internet’s most crucial cryptographic algorithms, is so weak to...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




