Featured News
-
 173Vulnerabilities
173VulnerabilitiesKemoge Android Adware Campaign Can Lead to Device Takeover
Google has been busy removing a number of apps from Google Play that are disguised as popular selections that are actually pushing...
-
 187Hacked
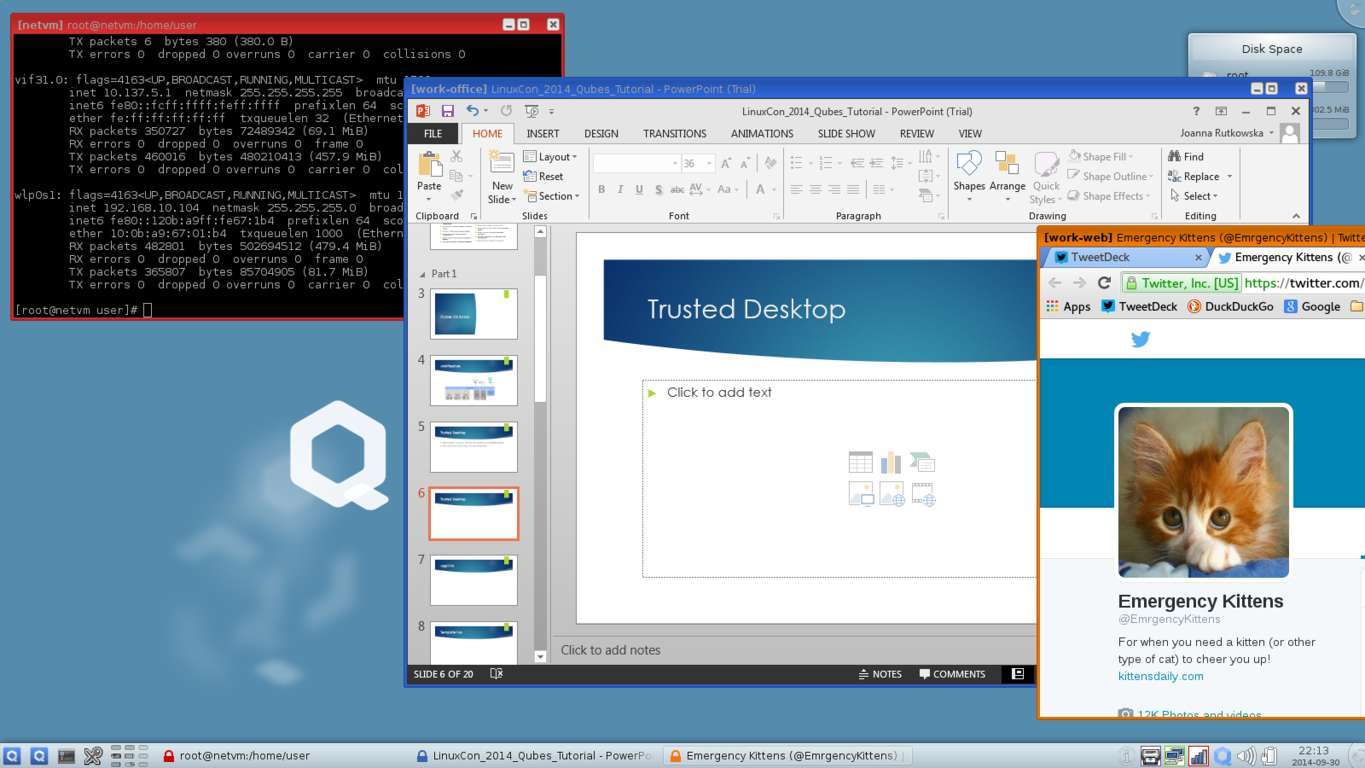
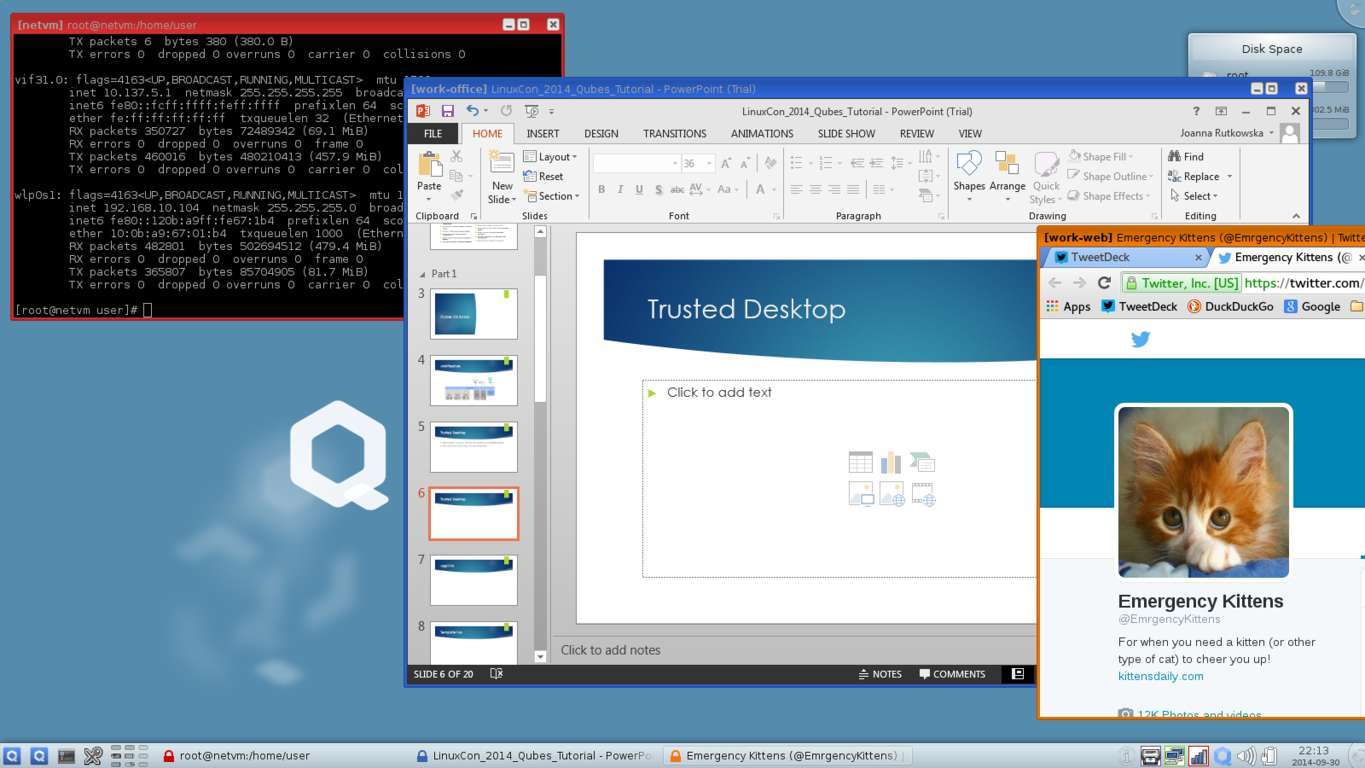
187HackedFree and Secure Qubes OS Protects You By Assuming that It’s Already Hacked
Short Bytes: Qubes OS is a free and open-source software (FOSS) that takes the security standards to a new level. It makes use...
-

 221Hacked
221HackedGoogle Expert Detects Zero-Day Exploit in Avast Antivirus
Short Bytes: Avast was detected with a serious zero-day exploit by a Google security expert. The antivirus software was vulnerable to malicious...
-

 107Data Security
107Data SecurityNew Moker RAT Bypasses Detection
Researchers warned Tuesday the latest APT to make the rounds features a remote access Trojan that can effectively mitigate security measures on machines and grant...
-

 184Vulnerabilities
184VulnerabilitiesZero-Day Exploit Found in Avast Antivirus
Avast was vulnerable to malicious HTTPS connections. One of Google’s security experts found a zero-day exploit inside the Avast antivirus, which the company...
-

 184News
184NewsBrazilian Hackers Target Government Websites, Question Corruption and NSA Snooping
A group of Brazilian hackers took over a couple of government-owned domains on Sunday posing the question, if these websites are so easy...
-

 295News
295NewsMicrosoft Transforms Sci-Fi into Real Life with Wearable HoloLens Kit
Microsoft, at their Windows 10 Devices event in New York, unveiled the pricing and availability of the HoloLens Development Edition. During the...
-

 379Surveillance
379SurveillanceSnowden Exposes “Smurf Suite”, Reveals GCHQ Hacked Cisco Routers in Pakistan
Since joining Twitter, Edward Snowden is more active than ever. In his latest revelation, the whistleblower has claimed that the British intelligence agency...
-

 192Cyber Events
192Cyber EventsAnonymous Starts Operation Black October To Target Banking Sector
It’s time to Pull your Money Out of the Banks- Suggests the Online Hacktivist Group — Anonymous Takes Hacktivism to Another Level. The...
-

 205Opinion
205OpinionAre healthcare organizations ready to get serious about security … now?
ESET security researcher Lysa Myers looks at a few of the questions she has been hearing more often about the recent surfeit...
-

 118Scams
118ScamsWhatsApp scam extends into multiple countries and brands
IKEA, KFC, H&M and 7-Eleven are just a few popular brands that are being exploited by cybercriminals via WhatsApp. We take a...
-
 499Scams
499ScamsTech Support Scams: Top of the Pop‑Ups
Support scams and fake alerts are still big business. We look at scammer psychology and a little parapsychology.
-

 97Data Security
97Data SecurityCreators of the Benevolent Linux.Wifatch Malware Reveal Themselves
Linux.Wifatch’s creators call themselves The White Team.The Linux.Wifatch malware, also dubbed as the “vigilante malware” has been going around the Internet, infecting...
-

 224Hacked
224HackedBeijing is 100% Covered by the Skynet of Surveillance Cameras
Short Bytes: China, in its effort to improve its security during the National Holiday, covered entire Beijing under video surveillance. In the...
-

 256News
256NewsSouth Korean subway system hacked, North Korea a possible culprit
The Subway system at the heart of Seoul, South Korea was hacked in 2014 and a local lawmaker claims that the culprit...
-
 197Data Security
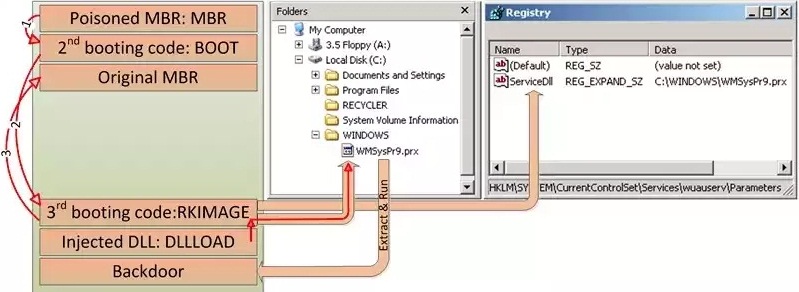
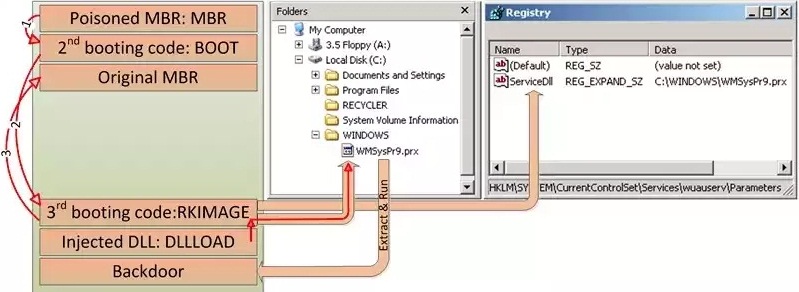
197Data SecurityHDRoot Bootkit Impersonates Microsoft’s Net Command
HDRoot is the work of the Winnti APT group. Hackers activating mainly in South-East Asia have developed a new bootkit trojan, which disguises...
-

 112Vulnerabilities
112VulnerabilitiesRemote code exec hijack hole found in Huawei 4G USB modems
Ruskies sling malicious packet to trigger denial of service. Positive Technologies researchers Timur Yunusov and Kirill Nesterov have found since-patched remote execution...
-

 160Vulnerabilities
160VulnerabilitiesCisco shuts down million-dollar ransomware operation
Group used Angler Exploit kit to push ransomware on unsuspecting Internet users. Security researchers have disrupted an online criminal operation they estimated...
-

 180Geek
180GeekBanking Malware Masked as PayPal App Targeting Android Users
Hackers are targeting users with fake PayPal app update email which actually comes with an embedded link of an Android banking malware....
-
 169Lists
169ListsWhich Phones Are Getting the Android 6.0 Marshmallow Update? The Complete List
Short Bytes: The Android 6.0 Marshmallow update party has begun and we are here with the complete list of devices that are getting...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets




