Featured News
-

 180Geek
180GeekBanking Malware Masked as PayPal App Targeting Android Users
Hackers are targeting users with fake PayPal app update email which actually comes with an embedded link of an Android banking malware....
-
 171Lists
171ListsWhich Phones Are Getting the Android 6.0 Marshmallow Update? The Complete List
Short Bytes: The Android 6.0 Marshmallow update party has begun and we are here with the complete list of devices that are getting...
-

 176Data Security
176Data SecurityMeet The New Virus Protecting Routers From Hackers
For hackers, routers are an easy target, perhaps because they are seldom updated and virus-scanned and are also easily cracked. But shockingly,...
-

 159Surveillance
159SurveillanceActivists Fly Drone Over NSA complex in Germany, Dropping Pamphlets Against Spying
Former NSA spy Edward Snowden may have exposed the government’s surveillance program around the world, but it didn’t change the way security...
-

 134Malware
134MalwareNew YiSpecter malware attacks iOS devices without jailbreak
A new malware identified as YiSpecter attacks iOS devices with and without jailbreak, researchers from Palo Alto Networks have revealed. ESET has...
-
 99News
99NewsPro-Palestinian Hackers Took over Radio Tel Aviv Website
A group of pro-Palestinian hackers took over the official website of Radio Tel Aviv (TLV) on Sunday and left a deface page...
-

 159Data Security
159Data SecurityHow I could hack internet bank accounts of Danish largest bank in a few minutes
In August I visited the Chaos Communication Camp near Berlin. Once every four years this great and world’s greatest hacker festival is...
-

 532Banking
532BankingJean‑Ian Boutin: Banking trojan threat is not going anywhere
In an exclusive for We Live Security, Jean-Ian Boutin, a malware researcher at ESET, shares his thoughts on the past, present and...
-

 117Incidents
117IncidentsDonald Trump’s hotel chain reveals hack ‘may have stolen credit card data’
Malware that was active for over a year could have ‘accessed payment card information as it was being inputted,’ Trump Hotel Collection...
-

 220Geek
220GeekCanonical is Organizing India’s First Ever Ubuntu Hackathon
Short Bytes: Canonical is organizing India’s first ever Ubuntu Hackathon in Bangalore between October 15-16, 2015. Know about different categories, great prizes...
-

 129Vulnerabilities
129VulnerabilitiesGoogle Pushes Stagefright 2.0 Patches to Nexus Devices
Google today patched the latest round of Stagefright vulnerabilities in Android, pushing them out as part of its latest over-the-air update to...
-
 281Hacked
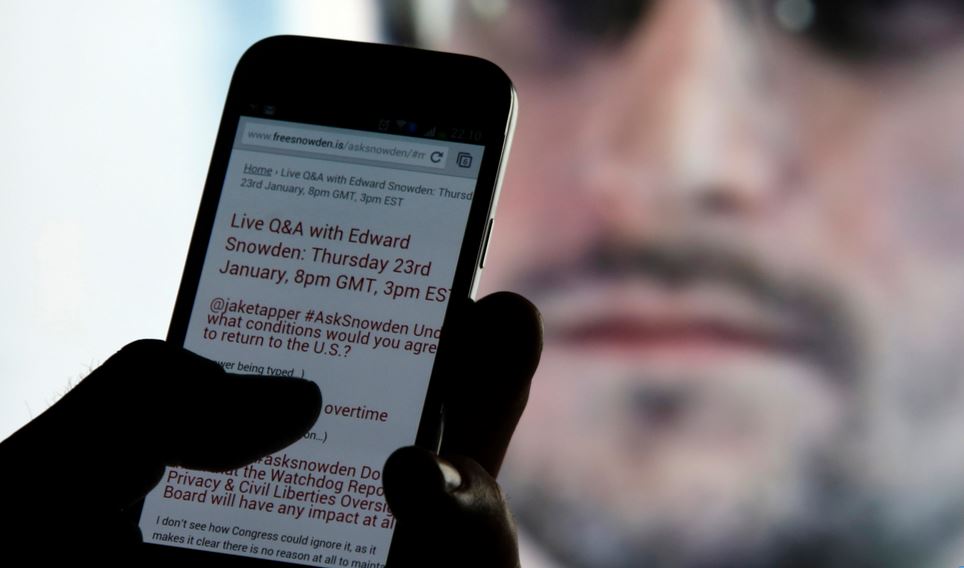
281HackedEdward Snowden: “Smartphones Can Be Easily Hacked With Just 1 Text Message”
Short Bytes: In a recent interview, Edward Snowden has said that spy agencies have lots of tools that could be used to...
-

 199Incidents
199IncidentsNew Outlook mailserver attack steals massive number of passwords
Backdoor in Outlook Web Application operates inside target’s firewall. Researchers have uncovered advanced malware that can steal virtually all of a large...
-

 205Malware
205MalwareMeet GreenDispenser: A New Breed of ATM Malware
On the heels of recent disclosures of ATM malware such as Suceful [1], Plotus [2] andPadpin [3] (aka Tyupkin), Proofpoint research has...
-

 280News
280NewsHackers show US Police Department Vehicles can be hacked
Security researchers Chris Valasek and Charlie Miller helped the world understand that late-model vehicles are vulnerable to cyber attacks. We have read...
-

 225Geek
225GeekYiSpecter- Latest Malware Hits iOS Devices
YiSpecter malware infects iOS devices by exploiting private APIs — Reports suggest, Chinese and Taiwanese users of iOS devices have been affected the most. According...
-
 58Cyber Crime
58Cyber CrimeCybercrime ‘more threatening than ever’
Cybercrime is more aggressive and confrontational than it has ever been, Europol's latest Internet Organised Crime Threat Assessment (IOCTA) has stated.
-

 137Incidents
137IncidentsA vigilante hacker is changing 10,000 Wi-Fi passwords
Someone is hacking unprotected Wi-Fi routers everywhere — and forcing them to be on guard. Does your home Wi-Fi use a default...
-

 187Hacked
187HackedNew Intel Skylake CPUs Now Making Your PCs More Secure Than Ever
Short Bytes: Intel has incorporated the new SGX security technology in its Skylake CPUs, further strengthening the platform. Intel’s Sixth generation super performers...
-

 179Data Security
179Data SecurityHacking Wireless Printers With Phones on Drones
YOU MIGHT THINK that working on a secured floor in a 30-story office tower puts you out of reach of Wi-Fi hackers...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




