Featured News
-

 254Hacked
254HackedDuckDuckGo Taunts Google: “You Don’t Need To Track Users To Make Money”
Short Bytes: DuckDuckGo CEO Gabriel Weinberg takes a dig at Google in his AMA session saying, “It is a myth you need...
-

 211Data Security
211Data Security2015 NOBEL PEACE PRIZE IS BETWEEN SNOWDEN, POPE AND MERKEL?
Today the Nobel Peace Prize 2015 will be announced. Will it be a controversial choice? The Nobel Committee will announce the 2015...
-

 211Data Security
211Data SecurityWordPress XML-RPC Service Used to Amplify Brute-Force Attacks
Hackers are hiding hundreds or thousands of username/password combinations in one single XML-RPC request. WordPress sites are being abused once again and there...
-

 483Cyber Crime
483Cyber CrimePublic Wi‑Fi: Convenience trumps risks
In the rush for convenience, we have overlooked security when it comes to public Wi-Fi. And, as this feature investigates, there are...
-

 306Hacked
306HackedHow to Keep Your WhatsApp Data Safe With Google Drive and Encryption
Short Bytes: To keep your WhatsApp data safe and encrypted, WhatsApp has partnered with Google Drive. Take a look to know how to...
-

 111Privacy
111PrivacyWebcam hacker spent up to 12 hours a day watching his victims
A hacker who used the notorious Blackshades RAT malware to hijack webcams on computers, and secretly watch people engaged in sexual activity,...
-
 163Vulnerabilities
163VulnerabilitiesDisclosed Netgear Router Vulnerability Under Attack
A vulnerability in Netgear routers, already disclosed by two sets of researchers at different security companies, has been publicly exploited. Netgear, meanwhile,...
-

 203Hacked
203HackedJournalist Convicted of Hacking With the Help of Anonymous, Could Face 25-Years Jail Time
Matthew Keys with his attorneys outside Federal Court in Sacramento. He was found guilty in the hacking case against L.A.Times and Tribune...
-

 207Hacked
207HackedThis Dangerous Malware Has the Ability to Root Your Smartphones
Short Bytes: A new malicious adware is here to make your lives harder. Kemoge adware has the ability to do some serious damage...
-

 173Hacked
173HackedGoogle’s Guardian: Parisa Tabriz ‘The Security Princess’
Short Bytes: “Parisa Tabriz-The Security Princess” is Google’s guardian who protects the tech giant from the ‘black hat’ attackers. She is Google’s biggest...
-

 142Malware
142MalwareWebcam hacker spied on sex acts with BlackShades malware
A Leeds-based hacker used a notorious piece of malware called BlackShades to spy on people via their webcams. Investigators from the National...
-
 116Incidents
116IncidentsBackdoor infecting Cisco VPNs steals customers’ network passwords
Dozens of successful attacks detected that install malicious code on company portals. Attackers are infecting a widely used virtual private network product...
-

 151Geek
151GeekNew Android Malware “Kemoge” Spams Your Smartphone with Ads
Smartphones of Android users are again under a malware attack, this time with unsolicited unwanted ads. Did you know hackers develop Android malware...
-

 130Cyber Crime
130Cyber CrimeHacker Caught Spying on Users’ Webcams During Sexual Activities
A hacker named Stefan Rigo used intrusive software known as Blackshades to gain access and control over strangers’ webcams. The computers of a couple got hacked by...
-
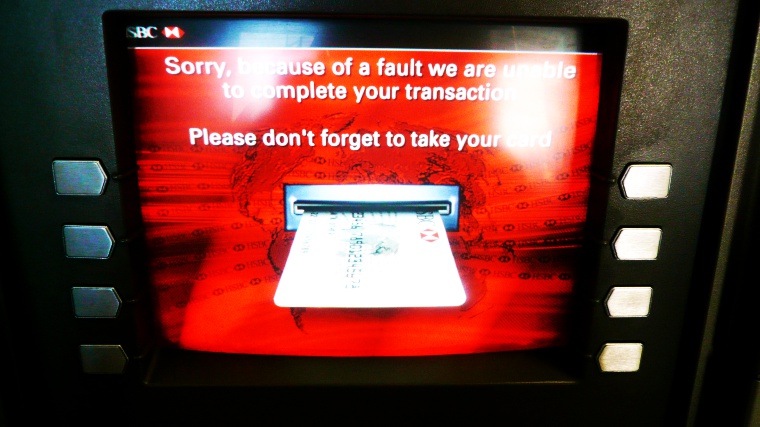
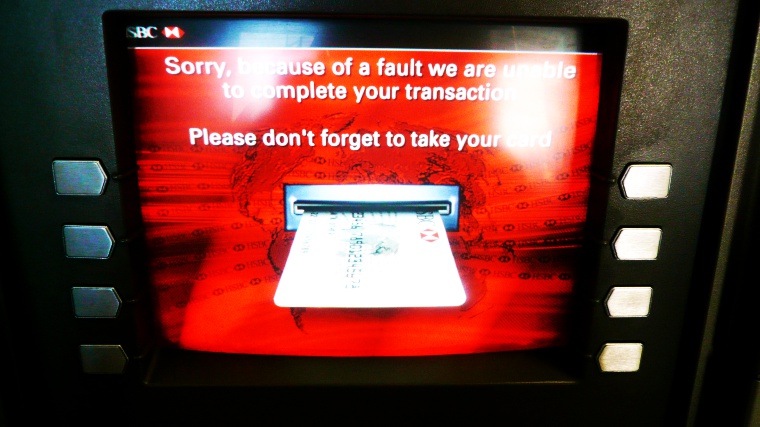 313Cyber Crime
313Cyber CrimeHackers Targeting ATMs with “GreenDispenser” Money Stealing Malware
The global security company ProofPoint has identified a suspicious malware on its radar capable of stealing money from an ATM faster than...
-

 176Data Security
176Data SecurityChinese Hackers Breached LoopPay, Whose Tech Is Central to Samsung Pay
Months before its technology became the centerpiece of Samsung’s new mobile payment system, LoopPay, a small Massachusetts subsidiary of the South Korean...
-

 668How To
668How ToHow To Enable Two-factor Authentication For Google, Facebook?
Short Bytes: Two-factor authentication is amongst many options, yet one of the most underestimated methods, to improve your online security. If you...
-

 169Data Security
169Data SecuritySHA1 algorithm securing e-commerce and software could break by year’s end
Researchers warn widely used algorithm should be retired sooner. SHA1, one of the Internet’s most crucial cryptographic algorithms, is so weak to...
-

 115Data Security
115Data SecurityBitcoin Transactions Were Under Attack for a Week, Prankster Reveals Himself
Transactions were being duplicated in a malleability attack.A Russian man that calls himself “Alister Maclin” has been disrupting the Bitcoin network for...
-
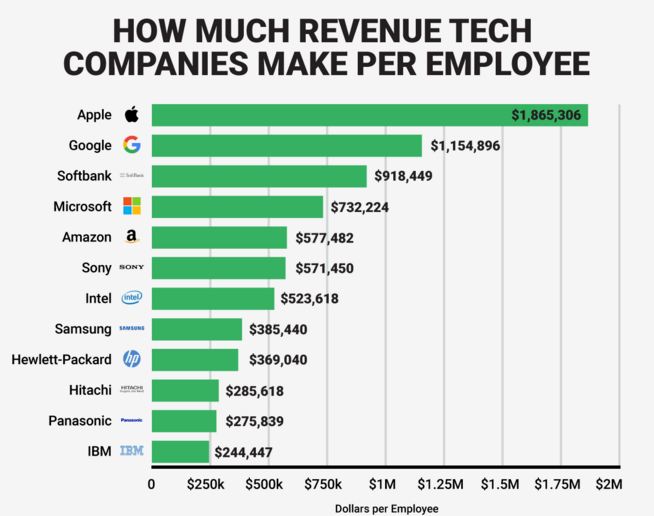
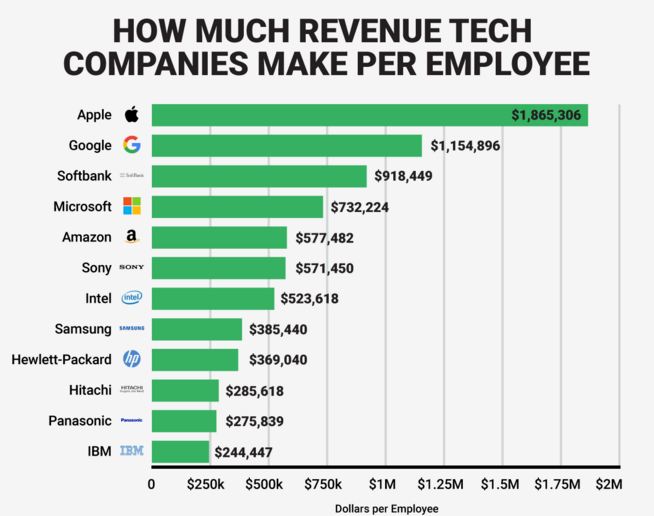 221Lists
221ListsHow Much Money Top Tech Companies Make Per Employee
Image Credit: BusinessInsider Short Bytes: Top tech giant like Google and Microsoft are worth billions and credit their working teams for the...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




