Featured News
-

 84Data Security
84Data SecurityUS Ports – Cyber attacks can cause the release of dangerous chemicals
US Ports are still vulnerable to cyber attacks that release dangerous chemicals, cybersecurity in the maritime industry is crucial for Homeland security....
-

 92Data Security
92Data SecurityVariants now spawning off new Android SMS malware
AndroidOS.SmsThief does what it says on the tin – acts as a thief through SMS, on Android. Mobile network security and threat...
-
 147Vulnerabilities
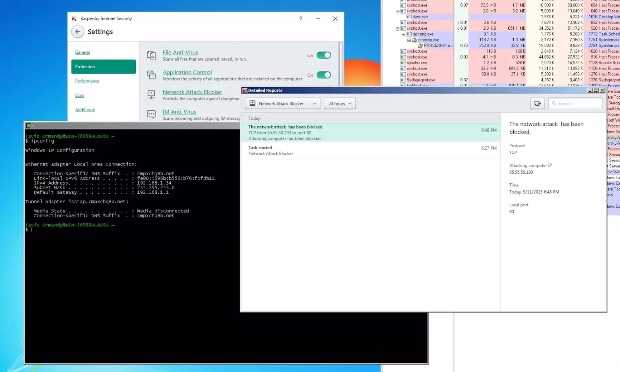
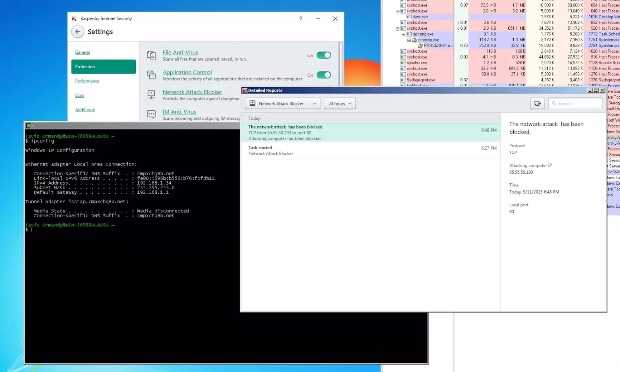
147VulnerabilitiesKaspersky Antivirus Fixes Bug That Allowed Attackers to Block Windows Update and Others Services
Attackers could have fooled Kaspersky antivirus in blocking Windows Update or some of its own update servers A vulnerability that allowed abuse...
-

 198Malware
198MalwareZeus Trojan and MWI Exploit Kit Used Against Israeli Public Sector
Security vendor interrupts hacking campaign targeting Israeli security firms, government agencies, and hospitals.Security experts have identified and isolated a series of attacks...
-

 109Vulnerabilities
109VulnerabilitiesBoffin’s easy remote hijack hack pops scores of router locks
Singaporean telco’s customer premises equipment is a gateway to security hell. Thousands of routers mandated for use by a major Singaporean telco...
-
 344Lists
344Lists10 Inventions That Make Nikola Tesla One Of The Greatest Scientists Of All Time
Short Bytes: Nikola Tesla, who is regarded as of the greatest scientists of all times, has gifted the world in every possible way...
-
 245Hacked
245HackedThis Computer Cluster Cracks Every Windows Password in 5.5-hours or Less
Short Bytes: A password-cracking expert has created a new computer cluster that cycles about 350 billion guesses per second and it can crack...
-

 218News
218News20 Sites to Download just about everything
Download Free Software,Movies, Music, Templates, WordPress themes, Blogger Themes and Icon pack with these websites. Theses are totally free websites for any...
-
 233Geek
233GeekLearn it Faster: The Complete Linux Kernel in a Single Map
Short Bytes: Today, we are sharing an interactive Linux Kernel map that will teach you the basics and understand the various subsystems....
-

 239Hacked
239HackedSurprise: For the First Time, USA Asked and China Arrested Hackers
Short Bytes: The Chinese government has taken an unprecedented step to comply with a U.S. request and arrest some hackers suspected of hacking...
-
 125News
125NewsTop 10 Android Apps for the lulz
Have you known that laughing may lengthen your life? If you install some amazing programs on your Android tablet, you will smile...
-

 251Geek
251GeekScammers Targeting Users with Shocking Video Facebook Scam
Social media sites are storehouses of people who are easily duped into believing almost anything which is posted and some proof of...
-

 164Geek
164GeekMan Charged with Animal Cruelty After Video Emerges on Facebook
A man is now in jail for having been part of a video that showed him abusing two dogs in Sioux Falls,...
-

 208Data Security
208Data SecurityCanadian Military to Hire Hackers to Improve Security of its Automotive System
The Canadian military, government and the Department of National Defence is reportedly in search for a contractor who can find vulnerabilities in...
-

 158Data Security
158Data SecurityIn a first, Chinese hackers are arrested at the behest of the U.S. government
The Chinese government has quietly arrested a handful of hackers at the urging of the U.S. government — an unprecedented step to...
-
 200Malware
200MalwareAbusing Windows Management Instrumentation (WMI) to Build a persistent, Asynchronous and Fileless Backdoor
Matt Graeber showed the method on performing WMI attacks and its effects, but he didn’t talk much about the details. Therefore, this...
-

 262Vulnerabilities
262VulnerabilitiesSecurity Researcher Disappointed with How an XSS Bug Was Fixed in Drupal 8
Researcher finds reflected XSS bug in Drupal 8.Drupal 8 isn’t even out yet but security experts have been hard at work auditing...
-

 111Data Security
111Data SecurityMatthew Keys’ Hacking Conviction May Not Survive an Appeal
HE CONVICTION OF former Reuters employee Matthew Keys on hacking charges this week has renewed focus on a controversial federal law that...
-

 214Vulnerabilities
214VulnerabilitiesEuropean Aviation Agency Warns of Aircraft Hacking
The director of one of Europe’s top aviation agencies warned on Thursday that hackers could infiltrate critical systems in an airplane on...
-

 252Cyber Events
252Cyber EventsSaudi Wife May Face Prison For Uploading Video of Cheating Husband
A Saudi woman created a furor by scandalizing her cheating husband by posting a video of him kissing their maid on social...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




