Featured News
-

 190Hacked
190HackedNew Intel Skylake CPUs Now Making Your PCs More Secure Than Ever
Short Bytes: Intel has incorporated the new SGX security technology in its Skylake CPUs, further strengthening the platform. Intel’s Sixth generation super performers...
-

 180Data Security
180Data SecurityHacking Wireless Printers With Phones on Drones
YOU MIGHT THINK that working on a secured floor in a 30-story office tower puts you out of reach of Wi-Fi hackers...
-

 182Data Security
182Data SecurityHow to Hack and Decrypt WhatsApp Database on rooted devices
The post includes a detailed procedure to hack and decrypt WhatsApp Database remotely on rooted Android mobile devices. Very Interesting!. A few...
-

 302Kids Online
302Kids OnlineThe best social networks for younger children
If you're looking to introduce your child to social networks and want peace of mind, look no further. Here are some of...
-

 292Hacked
292HackedYour Stolen/Hacked Identity is Sold Just For $1 in The Dark Web
Short Bytes: Increasing data breaches have made the personal identifiable information (PII) market very hot. The latest report outlines the different aspects...
-

 313Malware
313MalwareYiSpectre, the First iOS Malware That Attacks Non-Jailbroken Devices
The malware spreads with the help of an adult movie player. Security researchers at Palo Alto Networks have discovered and analyzed malware that...
-

 84Data Security
84Data SecurityVW’s ‘neat hack’ exposes danger of corporate software
It was only old-fashioned detective work that forced Volkswagen to admit to the existence of its ‘defeat device’. And that should worry...
-

 312Data Security
312Data SecurityHow to do hacking attacks over satellite communications?
Hack Satellite comunication In this article we will cover satellite based hacking attack which has been used by hacking groups since...
-

 381Data Security
381Data SecurityHOW TO INTERCEPT SATELLITE COMMUNICATIONS EASILY?
In today world we use satellite communication in many respects and industries and we all know how important they are in our...
-
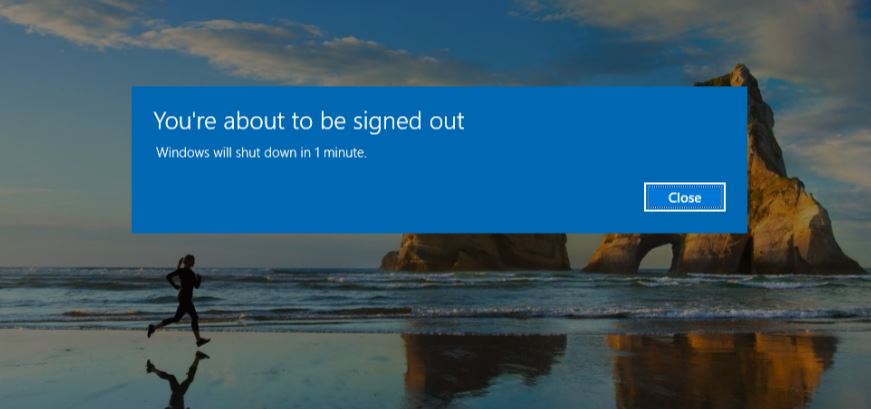
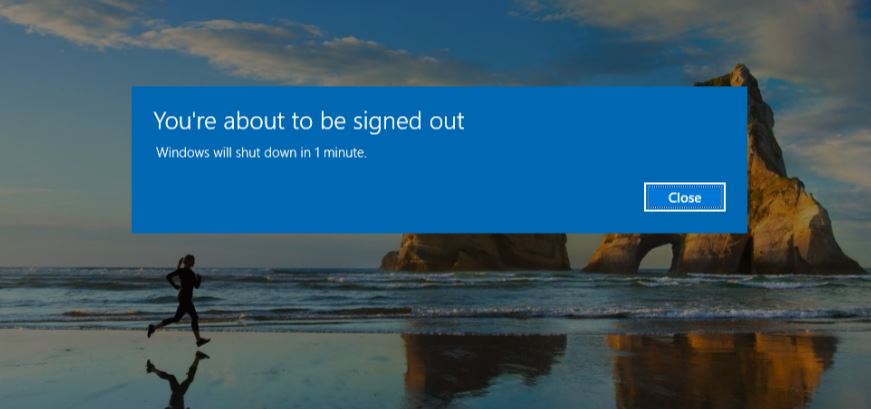 316How To
316How ToHow To Schedule A Shutdown For Windows OS?
Short Bytes: This article describes the steps to schedule a Shutdown command for Windows OS. Take a look. The very first task...
-
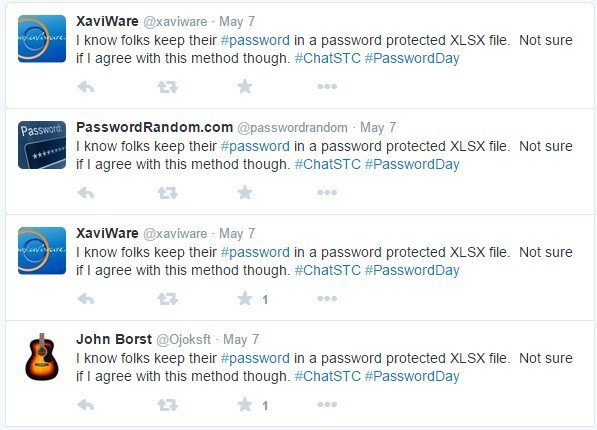
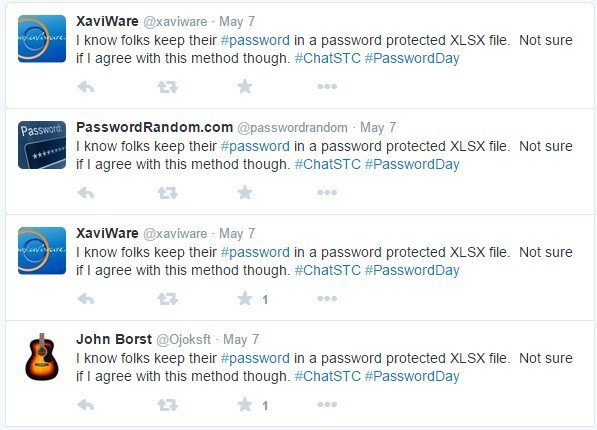 92How To
92How ToHow To Find The People Stealing Your Tweets On Twitter
This small piece of python code will find the people stealing your tweets and copy-pasting them on their twitter timeline. This python...
-
 259Geek
259GeekMS Word Vulnerability Exploited in Operation Pony Express to Spread Malware
Operation Pony Express was a spear-phishing campaign that was detected by Sophos researchers between April and May 2015. The research team identified...
-

 292Hacked
292HackedFirst Step to Effective Security – How to Know if You’ve Been Hacked
Short Bytes: Was your data compromised in the latest data breaches? How to know if you’ve been hacked? Here are the answers. The...
-
 282Geek
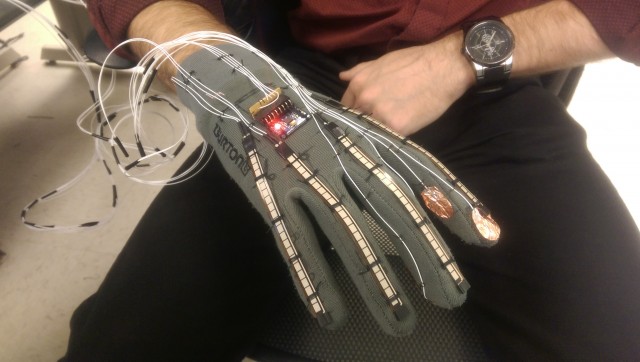
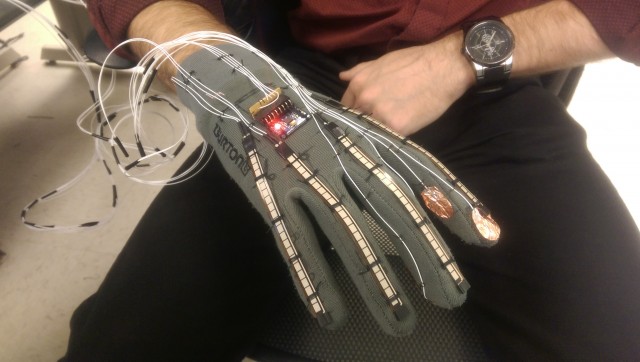
282GeekFuturistic Smart-Glove Can Translate Sign Language Into Text and Speech
Scientists are constantly working on user-friendly products for those with physical disabilities. In the past, these wearable glasses came out to help...
-

 113Geek
113GeekStagefright 2.0: Security Flaw in Android Puts 1 Billion Devices at Risk
The risk of remote hacking is triggered through the faults in the media processing components that may be misused by malicious websites....
-
 287Geek
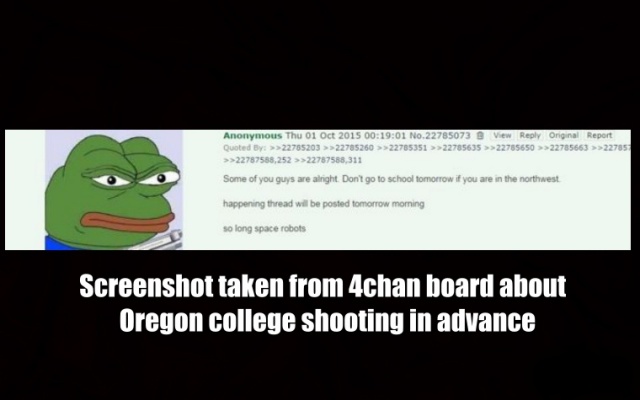
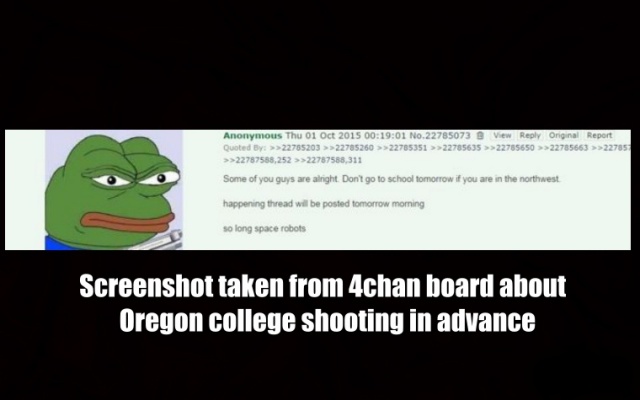
287GeekWas Oregon Shooting Predicted on 4chan?
Someone used 4chan to post about Oregon college shooting in the US before it actually took place. The sudden increase of Internet users...
-
 473Geek
473GeekWhat is Free and Open Source Software (FOSS) and Why You Should Use it?
Short Bytes: FOSS (Free And Open Software) is the modern day result of the free software movement that draws its philosophies from...
-

 106Malware
106MalwareDangerous resurgent banking malware hits UK
Bank trojan twin pivots to smash supply chain biz. The formidable Dyreza and Dridex banking malware are back in renewed and rejigged...
-

 126Malware
126MalwareAndroid Malware Disguises as PayPal App
A recent spam campaign is leading users to a fake PayPal app which steals their real credentials, but also comes hard-coded to...
-

 314Cyber Crime
314Cyber CrimeFBI Caught Paedophile By Infecting Tor Web Browser
Do you think that using anonymity software like Tor will protect your online presence from spies? A new spyware has been developed...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




