Featured News
-

 180Data Security
180Data SecurityMeet The New Virus Protecting Routers From Hackers
For hackers, routers are an easy target, perhaps because they are seldom updated and virus-scanned and are also easily cracked. But shockingly,...
-

 163Surveillance
163SurveillanceActivists Fly Drone Over NSA complex in Germany, Dropping Pamphlets Against Spying
Former NSA spy Edward Snowden may have exposed the government’s surveillance program around the world, but it didn’t change the way security...
-

 138Malware
138MalwareNew YiSpecter malware attacks iOS devices without jailbreak
A new malware identified as YiSpecter attacks iOS devices with and without jailbreak, researchers from Palo Alto Networks have revealed. ESET has...
-
 104News
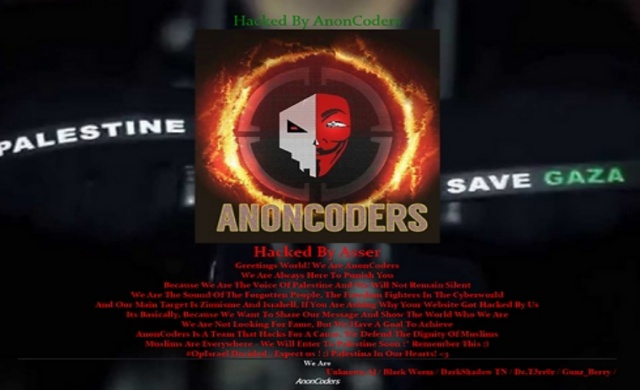
104NewsPro-Palestinian Hackers Took over Radio Tel Aviv Website
A group of pro-Palestinian hackers took over the official website of Radio Tel Aviv (TLV) on Sunday and left a deface page...
-

 162Data Security
162Data SecurityHow I could hack internet bank accounts of Danish largest bank in a few minutes
In August I visited the Chaos Communication Camp near Berlin. Once every four years this great and world’s greatest hacker festival is...
-

 541Banking
541BankingJean‑Ian Boutin: Banking trojan threat is not going anywhere
In an exclusive for We Live Security, Jean-Ian Boutin, a malware researcher at ESET, shares his thoughts on the past, present and...
-

 119Incidents
119IncidentsDonald Trump’s hotel chain reveals hack ‘may have stolen credit card data’
Malware that was active for over a year could have ‘accessed payment card information as it was being inputted,’ Trump Hotel Collection...
-

 223Geek
223GeekCanonical is Organizing India’s First Ever Ubuntu Hackathon
Short Bytes: Canonical is organizing India’s first ever Ubuntu Hackathon in Bangalore between October 15-16, 2015. Know about different categories, great prizes...
-

 132Vulnerabilities
132VulnerabilitiesGoogle Pushes Stagefright 2.0 Patches to Nexus Devices
Google today patched the latest round of Stagefright vulnerabilities in Android, pushing them out as part of its latest over-the-air update to...
-
 288Hacked
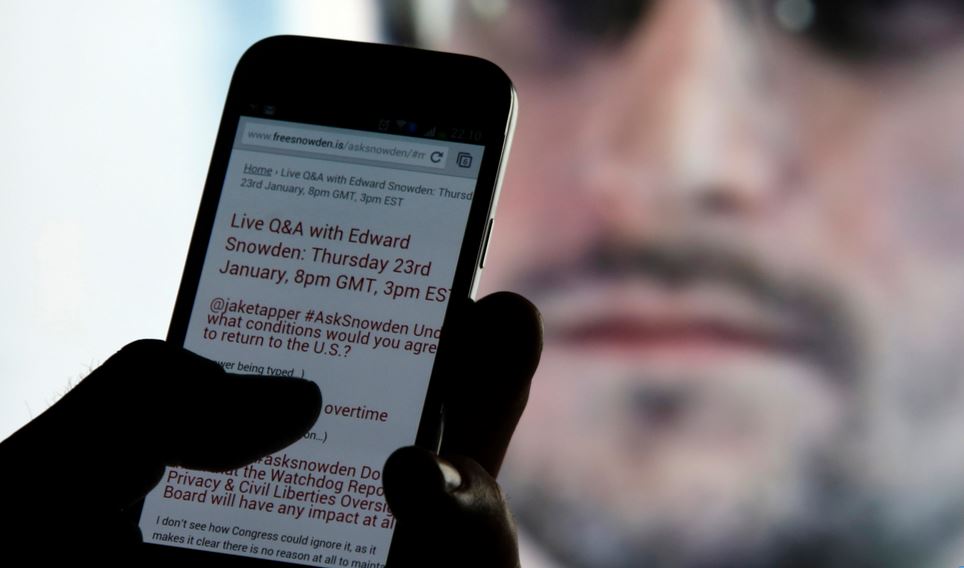
288HackedEdward Snowden: “Smartphones Can Be Easily Hacked With Just 1 Text Message”
Short Bytes: In a recent interview, Edward Snowden has said that spy agencies have lots of tools that could be used to...
-

 202Incidents
202IncidentsNew Outlook mailserver attack steals massive number of passwords
Backdoor in Outlook Web Application operates inside target’s firewall. Researchers have uncovered advanced malware that can steal virtually all of a large...
-

 212Malware
212MalwareMeet GreenDispenser: A New Breed of ATM Malware
On the heels of recent disclosures of ATM malware such as Suceful [1], Plotus [2] andPadpin [3] (aka Tyupkin), Proofpoint research has...
-

 286News
286NewsHackers show US Police Department Vehicles can be hacked
Security researchers Chris Valasek and Charlie Miller helped the world understand that late-model vehicles are vulnerable to cyber attacks. We have read...
-

 228Geek
228GeekYiSpecter- Latest Malware Hits iOS Devices
YiSpecter malware infects iOS devices by exploiting private APIs — Reports suggest, Chinese and Taiwanese users of iOS devices have been affected the most. According...
-
 61Cyber Crime
61Cyber CrimeCybercrime ‘more threatening than ever’
Cybercrime is more aggressive and confrontational than it has ever been, Europol's latest Internet Organised Crime Threat Assessment (IOCTA) has stated.
-

 140Incidents
140IncidentsA vigilante hacker is changing 10,000 Wi-Fi passwords
Someone is hacking unprotected Wi-Fi routers everywhere — and forcing them to be on guard. Does your home Wi-Fi use a default...
-

 191Hacked
191HackedNew Intel Skylake CPUs Now Making Your PCs More Secure Than Ever
Short Bytes: Intel has incorporated the new SGX security technology in its Skylake CPUs, further strengthening the platform. Intel’s Sixth generation super performers...
-

 183Data Security
183Data SecurityHacking Wireless Printers With Phones on Drones
YOU MIGHT THINK that working on a secured floor in a 30-story office tower puts you out of reach of Wi-Fi hackers...
-

 183Data Security
183Data SecurityHow to Hack and Decrypt WhatsApp Database on rooted devices
The post includes a detailed procedure to hack and decrypt WhatsApp Database remotely on rooted Android mobile devices. Very Interesting!. A few...
-

 307Kids Online
307Kids OnlineThe best social networks for younger children
If you're looking to introduce your child to social networks and want peace of mind, look no further. Here are some of...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




