Featured News
-

 547Banking
547BankingJean‑Ian Boutin: Banking trojan threat is not going anywhere
In an exclusive for We Live Security, Jean-Ian Boutin, a malware researcher at ESET, shares his thoughts on the past, present and...
-

 122Incidents
122IncidentsDonald Trump’s hotel chain reveals hack ‘may have stolen credit card data’
Malware that was active for over a year could have ‘accessed payment card information as it was being inputted,’ Trump Hotel Collection...
-

 228Geek
228GeekCanonical is Organizing India’s First Ever Ubuntu Hackathon
Short Bytes: Canonical is organizing India’s first ever Ubuntu Hackathon in Bangalore between October 15-16, 2015. Know about different categories, great prizes...
-

 136Vulnerabilities
136VulnerabilitiesGoogle Pushes Stagefright 2.0 Patches to Nexus Devices
Google today patched the latest round of Stagefright vulnerabilities in Android, pushing them out as part of its latest over-the-air update to...
-
 297Hacked
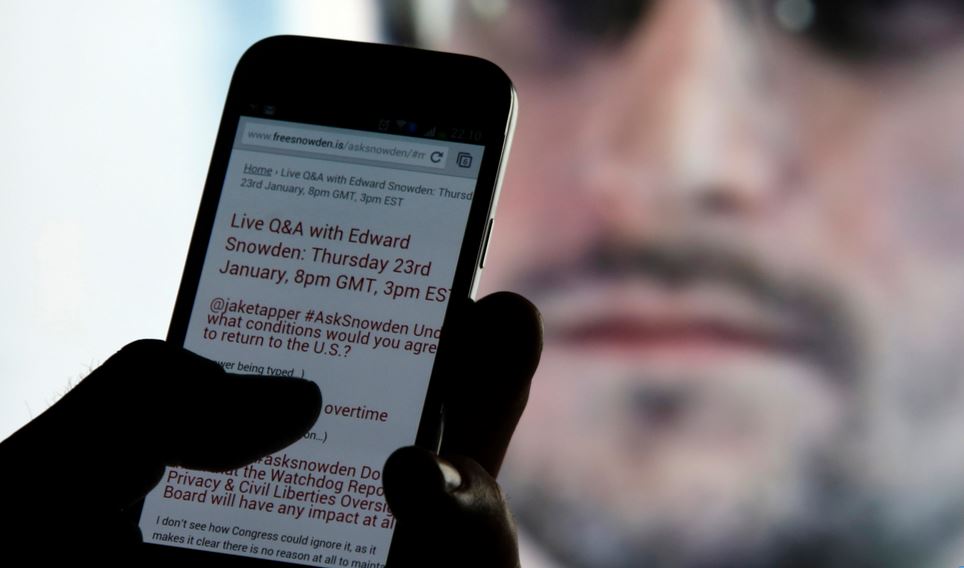
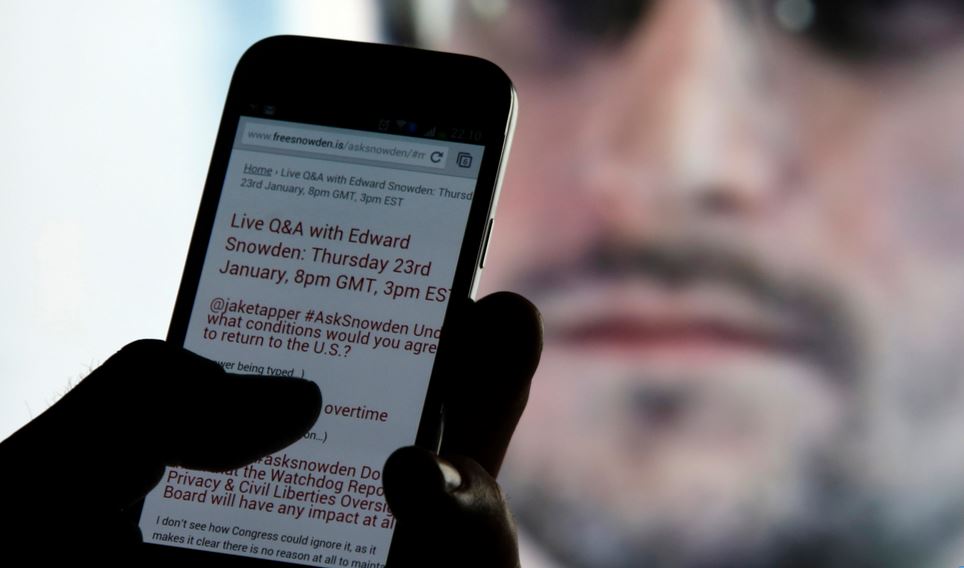
297HackedEdward Snowden: “Smartphones Can Be Easily Hacked With Just 1 Text Message”
Short Bytes: In a recent interview, Edward Snowden has said that spy agencies have lots of tools that could be used to...
-

 204Incidents
204IncidentsNew Outlook mailserver attack steals massive number of passwords
Backdoor in Outlook Web Application operates inside target’s firewall. Researchers have uncovered advanced malware that can steal virtually all of a large...
-

 220Malware
220MalwareMeet GreenDispenser: A New Breed of ATM Malware
On the heels of recent disclosures of ATM malware such as Suceful [1], Plotus [2] andPadpin [3] (aka Tyupkin), Proofpoint research has...
-

 289News
289NewsHackers show US Police Department Vehicles can be hacked
Security researchers Chris Valasek and Charlie Miller helped the world understand that late-model vehicles are vulnerable to cyber attacks. We have read...
-

 230Geek
230GeekYiSpecter- Latest Malware Hits iOS Devices
YiSpecter malware infects iOS devices by exploiting private APIs — Reports suggest, Chinese and Taiwanese users of iOS devices have been affected the most. According...
-
 63Cyber Crime
63Cyber CrimeCybercrime ‘more threatening than ever’
Cybercrime is more aggressive and confrontational than it has ever been, Europol's latest Internet Organised Crime Threat Assessment (IOCTA) has stated.
-

 142Incidents
142IncidentsA vigilante hacker is changing 10,000 Wi-Fi passwords
Someone is hacking unprotected Wi-Fi routers everywhere — and forcing them to be on guard. Does your home Wi-Fi use a default...
-

 195Hacked
195HackedNew Intel Skylake CPUs Now Making Your PCs More Secure Than Ever
Short Bytes: Intel has incorporated the new SGX security technology in its Skylake CPUs, further strengthening the platform. Intel’s Sixth generation super performers...
-

 187Data Security
187Data SecurityHacking Wireless Printers With Phones on Drones
YOU MIGHT THINK that working on a secured floor in a 30-story office tower puts you out of reach of Wi-Fi hackers...
-

 189Data Security
189Data SecurityHow to Hack and Decrypt WhatsApp Database on rooted devices
The post includes a detailed procedure to hack and decrypt WhatsApp Database remotely on rooted Android mobile devices. Very Interesting!. A few...
-

 313Kids Online
313Kids OnlineThe best social networks for younger children
If you're looking to introduce your child to social networks and want peace of mind, look no further. Here are some of...
-

 303Hacked
303HackedYour Stolen/Hacked Identity is Sold Just For $1 in The Dark Web
Short Bytes: Increasing data breaches have made the personal identifiable information (PII) market very hot. The latest report outlines the different aspects...
-

 321Malware
321MalwareYiSpectre, the First iOS Malware That Attacks Non-Jailbroken Devices
The malware spreads with the help of an adult movie player. Security researchers at Palo Alto Networks have discovered and analyzed malware that...
-

 90Data Security
90Data SecurityVW’s ‘neat hack’ exposes danger of corporate software
It was only old-fashioned detective work that forced Volkswagen to admit to the existence of its ‘defeat device’. And that should worry...
-

 320Data Security
320Data SecurityHow to do hacking attacks over satellite communications?
Hack Satellite comunication In this article we will cover satellite based hacking attack which has been used by hacking groups since...
-

 388Data Security
388Data SecurityHOW TO INTERCEPT SATELLITE COMMUNICATIONS EASILY?
In today world we use satellite communication in many respects and industries and we all know how important they are in our...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




