Featured News
-
 326How To
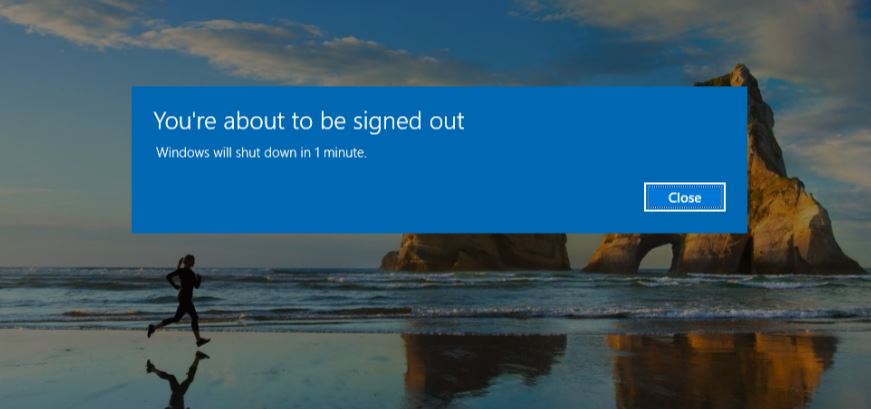
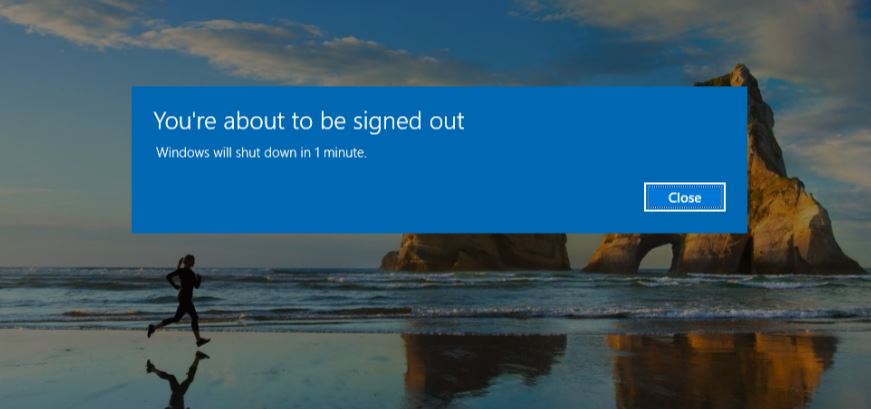
326How ToHow To Schedule A Shutdown For Windows OS?
Short Bytes: This article describes the steps to schedule a Shutdown command for Windows OS. Take a look. The very first task...
-
 100How To
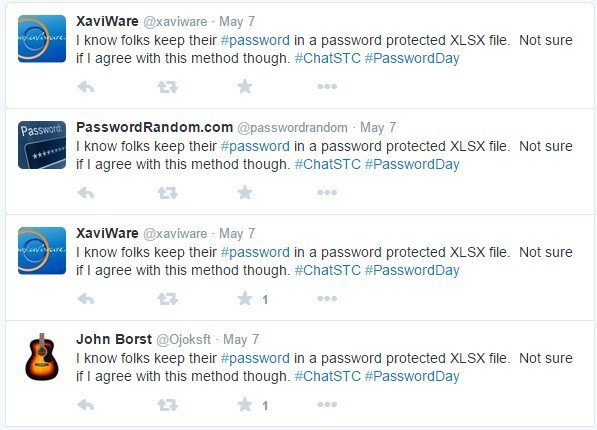
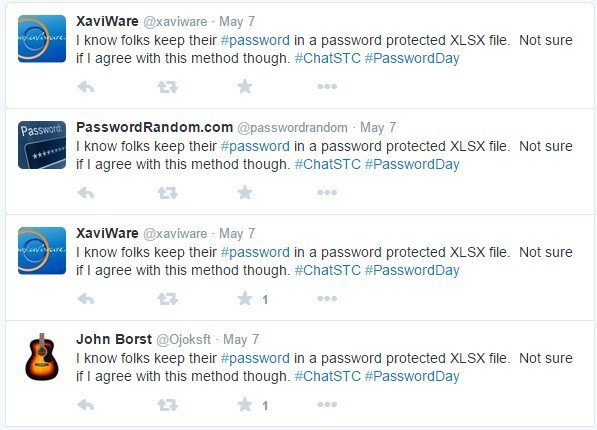
100How ToHow To Find The People Stealing Your Tweets On Twitter
This small piece of python code will find the people stealing your tweets and copy-pasting them on their twitter timeline. This python...
-
 267Geek
267GeekMS Word Vulnerability Exploited in Operation Pony Express to Spread Malware
Operation Pony Express was a spear-phishing campaign that was detected by Sophos researchers between April and May 2015. The research team identified...
-

 303Hacked
303HackedFirst Step to Effective Security – How to Know if You’ve Been Hacked
Short Bytes: Was your data compromised in the latest data breaches? How to know if you’ve been hacked? Here are the answers. The...
-
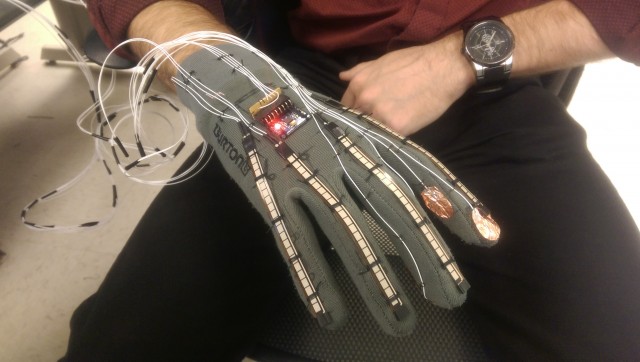
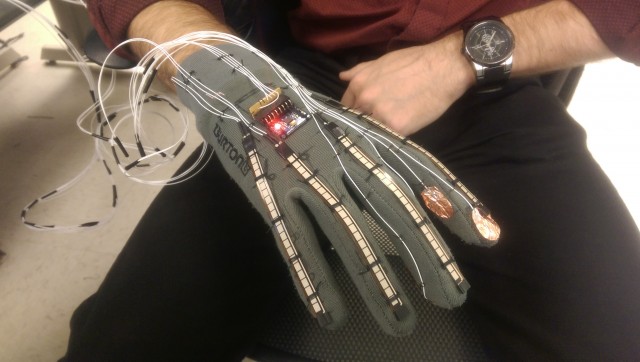 293Geek
293GeekFuturistic Smart-Glove Can Translate Sign Language Into Text and Speech
Scientists are constantly working on user-friendly products for those with physical disabilities. In the past, these wearable glasses came out to help...
-

 119Geek
119GeekStagefright 2.0: Security Flaw in Android Puts 1 Billion Devices at Risk
The risk of remote hacking is triggered through the faults in the media processing components that may be misused by malicious websites....
-
 303Geek
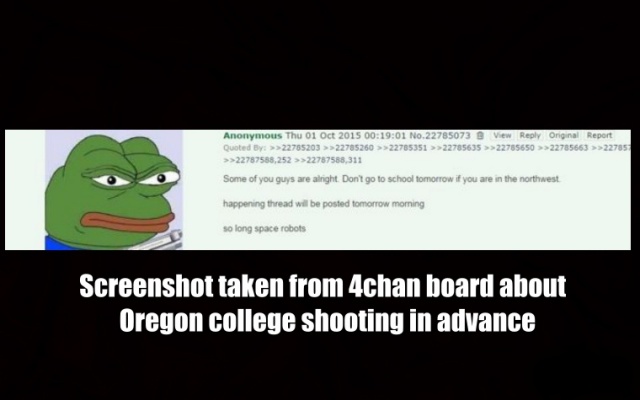
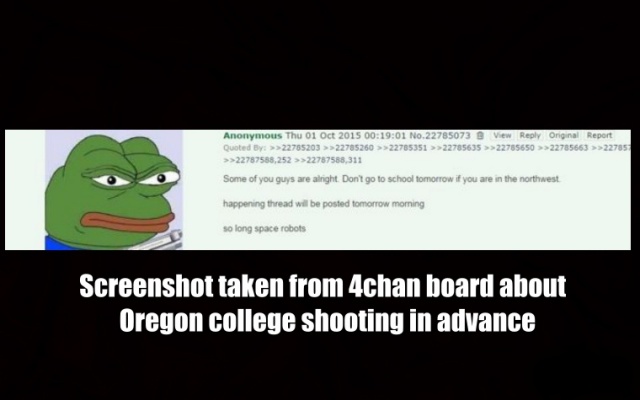
303GeekWas Oregon Shooting Predicted on 4chan?
Someone used 4chan to post about Oregon college shooting in the US before it actually took place. The sudden increase of Internet users...
-
 486Geek
486GeekWhat is Free and Open Source Software (FOSS) and Why You Should Use it?
Short Bytes: FOSS (Free And Open Software) is the modern day result of the free software movement that draws its philosophies from...
-

 113Malware
113MalwareDangerous resurgent banking malware hits UK
Bank trojan twin pivots to smash supply chain biz. The formidable Dyreza and Dridex banking malware are back in renewed and rejigged...
-

 134Malware
134MalwareAndroid Malware Disguises as PayPal App
A recent spam campaign is leading users to a fake PayPal app which steals their real credentials, but also comes hard-coded to...
-

 326Cyber Crime
326Cyber CrimeFBI Caught Paedophile By Infecting Tor Web Browser
Do you think that using anonymity software like Tor will protect your online presence from spies? A new spyware has been developed...
-

 169Incidents
169IncidentsPatreon was warned of serious website flaw 5 days before it was hacked
Even worse: Thousands of other sites are making the same facepalm-worthy mistake. Five days before Patreon.com officials said their donations website was...
-

 115Vulnerabilities
115VulnerabilitiesSamsung Decides Not to Patch Kernel Vulnerabilities in Some S4 Smartphones
Two kernel vulnerabilities were left unpatched on older devices running Android Jelly Bean and KitKat. QuarksLAB, a security research company based in Paris,...
-

 198Vulnerabilities
198VulnerabilitiesWordPress Jetpack Plugin Patched Against Stored XSS Vulnerability
After a few critical bugs were recently discovered and patched in the core WordPress engine—a rarity with WordPress-related security issues—order has apparently...
-
 204Hacked
204HackedEdward Snowden Gets Bombarded With 47GB of Twitter Notifications
Short Bytes: Former NSA contractor and a newbie to Twitter, Edward Snowden, forgot to turn off the email notifications on Twitter and...
-

 319Data Security
319Data SecurityHackers Can Exploit Security Flaws In Drones To Hijack Flight Controller
Security flaws have been found in drones that could allow hackers to target and attack the flight controller which includes numerous sensors...
-

 390News
390NewsExperian Hack Leads To Data Breach of T-Mobile Customers
Experian, a major credit reference agency has suffered a huge data breach. Around 15 million T-Mobile users (who signed up for T-Mobile’s...
-

 258Geek
258GeekFacebook Becomes Livelier with a 7-sec Video Profile Pic
On Tuesday, Facebook announced that tests are being conducted which will allow users to change their static profile pic to a 7-sec video clip. Facebook is now...
-

 187Hacked
187Hacked15 Million T-Mobile Users’ Data Stolen From Experian Hack
Short Bytes: T-Mobile CEO John Legere has confirmed that its 15 million users’ database has been hacked as its credit vendor Experian...
-
 298Hacked
298HackedHackers Spreading New Router Malware That Actually Makes Routers More Secure
Short Bytes: Linux.Wifatch not only prevents further attacks from router malware, it also shows a message telling the people to change passwords and...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




