Featured News
-

 174Malware
174MalwareNew malware infects ATMs, dispenses cash on command
The GreenDispenser malware displays an error on the infected ATMs so that only criminals can use them. Security researchers have discovered a...
-

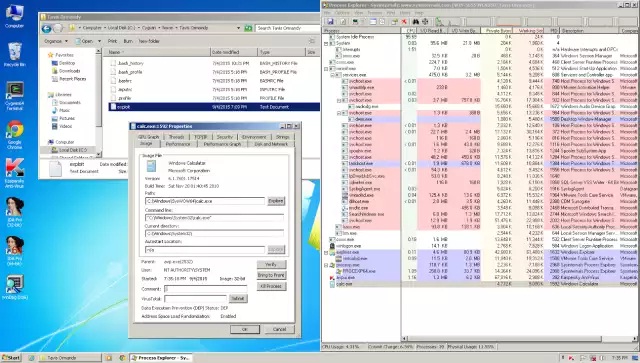
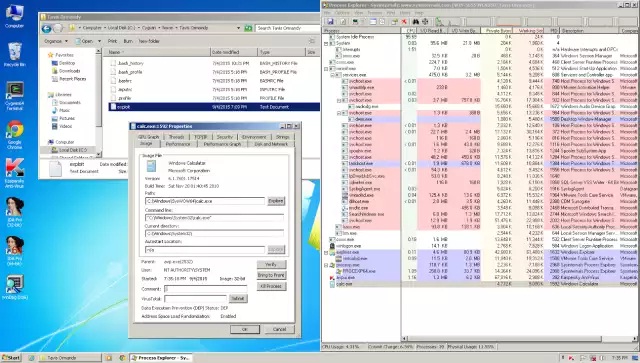
 259Data Security
259Data SecurityLenovo Laptops and Computers Come with Pre-Installed Spyware
Lenovo has been caught, yet again, installing apps on its laptops and workstations without the user’s consent or knowledge, as Michael Horowitz...
-

 114Vulnerabilities
114VulnerabilitiesCisco Patches Denial-of-Service, Bypass Vulnerabilities in IOS
Cisco pushed out on Wednesday its usual semiannual round of patches for IOS, the software the company uses for most of its...
-
 155Vulnerabilities
155Vulnerabilities‘RipSec’ goes to Hollywood: how the iCloud celeb hack happened
TV starlet offers iCloud access, photoshopped nudes, to bait voyeur hackers. The chief hacker behind the infamous iCloud celebrity hacks has revealed...
-

 224Geek
224GeekPopular Android Games Hit By Malware
The IT security researchers at ESET detected malware on popular Android games which created quite a furor among users. A couple of...
-

 106Hacked
106HackedApple Tells the 25 Most Popular XcodeGhost Infected iOS Apps
Short Bytes: Today, Apple has released a list of the 25 most popular XcodeGhost infected iOS apps. The tech company tells the...
-
 276Lists
276ListsHow BIG is Google, Really?
Short Bytes: Google is synonymous with the Internet today, and the word in itself has become a verb. So what made Google...
-

 221Password
221PasswordiOS 9 security flaw lets attackers access device through Siri
Apple’s iOS 9 contains a security flaw that lets cybercriminals gain limited access to a device through Siri.
-

 107Malware
107MalwareHey Scandos, missed that parcel? Here’s some ransomware instead
Variant of CryptoLocker makes an unwelcome appearance. Spam emails disguised as messages from local post offices – but actually packing the latest...
-
 161Incidents
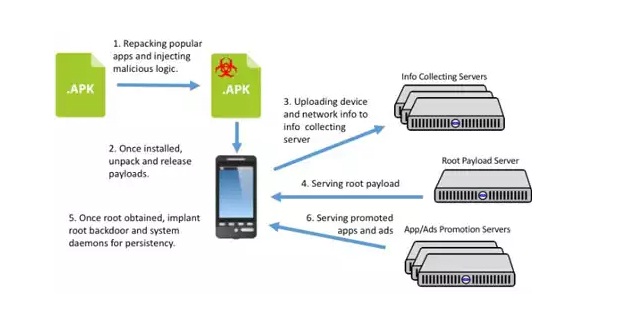
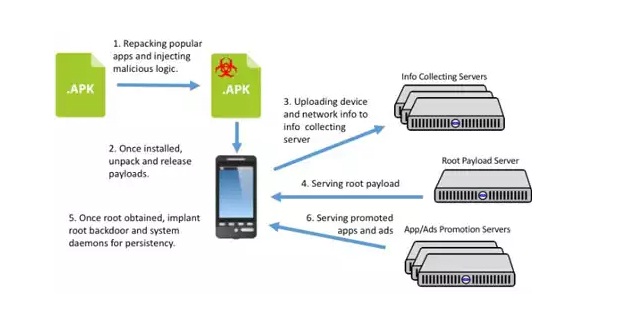
161IncidentsChinese promotion company hijacks Android devices around the world
A Chinese mobile app promotion company has created malicious adware that allows them to gain complete control of users’ Android devices. The...
-

 71Data Security
71Data SecurityAn Introduction to Hardware Hacking: the RIPE Atlas probe
RIPE NCC is building the largest Internet measurement network ever made. RIPE Atlas employs a global network of probes that measure Internet...
-

 187Incidents
187IncidentsFingerprints of over 5.6 Million Americans Stolen During the OPM Hack
The data breach at the US Office of Personnel Management (OPM) is slowly shaping up to be one of the biggest hacks...
-
 158Vulnerabilities
158VulnerabilitiesSecurity wares like Kaspersky AV can make you more vulnerable to attacks
Antivirus applications and other security software are supposed to make users more secure, but a growing body of research shows that in...
-

 176Geek
176GeekYour iOS 9 Lockscreen Can Be Bypassed in 30 Seconds
A security flaw has been discovered in Apple’s mobile software iOS 9 that lets strangers exploit Siri in order to bypass lock...
-

 312Geek
312GeekFacebook Following NSA Footsteps to Spy on Users: Belgium’s Privacy Advocate
In June this year, we reported how Facebook was sued by Belgium’s Privacy Commission (BPC) for tracking users even those who never made...
-

 318Cyber Events
318Cyber EventsUS Navy Developing Cyber Protection System to Protect Ships from Cyberattacks
The experts over at United States Navy are busy in the development of a cyber-protection system, codenamed RHIMES (the Resilient Hull, Mechanical,...
-

 275Geek
275GeekHaving Nude Selfies on Phone May Send You to Prison in the U.S.
A high schooler from North Carolina and his girlfriend are expecting prosecution both as minor victims and adult culprits for keeping nude...
-

 313Geek
313GeekHere’s How Someone Made a PiPhone- A Raspberry Pi Based Smartphone
Short Bytes: In this article, I’m going to share how someone made a “PiPhone”. Well, as the name suggests, PiPhone is a...
-

 328Geek
328GeekApple XcodeGhost Malware: List of iOS Apps You Should Delete Immediately
Apple’s App Store in China has apparently been penetrated by Hackers which experts say has placed the devices of hundreds of millions...
-
 116Scams
116ScamsCriminals, linguistics, literacy and attribution
Linguistics and some form of textual analysis can be helpful in analysing malware and scams. Regional attribution, though, still requires caution.
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




