Featured News
-
 164Malware
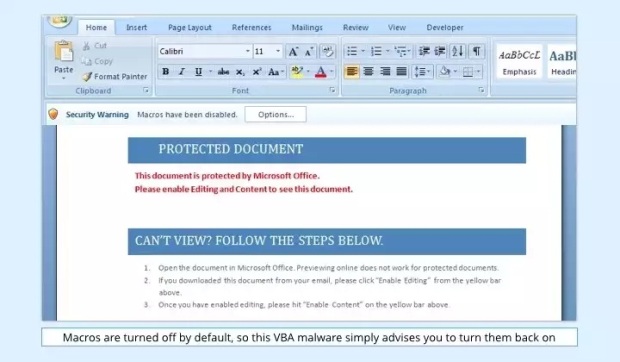
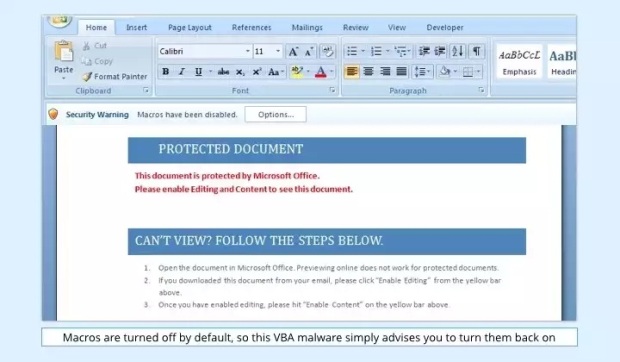
164MalwareVBA Malware Makes a Comeback Inside Booby-Trapped Word Documents
VBA stands for Visual Basic for Applications and is a programming language developed by Microsoft to help programmers create Windows applications using...
-

 161How To
161How ToTurn Off Wi-Fi Assist in iOS 9 As It Sucks All Your Data
Short Bytes: iOS 9 has a new feature Wi-Fi Assist that sucks your cellular data if the W-Fi coverage in your area...
-

 268Hacked
268HackedThe Pirate Bay Founder Finally Released From Prison After 3 Years
Short Bytes: The Pirate Bay co-founder Gottfrid Svartholm Warg is truly free again. Kristina Svartholm, his mother, announced the release on Twitter this Monday. The...
-

 127Incidents
127IncidentsHack attacks strike top porn sites
A malicious advertising campaign has targeted top adult sites like Pornhub and YouPorn. Several of the world’s most popular pornographic websites were...
-

 90Data Security
90Data SecurityStoring secret crypto keys in the Amazon cloud? New attack can steal them
Technique allows full recovery of 2048-bit RSA key stored in Amazon’s EC2 service. Piercing a key selling point of commercial cloud computing...
-

 175Malware
175MalwareTrojan Found Pre-Installed on Some Android Devices
A trojan strand targeting Android devices has been found coming pre-installed inside the firmware of some Android smartphones by Dr.Web, a Russian-based...
-

 114Data Security
114Data SecurityNew DDoS attack uses smartphone browsers to flood site with 4.5bn requests
Researchers have found that smartphone browsers can deliver a powerful flooding attack. Researchers suspect a mobile advertising network has been used to...
-
 237Cyber Crime
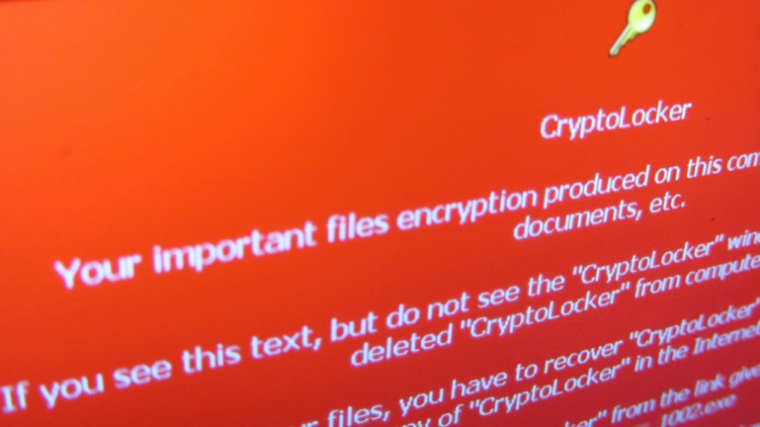
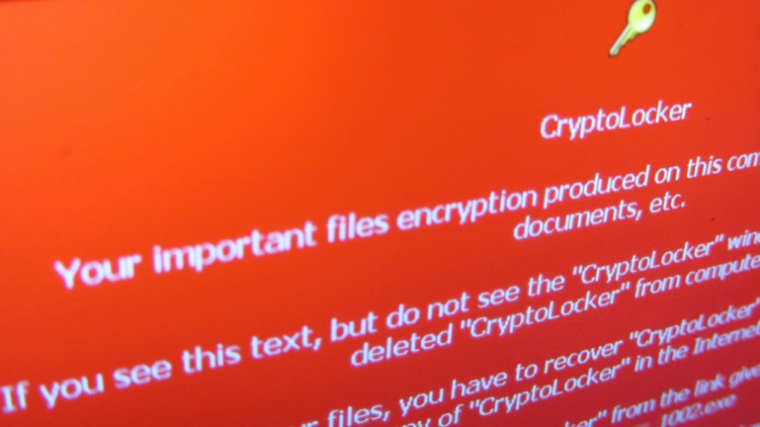
237Cyber CrimeHackers delivering ransomware virus in package delivery e-mails
A new ransomware email campaign detected in the fake email messages sent by either PostNord or Post Denmark, identified as Cryptolocker2. Hackers...
-
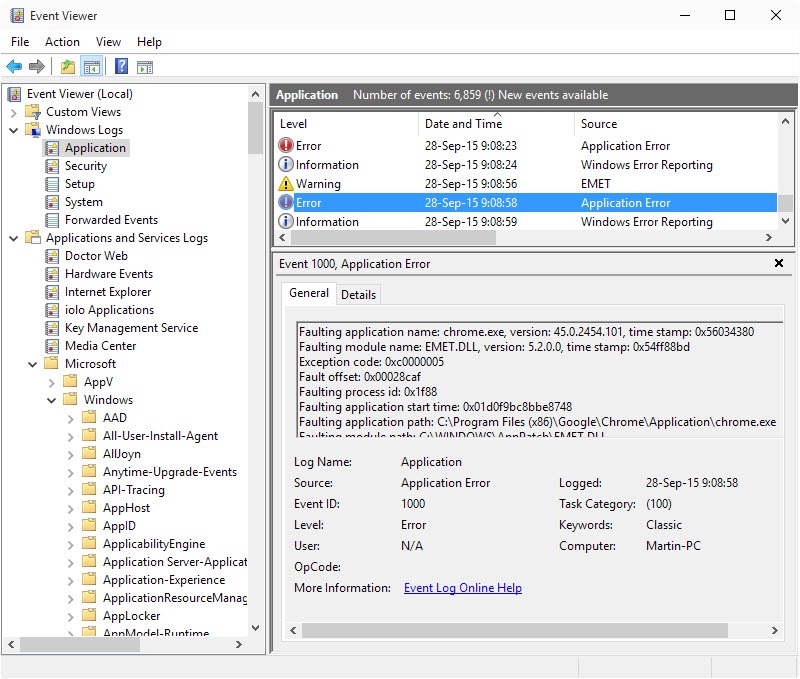
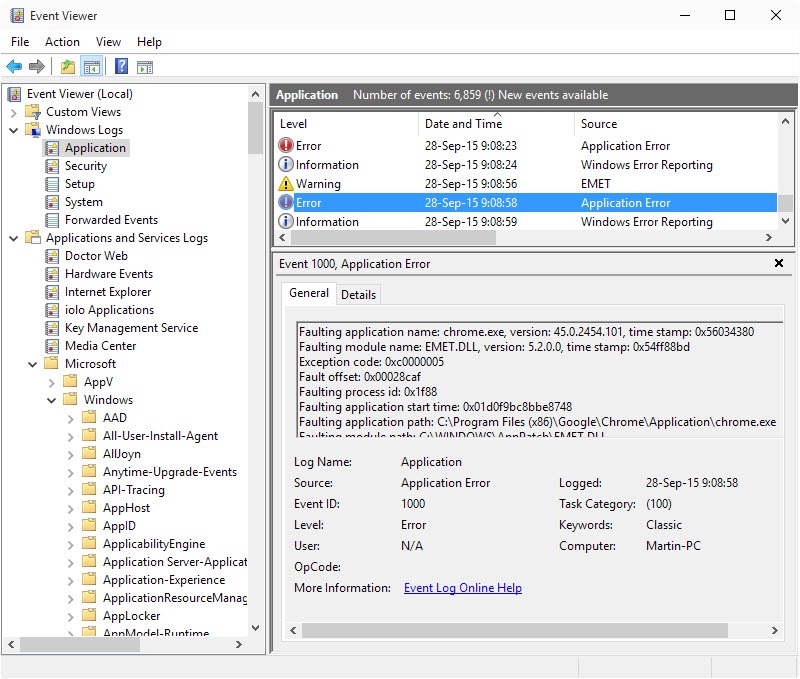 184Vulnerabilities
184VulnerabilitiesAdvanced Microsoft Enhanced Mitigation Experience Toolkit (EMET) Tips
The Microsoft Enhanced Mitigation Experience Toolkit, short EMET, is an optional download for all supported client and server versions of Microsoft’s Windows...
-

 127Vulnerabilities
127VulnerabilitiesVeraCrypt 1.15 fixes two recently reported TrueCrypt vulnerabilities
Yesterday’s update of the encryption software VeraCyrpt fixed two vulnerabilities that security researcher James Forshaw discovered in TrueCrypt’s source code. TrueCrypt, which...
-
 121Malware
121MalwareIntelligent system to check malware hidden in shortened Twitter URLs
Tool to check malware in Twitter URLs to be tested during European Football Championships next summer. An intelligent system has been created...
-
 78Data Security
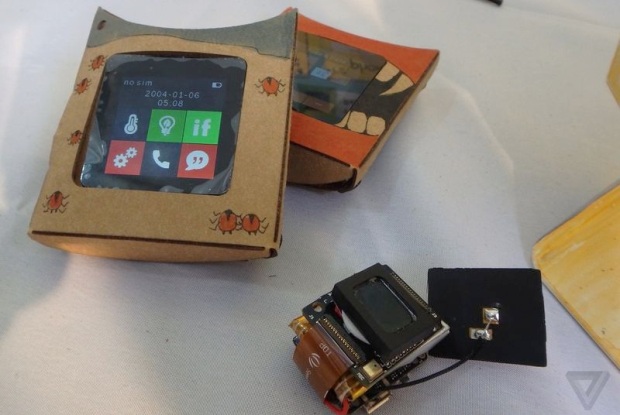
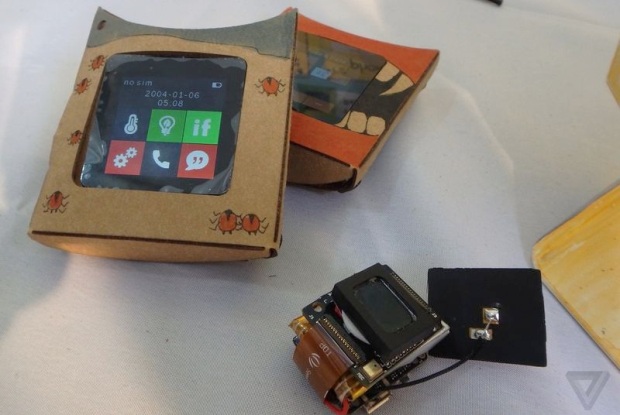
78Data SecurityRephone lets you hack a cellular radio into anything
Yesterday at the Maker Faire in New York, we had a chance to check out the Rephone, a clever little project that...
-

 186Opinion
186OpinionESET Presentations at Virus Bulletin 2015
Some of the good things in store for those attending Virus Bulletin 2015.
-

 172Geek
172GeekSocial Experiment: What Happens When Your Child Falls for Fake Social Media Profiles
Most of us have heard of ‘stranger danger’ and most of us have been educated as children or have educated children about...
-
 325Geek
325GeekCoding Trends: The Top 21 Programming Languages of 2015
Short Bytes: RedMonk’s bi-annual programming language ranking is out and it shows that JavaSript continues to rule the web. Also, Apple’s Swift...
-

 191Cyber Crime
191Cyber CrimeHackers Hosting eBay Phishing Sites on eBay’s Network
Hackers are stealing eBay usernames and passwords by hosting phishing sites on eBay’s very own network. These sites appear convincing because of the...
-

 285Hacked
285HackedHackers Are Using This Malware to Make ATMs Vomit Cash
Short Bytes: Security firm Proofpoint has noticed some instances of a new ATM malware called GreenDispenser. Hackers can empty the whole ATM...
-
Computer Forensics
Check if your Hard drive is close to dying
Windows doesn’t provide a built in tool , through which you can check your S.M.A.R.T Data. You will have to use a...
-

 272Geek
272GeekLatest Facebook Prototype AI Monitors and Narrates Events in the Video
Facebook has finally improved its AI mechanism and unveiled its personal digital assistant that enhances your video watching experience tremendously. According to...
-

 252News
252NewsHacked Uber Accounts of US Based Customers Used in China
Uber’s tentative and troublesome entry into the Chinese market has been compounded by news that Hacked Uber Accounts of Uber Riders are...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




