Featured News
-
 250Geek
250GeekLearn it Faster: The Entire Python Language in a Single Image
Short Bytes: What if you had to study one single page to get the complete idea of a programming language? In this...
-

 168Vulnerabilities
168VulnerabilitiesWestern Digital My Cloud Devices Can Be Hacked by Local or Remote Attackers
Security researchers at VerSprite have tested and discovered a few vulnerabilities in Western Digital’s My Cloud NAS (Network Attached Storage) hard drive,...
-
 74Malware
74MalwareNew Adware Facilitates the Distribution of Trojans for Mac Users
A new piece of adware that serves as an entry point for future trojan infections was discovered by Dr.Web security researchers. This...
-

 126Incidents
126IncidentsApple hack exposes flaws in building apps in China
China’s “Great Firewall” may have been partly to blame for the first major attack on Apple Inc’s (AAPL.O) App Store, but experts...
-
 166Malware
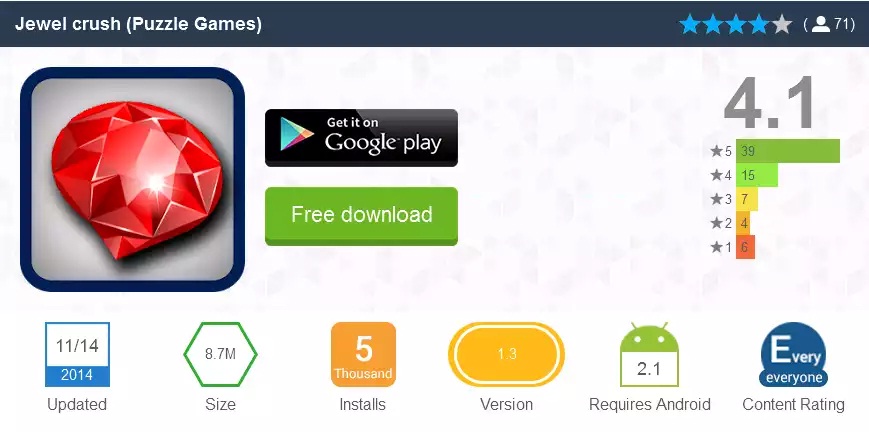
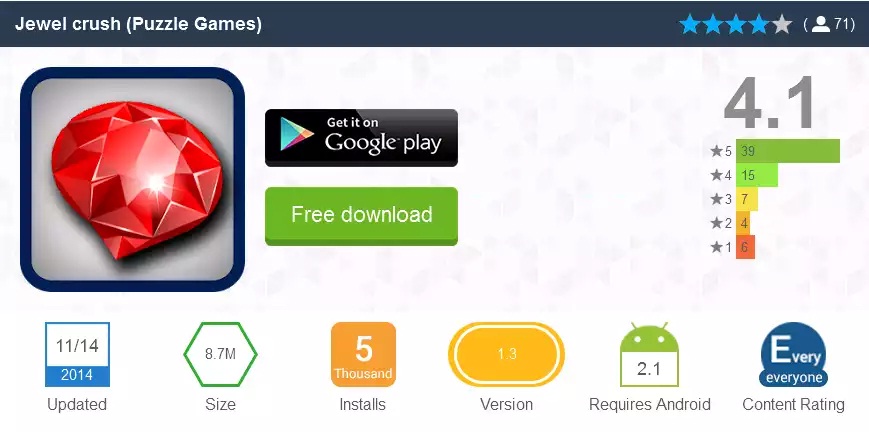
166MalwareAndroid trojan drops in, despite Google’s Bouncer
We at ESET recently discovered an interesting stealth attack on Android users, an app that is a regular game but with one...
-

 313Geek
313GeekUS Air Force EC-130H Aircraft with Hacking Kit can Hack Enemy Networks
United States Air Force at the Air and Space conference held in Maryland, has unveiled a specifically designed aircraft named EC-130H Compass Call that...
-

 163Vulnerabilities
163VulnerabilitiesModel Assesses Readiness to Accept Outside Vulnerability Reports
The proliferation of independent and vendor-sponsored bug bounties has not only put some money in researchers’ pockets, but has also forced enterprises—and...
-

 202Geek
202GeekDo You Believe in Aliens? Well, Edward Snowden Does
Edward Snowden claims that if the technology keeps on becoming sophisticated and flawless then we may never be able to locate aliens...
-
 188Data Security
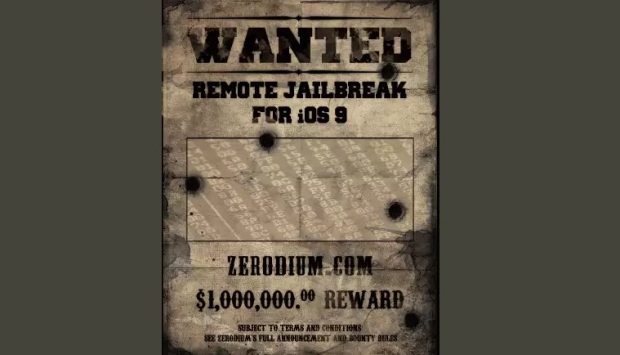
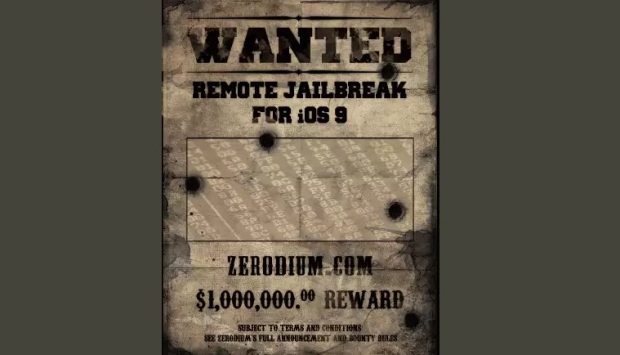
188Data SecurityExploit broker offers $1 million for reliable iOS 9 exploit
Here’s a treat for hackers and security researchers who don’t mind selling information about zero-day vulnerabilities to the highest bidder: Zerodium, the...
-
 383Hacked
383HackedWorld’s Biggest 0-day Bug Bounty Program: Hack Apple iOS 9 to Win $1,000,000
Short Bytes: Security firm Zerodium has launched “The Million Dollar iOS 9 Bug Bounty”, that offers $1 million for finding vulnerabilities and...
-

 242Data Security
242Data SecuritySoon, you may not be able to delete WhatsApp messages for 90 days
Govt mulls a policy that requires users to save messages, and hand them over to law enforcement agencies, if asked. Deleting WhatsApp...
-

 174Vulnerabilities
174VulnerabilitiesAdobe Patches 23 Critical Vulnerabilities in Flash Player
Adobe has released a Flash Player update that addresses 23 critical vulnerabilities in the software, many which can lead to code execution....
-

 187Malware
187MalwareTop QLD sex shop cops Cryptowall lock; cops flop as state biz popped
Cryptowall attackers are smashing businesses in the Australian state of Queensland, according to the owner of a Townsville sex shop which has...
-

 150Geek
150GeekGhost Push Android Malware Responsible for Infecting 600k New Users Daily
The Ghost Push malware comes with those Android apps that are available at non-Google app stores. The newly discovered Android malware dubbed as Ghost Push Malware has...
-

 206Vulnerabilities
206VulnerabilitiesAndroid Malware Steals Money from Your Bank Account, Hides SMS Transaction Alerts
New Android malware was discovered, able to steal money from online banking accounts, and hide SMS notifications coming to confirm financial transactions....
-
 376Hacked
376HackedStay Informed, Stay Away from Facebook Dislike Button Scams
Short Bytes: It’s reported that scammers are taking advantage of Facebook Dislike button anticipation and they’re using the Facebook users. These scams trick...
-

 85Data Security
85Data SecurityBitcoinist Weekly News Re-Hash: BitPay Hack, California Bitcoin Bill Dies
After two weeks of sharp, last minute changes in the Bitcoin price, the markets caught a break this week, with the price...
-

 97Hacked
97HackedIndia’s New Encryption Policy is Ridiculous, Deleting Your Chats Could Soon Become Illegal
Short Bytes: The government of India doesn’t understand the concept of online privacy and the importance of encryption. A new government body...
-

 73Malware
73MalwareApple removes hundreds of malicious apps after major malware attack
Apple has removed more than 300 malicious apps after confirming the first major breach to its iOS app store.
-
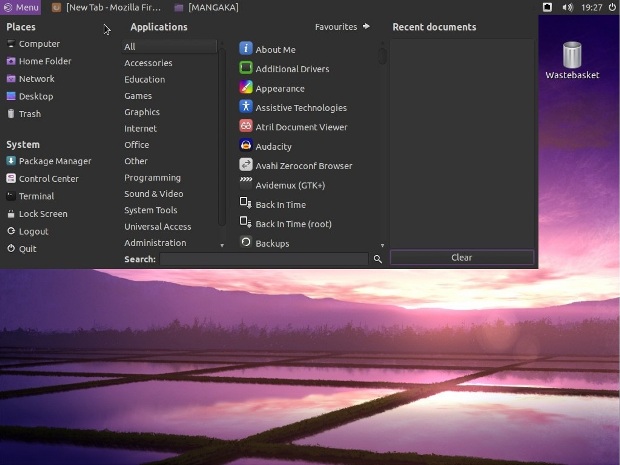
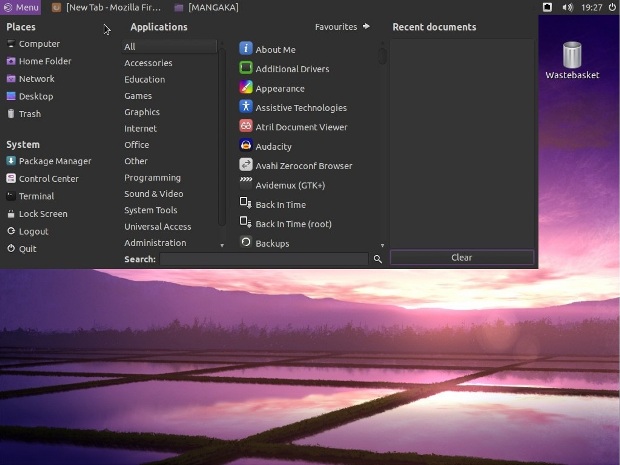 73Data Security
73Data SecurityLinux Mangaka Mou Arrives for Anime and Manga Fans, Based on Ubuntu 14.04 LTS
Just a few minutes ago, September 20, Animesoft International had the great pleasure of informing Softpedia about the immediate availability for download...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




