Featured News
-

 260News
260NewsHow Your ATM Card Data Could Get Hacked
Security experts have warned ATM (Automated Teller Machine) users to stay clear from suspicious ATMs for past several years because of numerous...
-
 231Geek
231Geek“My First Line of Code”: Linux Creator Linus Torvalds
Short Bytes: Linus Torvalds is the creator of Linux and he still decides what will happen in the world of Linux. Read...
-

 233News
233NewsAnonymous Hacks Vietnam Govt websites Against Human Rights Abuse
The online hacktivists affiliated to Anonymous, AntiSec and HagashTeam conducted a cyber attack on Vietnamese government websites against online censorship and human...
-

 188News
188NewsScreenshot Malware Spying On Online Poker Players
A unique malware has been found by security experts which spies on the players of online poker gaming sites, specifically Full Tilt...
-
 271Hacked
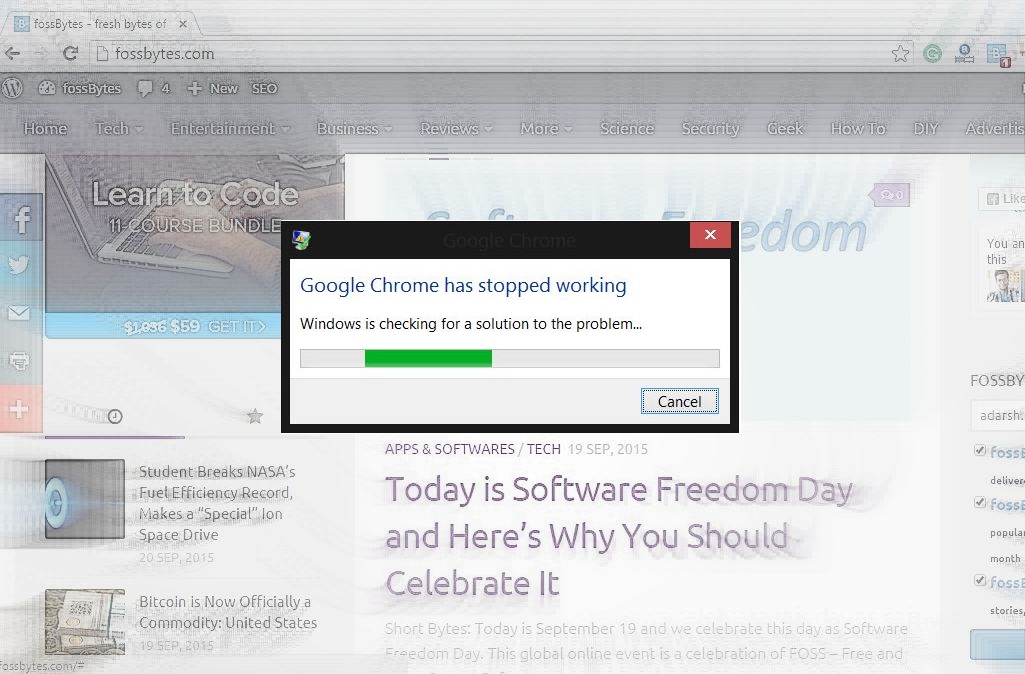
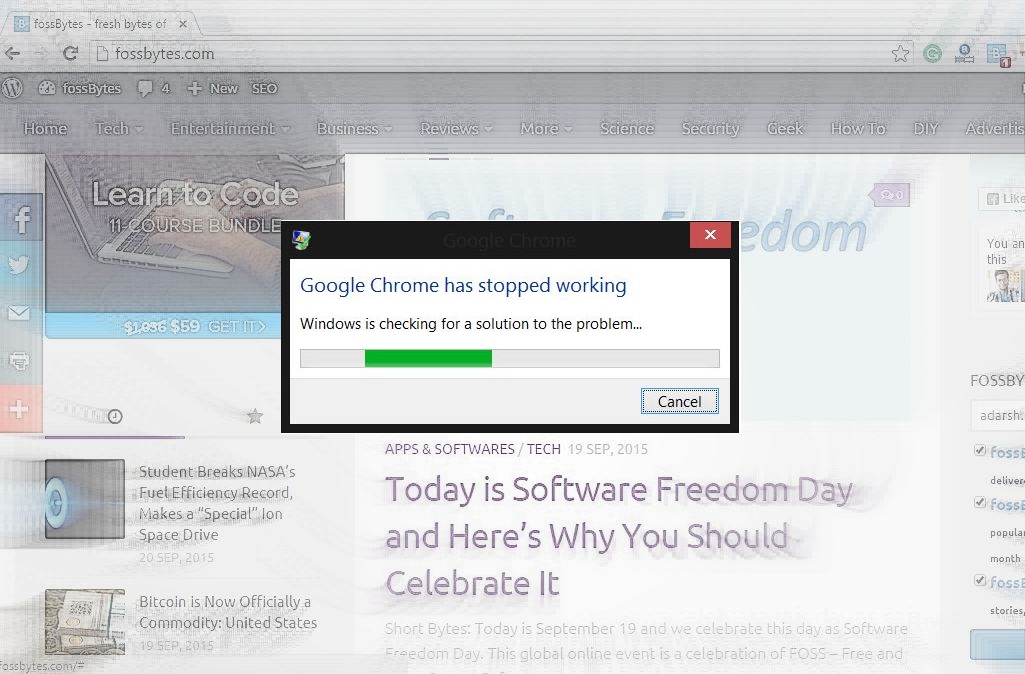
271HackedHow and Why Crash Google Chrome With These 16 Characters in 2 Seconds
Short Bytes: Do you want to crash someone’s Google Chrome just for the heck of it? Here’s how to do it with...
-

 303Geek
303GeekMicrosoft Windows Devices Responsible For 80% of Malware Infections
Microsoft Windows, in spite of having an insignificant share in the mobile market, is the leading operating system that is responsible for...
-
 317News
317NewsPhishing Attack Causes Bitcoin Payment Processor BitPay to Lose $1.8M
BitPay the Atlanta-based Bitcoin payment processor had been hit by a massive phishing attack costing the company $1.8 million. Verified by the...
-
 164Data Security
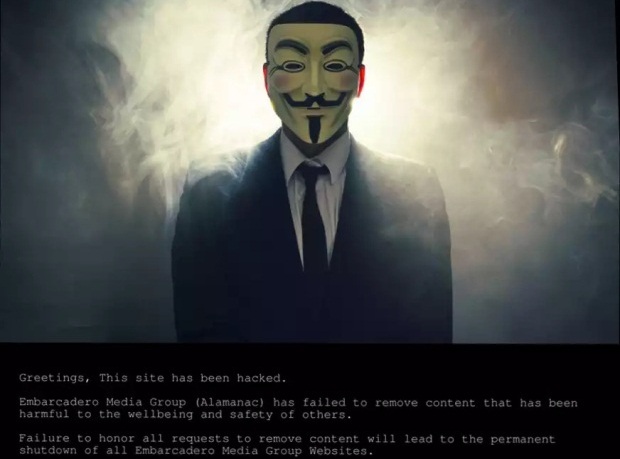
164Data SecurityHackers Hold Silicon Valley’s Hometown Newspapers Hostage
Sometime yesterday, 17 September, hackers took over the websites of Silicon Valley’s Embarcadero Media Group, publisher of the Palo Alto Weekly, theAlmanac,...
-
 148Malware
148MalwareAT&T Employees Installed Malware on Their PCs to Aid Phone Unlocking Service
AT&T has filed a lawsuit against 3 former call center employees, accusing them of installing malware on their servers with the purpose...
-

 97Data Security
97Data SecurityHack Brief: Malware Sneaks Into the Chinese iOS App Store
THE APPLE ECOSYSTEM is well known for very rarely letting any dodgy apps enter it because of the company’s stringent security checks....
-

 124Malware
124MalwareNew PoS Trojan Can Download Other Malware, Launch DDOS Attacks
The world of computer viruses and antivirus solutions is in a constant change, with cyber-crooks evolving their code and cyber-security firms trying...
-

 189Vulnerabilities
189VulnerabilitiesD-Link Accidentally Leaks Private Code-Signing Keys
A simple mistake by networking gear manufacturer D-Link could have opened the door for costly damage. Private keys used to sign software...
-
 221Tricks & How To's
221Tricks & How To's10 Windows Commands you need to know for Troubleshooting
The command line is an interface for typing commands directly to a computer’s operating system. It is usually used to resolve Microsoft...
-

 282Hacked
282Hacked“seL4” is an Unhackable Kernel for Keeping All Computers Safe From Cyberattack
Short Bytes: The Australian national research agency Data61 has developed an unhackable kernel named seL4 and proved its unhackable property mathematically. The kernel...
-
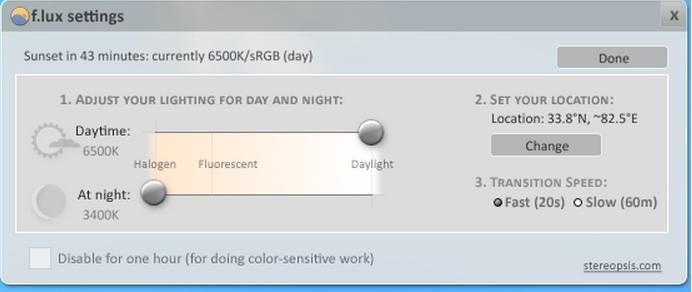
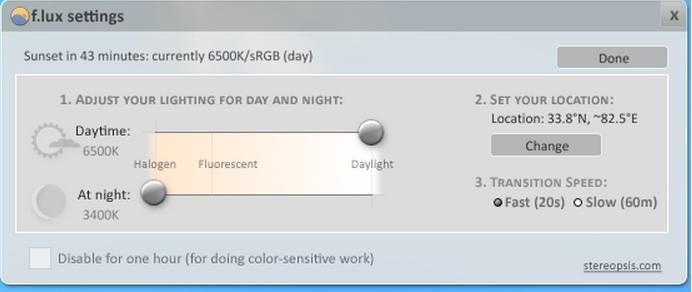 169Tricks & How To's
169Tricks & How To'sSave your eyes from Computer Strain
No more watery eyes, when you wake up from sleep in the middle of the night to work on your bright computer...
-

 301Data Security
301Data SecurityRussian Hacker who stole 160 million credit card details gets sentenced for 30 years in prison
Russian national pleads guilty in global hacking scheme. Russian Hacker Vladimir Drinkman faces 30 years sentence after pleading guilty to hacking NASDAQ,...
-
 72Malware
72MalwareThe evolution of ransomware: From PC Cyborg to a service for sale
A look back at how ransomware – a type of malware used mostly for hijacking user data – has evolved from the...
-
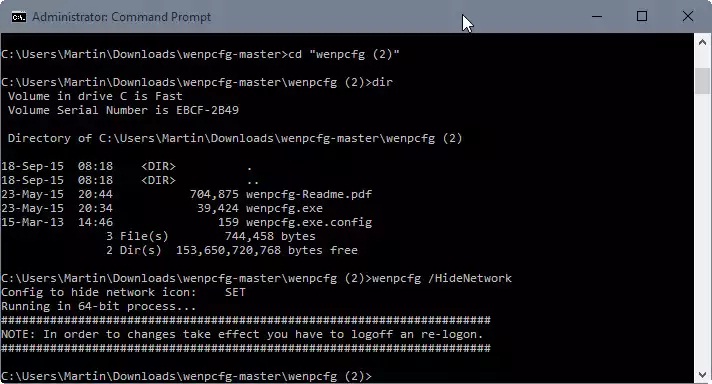
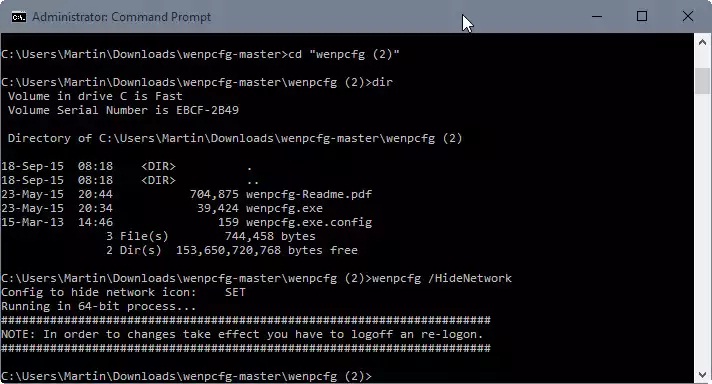 97Data Security
97Data SecurityRemove Libraries, Network, Homegroup and other links from File Explorer
When you open File Explorer in Windows 10, the system’s default file browsing and management tool, you will notice immediately that it...
-
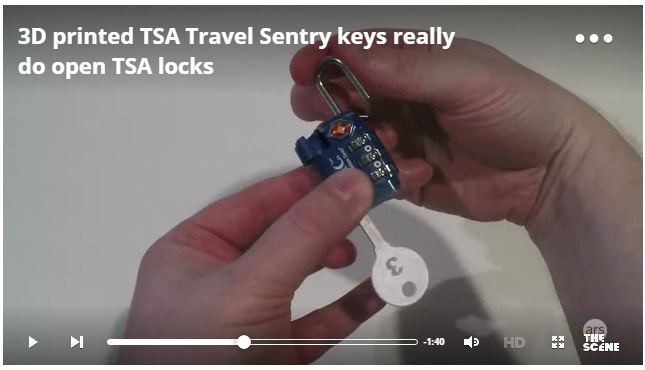
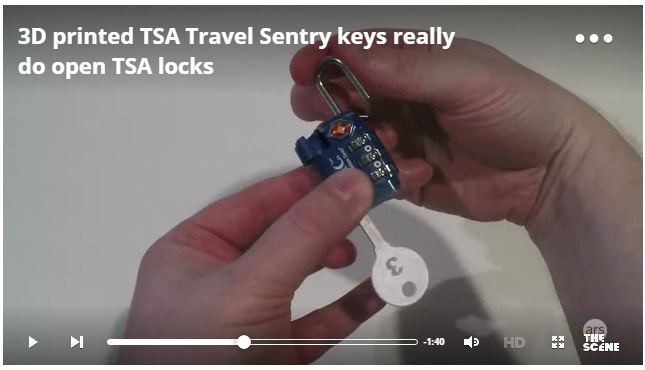 74Data Security
74Data Security3D printed TSA Travel Sentry keys really do open TSA locks
Last year, the Washington Post published a story on airport luggage handling that contained unobscured images of the “backdoor” keys of the Transportation...
-

 148Malware
148MalwareDutch Police Arrest Alleged CoinVault Ransomware Authors
Ransomware has emerged as major threat to consumers and businesses in recent years, and law enforcement agencies and security researchers have taken...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




