Featured News
-

 223Password
223PasswordiOS 9 security flaw lets attackers access device through Siri
Apple’s iOS 9 contains a security flaw that lets cybercriminals gain limited access to a device through Siri.
-

 111Malware
111MalwareHey Scandos, missed that parcel? Here’s some ransomware instead
Variant of CryptoLocker makes an unwelcome appearance. Spam emails disguised as messages from local post offices – but actually packing the latest...
-
 165Incidents
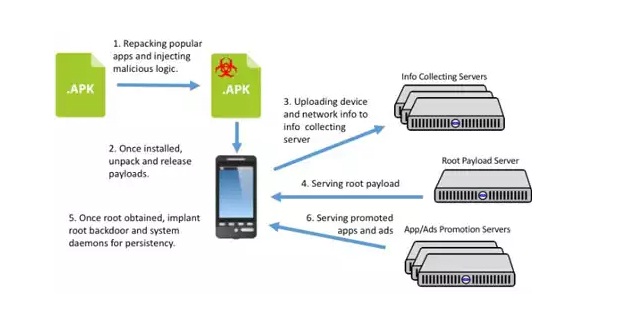
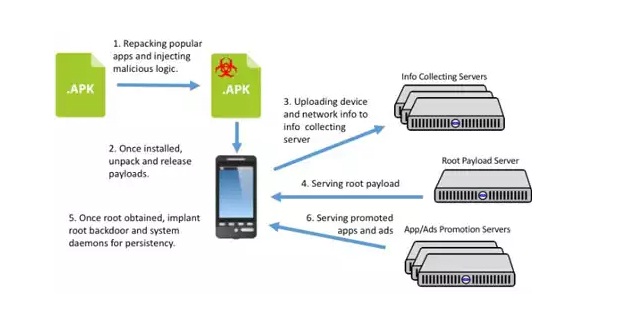
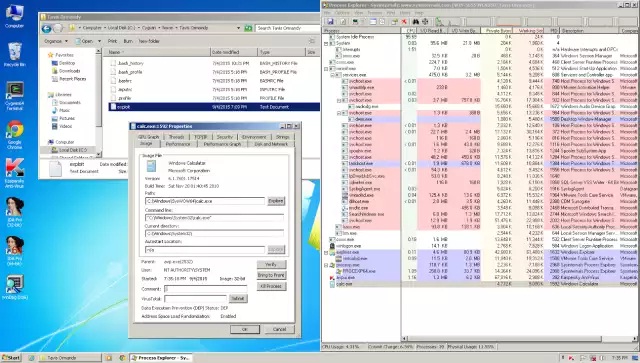
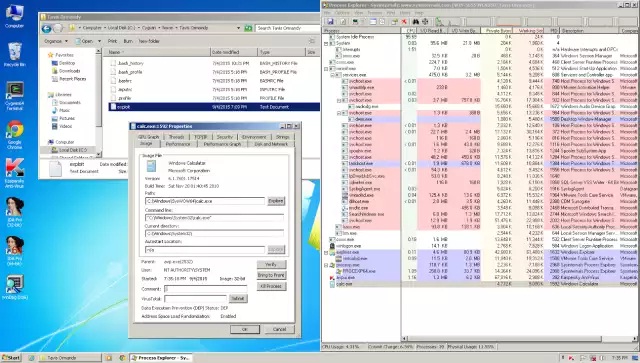
165IncidentsChinese promotion company hijacks Android devices around the world
A Chinese mobile app promotion company has created malicious adware that allows them to gain complete control of users’ Android devices. The...
-

 72Data Security
72Data SecurityAn Introduction to Hardware Hacking: the RIPE Atlas probe
RIPE NCC is building the largest Internet measurement network ever made. RIPE Atlas employs a global network of probes that measure Internet...
-

 191Incidents
191IncidentsFingerprints of over 5.6 Million Americans Stolen During the OPM Hack
The data breach at the US Office of Personnel Management (OPM) is slowly shaping up to be one of the biggest hacks...
-
 161Vulnerabilities
161VulnerabilitiesSecurity wares like Kaspersky AV can make you more vulnerable to attacks
Antivirus applications and other security software are supposed to make users more secure, but a growing body of research shows that in...
-

 178Geek
178GeekYour iOS 9 Lockscreen Can Be Bypassed in 30 Seconds
A security flaw has been discovered in Apple’s mobile software iOS 9 that lets strangers exploit Siri in order to bypass lock...
-

 317Geek
317GeekFacebook Following NSA Footsteps to Spy on Users: Belgium’s Privacy Advocate
In June this year, we reported how Facebook was sued by Belgium’s Privacy Commission (BPC) for tracking users even those who never made...
-

 322Cyber Events
322Cyber EventsUS Navy Developing Cyber Protection System to Protect Ships from Cyberattacks
The experts over at United States Navy are busy in the development of a cyber-protection system, codenamed RHIMES (the Resilient Hull, Mechanical,...
-

 280Geek
280GeekHaving Nude Selfies on Phone May Send You to Prison in the U.S.
A high schooler from North Carolina and his girlfriend are expecting prosecution both as minor victims and adult culprits for keeping nude...
-

 317Geek
317GeekHere’s How Someone Made a PiPhone- A Raspberry Pi Based Smartphone
Short Bytes: In this article, I’m going to share how someone made a “PiPhone”. Well, as the name suggests, PiPhone is a...
-

 332Geek
332GeekApple XcodeGhost Malware: List of iOS Apps You Should Delete Immediately
Apple’s App Store in China has apparently been penetrated by Hackers which experts say has placed the devices of hundreds of millions...
-
 120Scams
120ScamsCriminals, linguistics, literacy and attribution
Linguistics and some form of textual analysis can be helpful in analysing malware and scams. Regional attribution, though, still requires caution.
-
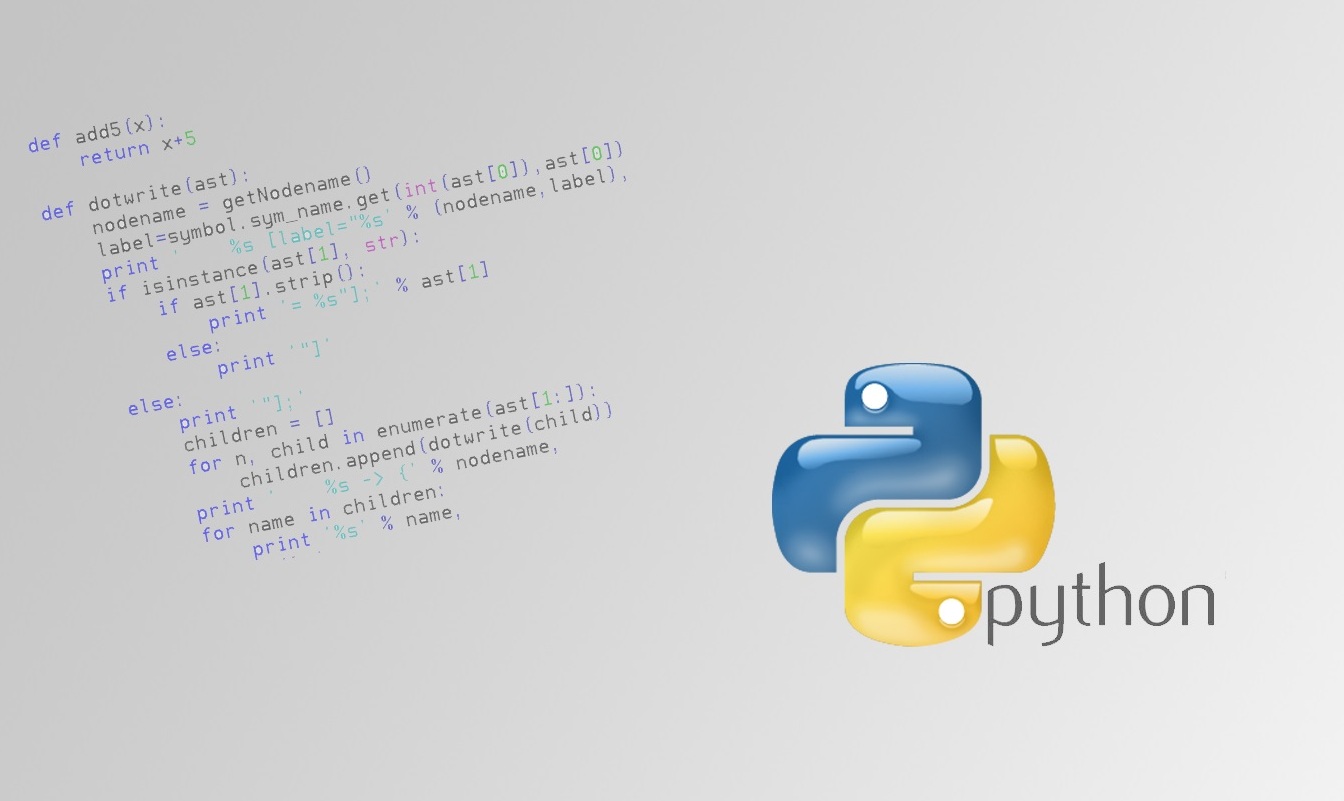
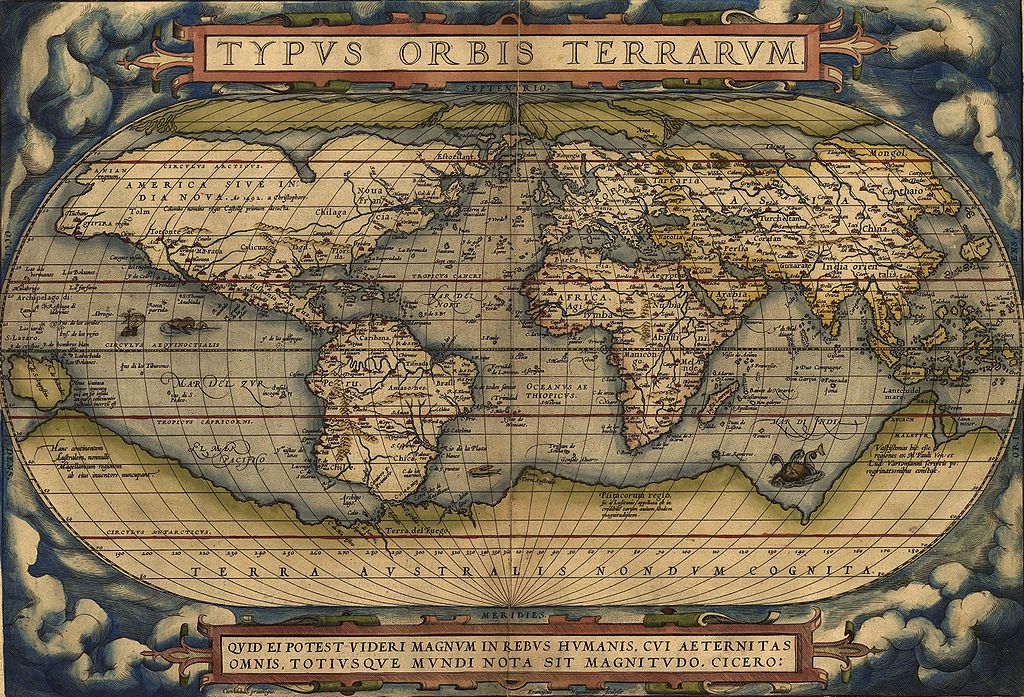
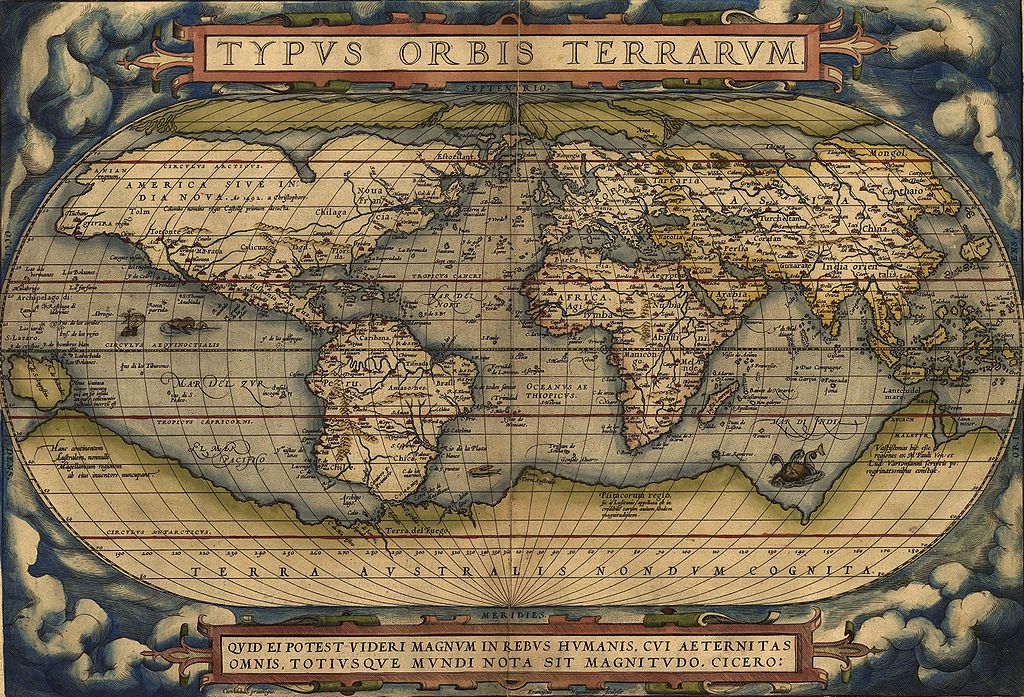
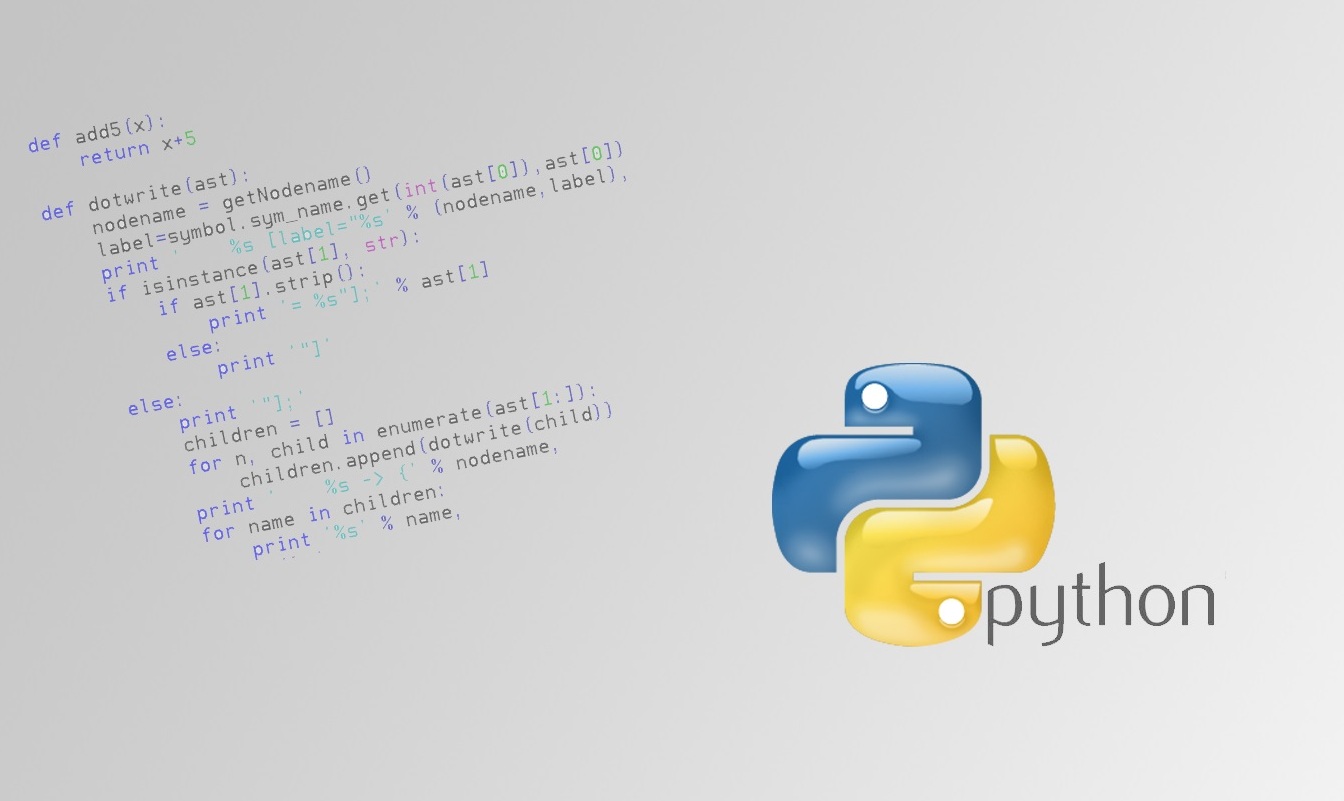 256Geek
256GeekLearn it Faster: The Entire Python Language in a Single Image
Short Bytes: What if you had to study one single page to get the complete idea of a programming language? In this...
-

 169Vulnerabilities
169VulnerabilitiesWestern Digital My Cloud Devices Can Be Hacked by Local or Remote Attackers
Security researchers at VerSprite have tested and discovered a few vulnerabilities in Western Digital’s My Cloud NAS (Network Attached Storage) hard drive,...
-
 76Malware
76MalwareNew Adware Facilitates the Distribution of Trojans for Mac Users
A new piece of adware that serves as an entry point for future trojan infections was discovered by Dr.Web security researchers. This...
-

 129Incidents
129IncidentsApple hack exposes flaws in building apps in China
China’s “Great Firewall” may have been partly to blame for the first major attack on Apple Inc’s (AAPL.O) App Store, but experts...
-
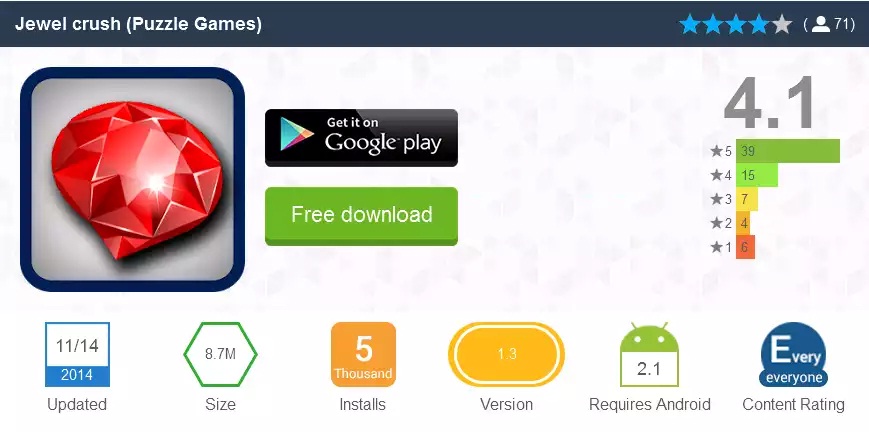
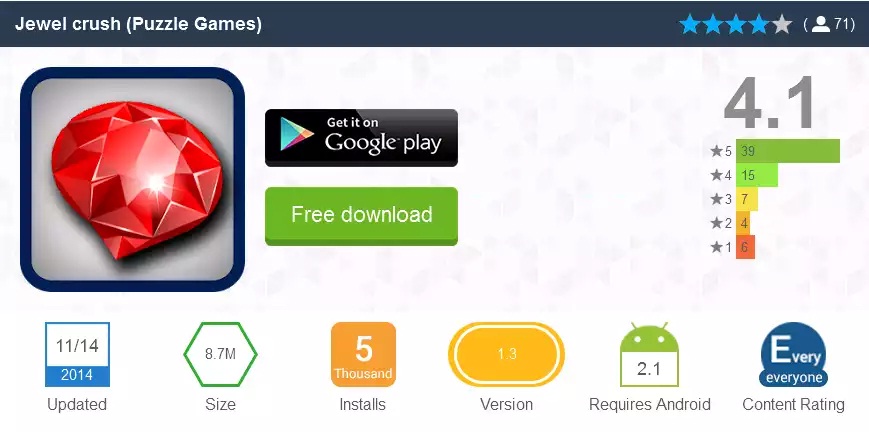 169Malware
169MalwareAndroid trojan drops in, despite Google’s Bouncer
We at ESET recently discovered an interesting stealth attack on Android users, an app that is a regular game but with one...
-

 315Geek
315GeekUS Air Force EC-130H Aircraft with Hacking Kit can Hack Enemy Networks
United States Air Force at the Air and Space conference held in Maryland, has unveiled a specifically designed aircraft named EC-130H Compass Call that...
-

 166Vulnerabilities
166VulnerabilitiesModel Assesses Readiness to Accept Outside Vulnerability Reports
The proliferation of independent and vendor-sponsored bug bounties has not only put some money in researchers’ pockets, but has also forced enterprises—and...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




