Featured News
-

 206Geek
206GeekDo You Believe in Aliens? Well, Edward Snowden Does
Edward Snowden claims that if the technology keeps on becoming sophisticated and flawless then we may never be able to locate aliens...
-
 190Data Security
190Data SecurityExploit broker offers $1 million for reliable iOS 9 exploit
Here’s a treat for hackers and security researchers who don’t mind selling information about zero-day vulnerabilities to the highest bidder: Zerodium, the...
-
 388Hacked
388HackedWorld’s Biggest 0-day Bug Bounty Program: Hack Apple iOS 9 to Win $1,000,000
Short Bytes: Security firm Zerodium has launched “The Million Dollar iOS 9 Bug Bounty”, that offers $1 million for finding vulnerabilities and...
-

 245Data Security
245Data SecuritySoon, you may not be able to delete WhatsApp messages for 90 days
Govt mulls a policy that requires users to save messages, and hand them over to law enforcement agencies, if asked. Deleting WhatsApp...
-

 176Vulnerabilities
176VulnerabilitiesAdobe Patches 23 Critical Vulnerabilities in Flash Player
Adobe has released a Flash Player update that addresses 23 critical vulnerabilities in the software, many which can lead to code execution....
-

 189Malware
189MalwareTop QLD sex shop cops Cryptowall lock; cops flop as state biz popped
Cryptowall attackers are smashing businesses in the Australian state of Queensland, according to the owner of a Townsville sex shop which has...
-

 155Geek
155GeekGhost Push Android Malware Responsible for Infecting 600k New Users Daily
The Ghost Push malware comes with those Android apps that are available at non-Google app stores. The newly discovered Android malware dubbed as Ghost Push Malware has...
-

 208Vulnerabilities
208VulnerabilitiesAndroid Malware Steals Money from Your Bank Account, Hides SMS Transaction Alerts
New Android malware was discovered, able to steal money from online banking accounts, and hide SMS notifications coming to confirm financial transactions....
-
 378Hacked
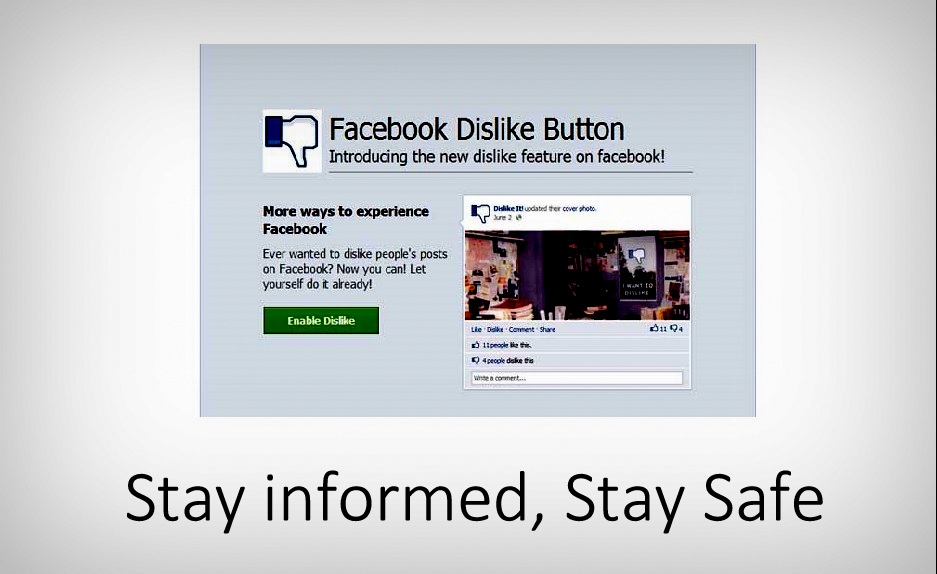
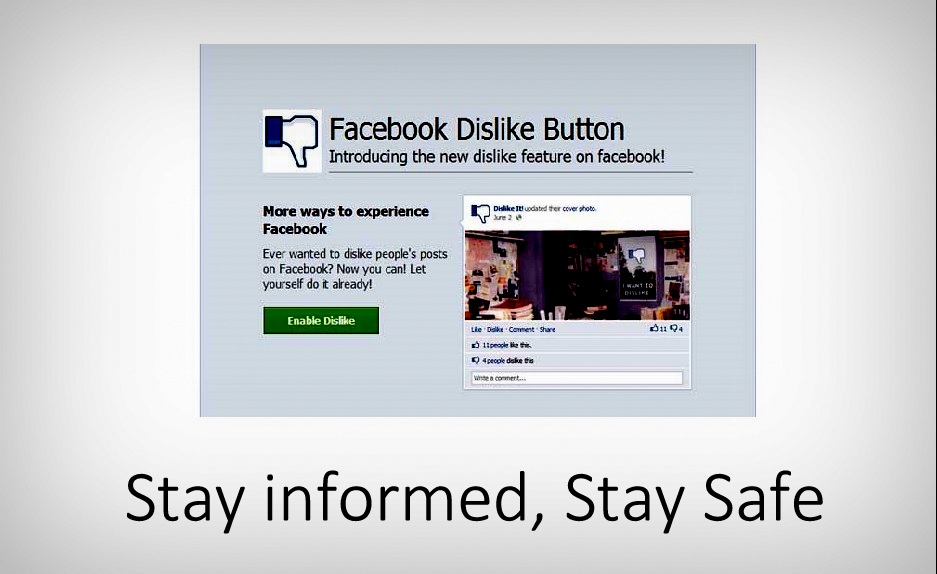
378HackedStay Informed, Stay Away from Facebook Dislike Button Scams
Short Bytes: It’s reported that scammers are taking advantage of Facebook Dislike button anticipation and they’re using the Facebook users. These scams trick...
-

 89Data Security
89Data SecurityBitcoinist Weekly News Re-Hash: BitPay Hack, California Bitcoin Bill Dies
After two weeks of sharp, last minute changes in the Bitcoin price, the markets caught a break this week, with the price...
-

 100Hacked
100HackedIndia’s New Encryption Policy is Ridiculous, Deleting Your Chats Could Soon Become Illegal
Short Bytes: The government of India doesn’t understand the concept of online privacy and the importance of encryption. A new government body...
-

 74Malware
74MalwareApple removes hundreds of malicious apps after major malware attack
Apple has removed more than 300 malicious apps after confirming the first major breach to its iOS app store.
-
 74Data Security
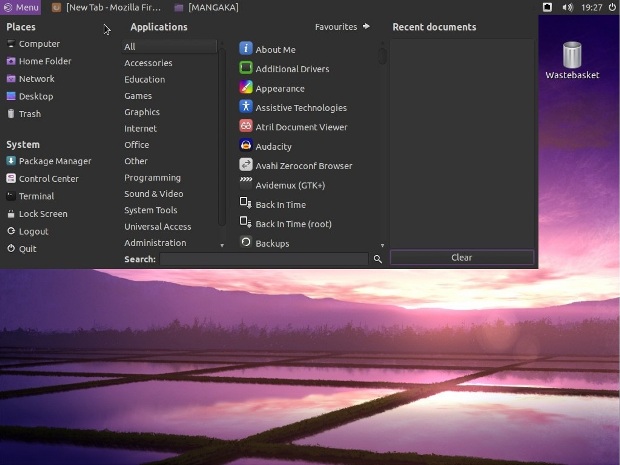
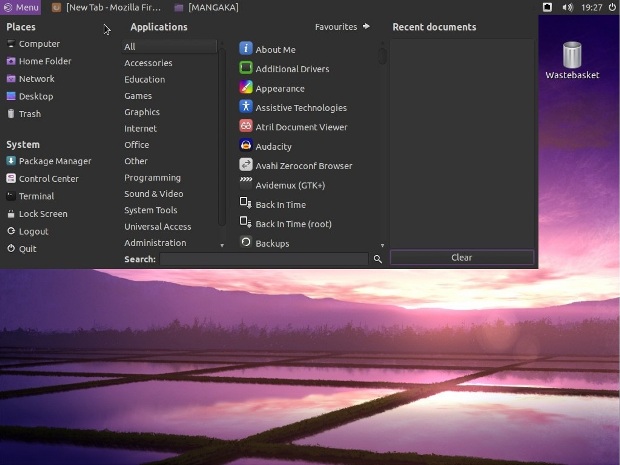
74Data SecurityLinux Mangaka Mou Arrives for Anime and Manga Fans, Based on Ubuntu 14.04 LTS
Just a few minutes ago, September 20, Animesoft International had the great pleasure of informing Softpedia about the immediate availability for download...
-

 178Incidents
178IncidentsUS Air Force Creates an Airplane for Hacking Enemy Military Networks
At the Air Force Association Air & Space conference in National Harbor, Maryland (near Washington), Major General Burke Wilson revealed a new...
-

 217Data Security
217Data SecurityHow malware finally infected Apple iOS apps: XCodeGhost
Hackers can’t easily get malware directly in iOS apps so they’re taking a different approach: Modifying the programming environment that Apple provides...
-

 214Incidents
214IncidentsAnonymous Philippines Hacks Telecom Commission Site Against Slow Internet Speed
Anonymous Philippines, an affiliate of the online hacktivist group Anonymous, hacked and defaced the official website of the country’s National Telecommunications Commission (NTC) Sunday...
-

 238Geek
238GeekScammers Targeting Facebook Users with Dislike Button Scam
New Dislike button scam has started to make rounds on the Facebook, one of the most popular and widely used social media...
-
 369How To
369How ToGetting Started With Docker – Intro to Containers World (Part -1)
Short Bytes: Linux containers (LXC) are very popular these days among developers and companies (perhaps due to Docker, which leverages LXC on the...
-

 268News
268NewsHow Your ATM Card Data Could Get Hacked
Security experts have warned ATM (Automated Teller Machine) users to stay clear from suspicious ATMs for past several years because of numerous...
-
 238Geek
238Geek“My First Line of Code”: Linux Creator Linus Torvalds
Short Bytes: Linus Torvalds is the creator of Linux and he still decides what will happen in the world of Linux. Read...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




