Featured News
-
 75Data Security
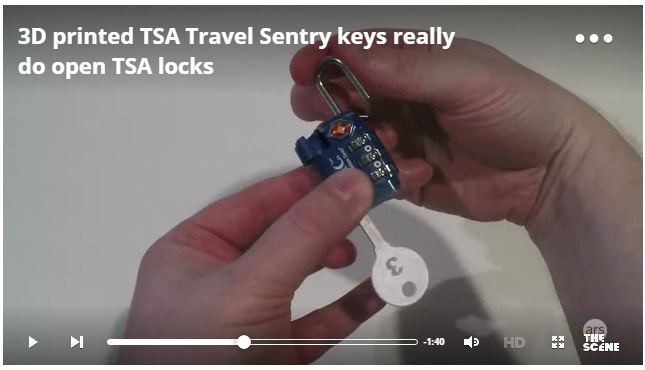
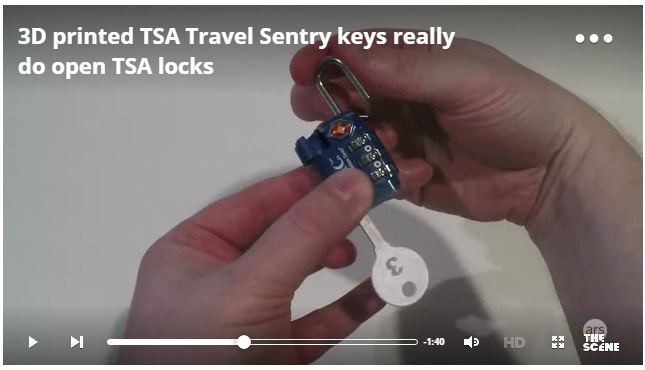
75Data Security3D printed TSA Travel Sentry keys really do open TSA locks
Last year, the Washington Post published a story on airport luggage handling that contained unobscured images of the “backdoor” keys of the Transportation...
-

 148Malware
148MalwareDutch Police Arrest Alleged CoinVault Ransomware Authors
Ransomware has emerged as major threat to consumers and businesses in recent years, and law enforcement agencies and security researchers have taken...
-
 101Malware
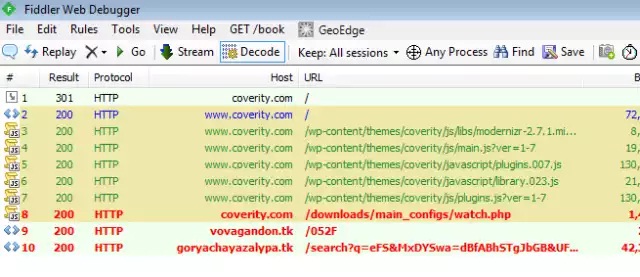
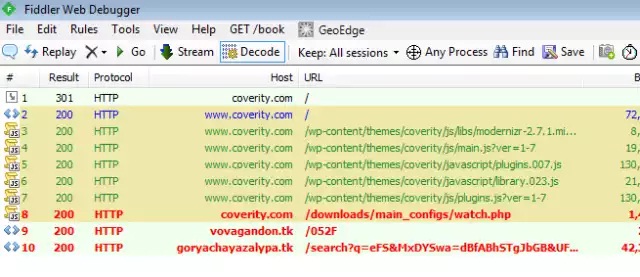
101MalwareActive malware campaign uses thousands of WordPress sites to infect visitors
15-day-old campaign has spiked in past 48 hours, with >5,000 new infections daily. Attackers have hijacked thousands of websites running the WordPress...
-

 172Geek
172GeekAVG Sells Your Data To Third Parties To Make Money
Antivirus and Security vendor AVG, based in Czech Republic and creator of one of the world’s leading antivirus software collections, is excited...
-
 105Cyber Crime
105Cyber CrimeHackers Using Amazon As A Bait For Phishing Attacks
A new phishing campaign has been doing the rounds on the Internet in which hackers are using Amazon UK’s fake email message...
-

 194Geek
194GeekSuspected Bomb Maker to Social Media Hero: Ahmed The Clock Boy’s Enviable Invite List
The Internet and primarily Social Media has catapulted Ahmed Mohammed into an overnight celebrity. Ahmed, a 14-year-old Muslim schoolboy from Texas was...
-

 178Geek
178GeekFacebook Joins Hands with Germany to Counter Anti-Refugee Hate Speech
The social media has lately been criticized greatly for reacting leisurely in eliminating racist images/ comments and xenophobic posts from the site,...
-

 207Geek
207GeekFacebook Users With Lots of Friends Could Be Psychologically Harmed, Study
Facebook users with a large number of friends having different characteristics could be at risk of being harmed psychologically, emotionally and even...
-
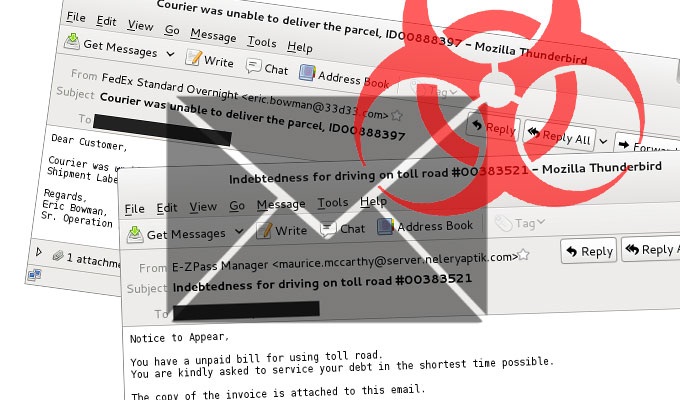
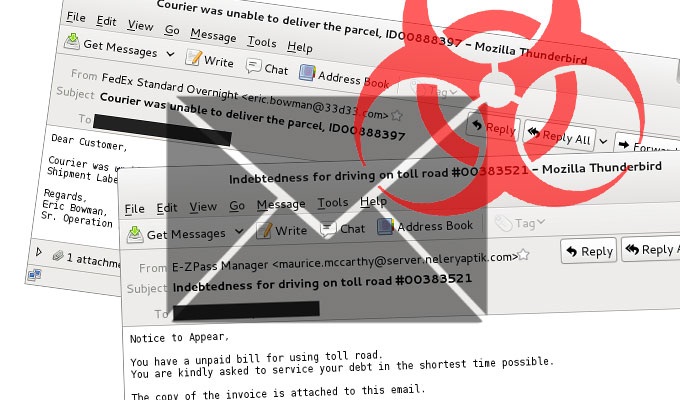 92Malware
92MalwareSpam Campaign Continuing to Serve Up Malicious .js Files
A malicious spam campaign that’s been doling out zipped Javascript (.js) files remains an issue, the SANS Internet Storm Center warns. The...
-

 149Data Security
149Data SecurityNine major banks working on Bitcoin-like block chain tech for market trading
JP Morgan Chase, Credit Suisse, RBS, and Barclays among banks backing effort. The banks of the world are taking a page from...
-
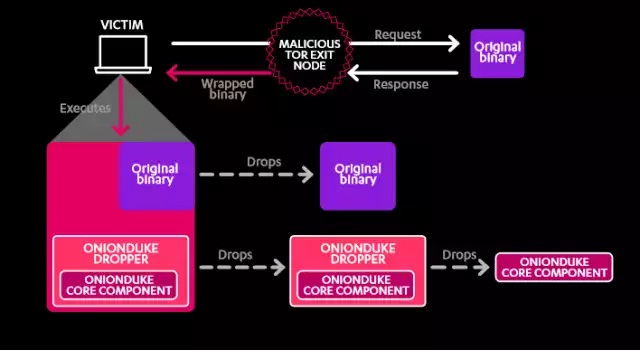
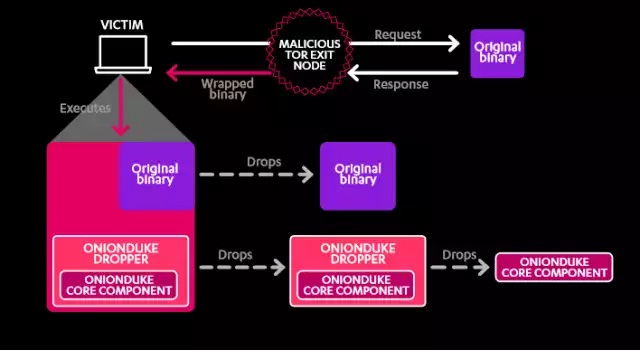 97Malware
97MalwareSeven years of malware linked to Russian state-backed cyberespionage
F-Secure report details “The Dukes” malware family and its Russian connections. For the past seven years, a cyberespionage group operating out of...
-
 287Vulnerabilities
287VulnerabilitiesMicrosoft Patches XSS Vulnerability in SharePoint 2013
SharePoint, one of the tools included with Microsoft Office’s server suite, has been patched to protect users from a persistent XSS (cross-site...
-

 178Vulnerabilities
178VulnerabilitiesApple mitigates but doesn’t fully fix critical iOS Airdrop vulnerability
Proof-of-concept exploit installs malicious app on nearby iPhones. Apple has mitigated a critical iOS vulnerability that allows attackers within Bluetooth range of...
-

 181Cyber Crime
181Cyber CrimeRussian hacker Responsible for Massive Data Breach Finally Pleads Guilty
The infamous Russian hacker, Vladimir Drinkman, has admitted his contribution in what has been regarded by the Justice Department as “the largest...
-

 288Geek
288GeekFacebook Dislike Button is coming but has some disadvantages
Are you also one of those like me who has always believed Facebook needed a Dislike button? If yes, then there is...
-
 272How To
272How ToiOS 9 Software Update Failed? Here’s How to Get Update Using Your Computer
Short Bytes: The iOS 9 update is available for download, but lots of Apple users are complaining that before the upgrade even begins...
-
 294Hacked
294HackedDid NSA and GCHQ Spy on You? Here’s How to Find Out and Complain
Short Bytes: Do you have a feeling that NSA and its British counterpart GCHQ spied on you? Well, how to confirm this? Using...
-
 349Geek
349GeekDid You Know? 13 Amazing Facts About Linux That Will Surprise You
ShortBytes: Linux kernel is one of the most popular and powerful platforms to work upon, but do you know all the facts about...
-
 205Hacked
205HackedThis Computer Chip Self-destructs in 10 Seconds to Protect Your Secrets
Short Bytes: PARC has developed a self-destructing computer chip under DARPA’s vanishing programmable resource project. The chip, made of Gorilla glass, will...
-

 102Vulnerabilities
102VulnerabilitiesAndroid’s 5.x Lock Screen may be bypassed by attackers
Android devices may be protected by a lock screen which requires some form of authentication before access to most phone features, its...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




