Featured News
-

 238News
238NewsAnonymous Hacks Vietnam Govt websites Against Human Rights Abuse
The online hacktivists affiliated to Anonymous, AntiSec and HagashTeam conducted a cyber attack on Vietnamese government websites against online censorship and human...
-

 194News
194NewsScreenshot Malware Spying On Online Poker Players
A unique malware has been found by security experts which spies on the players of online poker gaming sites, specifically Full Tilt...
-
 278Hacked
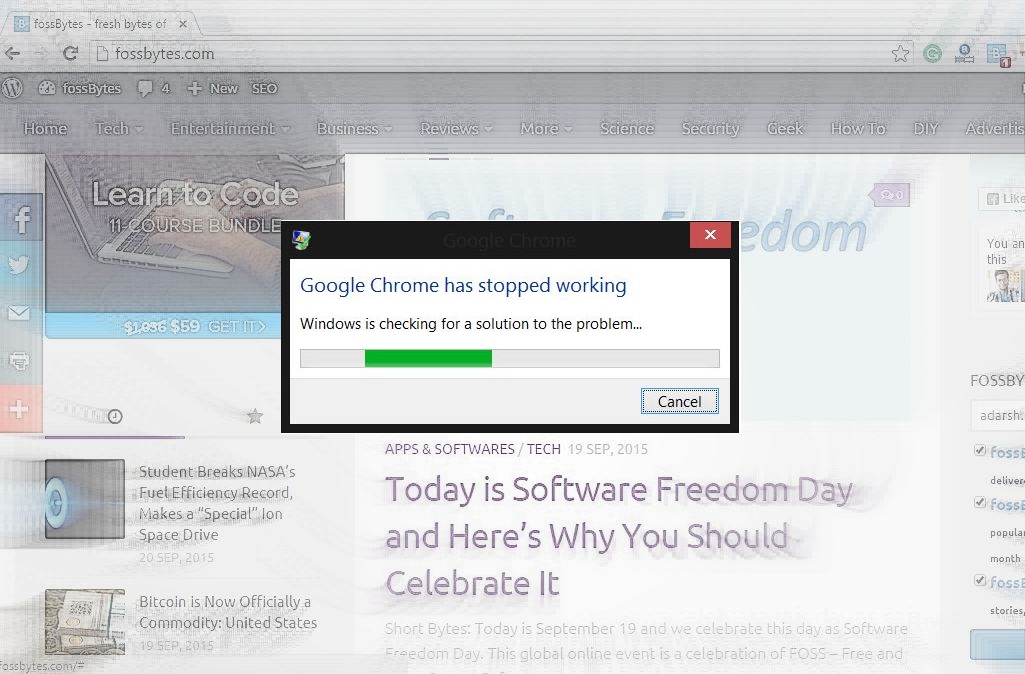
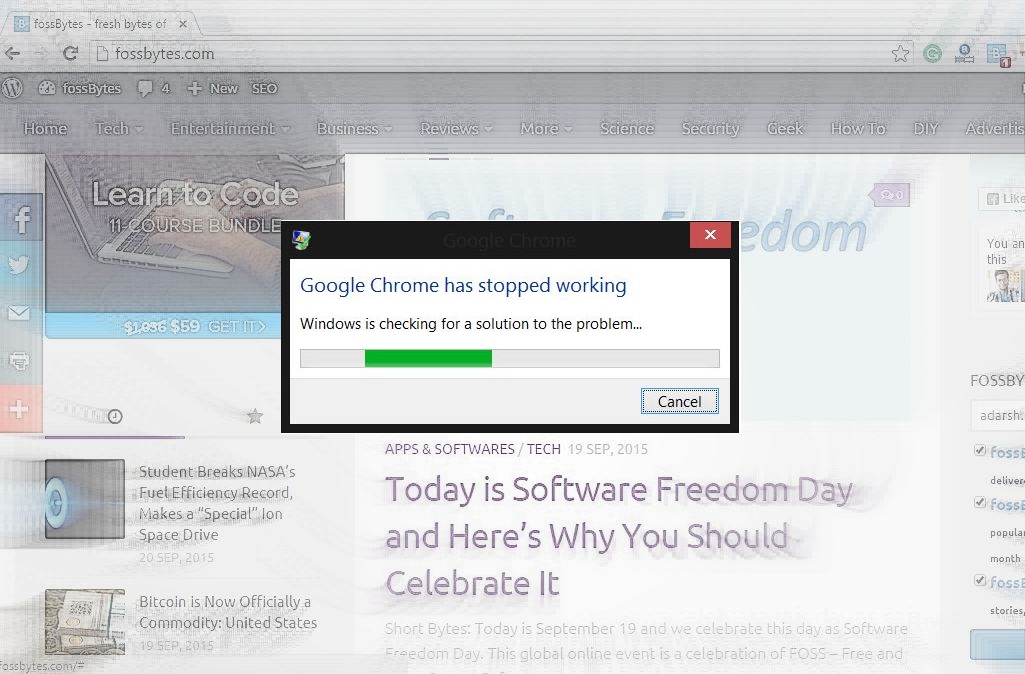
278HackedHow and Why Crash Google Chrome With These 16 Characters in 2 Seconds
Short Bytes: Do you want to crash someone’s Google Chrome just for the heck of it? Here’s how to do it with...
-

 308Geek
308GeekMicrosoft Windows Devices Responsible For 80% of Malware Infections
Microsoft Windows, in spite of having an insignificant share in the mobile market, is the leading operating system that is responsible for...
-
 322News
322NewsPhishing Attack Causes Bitcoin Payment Processor BitPay to Lose $1.8M
BitPay the Atlanta-based Bitcoin payment processor had been hit by a massive phishing attack costing the company $1.8 million. Verified by the...
-
 168Data Security
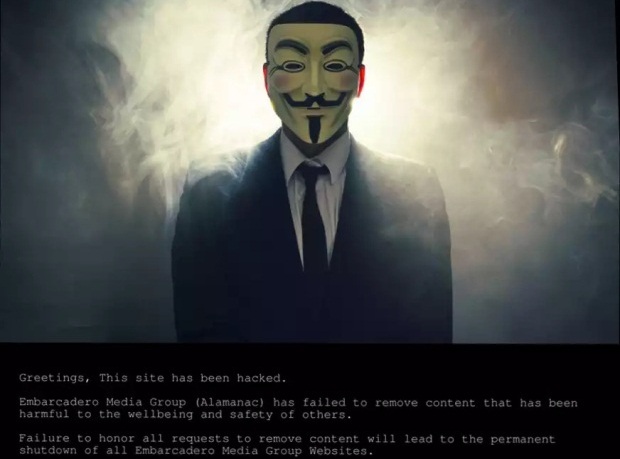
168Data SecurityHackers Hold Silicon Valley’s Hometown Newspapers Hostage
Sometime yesterday, 17 September, hackers took over the websites of Silicon Valley’s Embarcadero Media Group, publisher of the Palo Alto Weekly, theAlmanac,...
-
 150Malware
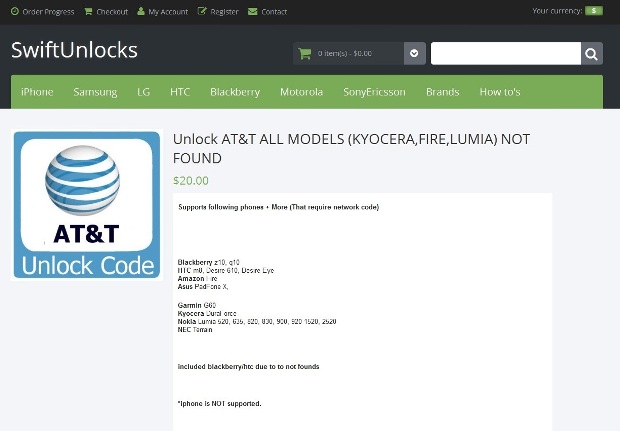
150MalwareAT&T Employees Installed Malware on Their PCs to Aid Phone Unlocking Service
AT&T has filed a lawsuit against 3 former call center employees, accusing them of installing malware on their servers with the purpose...
-

 102Data Security
102Data SecurityHack Brief: Malware Sneaks Into the Chinese iOS App Store
THE APPLE ECOSYSTEM is well known for very rarely letting any dodgy apps enter it because of the company’s stringent security checks....
-

 127Malware
127MalwareNew PoS Trojan Can Download Other Malware, Launch DDOS Attacks
The world of computer viruses and antivirus solutions is in a constant change, with cyber-crooks evolving their code and cyber-security firms trying...
-

 197Vulnerabilities
197VulnerabilitiesD-Link Accidentally Leaks Private Code-Signing Keys
A simple mistake by networking gear manufacturer D-Link could have opened the door for costly damage. Private keys used to sign software...
-
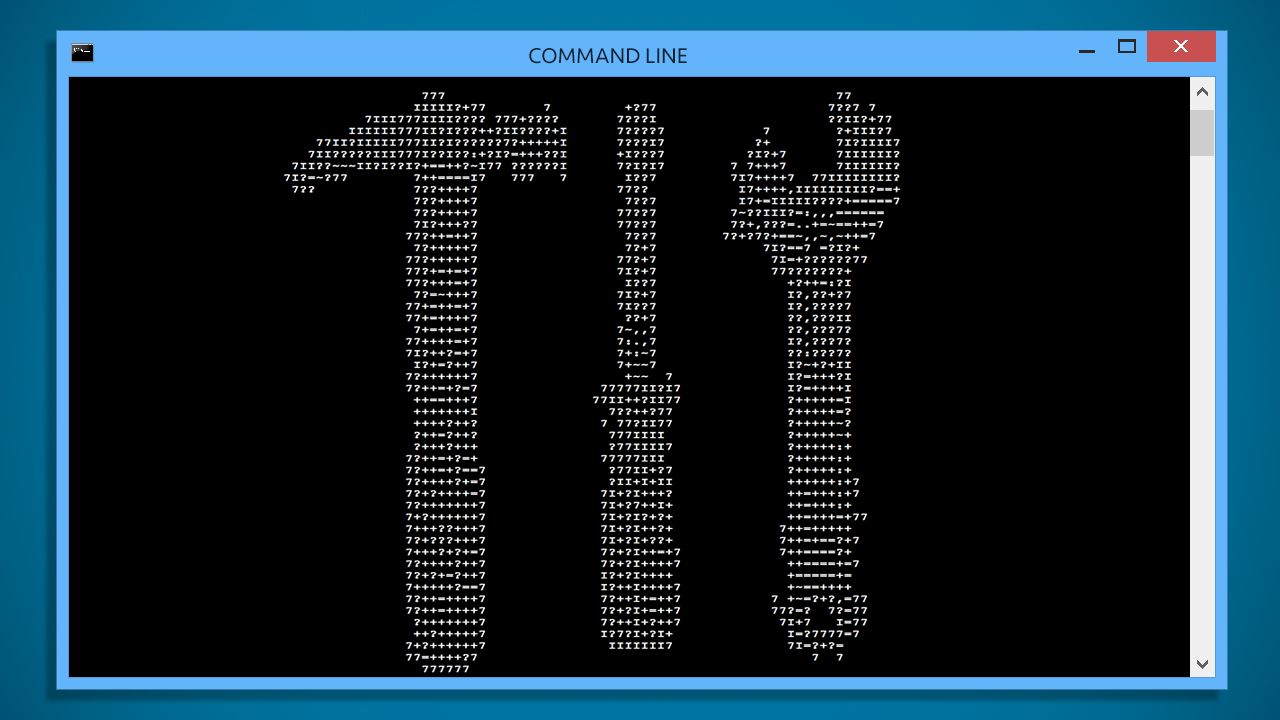
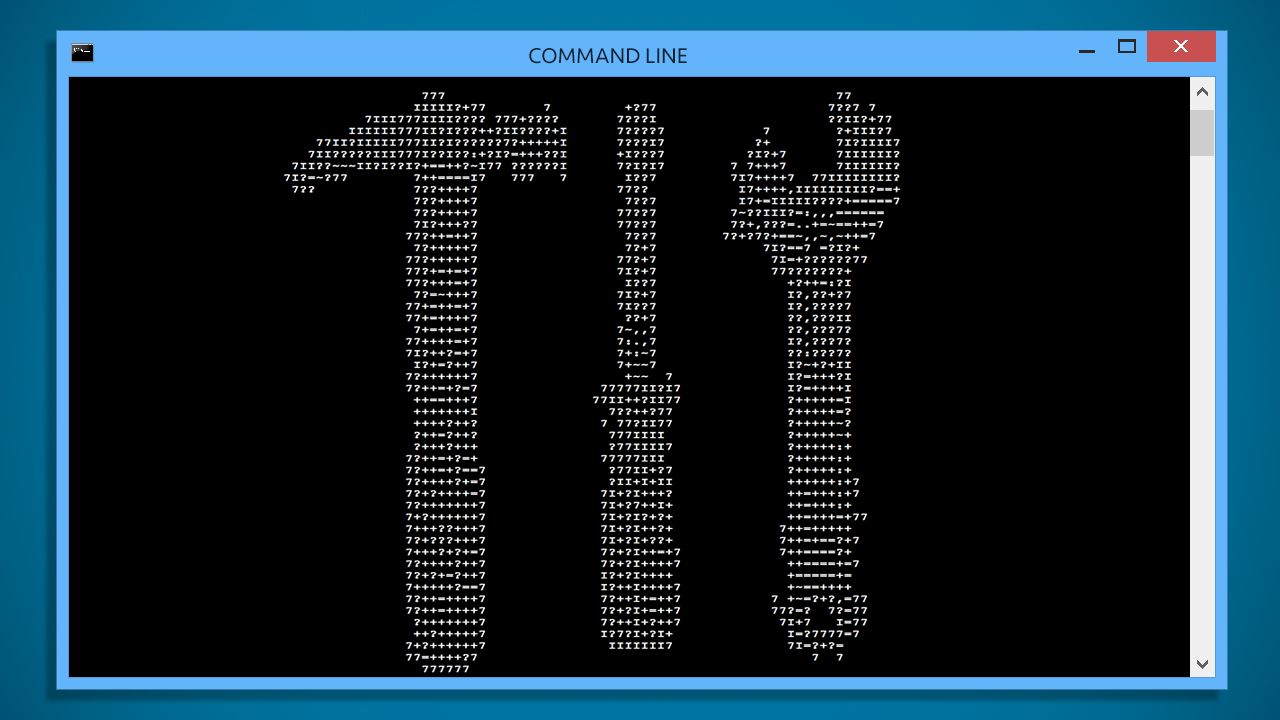 226Tricks & How To's
226Tricks & How To's10 Windows Commands you need to know for Troubleshooting
The command line is an interface for typing commands directly to a computer’s operating system. It is usually used to resolve Microsoft...
-

 287Hacked
287Hacked“seL4” is an Unhackable Kernel for Keeping All Computers Safe From Cyberattack
Short Bytes: The Australian national research agency Data61 has developed an unhackable kernel named seL4 and proved its unhackable property mathematically. The kernel...
-
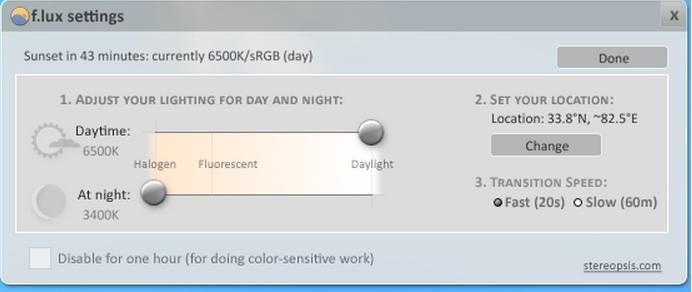
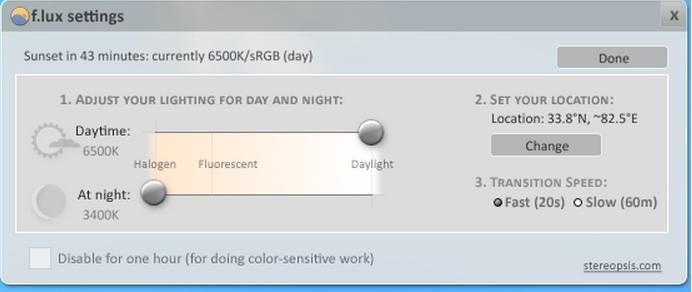 174Tricks & How To's
174Tricks & How To'sSave your eyes from Computer Strain
No more watery eyes, when you wake up from sleep in the middle of the night to work on your bright computer...
-

 311Data Security
311Data SecurityRussian Hacker who stole 160 million credit card details gets sentenced for 30 years in prison
Russian national pleads guilty in global hacking scheme. Russian Hacker Vladimir Drinkman faces 30 years sentence after pleading guilty to hacking NASDAQ,...
-
 76Malware
76MalwareThe evolution of ransomware: From PC Cyborg to a service for sale
A look back at how ransomware – a type of malware used mostly for hijacking user data – has evolved from the...
-
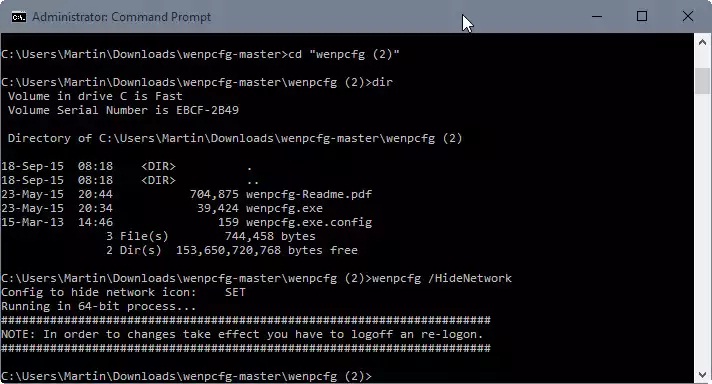
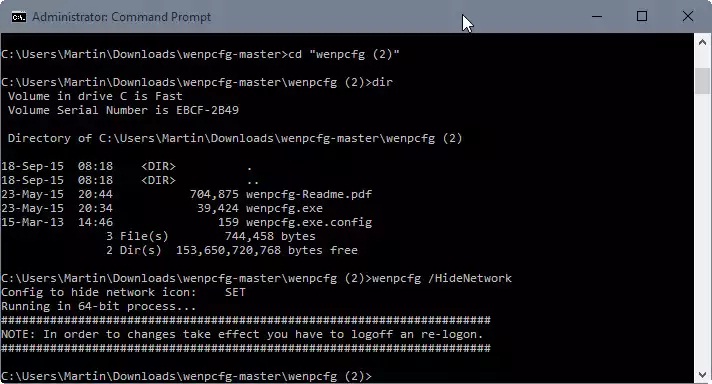 101Data Security
101Data SecurityRemove Libraries, Network, Homegroup and other links from File Explorer
When you open File Explorer in Windows 10, the system’s default file browsing and management tool, you will notice immediately that it...
-
 77Data Security
77Data Security3D printed TSA Travel Sentry keys really do open TSA locks
Last year, the Washington Post published a story on airport luggage handling that contained unobscured images of the “backdoor” keys of the Transportation...
-

 151Malware
151MalwareDutch Police Arrest Alleged CoinVault Ransomware Authors
Ransomware has emerged as major threat to consumers and businesses in recent years, and law enforcement agencies and security researchers have taken...
-
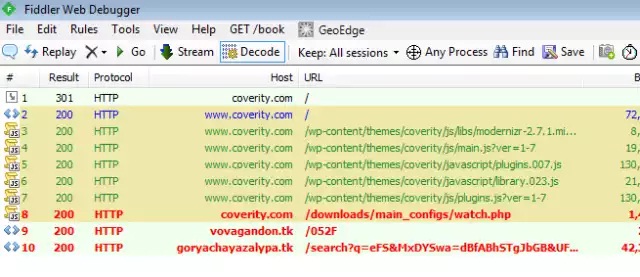
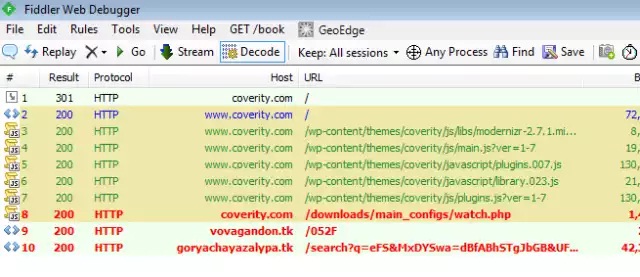 108Malware
108MalwareActive malware campaign uses thousands of WordPress sites to infect visitors
15-day-old campaign has spiked in past 48 hours, with >5,000 new infections daily. Attackers have hijacked thousands of websites running the WordPress...
-

 176Geek
176GeekAVG Sells Your Data To Third Parties To Make Money
Antivirus and Security vendor AVG, based in Czech Republic and creator of one of the world’s leading antivirus software collections, is excited...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




