Featured News
-
 278Hacked
278HackedThe Top 5 Most Hackable Cars You Shouldn’t Buy (And the Safest Ones)
Short Bytes: A forensic consultancy PT&C}|LWG Forensic Consulting Services has made a list of top 5 most hackable cars by performing a...
-

 154Cyber Crime
154Cyber CrimeHackers Can Infect ATM With Malware To Hold Your Card
Security researchers over at FireEye have discovered a serious security flaw within the ATM (Automated Teller Machine) that could be exploited by...
-

 298Geek
298GeekPosting @[4:0] in Facebook Comment Shows ‘Mark Zuckerberg’, it Won’t Get You Hacked
Get Mark Zuckerberg Displayed simply by typing @[4:0] as a Facebook Comment — This isn’t a hacking related issue so no need to be on high...
-

 226Geek
226GeekWindows 10 Lets Users Log into Their PC with a Picture Password
Since its release, Windows 10 is surrounded by controversies, but at the same time the operating system offers some mind-blowing features such as...
-

 191Geek
191GeekNew Android Malware Changes PIN Code and Demand Ransom
Android users need to be highly careful while using your smartphone as ESET researchers have identified simplocker, a new screen-locking malware that...
-
 190Hacked
190HackedNorth Korea Hacks Into Word Processor Used by South Korean Government
Short Bytes: According to the security firm FireEye, Hangul Word Processor program used by the South Korean government was recently hacked by North...
-
 220How To
220How ToCrack WPA & WPA2 with Cowpatty and Negpmk on Kali Linux
In this tutorial we are going to teach you How to crack WPA & WPA 2 with cowpatty and negpmk on Kali Linux. We...
-

 272Hacked
272HackedIntel Makes Automotive Security Review Board to Save Your Cars From Getting Hacked
Short Bytes: In the wake of recent car hacks and security breaches, Intel has planned to establish an Automotive Security Review Board (ASRB)...
-
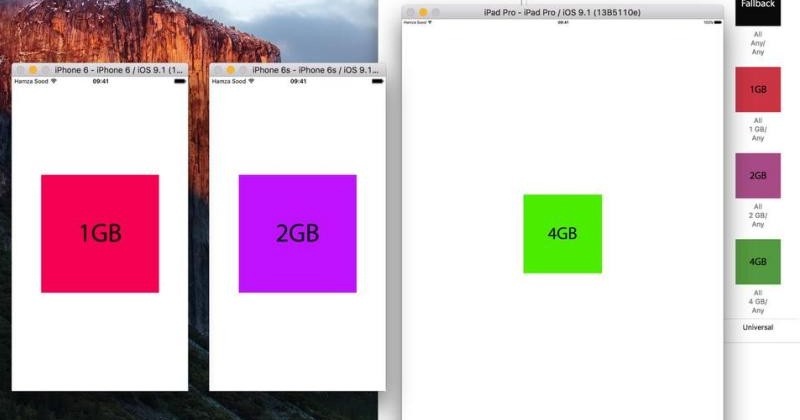
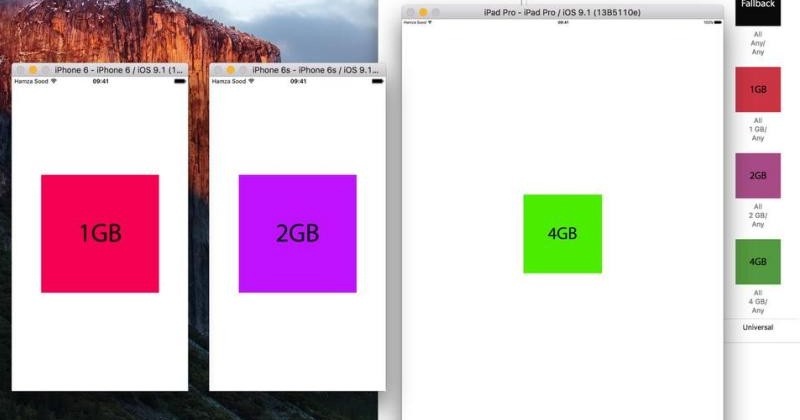 79Data Security
79Data SecurityXcode hack confirms 2GB RAM on iPhone 6s, 4GB on iPad Pro
Apple is traditionally mum on some details of its devices’ hardware, preferring to talk about how “B is X times faster than...
-

 72Data Security
72Data SecurityHow did jihadists hack into top UK ministerial emails if no security breach took place?
Answers on a postcard from Syria, please. GCHQ has declined to comment on a report in the Daily Telegraph this weekend, which...
-

 164Vulnerabilities
164VulnerabilitiesYokogawa patches widespread SCADA vulnerability
Networking process crashed by crafted packets. One of the world’s major suppliers of industrial networking kit, Japanese company Yokogawa, has alerted the...
-
 196Malware
196MalwareNorth Korea Installs Backdoor in South Korea’s Favorite Word Processor
Hackers linked to known North Korean attack points and methods exploited a zero-day vulnerability in the Hangul Word Processor (HWP), widely deployed...
-
Firewall
GlassWire – Best Firewall Software
GlassWire is a lot more than just a great firewall. The free firewall software monitors your network in an easy to understand...
-

 332How To
332How ToGetting Started With Raspberry Pi – Knowing Your Pi (Part – 1)
Short Bytes: The credit-card-sized Raspberry Pi was released long back in 2012 and it has grown to become one of the most...
-

 208Geek
208GeekWhat’s New in iOS 9 SDK?
Short Bytes: iOS 9 SDK includes new APIs and services that are enabling new categories of apps and features. Multitasking and gaming APIs...
-

 201News
201NewsSmartwatch Users Beware – Report Identifies Vulnerabilities in Wearable Devices
In the past, we reported how your wearable fitness trackers can be hacked. Now, The university of Illinois at Urbana-Champaign’s associate professor Romit Roy Choudhry...
-
 120Data Security
120Data SecuritySurvey Shows Most Americans are Fine with Backdoor in Their Devices
A recent survey from Vormetric revealed that people in the United States are OK with the addition of backdoors in their devices/software....
-

 203News
203NewsTop British Ministers Hacked by ISIS in Sophisticated Espionage Operation
Crucial information held by some of the most senior ministers of David Cameron (including Home Secretary Theresa May) has possibly landed in...
-

 292Cyber Crime
292Cyber CrimeSearching For Hacking Software Leads to Vulnerable Spammy Sites
Thousands of legit websites’ security has been compromised to secretly redirect the visitors, coming through specific search terms, to prospective fraudulent websites...
-
 117Geek
117GeekWordPress High CPU Load Bug After 4.3 “Billie” Upgrade and How to Fix it
Short Bytes: WordPress high CPU load bug – We faced it and I am guessing thousands of other blogs hosted on WordPress faced it too, when...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




