Featured News
-
 107Cyber Crime
107Cyber CrimeHackers Using Amazon As A Bait For Phishing Attacks
A new phishing campaign has been doing the rounds on the Internet in which hackers are using Amazon UK’s fake email message...
-

 198Geek
198GeekSuspected Bomb Maker to Social Media Hero: Ahmed The Clock Boy’s Enviable Invite List
The Internet and primarily Social Media has catapulted Ahmed Mohammed into an overnight celebrity. Ahmed, a 14-year-old Muslim schoolboy from Texas was...
-

 182Geek
182GeekFacebook Joins Hands with Germany to Counter Anti-Refugee Hate Speech
The social media has lately been criticized greatly for reacting leisurely in eliminating racist images/ comments and xenophobic posts from the site,...
-

 209Geek
209GeekFacebook Users With Lots of Friends Could Be Psychologically Harmed, Study
Facebook users with a large number of friends having different characteristics could be at risk of being harmed psychologically, emotionally and even...
-
 94Malware
94MalwareSpam Campaign Continuing to Serve Up Malicious .js Files
A malicious spam campaign that’s been doling out zipped Javascript (.js) files remains an issue, the SANS Internet Storm Center warns. The...
-

 151Data Security
151Data SecurityNine major banks working on Bitcoin-like block chain tech for market trading
JP Morgan Chase, Credit Suisse, RBS, and Barclays among banks backing effort. The banks of the world are taking a page from...
-
 99Malware
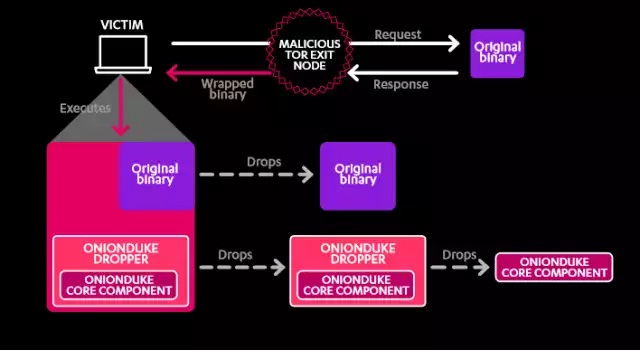
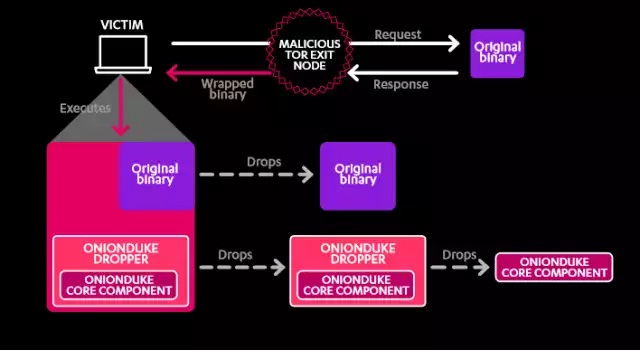
99MalwareSeven years of malware linked to Russian state-backed cyberespionage
F-Secure report details “The Dukes” malware family and its Russian connections. For the past seven years, a cyberespionage group operating out of...
-
 289Vulnerabilities
289VulnerabilitiesMicrosoft Patches XSS Vulnerability in SharePoint 2013
SharePoint, one of the tools included with Microsoft Office’s server suite, has been patched to protect users from a persistent XSS (cross-site...
-

 181Vulnerabilities
181VulnerabilitiesApple mitigates but doesn’t fully fix critical iOS Airdrop vulnerability
Proof-of-concept exploit installs malicious app on nearby iPhones. Apple has mitigated a critical iOS vulnerability that allows attackers within Bluetooth range of...
-

 184Cyber Crime
184Cyber CrimeRussian hacker Responsible for Massive Data Breach Finally Pleads Guilty
The infamous Russian hacker, Vladimir Drinkman, has admitted his contribution in what has been regarded by the Justice Department as “the largest...
-

 292Geek
292GeekFacebook Dislike Button is coming but has some disadvantages
Are you also one of those like me who has always believed Facebook needed a Dislike button? If yes, then there is...
-
 276How To
276How ToiOS 9 Software Update Failed? Here’s How to Get Update Using Your Computer
Short Bytes: The iOS 9 update is available for download, but lots of Apple users are complaining that before the upgrade even begins...
-
 299Hacked
299HackedDid NSA and GCHQ Spy on You? Here’s How to Find Out and Complain
Short Bytes: Do you have a feeling that NSA and its British counterpart GCHQ spied on you? Well, how to confirm this? Using...
-
 355Geek
355GeekDid You Know? 13 Amazing Facts About Linux That Will Surprise You
ShortBytes: Linux kernel is one of the most popular and powerful platforms to work upon, but do you know all the facts about...
-
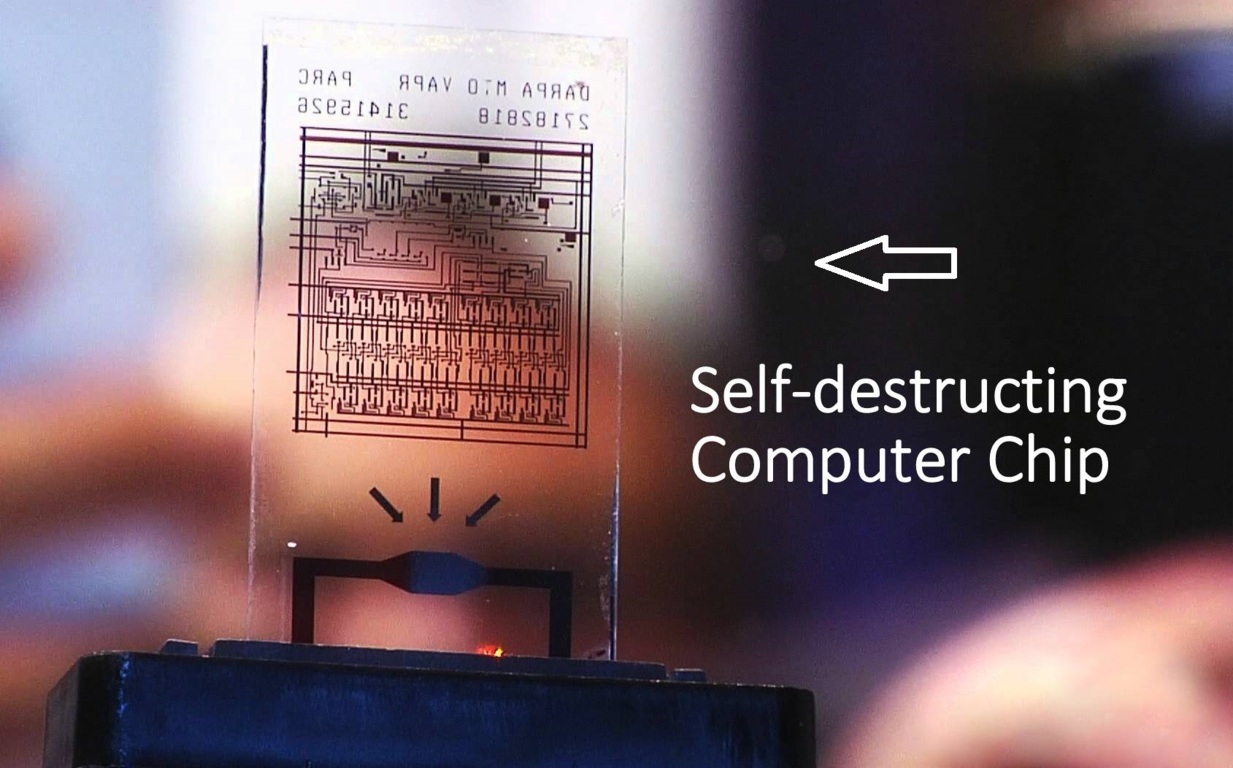
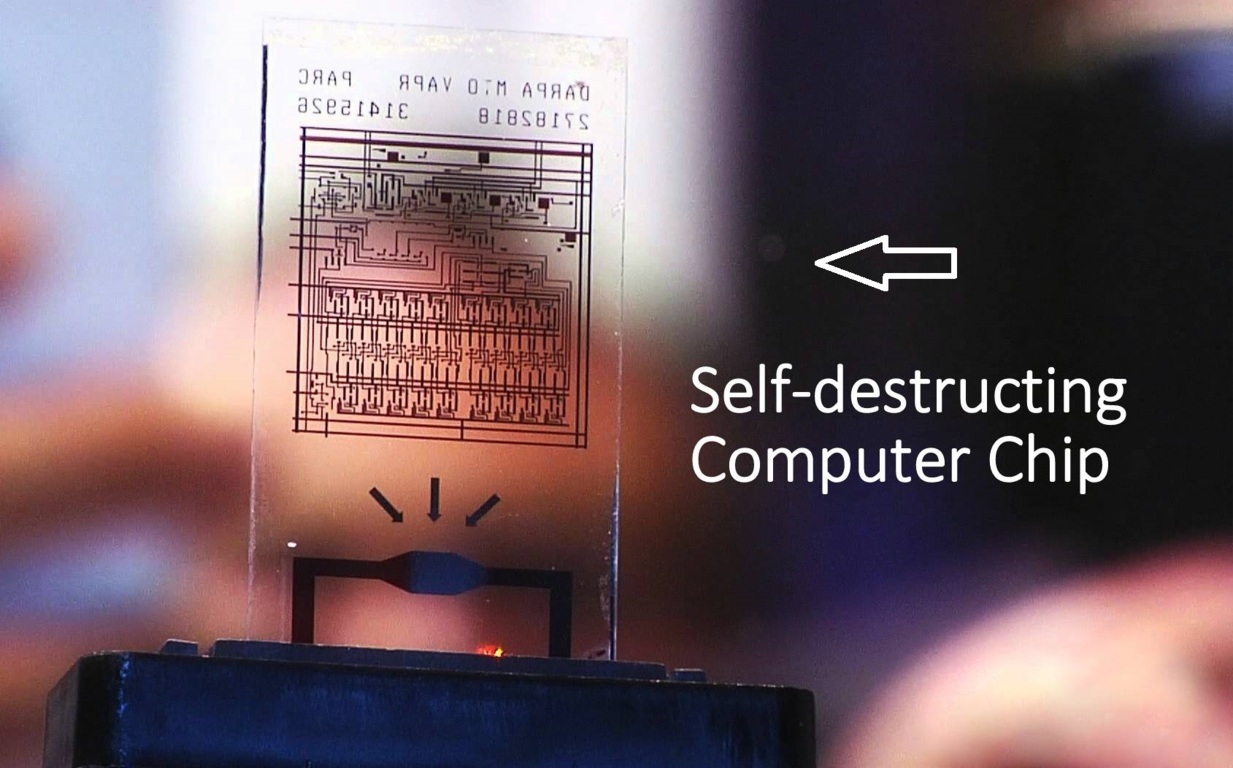 209Hacked
209HackedThis Computer Chip Self-destructs in 10 Seconds to Protect Your Secrets
Short Bytes: PARC has developed a self-destructing computer chip under DARPA’s vanishing programmable resource project. The chip, made of Gorilla glass, will...
-

 104Vulnerabilities
104VulnerabilitiesAndroid’s 5.x Lock Screen may be bypassed by attackers
Android devices may be protected by a lock screen which requires some form of authentication before access to most phone features, its...
-

 102Data Security
102Data SecurityFacebook sees a ‘dislike’ button in your future
In a Q&A session, CEO Mark Zuckerberg says Facebook will offer more choices than merely “like.” He also discusses virtual reality, artificial...
-

 162Vulnerabilities
162VulnerabilitiesWordPress Patches Serious Shortcodes Core Engine Vulnerability
WordPress core engine security vulnerabilities aren’t rare, but they are uncommon. Most issues affecting the integrity of sites running on the content...
-
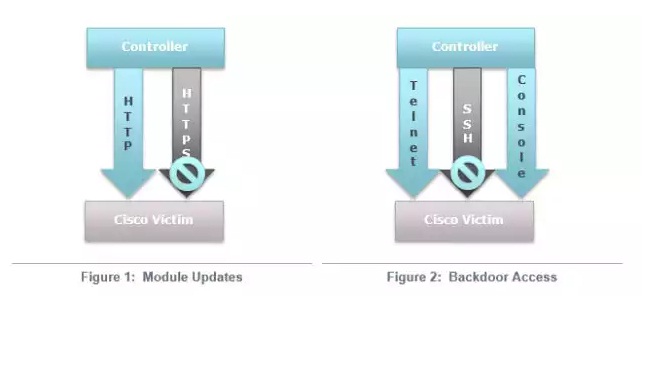
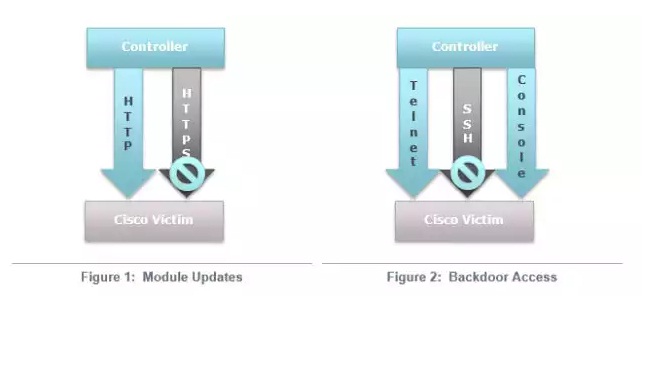 121Vulnerabilities
121VulnerabilitiesCisco routers in at least 4 countries infected by highly stealthy backdoor
More than a dozen routers in four countries infected with fully featured implants. Researchers have uncovered active and highly clandestine attacks that...
-
 178Malware
178MalwareCoreBot Adds New Capabilities, Transitions to Banking Trojan
As researchers expected it would, CoreBot, the credential-stealing malware that surfaced last month, has added a bevy of new capabilities and reinvented...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




