Featured News
-

 214Android Hacking
214Android HackingWhatsapp Tricks and Hacks 2015
List of Top tricks and hacks of 2015 #1 Use WhatsApp Without Your Mobile Number If you don’t want to use your...
-

 272Geek
272GeekFacebook Sued Again Over Its Creepy Facial Recognition Software
The social network’s face-recognition software has been sued again and to add salt to their wounds, privacy groups also have issued warnings....
-

 298Banking
298BankingCustomers of UK’s Metro Bank targeted by Twitter fraudsters
Be on the lookout for copycat social media accounts which may be attempting to lead your customers astray.
-

 172Data Security
172Data SecurityAshley Madison Hack Latest Reminder Stupid Passwords Are Stupid
The recent hack of fembot dating extramarital affairs website Ashley Madison, which resulted in data from millions of accounts being dumped online, has one more salutary...
-

 202Data Security
202Data SecuritySelf-Driving Cars Are Hackable
Jonathan Petit, security researcher at Security Innovation, Inc., has revealed he can easily fool the LiDAR sensors on any self-driving car to...
-
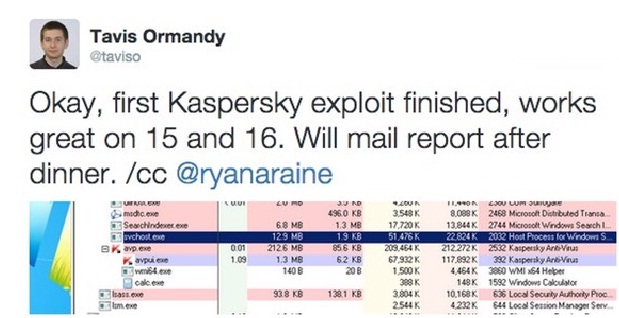
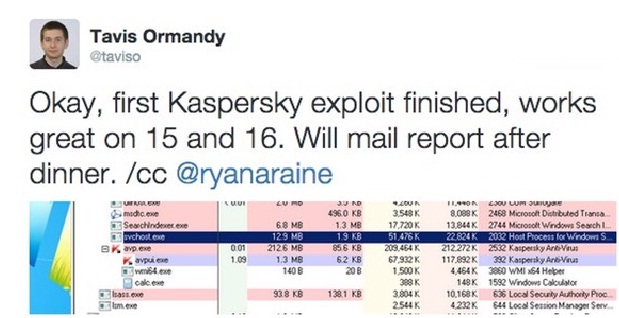 170Vulnerabilities
170VulnerabilitiesZero-day vulnerabilities reportedly found in Kaspersky and FireEye security products
Sounds like it’s going to be a busy few days for R&D and PR departments at least two security companies. This weekend,...
-

 93Data Security
93Data SecurityCoder pleads guilty to writing Gozi banking trojan
A man credited with helping to create the infamous Gozi banking malware has pled guilty in a US court. Deniss Calovskis, 30,...
-

 180Malware
180MalwareOutdated WordPress Sites Used to Deliver Teslacrypt Ransomware
Heimdal Security researchers have observed a new ransomware campaign that utilizes the Neutrino exploit kit to deliver Teslacrypt ransomware to victims via...
-

 290Geek
290GeekiPhone Saves Man’s Life by Stopping a Bullet from Close Range
For those who were complaining about the size of iPhone 5, this guy from the Fresno State owes his life to iPhone 5....
-

 251News
251NewsMozilla’s Bugzilla Hacked, Stolen Data Used For Targeting Firefox users
Mozilla yesterday detailed a security attack on its bug tracker and testing tool Bugzilla, as well as the steps it is taking to mitigate...
-

 302Geek
302GeekMeet Mycroft – World’s 1st Open Source Artificial Intelligence Based on Linux, Raspberry Pi and Arduino
Short Bytes: Using the Internet of Things we will control our future lives by inculcating electronics and internet in each and every small...
-

 305Geek
305GeekHomemade Helicopter Powered By 54 Miniature Drones
Last week, a YouTube user posted a video on his profile in which he recorded a test flight of his homemade personal...
-
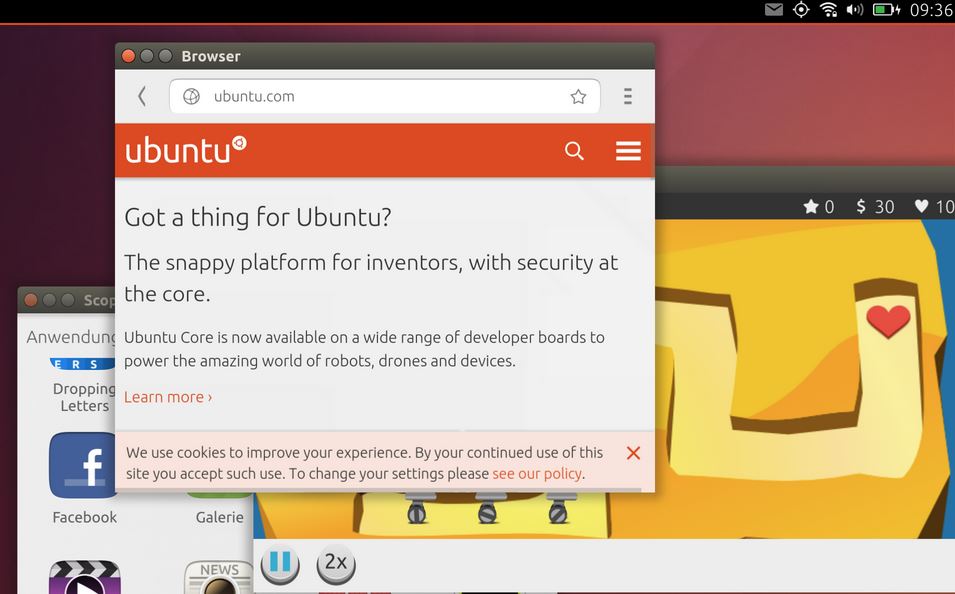
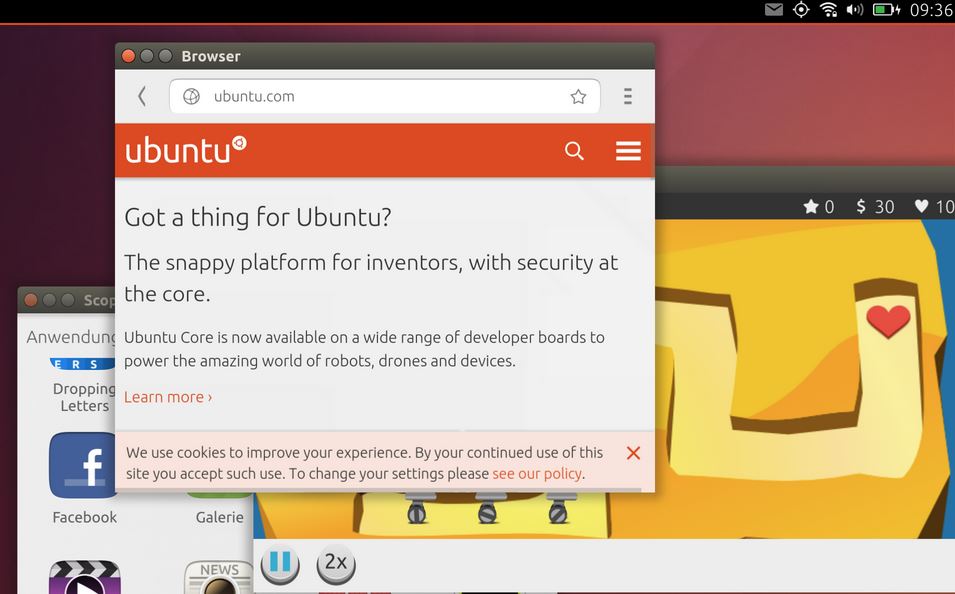 315Geek
315GeekHow to Run Ubuntu Phone in Windowed Mode
Short Bytes: Ubuntu powered phones are gaining popularity each day and we are here with a tweak to run Ubuntu Phone in windowed...
-

 180Reviews
180ReviewsHooks App Review – Get Instant Notifications for Things Important to You
Short Bytes: Hooks is an award winning alert and notification app available for Android and iOS which can send you a notification for anything...
-

 159News
159NewsGenius Teenager Hacked His Parent’s iPhone Text
A genius teenager was planning to throw a party (maybe at his home), but it is usually hard to convince your parents...
-
 325Lists
325ListsSurprising Facebook Facts That You Didn’t Know
Short Bytes: Facebook with its multi-billion user base, is the biggest social media giant today. But there are some things you might not...
-

 73Data Security
73Data Security‘UNSW is drunk’: Facebook page gets hacked on university’s Open Day
UNSW staff had to scramble to contain an embarrassing outbreak of undergraduate humour, after the university’s Facebook page was hacked on its annual...
-
 203Hacked
203HackedMicrosoft: Windows 7 and 8.1 “Spying” Updates Are Completely Optional
Short Bytes: After being criticized due to the introduction of Windows 10-like spying features in Windows 7 and 8.1, Microsoft has tried...
-

 161Vulnerabilities
161VulnerabilitiesAttackers bundle an old version of TeamViewer to exploit vulnerability
We’re used to seeing malware that exploits unpatched vulnerabilities in software. But in a new twist attackers are bundling an old version...
-
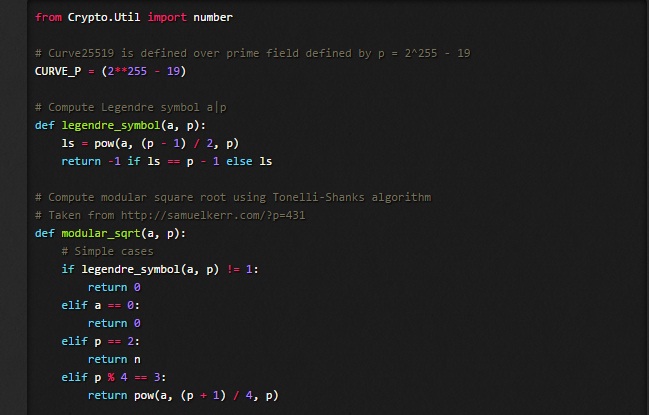
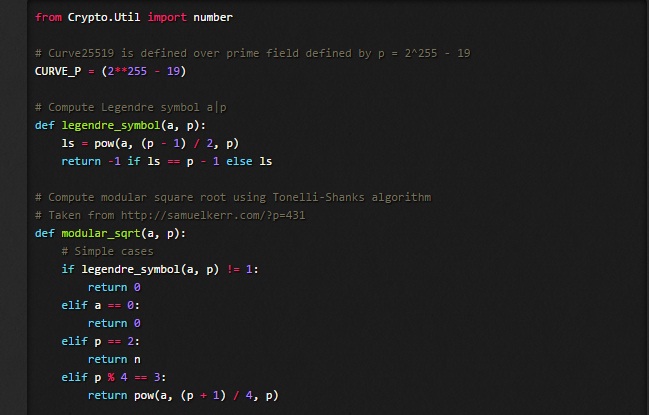 103Data Security
103Data SecurityDetecting an asymmetric Curve25519 backdoor in RSA key generation algorithms
While working on some forthcoming research on cryptographic backdoors i came across an interesting asymmetric backdoor designed to subvert RSA key generation...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




