Featured News
-
 201Vulnerabilities
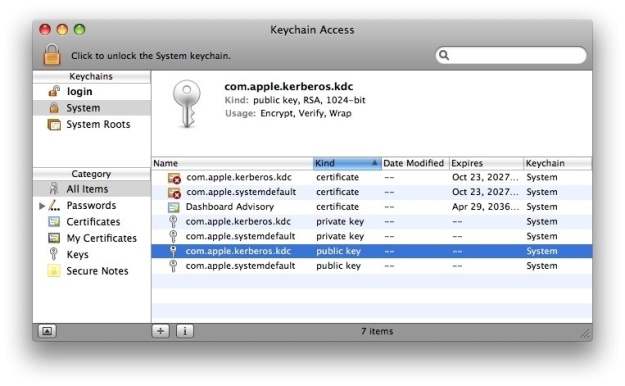
201VulnerabilitiesAttackers Can Steal Passwords from the Mac Keychain via Email or SMS
It didn’t even take a day for security researchers to find a serious way of exploiting the mechanism through which user clicks...
-
 276Malware
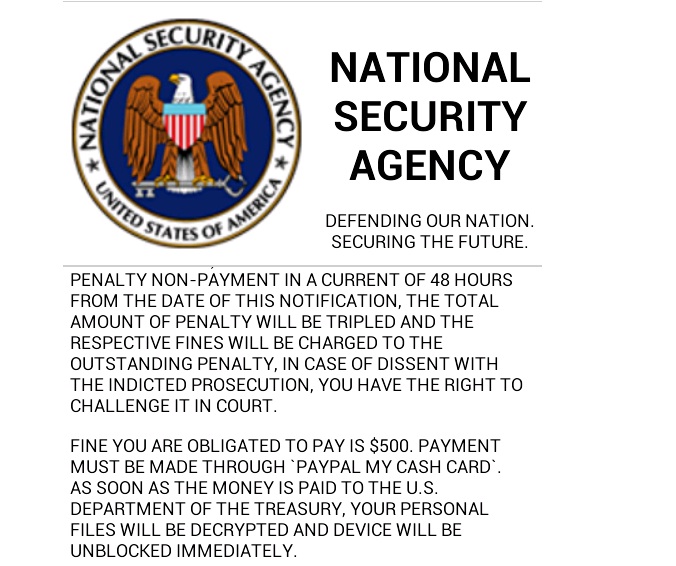
276MalwareRISK ASSESSMENT / SECURITY & HACKTIVISM Android ransomware uses XMPP chat to call home, claims it’s from NSA
A new variant of mobile ransomware that encrypts the content of Android smartphones is putting a new spin on both how it...
-

 299Geek
299GeekLinux Foundation Giving Free Chromebooks to Students Enrolling in Their Training Program
Short Bytes: The Linux Foundation is giving away one free Chromebook to those who will enroll in its one-month training courses. This...
-

 172Vulnerabilities
172VulnerabilitiesNetflix Sleepy Puppy Awakens XSS Vulnerabilities in Secondary Applications
Most automated scanning and security tools that ferret out cross-site scripting vulnerabilities don’t do much analysis beyond the target application. Netflix this...
-

 182Incidents
182Incidents9 baby monitors wide open to hacks that expose users’ most private moments
Despite its ubiquity, Internet of Things security still isn’t ready for prime time. The security of Internet-connected baby monitors got a failing...
-
 190Geek
190GeekNew Tool Reveals Your Personality Through Facebook ‘Likes’
This tool has been developed by the University of Cambridge and uses Facebook Likes data to estimate a person’s key psychological traits,...
-

 158Cyber Events
158Cyber EventsAnonymous Offshoot GhostSec Launches Another Phase of Attacks Against ISIS
Another phase of an online battle against the members of the so-called Islamic State (IS, previously ISIS/ISIL) group has been launched throughout the world by...
-
 344How To
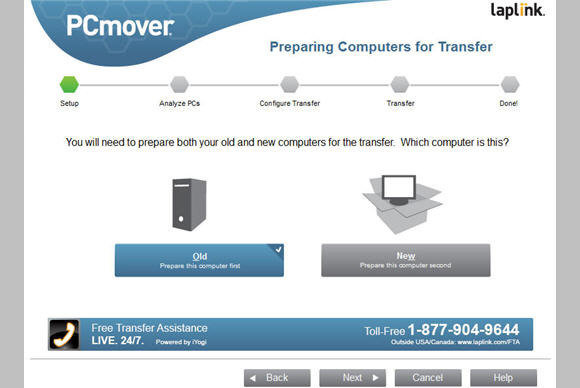
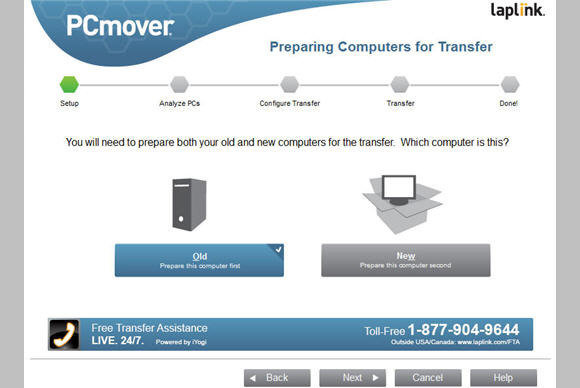
344How ToFree App from Microsoft to Move Your Files from Windows 7 to Windows 10
Microsoft partners with Laplink Software, Inc. to provide free download of Laplink’s file transfer software PCmover. According to Thomas Kool, Laplink’s CEO...
-

 292Cyber Events
292Cyber EventsLizard Squad Shuts Down British National Crime Agency Site
The United Kingdom’s National Crime Agency (NCA) website was taken down by the cyber-attackers using Distributed Denial of Service (DDoS) attack, apparently...
-

 132Geek
132GeekDetails No One Should Keep on Facebook
If you are using Facebook, there is certain information which should never be used whatsoever. The primary reason behind using Facebook is to...
-
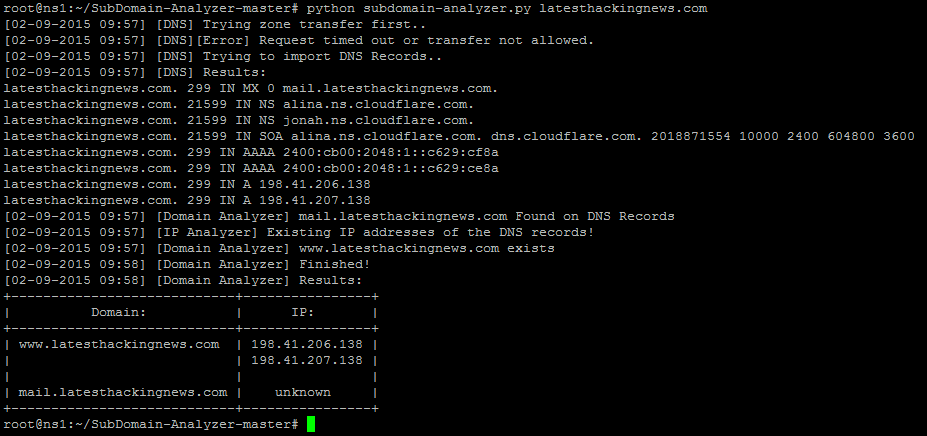
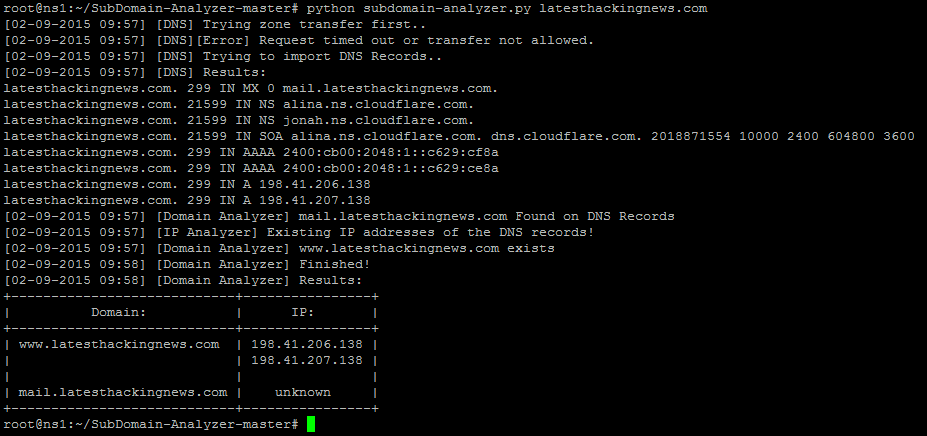 256How To
256How ToHow To View The Details of A Domain With SubDomain Analyzer
From the following steps SubDomain-Analyzer gets data from a domain: Get the zone transfer file Gathers all the information from DNS records...
-

 512Privacy
512Privacy10 steps to staying secure on public Wi‑Fi
The convenience of public Wi-Fi for many people is invaluable, yet there are risks. With all this in mind, here are 10...
-
 171Malware
171MalwareCreate your own Ransomware – Open source Ransomware malware
Ransomware, the biggest pain that is causing many PC and laptop completely encrypted. If you don’t have money or brains, you cannot...
-

 192Incidents
192IncidentsMillions hit by personal data hack still have not been told
The U.S. government has not yet notified any of the 21.5 million federal employees and contractors whose security clearance data was hacked...
-

 328Cyber Crime
328Cyber CrimeFormer US Federal Agent Pleads Guilty To $820,000 Bitcoin Laundering
Earlier today, a former United States secret service agent pleaded guilty for the theft of over $820,000 worth of digital currency, Bitcoin,...
-

 90Malware
90MalwareVMworld: VM acceleration – how do we get there?
If you have a ton of VMs sprawling the globe, how do you make them all fast? That’s the subject floating around...
-

 150Vulnerabilities
150VulnerabilitiesPayPal XSS Vulnerability Found, Fixed Before Being Exploited
A stored XSS vulnerability was identified and reported by Bitdefender’s staff to PayPal, one that could have been easily used by hackers...
-

 162Vulnerabilities
162VulnerabilitiesUPnP Trouble Puts Devices Behind Firewall at Risk
Security vulnerabilities in UPnP continue to crop up and continue to put millions of home networking devices at risk for compromise. The...
-

 100Malware
100MalwareHidden password-stealing malware lurking in your GPU card? Intel Security thinks not
Fears that malware is hiding in people’s graphics chipsets may be overclocked, according to Intel Security. Earlier this year, researchers from the...
-
 177Data Security
177Data SecurityCoreBot Can Steal Your Credentials, Download and Execute Malware
CoreBot is a new malware that steals user credentials and have the ability to cause a great amount of trouble. This stealer...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




