Featured News
-
 177Geek
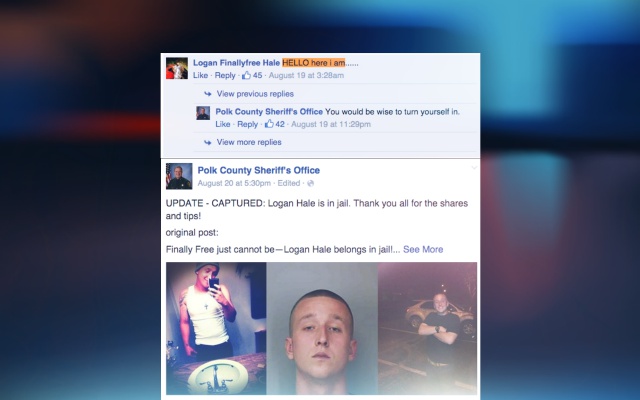
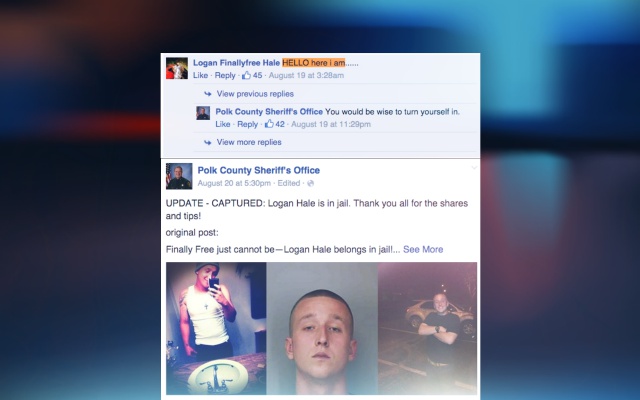
177GeekWanted Florida Man Taunts Police on their Facebook Page, Gets Arrested
Florida man who is on the top of the wanted list was found making fun of the cops that also on their...
-

 337Cyber Crime
337Cyber CrimeBBB CEO Falls for Dropbox Phishing Scam, Sends Out Malware Emails
In May 2015, we reported an alert to be careful of a Dropbox phishing scam, but it seems not everyone takes such scams...
-
 350Geek
350GeekMicrosoft Releases Updates To Spy On Windows 7, 8 and 8.1 Users
Back at the beginning of this month, we reported that how Microsoft has planned to spy on its users by releasing their...
-

 226Kids Online
226Kids OnlineMake password into a story and more parental hacks
It’s important to ensure your child's data and devices are secure at school and at home. Check out our to back to...
-
 309Privacy
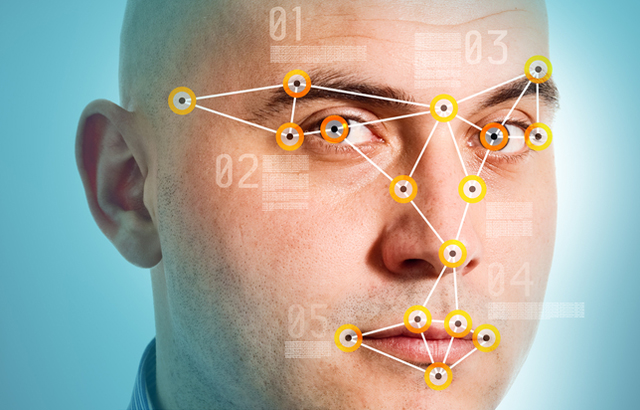
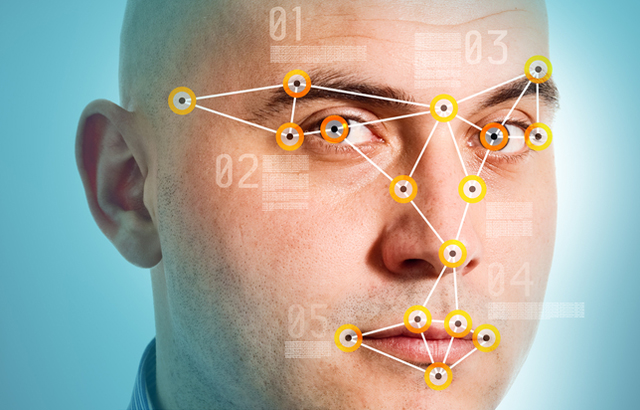
309PrivacyHow does facial recognition technology work?
In this hi-tech age, your face is increasingly becoming a digital ID for authenticating who you are online. We look at how...
-
 253Hacking Tutorials
253Hacking TutorialsReset Windows Password with Kali
Sometimes we forget our password, or even we want to reset the password of the windows OS of our friends, officemate or...
-

 309News
309NewsRoyal Saudi Air Force Website Hacked By Iranian Hackers
An Iranian hacker from Iran Hack Security Team hacked and defaced the official website of Royal Saudi Air Force this Friday morning. Though the...
-
 299Cyber Crime
299Cyber CrimeUniversity of Michigan Employees Trapped by Google Phishing Email
Around 150 University of Michigan employees lost sensitive information thanks to scammed emails, informs the university’s Division of Public Safety and Security....
-

 187Cyber Crime
187Cyber CrimeNew Amazon Phishing Scam Steals Credit Card Details
An email is being sent to users having the subject line ‘New Security feature’ and its sender appears to be Amazon. In...
-
 368How To
368How ToHere’s How to Use Microsoft Edge Without Installing Windows 10
Short Bytes: If you want to test Microsoft Edge without installing Windows 10 on your computer, here’s a good news for you....
-

 143Geek
143GeekWindows 10 Should be banned for Spying on Users – Demands Russia
After the release of Windows 10, we reported how the operating system spies on its users and how to disable selected features...
-

 408Geek
408GeekProtonMail is Now Open Source, iOS, Android Apps Unveiled
The world’s securest Switzerland based emailing service provider ProtonMail goes open source with the public release of their webmail interface version 2.0....
-

 395Hacked
395HackedRussians Demand Windows 10 Ban Because it “Spies on Users”
Short Bytes: Russian lawyers, lawmakers and state agencies have filed complaints seeking Windows 10 ban. They have claimed that Windows 10 OS...
-

 288Geek
288Geek4GB, 8GB Or 16GB; How Much RAM Do You Need?
Short Bytes: How much you should RAM: 4 GB, 8 GB or 16 GB? It’s one tricky choice that every computer buyer,...
-

 363Google Dorks
363Google DorksGoogle Dorks – Google Hacking
Google search engine find answer to our question which is helpful in our daily lives, search about our school assignments, reports, presentation and...
-

 329News
329NewsUK Based Recruitment Portal Suffers Massive Data Breach
A Saudi hacker going with the online handle of JM511 has breached into the server of a UK-based international network of independent...
-

 288Surveillance
288SurveillanceSpotify’s CEO Apologises For Collecting Private Data of its Users
Spotify wanted to collect everything that you don’t want to share with strangers and that includes your personal photos. The Internet is...
-

 166Kids Online
166Kids OnlineHow to nurture your child’s security genius
Is your child a security genius? If you think so, here’s what you can do to harness that potential for a career...
-
 246Geek
246GeekFacebook Phishing Scam, ’17 dead in a roller coaster accident’
We just got to know that a new phishing scam has started to make rounds on the popular social media network, Facebook....
-

 321How To
321How ToHow to Fix Windows 10 Slow Performance Issue and Increase Overall System Speed
Short Bytes: Many Windows users are facing reduced performance issues in Windows 10. This appears in the form of input lags and could...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




