Featured News
-
 248Geek
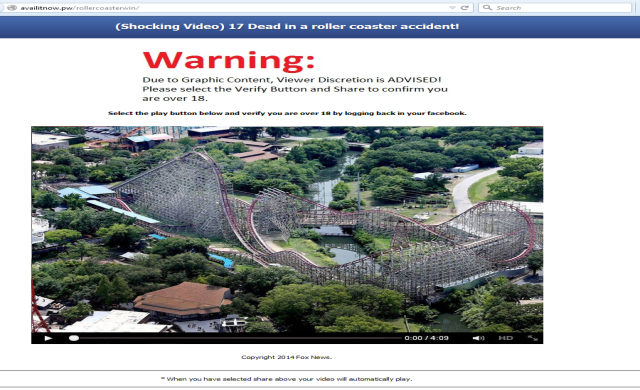
248GeekFacebook Phishing Scam, ’17 dead in a roller coaster accident’
We just got to know that a new phishing scam has started to make rounds on the popular social media network, Facebook....
-

 322How To
322How ToHow to Fix Windows 10 Slow Performance Issue and Increase Overall System Speed
Short Bytes: Many Windows users are facing reduced performance issues in Windows 10. This appears in the form of input lags and could...
-

 288How To
288How ToHow to Boot and Install Kali Linux 2.0 with USB
In this tutorial we will teach you how to boot Kali Linux 2.0 in USB and Install it. Also Read: Download...
-

 277News
277NewsAnonymous Hacks South African Government Contractor for OpMonsanto
Remember the Anonymous hackers behind the massive World Trade Center (WTC) leak? Well, they are back with another breach. The online hacktivist...
-

 280Geek
280GeekGetting Started With Linux: Part III (Command Line)
Today, we are bringing to you our third article in the “Getting Started With Linux” series. The part III deals with the...
-

 170News
170NewsU.S. Embassy Official Charged with Sextortion, Cyber Stalking Scheme
On Tuesday, a former United States embassy employee and a resident of Atlanta, Michael C. Ford has been accused of sextortion attempts...
-

 233How To
233How ToHow to Download and Install Android Marshmallow on Your Nexus Device
Short Bytes: Google has released the final preview of Android Marshmallow 6.0 and you can download it right now and install it...
-

 275News
275NewsWeb.com Security Breached, 93,000 Customers Credit Card Data Stolen
Last week, hackers breached into the servers of Web.com group, (a reputable online web services provider) and managed to access and steal...
-

 413Kids Online
413Kids OnlineNine out of ten parents worry about kids online − yet few act
The internet is arguably the new frontier for communication, collaboration and business but, with criminals also using it for ill-gotten gains, it...
-
 161News
161NewsUniversity of Virginia Servers Breached, Chinese Connection Detected
University of Virginia the latest to suffer Hack Attack — The attack allegedly originated from China. This weekend the University of Virginia...
-

 91Data Security
91Data SecurityFlaw in Remote Keyless System left Cars Vulnerable to Theft
The latest trend of vehicle hacking started by the DefCon and BlackHat security conferences has ignited a battle between the car manufacturers...
-

 106Opinion
106OpinionBack to university: cybersecurity now a major concern in higher education
Cybersecurity topics and panels were rated one of the “6 Best Things” at the recent Campus Tech conference, in Boston.
-

 300Lists
300ListsSalaries of Software Engineers: Top Paying Skills, Top Roles and Best Engineering Schools
Short Bytes: Making an attempt to inform you about the market trends of salaries of software engineers, we bring you an infographic...
-

 114Privacy
114PrivacyImpact Team releases stolen Ashley Madison data online
The Impact Team have released stolen Ashley Madison data on the dark web, which includes personal information belonging to 37 million users...
-

 278News
278NewsUnicef India Website Hacked by Turkish Hackers
A group of Turkish hackers hacked and defaced the official website of Unicef India (The United Nations Children’s Fund) last Sunday. A...
-

 85Cyber Crime
85Cyber CrimeMumsNet hit by hack, DDoS attack and SWAT
Mumsnet, the phenomenally popular British parenting website, has suffered an attack from hackers which has seen users' accounts breached, and passwords stolen....
-
 206News
206NewsAshley Madison Hack: Breached Data of 37 Million Users Published Online
Impact Team, the group of hackers who earlier stole a huge amount of personal data of about 37 million customers from the...
-
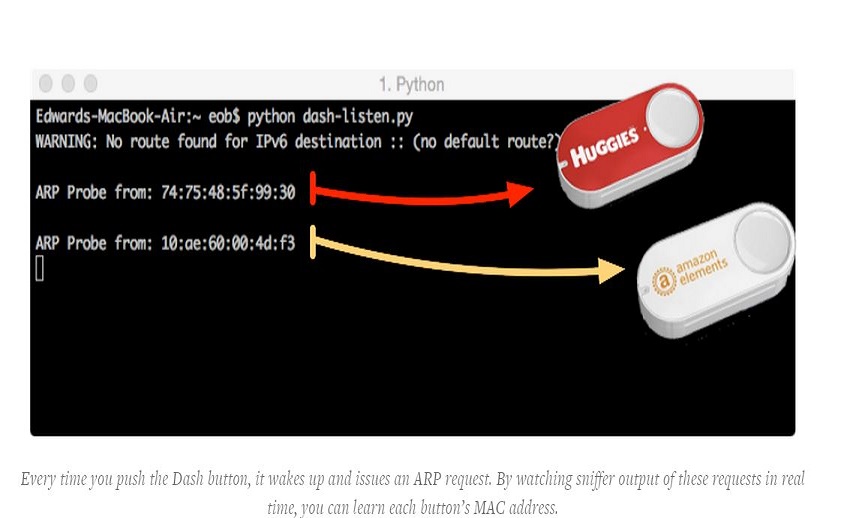
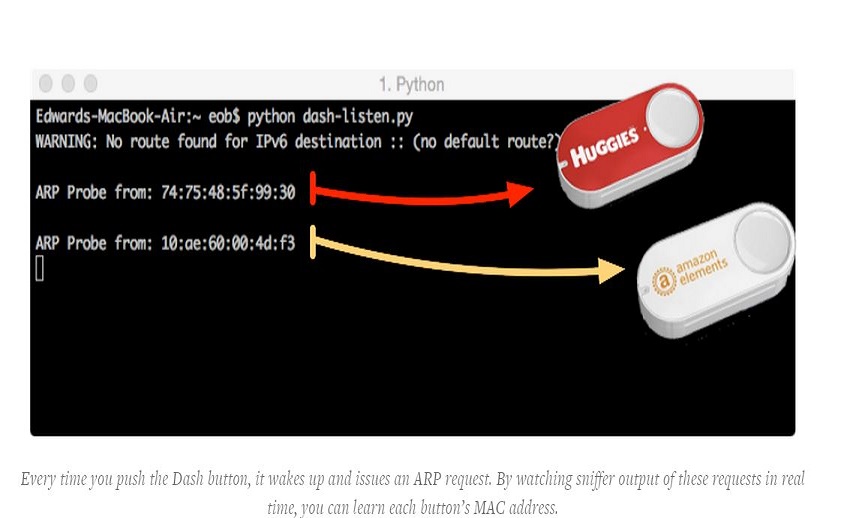 197Hacked
197HackedHow to Hack Amazon Dash Buttons To Do Anything
Short Bytes: A researcher has recently demonstrated an easy Amazon Dash Button hack. By following some simple steps, you can use this...
-

 77Cyber Crime
77Cyber CrimeCar security vulnerability study finally sees light of day
A major security vulnerability study into modern cars has finally been released, two years after it was originally intended to be published.
-

 121Opinion
121OpinionYour kids online: 5 ways to keep them out of harm’s way
With children gradually going back to school in Latin American regions, it’s time to remind our children of the importance of IT...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




