Featured News
-

 130Vulnerabilities
130VulnerabilitiesConcerns new Tor weakness is being exploited prompt dark market shutdown
Agora dark market suspends operations after finding “suspicious activity.” A dark market website that relies on the Tor privacy network to keep...
-

 122Malware
122MalwareMalware menaces poison ads as Google, Yahoo! look away
Booming attack vector offers mass malware distribution, stealthy targeting. Feature Online advertising has become an increasingly potent threat to end-user security on...
-

 168Vulnerabilities
168VulnerabilitiesPatched Ins0mnia Vulnerability Keeps Malicious iOS Apps Hidden
Apple’s monster security update of Aug. 13 included a patch for an iOS vulnerability that could beacon out location data and other...
-

 291Geek
291GeekAndroid Devices Vulnerable to Certifi-Gate Flaw Exploited By Remote Support Apps
Officials at Check Point, the IT security vendor, have discovered a rogue app on the Google Play Store that is exploiting the...
-
 325Geek
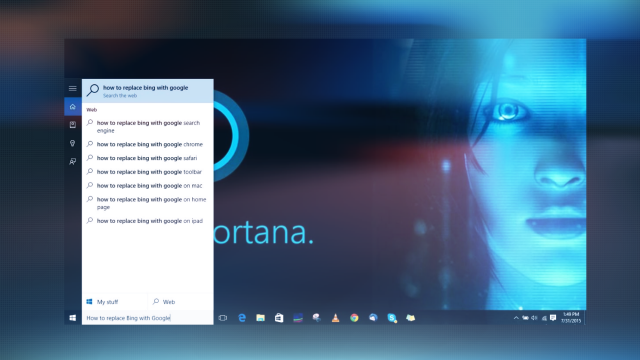
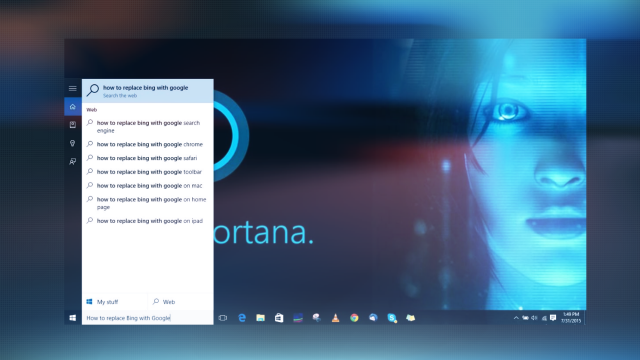
325GeekPrevent Windows 10 From Spying On Your Search Data
In the beginning of this month, Microsoft released the public version of their latest operating system Windows 10, which has already been...
-

 279News
279NewsiOS Jailbreak Backdoor Tweak Compromised 220,000 iCloud Accounts
The recent security breach on iOS platform left 220,000 iCloud user accounts vulnerable due to a backdoor privacy attack caused by the...
-

 229Scams
229ScamsSupport scams, malware and mindgames without frontiers
Introduction It might not have escaped your notice that I write quite a lot about support scams, an issue in which most...
-
 313Geek
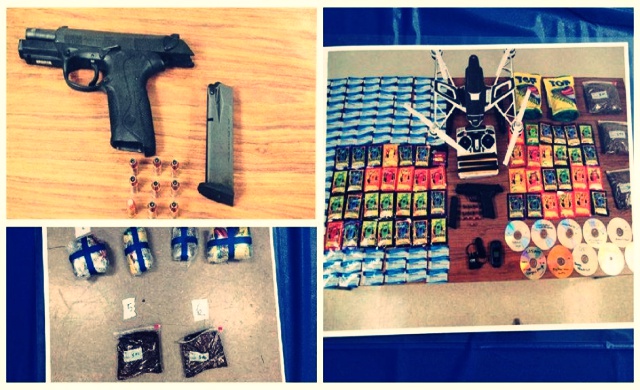
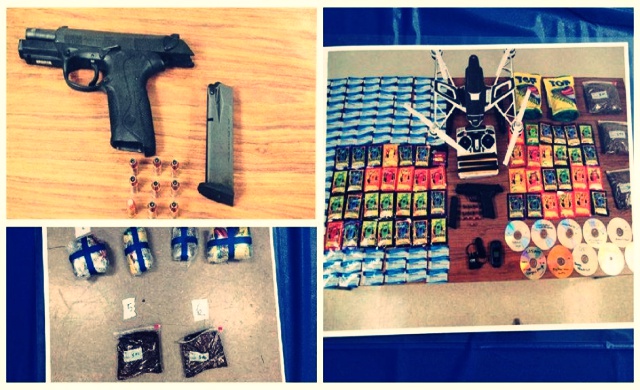
313GeekDrone Caught Delivering Drugs, X-Rated DVDs, Firearm at a High-Security Prison
The state of Maryland has witnessed an unusual case of package delivery; two individuals were found attempting to smuggle a few articles...
-
 276Hacked
276HackedIBM: Hackers are Using Tor Network More Frequently For Launching Hacking Attacks
Short Bytes: A report from IBM researchers has shown that the use of Tor network is on the rise. As a result, the growth...
-

 101Data Security
101Data SecurityHow hackers hijack the net’s phone books
Online services that charge to kick people out of games or bombard websites with data have been put out of action by...
-

 191Data Security
191Data SecurityHigh-heeled hacker builds pen-test kit into her skyscraper shoes
Social engineering with very obvious assets blinds you to techno-toolkit. MILDLY NSFW A Chinese hardware hacker has hidden a penetration-testing toolkit into her...
-

 192Data Security
192Data SecurityAshley Madison puts $377,000 bounty on hackers’ heads
Police suspect two suicides are related to the release of information stolen from the relationship-cheating website. Amid reports that the Ashley Madison...
-

 316News
316NewsPrisoner Hacked Jail TV System To Watch and Share Porn
A high-security Norwegian prison has experienced a unique event: a man was caught watching pornography on his TV after he hacked into...
-

 349Geek
349GeekWindows 10 Users Banned From Torrent Tracker Websites
The privacy concerns of Windows 10 users have reached new heights as the recent reports advice that Microsoft has implemented a feature...
-
 119Opinion
119OpinionAn Ashley Madison response plan: does your company have one?
The Ashley Madison data breach has created fresh cybersecurity threats for all organizations. A company response plan is needed. Here's what you...
-

 396News
396NewsPolice Captain Suicides After His Email Was Leaked in Ashley Madison Hack
A former police captain of the City of San Antonio police department committed suicide after his official email address was found amid...
-

 3.4KCyber Crime
3.4KCyber CrimeA big day for consumers: Companies answerable for poor cybersecurity
FTC has the authority to hold organisations to account for failing to deliver tough cybersecurity measures.
-

 107Cyber Crime
107Cyber CrimeChina Caught Spying on Tibetan Activists and Neighbouring Countries
China has been a usual suspect behind the cyber attacks carried out worldwide — From U.S. to India, everyone blames the red...
-
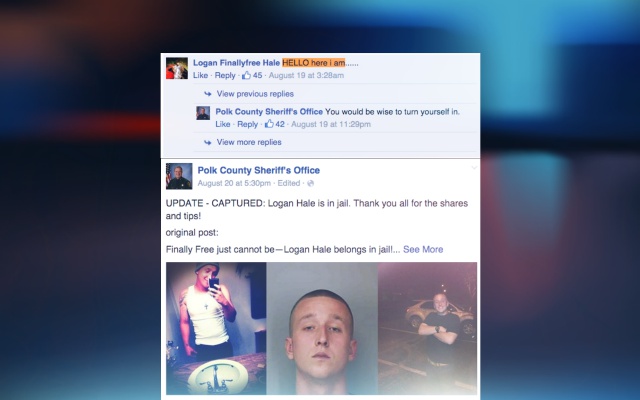
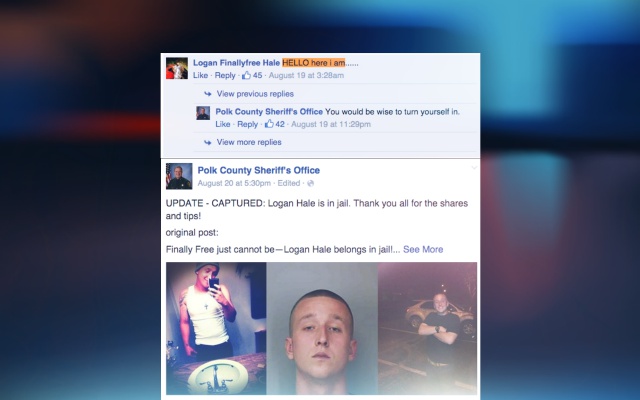 185Geek
185GeekWanted Florida Man Taunts Police on their Facebook Page, Gets Arrested
Florida man who is on the top of the wanted list was found making fun of the cops that also on their...
-

 351Cyber Crime
351Cyber CrimeBBB CEO Falls for Dropbox Phishing Scam, Sends Out Malware Emails
In May 2015, we reported an alert to be careful of a Dropbox phishing scam, but it seems not everyone takes such scams...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




