Featured News
-

 291Geek
291GeekGetting Started With Linux: Part III (Command Line)
Today, we are bringing to you our third article in the “Getting Started With Linux” series. The part III deals with the...
-

 177News
177NewsU.S. Embassy Official Charged with Sextortion, Cyber Stalking Scheme
On Tuesday, a former United States embassy employee and a resident of Atlanta, Michael C. Ford has been accused of sextortion attempts...
-

 238How To
238How ToHow to Download and Install Android Marshmallow on Your Nexus Device
Short Bytes: Google has released the final preview of Android Marshmallow 6.0 and you can download it right now and install it...
-

 283News
283NewsWeb.com Security Breached, 93,000 Customers Credit Card Data Stolen
Last week, hackers breached into the servers of Web.com group, (a reputable online web services provider) and managed to access and steal...
-

 420Kids Online
420Kids OnlineNine out of ten parents worry about kids online − yet few act
The internet is arguably the new frontier for communication, collaboration and business but, with criminals also using it for ill-gotten gains, it...
-
 169News
169NewsUniversity of Virginia Servers Breached, Chinese Connection Detected
University of Virginia the latest to suffer Hack Attack — The attack allegedly originated from China. This weekend the University of Virginia...
-

 97Data Security
97Data SecurityFlaw in Remote Keyless System left Cars Vulnerable to Theft
The latest trend of vehicle hacking started by the DefCon and BlackHat security conferences has ignited a battle between the car manufacturers...
-

 112Opinion
112OpinionBack to university: cybersecurity now a major concern in higher education
Cybersecurity topics and panels were rated one of the “6 Best Things” at the recent Campus Tech conference, in Boston.
-

 310Lists
310ListsSalaries of Software Engineers: Top Paying Skills, Top Roles and Best Engineering Schools
Short Bytes: Making an attempt to inform you about the market trends of salaries of software engineers, we bring you an infographic...
-

 120Privacy
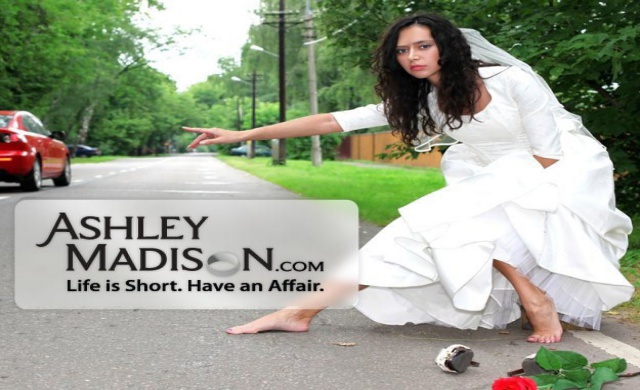
120PrivacyImpact Team releases stolen Ashley Madison data online
The Impact Team have released stolen Ashley Madison data on the dark web, which includes personal information belonging to 37 million users...
-

 287News
287NewsUnicef India Website Hacked by Turkish Hackers
A group of Turkish hackers hacked and defaced the official website of Unicef India (The United Nations Children’s Fund) last Sunday. A...
-

 91Cyber Crime
91Cyber CrimeMumsNet hit by hack, DDoS attack and SWAT
Mumsnet, the phenomenally popular British parenting website, has suffered an attack from hackers which has seen users' accounts breached, and passwords stolen....
-
 213News
213NewsAshley Madison Hack: Breached Data of 37 Million Users Published Online
Impact Team, the group of hackers who earlier stole a huge amount of personal data of about 37 million customers from the...
-
 206Hacked
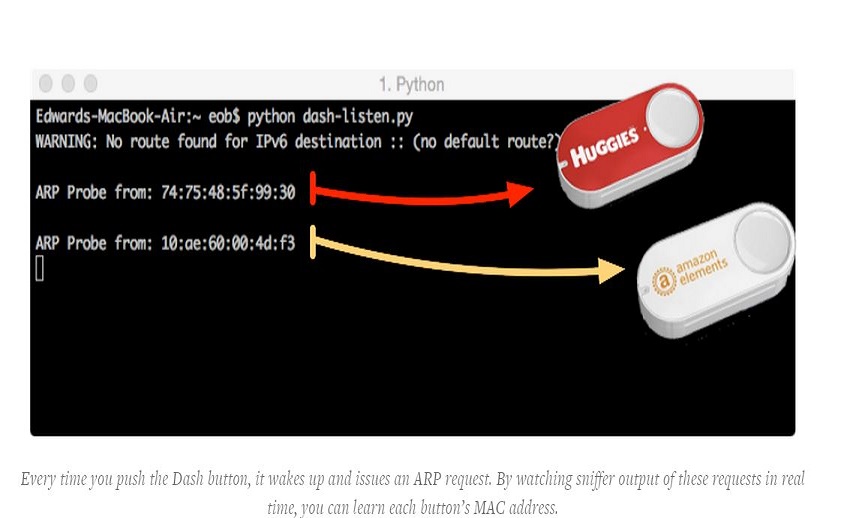
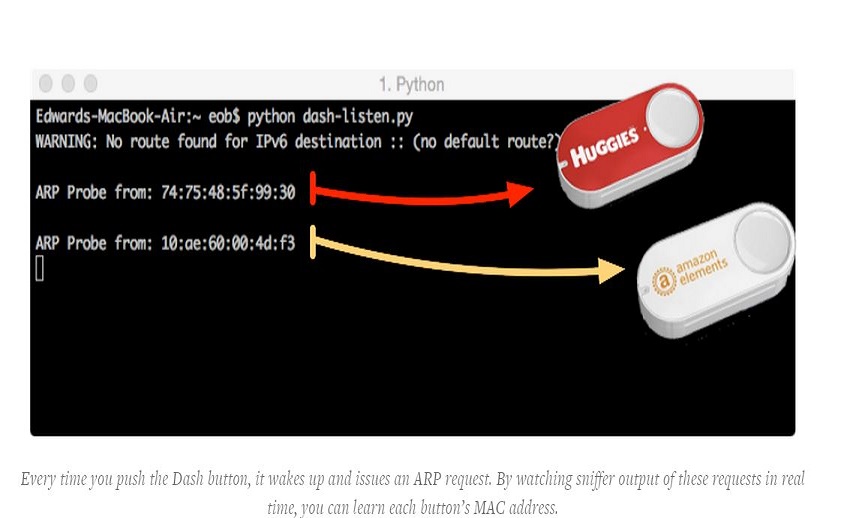
206HackedHow to Hack Amazon Dash Buttons To Do Anything
Short Bytes: A researcher has recently demonstrated an easy Amazon Dash Button hack. By following some simple steps, you can use this...
-

 82Cyber Crime
82Cyber CrimeCar security vulnerability study finally sees light of day
A major security vulnerability study into modern cars has finally been released, two years after it was originally intended to be published.
-

 127Opinion
127OpinionYour kids online: 5 ways to keep them out of harm’s way
With children gradually going back to school in Latin American regions, it’s time to remind our children of the importance of IT...
-

 305News
305NewsSecurity Breach Rattles IRS, 334,000 Tax Payers Data Stolen
A security breach of the Internal Revenue Service (IRS) that was previously reported during May in which hackers stole tax information of...
-

 296Geek
296GeekDarkode hacker accused of spreading Facebook malware pleads guilty
On Monday, the facilitator of online hacks through Darkode pleaded guilty for compromising the security of at least 77,000 computers. The 39-year...
-

 82Cyber Crime
82Cyber CrimeIRS data breach more severe than originally thought
IRS admits that the data breach it experienced in May is far bigger than previously thought.
-
 389Cyber Crime
389Cyber CrimePhishing unravelled
Phishing may well be one of the oldest online scams in the world, but it’s also one of the most effective and...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




