Featured News
-

 294Cyber Events
294Cyber EventsSpear Phishing Attack at Pentagon’s Network, Breached 4000 Military Accounts
The United States is now blaming the Russian hackers for hacking computers at the Pentagon. The United States military officials believe Russian...
-

 280Hacked
280HackedLaika BOSS: Lockheed Open Sources Secret Cyber Threat Detection Weapon
Short Bytes: Lockheed Martin has decided to open source its secret cyber threat detection tool Laika BOSS at the Black Hat Conference...
-

 100Opinion
100OpinionBlack Hat 2015 – Threats hit the road
This year at Black Hat, the focus was as much on hacking the intersections of data as on a specific computer platform.
-

 277Hacked
277HackedMan in the Cloud: Hackers Can Access Your Dropbox, Google Drive, OneDrive Files WITHOUT Password
Short Bytes: Researchers have found a new way to hack into your cloud syncing accounts without any username or password by deploying...
-
 282Hacked
282HackedRussian Hackers Attack Pentagon Computers, Used New and Unseen Methods
Short Bytes: In a recent cyberattack at Pentagon, Russian hackers are being suspected as the key players. This attack was launched around July...
-
 219Data Security
219Data SecurityShield Your PC from Radiofrequency, Hackers Can Steal Data Using Radio/Sound Waves
A recent experiment by a researcher would force you to reconsider the safety of your important data and make you put a...
-
 277Hacked
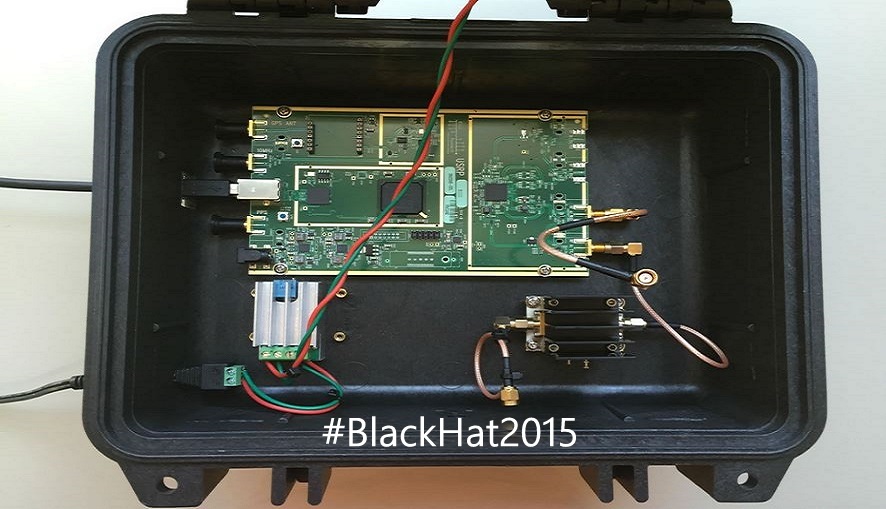
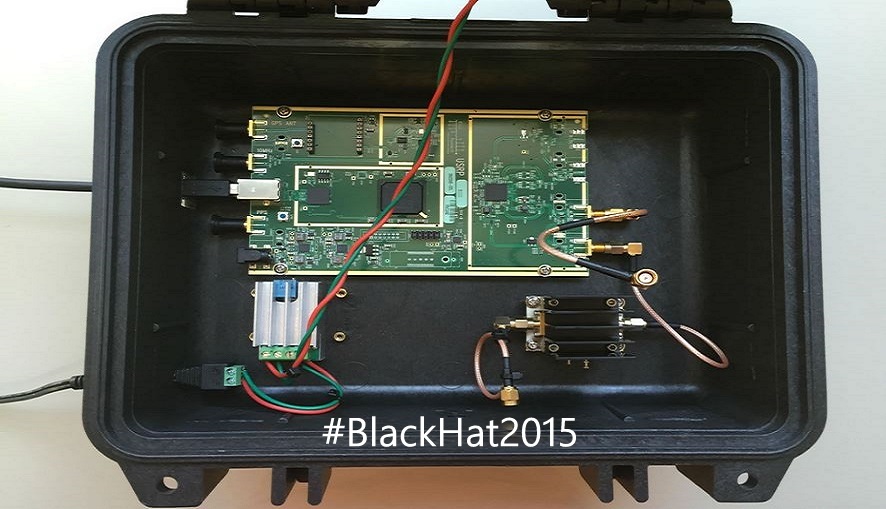
277HackedSatellite Hack: Hackers Can Easily Crack Satellites, Controlling Your Cars and Phones
Short Bytes: Colby Moore, a researcher from cyber security firm Synack, has taught the attendees of Black Hat Conf. something that can...
-

 228Hacking Tutorials
228Hacking TutorialsRunAsDate – Cracking Trial Software
It infuses the predefined date and time to the objective programming in this way preventing it from expiry. Demo variant programming basically...
-

 151Opinion
151OpinionHow’s Black Hat in 2015? It grows up (and leaves mom’s basement)
Blackhat grew! Not only did the hacker types leave their mom’s basement and get jobs, some even were forced to start explaining...
-

 202Cyber Crime
202Cyber CrimeISIS Social Media Recruiters Owned By 3 Chechen Girls
The extremist militant organization the so-called Islamic State (IS, previously ISIS/ISIL) often uses the recruitment tactic of catfishing, which means hiring Western females specifically...
-
 234Privacy
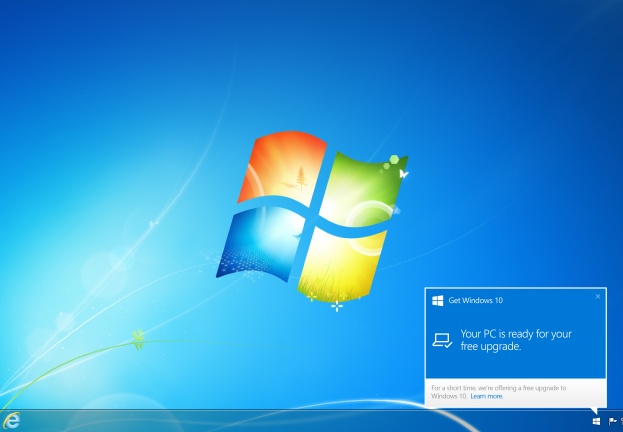
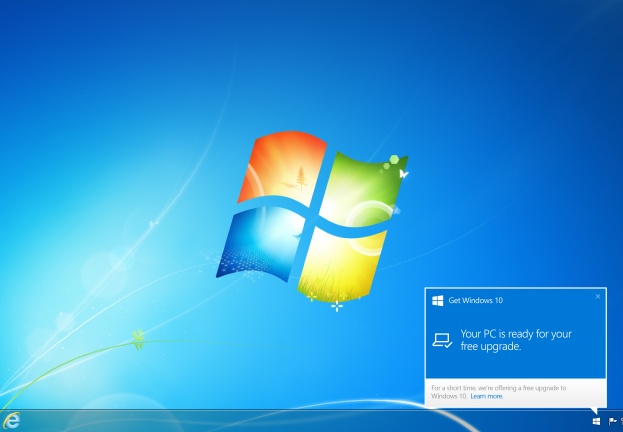
234PrivacyWindows 10, Privacy 0? ESET deep dives into the privacy of Microsoft’s new OS
Windows 10 offers more personalisation and integration than ever before. We take a look at the privacy implications of this.
-

 275Hacked
275HackedBiggest Security Update in History, Google Fixes Android Hijack Bug Stagefright
Short Bytes: This week, Google is releasing the “single largest software update the world has ever seen”. It has started rolling out patches for...
-

 329Hacked
329HackedSound Wave Hacking: Computers and Printers Hacked to Send Data as Sound Waves
Short Bytes: A team of security researchers have successfully demonstrated that the standard equipment inside computers, printers and other devices could be hacked...
-
 207Surveillance
207SurveillanceYour Smartphone and Laptop Battery Invading Your Privacy
A new research conducted by a group of researchers demonstrates how your smartphone and laptop battery can be used to invade your...
-

 235Cyber Events
235Cyber EventsU.S. Based Medical Software Company Breach Expose 4 Million People
The U.S. Department of Health and Human Services reports that earlier this year the records of 3.9 to 4 million people nationwide...
-
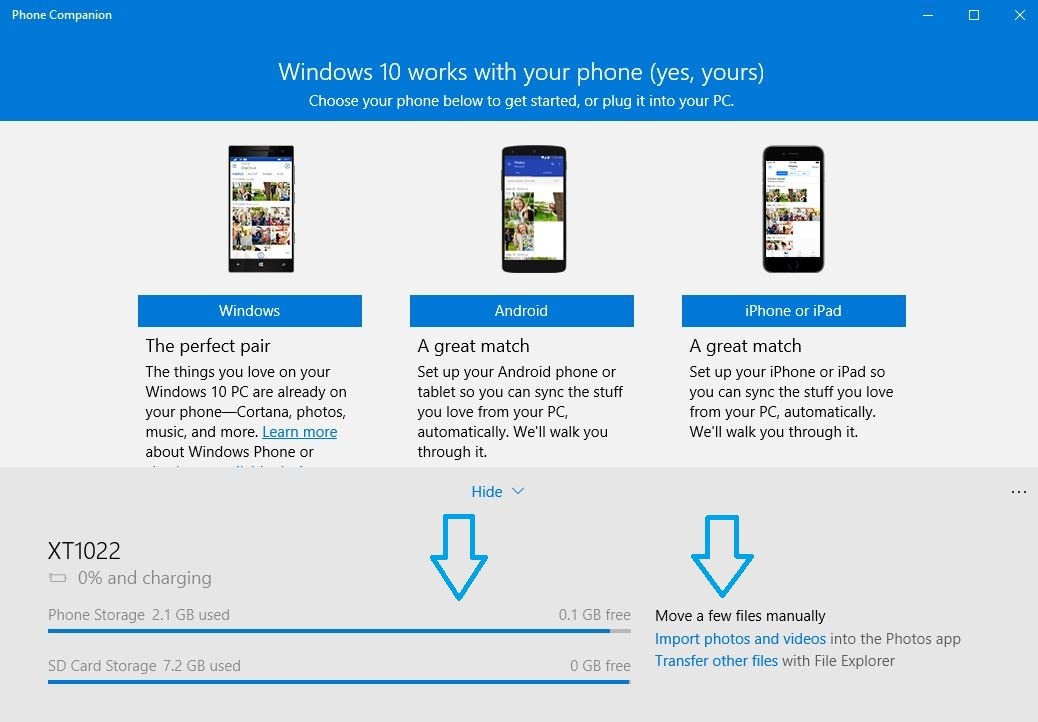
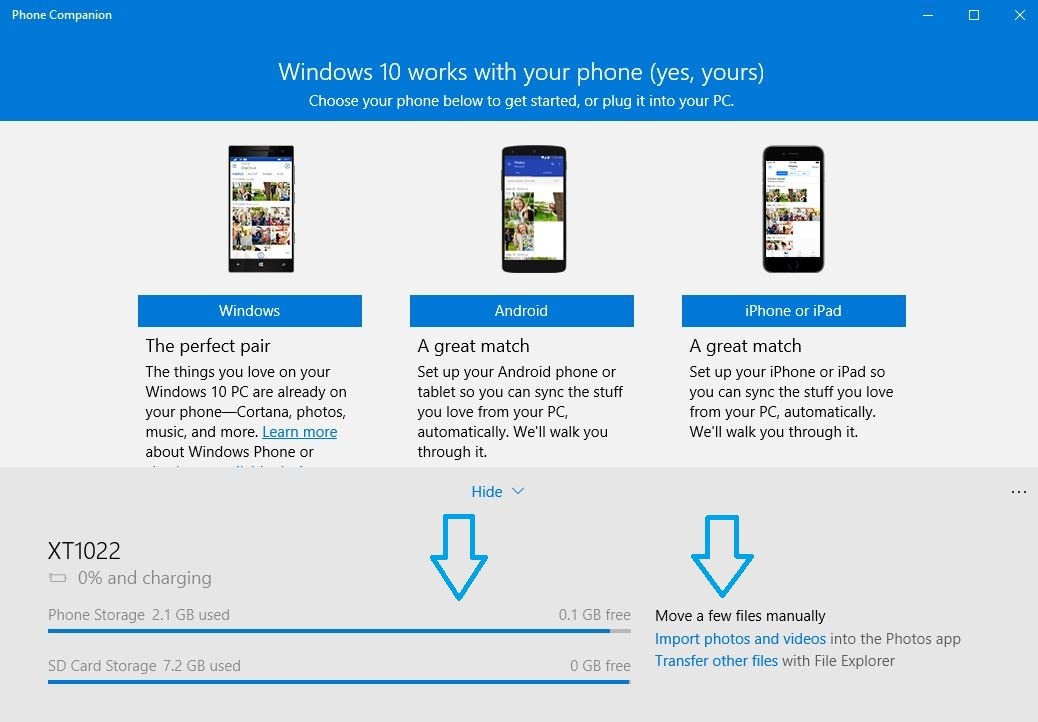 438How To
438How ToHow to Sync Your Android Phone and iPhone With Windows 10
Short Bytes: With Windows 10, there comes a pre-installed app called Windows 10 Phone Companion app. This app helps you to sync...
-

 288How To
288How ToCanonical Tells How to Choose the Best Laptop to Install Linux
Short Bytes: Canonical has released a list of Ubuntu desktop certified hardware to tell you the best laptop to install Linux. Even if...
-

 318Data Security
318Data SecurityElectronic Skateboards Are Easy To Hack
As we are approaching the much-awaited hacking conferences DefCon and Black Hat, security researchers and engineers are revealing their studies and exploits...
-
 247Data Security
247Data SecurityMiddle East’s Largest Classified Website Dubizzle Suffers Security Breach
Dubizzle, the popular Middle Eastern online classifieds for bargain hunters, sellers and job seekers has had its UAE servers compromised – albeit...
-

 70Malware
70MalwareTerracotta VPN network helps hackers remain anonymous
Hackers are using a commercially available VPN network in China to obscure the origin source of their activities.
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




